Professional Documents
Culture Documents
StamusNetworks CS JQNSM 102021 1
StamusNetworks CS JQNSM 102021 1
Uploaded by
promout8Original Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
StamusNetworks CS JQNSM 102021 1
StamusNetworks CS JQNSM 102021 1
Uploaded by
promout8Copyright:
Available Formats
Suricata Cheat Sheet | JQ commands for parsing Suricata NSM data CHEAT SHEET
Use this cheat sheet for tips and tricks to select, filter and get rapid results from Suricata using JQ - the JSON command-line processing tool - by parsing standard Suricata
eve.json logs. The commands covered in this cheat sheet are focused on the NSM data and protocol logs such as SMB, Anomaly, HTTP, DNS, TLS, Flow and others.
Select and show HTTP flows Show all NTP flows
jq -c 'select(.flow and .app_proto == "http")' eve.json jq 'select(.event_type=="flow" and .app_proto=="ntp")' eve.json
Display alerts only Show TLS records with version TLSv1
jq -c 'select(.alert)' eve.json jq 'select(.event_type=="tls" and .tls.version=="TLSv1")' eve.json
Select DNS log records with TTL values between 0 and 100 Display self signed certificates
jq 'select(.event_type=="dns")|select(.dns.ttl>0)|select(.dns.ttl<100)' | eve.json jq 'select(.event_type=="tls" and .tls.subject==.tls.issuerdn)’ eve.json
List all DCERPC requests Show DNS NXDOMAIN records
jq 'select(.event_type=="dcerpc")|.dcerpc.request' eve.json jq 'select(.event_type=="dns" and .dns.rcode=="NXDOMAIN")' eve.json
Select all protocol, flow, and alert records for flow_id: 1038930578016525 Show any SMB Anomaly event
jq 'select(.flow_id==1038930578016525)' eve.json jq 'select(.event_type=="anomaly" and .anomaly.app_proto=="smb")' eve.json
Sort and order per protocol and destination IP/Port
jq -c 'select(.flow)|[.dest_ip,.dest_port,.app_proto]' eve.json |sort|uniq -c|sort -nr|head
Show all destination IPs that have established flows with more than 10MB traffic to a client
jq 'select(.event_type=="flow" and .flow.state=="established" and .flow.bytes_toclient>10000000)|.dest_ip' eve.json
Copyright © 2021 CS-JQNSM-102021
www.stamus-networks.com
You might also like
- JNCIE-SP Self-Study Bundle (JNCIE-SP)Document3 pagesJNCIE-SP Self-Study Bundle (JNCIE-SP)BennyNo ratings yet
- CLI Temperatura y Cold Restart Ericsson TNDocument11 pagesCLI Temperatura y Cold Restart Ericsson TNandres1988maturin67% (9)
- Jcard InternalsDocument28 pagesJcard InternalsBuggy BuggysNo ratings yet
- NS2 Day 2Document24 pagesNS2 Day 2Ankith ReddyNo ratings yet
- Introduction To NS-2: Tutorial Overview of NS Walk-Through A Simple ExampleDocument33 pagesIntroduction To NS-2: Tutorial Overview of NS Walk-Through A Simple Exampleapi-26752519No ratings yet
- Call Setup Messages Layer 3Document755 pagesCall Setup Messages Layer 3nullkaNo ratings yet
- Timetra Port MibDocument161 pagesTimetra Port MibWilson OuYangNo ratings yet
- Licenses - Sl.issuance - Client Root Bridge TestDocument1 pageLicenses - Sl.issuance - Client Root Bridge TestbopufouriaNo ratings yet
- Gpon Olt TCDocument3 pagesGpon Olt TCtnarnoldNo ratings yet
- ACN - Lab - 2Document4 pagesACN - Lab - 2Jagrit SharmaNo ratings yet
- Advanced Troubleshooting of Citrix NetScalerDocument50 pagesAdvanced Troubleshooting of Citrix NetScalerTirza Sagredo de RaniNo ratings yet
- Docs If31 MibDocument71 pagesDocs If31 MibPablo FeliceNo ratings yet
- Advanced Computer Networks - Laboratory - 2 by - Vishal Jain (19103125)Document4 pagesAdvanced Computer Networks - Laboratory - 2 by - Vishal Jain (19103125)VISHAL JAINNo ratings yet
- Network Simulator ns-2: Prepared by Prof. Sachin Gajjar Pravin Gareta (08BEC156) Malav Mehta (08BEC159)Document31 pagesNetwork Simulator ns-2: Prepared by Prof. Sachin Gajjar Pravin Gareta (08BEC156) Malav Mehta (08BEC159)hardiksonagraNo ratings yet
- Command List MTCL - MGRDocument6 pagesCommand List MTCL - MGRWilliam Santos de AmorimNo ratings yet
- Network Enumeration With Nmap Module Cheat SheetDocument3 pagesNetwork Enumeration With Nmap Module Cheat Sheetskttoan1223No ratings yet
- Cisco ACI CLI Commands Cheat SheetDocument9 pagesCisco ACI CLI Commands Cheat Sheettest123No ratings yet
- TN - CLI COMMANDS - ImportantDocument12 pagesTN - CLI COMMANDS - Importanteyobal.gessese2015No ratings yet
- FLOW CHART of Computer Science ProjectDocument3 pagesFLOW CHART of Computer Science ProjectD4RKwizNo ratings yet
- Licenses - Sl.issuance - Client Ul OobDocument2 pagesLicenses - Sl.issuance - Client Ul OobbopufouriaNo ratings yet
- Asn1 Lte RRC EUTRA RRC DefinitionsDocument133 pagesAsn1 Lte RRC EUTRA RRC DefinitionsLuis Von MatterhornNo ratings yet
- Index: S.No Name of The Practical Page No. SignatureDocument8 pagesIndex: S.No Name of The Practical Page No. Signaturevishugrg2No ratings yet
- Unit III - XMPPDocument43 pagesUnit III - XMPParun134No ratings yet
- Enqueue Waits: Locks Thanks To Doug Burns For Much of The Row Lock ExampleDocument66 pagesEnqueue Waits: Locks Thanks To Doug Burns For Much of The Row Lock ExampleWahab AbdulNo ratings yet
- AppNote Vectorless Scan in RedHawk-SCDocument9 pagesAppNote Vectorless Scan in RedHawk-SCicmoneystarsNo ratings yet
- Esxcfg Command HelpDocument7 pagesEsxcfg Command HelpPieter BothaNo ratings yet
- NS2 DocumentationDocument15 pagesNS2 DocumentationreddygjNo ratings yet
- Protocol Messages - FRM LogsDocument23 pagesProtocol Messages - FRM LogssenjamirNo ratings yet
- ThresholdsDocument20 pagesThresholdsRamil BektimirovNo ratings yet
- 1.ɉɪɨɬɢɜɨɞɟɣɫɬɜɢɟ ɞɟɫɬɪɭɤɬɢɜɧɨɦɭ Ɜɯɨɞɹɳɟɦɭ Ɬɪɚɮɢɤɭ 2. Ɉɨɥɶɡɨɜɚɬɟɥɶɫɤɢɣ ɊɊ Ɩɪɚɜɨ ɧɚ ɞɨɫɬɭɩ Ɜ InternetDocument21 pages1.ɉɪɨɬɢɜɨɞɟɣɫɬɜɢɟ ɞɟɫɬɪɭɤɬɢɜɧɨɦɭ Ɜɯɨɞɹɳɟɦɭ Ɬɪɚɮɢɤɭ 2. Ɉɨɥɶɡɨɜɚɬɟɥɶɫɤɢɣ ɊɊ Ɩɪɚɜɨ ɧɚ ɞɨɫɬɭɩ Ɜ InternetИлья БердниковNo ratings yet
- PSPICE TutorialDocument32 pagesPSPICE TutorialSundari Devi BodasinghNo ratings yet
- 2304-2306 Log BookDocument4 pages2304-2306 Log BookCatherineOngNo ratings yet
- Huawei GGSN CommandsDocument19 pagesHuawei GGSN CommandsHarjinder Singh0% (1)
- Wireless SlidesDocument6 pagesWireless SlidesVinayNo ratings yet
- Esxcfg-Firewall Esxcfg-Nics Esxcfg-Vswitch Esxcfg-Vswif Esxcfg-Route Esxcfg-VmknicDocument6 pagesEsxcfg-Firewall Esxcfg-Nics Esxcfg-Vswitch Esxcfg-Vswif Esxcfg-Route Esxcfg-VmknicRogerio Cataldi RodriguesNo ratings yet
- Tut Hemant ns2Document24 pagesTut Hemant ns2dhurgadeviNo ratings yet
- DMVPN Ezvpn IsakmpDocument17 pagesDMVPN Ezvpn IsakmpSoni BroeryNo ratings yet
- Nessus Cheat SheatDocument1 pageNessus Cheat Sheatbashwork100% (12)
- Minilink CliDocument2 pagesMinilink Clipanincong100% (2)
- Comandos 20p EricssonDocument2 pagesComandos 20p EricssonCarlos EduardoNo ratings yet
- Fortinet CliDocument18 pagesFortinet CliBlas DiazNo ratings yet
- NS-2 Tutorial: Demokritos University of ThraceDocument31 pagesNS-2 Tutorial: Demokritos University of Thraceidra_fisNo ratings yet
- Computer Network Lab ManualDocument57 pagesComputer Network Lab ManualBhatNo ratings yet
- Monitoring Netflow With NfSenDocument5 pagesMonitoring Netflow With NfSenThanhNN0312No ratings yet
- leiauteNFe v4.00Document198 pagesleiauteNFe v4.00EwertonNo ratings yet
- Tema 14. SNMPNetflowDocument48 pagesTema 14. SNMPNetflowPaola GagñayNo ratings yet
- PKT TR CF PSTN On C01 071129Document50 pagesPKT TR CF PSTN On C01 071129wilco_virgoNo ratings yet
- Desch PSC3 Base MibDocument24 pagesDesch PSC3 Base MibAlejandro Rubio ReyesNo ratings yet
- Introduction To Wireless Simulations: Shao-Cheng WangDocument22 pagesIntroduction To Wireless Simulations: Shao-Cheng WangKhadidja IZNASNINo ratings yet
- Ns 2 Part 1Document7 pagesNs 2 Part 1Ketan DasNo ratings yet
- Ceragon-Mib 6.6.1.15Document131 pagesCeragon-Mib 6.6.1.15YanSenjaniNo ratings yet
- Network Command - HPUXDocument5 pagesNetwork Command - HPUXRashid NihalNo ratings yet
- IQBoard Boot MessageDocument19 pagesIQBoard Boot MessageIoannisNo ratings yet
- NR8961 2+0 Configuration StepsDocument11 pagesNR8961 2+0 Configuration Stepshan handokoNo ratings yet
- NR8961 2+0 Configuration StepsDocument11 pagesNR8961 2+0 Configuration Stepshan handokoNo ratings yet
- Roll - No:43358 - Batch: BE-IT 11-S11Document47 pagesRoll - No:43358 - Batch: BE-IT 11-S11pooja PatilNo ratings yet
- VHDL Code For LCD DisplayDocument7 pagesVHDL Code For LCD DisplayNguyễn Văn TâmNo ratings yet
- CISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkFrom EverandCISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkNo ratings yet
- Network with Practical Labs Configuration: Step by Step configuration of Router and Switch configurationFrom EverandNetwork with Practical Labs Configuration: Step by Step configuration of Router and Switch configurationNo ratings yet
- Next-Generation switching OS configuration and management: Troubleshooting NX-OS in Enterprise EnvironmentsFrom EverandNext-Generation switching OS configuration and management: Troubleshooting NX-OS in Enterprise EnvironmentsNo ratings yet
- Cisco Networks: Engineers' Handbook of Routing, Switching, and Security with IOS, NX-OS, and ASAFrom EverandCisco Networks: Engineers' Handbook of Routing, Switching, and Security with IOS, NX-OS, and ASANo ratings yet
- CB - EN.U4AIE22016 Computer Networking AssignmentDocument3 pagesCB - EN.U4AIE22016 Computer Networking AssignmentPranNo ratings yet
- (Aug, 2022) Fast2test 1Y0-241 PDF Dumps and 1Y0-241 Exam Questions (35-50)Document5 pages(Aug, 2022) Fast2test 1Y0-241 PDF Dumps and 1Y0-241 Exam Questions (35-50)Ahmad RenaldaNo ratings yet
- DCN Previous PapersDocument9 pagesDCN Previous Papers20-444 SnigdhakavyaNo ratings yet
- SIC Practicals PrintOutDocument54 pagesSIC Practicals PrintOutNiraj BelosheNo ratings yet
- ENARSI Chapter 22 STDocument34 pagesENARSI Chapter 22 STMaurice SarrNo ratings yet
- ModbusDocument35 pagesModbusyoussef mimmisNo ratings yet
- Assignment No 1Document2 pagesAssignment No 1hamza syedNo ratings yet
- Cisco IOS Voice Troubleshooting and Monitoring - HDocument30 pagesCisco IOS Voice Troubleshooting and Monitoring - HSantosh LopezNo ratings yet
- NZB SitesDocument7 pagesNZB SitesloveusantuNo ratings yet
- Chapter Four Communication ParadigmsDocument48 pagesChapter Four Communication Paradigmskim98No ratings yet
- SYSLOGDocument10 pagesSYSLOGDamian KominiakNo ratings yet
- Juniper Test-Inside jn0-104 Exam Dumps 2022-Dec-03 by Primo 79q VceDocument21 pagesJuniper Test-Inside jn0-104 Exam Dumps 2022-Dec-03 by Primo 79q VcemichaelmikealNo ratings yet
- CCNA 3 ENSA Practice PT Skills Assessment (PTSA)Document10 pagesCCNA 3 ENSA Practice PT Skills Assessment (PTSA)Sorin Ciprian PurcaruNo ratings yet
- Ethical Hacking - 4Document4 pagesEthical Hacking - 4Srinivasa ReddyNo ratings yet
- 7960 791 (H)Document131 pages7960 791 (H)Juan Riquelme HerreraNo ratings yet
- Online NetDocument13 pagesOnline NetJose AlcemirNo ratings yet
- ICND2-Chapter14 Key IdeasDocument2 pagesICND2-Chapter14 Key Ideashoang nguyen baNo ratings yet
- ISS - FirewallDocument10 pagesISS - FirewallgferantaNo ratings yet
- Flowcontrol PPT By-Vinod KumarDocument25 pagesFlowcontrol PPT By-Vinod KumarvinodNo ratings yet
- Nozomi Networks Protocol Support ListDocument6 pagesNozomi Networks Protocol Support ListCarlos GonzalezNo ratings yet
- ABL7XX 8XX Interface ManualDocument193 pagesABL7XX 8XX Interface Manual박수희No ratings yet
- Ch7. IPv6Document19 pagesCh7. IPv6Menow ShutterNo ratings yet
- MTCP Server NJNX eDocument7 pagesMTCP Server NJNX ecardonPTNo ratings yet
- Fanvil I16S DatasheetDocument2 pagesFanvil I16S DatasheetSoporte “SOPORTE ACE” AceNo ratings yet
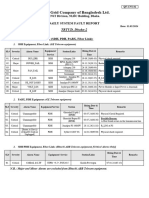
- Trtud Dhaka 2Document2 pagesTrtud Dhaka 2Iftekharul AminNo ratings yet
- Computer Network NoteDocument81 pagesComputer Network Noteupendrapaudel0No ratings yet
- MBSS - CISCO Access Switch 9200L - v1Document48 pagesMBSS - CISCO Access Switch 9200L - v1Rohit MishraNo ratings yet
- Ba Scalance-Xb-200 76Document72 pagesBa Scalance-Xb-200 76Celio Ricardo Quaio GoettenNo ratings yet
- Test Bank For Network Guide To Networks 8th Edition by WestDocument20 pagesTest Bank For Network Guide To Networks 8th Edition by Westeirlysphoebe0qf67No ratings yet