Professional Documents
Culture Documents
Traffic Encryption Options Direct Connect Ra
Uploaded by
mabe28290 ratings0% found this document useful (0 votes)
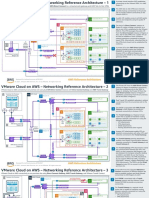
5 views5 pagesThis document describes four traffic encryption options when using AWS Direct Connect: 1) AWS Site-to-Site VPN to an Amazon VPC, 2) AWS Site-to-Site VPN to a Transit Gateway (Public VIF), 3) AWS Site-to-Site VPN Private IP VPN to AWS Transit Gateway, and 4) MACsec Security in AWS Direct Connect. It provides configuration steps for the first option of AWS Site-to-Site VPN to an Amazon VPC, which achieves encryption by combining the secure IPSec VPN tunnel with the low latency of AWS Direct Connect.
Original Description:
dxaws
Original Title
traffic-encryption-options-direct-connect-ra
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis document describes four traffic encryption options when using AWS Direct Connect: 1) AWS Site-to-Site VPN to an Amazon VPC, 2) AWS Site-to-Site VPN to a Transit Gateway (Public VIF), 3) AWS Site-to-Site VPN Private IP VPN to AWS Transit Gateway, and 4) MACsec Security in AWS Direct Connect. It provides configuration steps for the first option of AWS Site-to-Site VPN to an Amazon VPC, which achieves encryption by combining the secure IPSec VPN tunnel with the low latency of AWS Direct Connect.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
5 views5 pagesTraffic Encryption Options Direct Connect Ra
Uploaded by
mabe2829This document describes four traffic encryption options when using AWS Direct Connect: 1) AWS Site-to-Site VPN to an Amazon VPC, 2) AWS Site-to-Site VPN to a Transit Gateway (Public VIF), 3) AWS Site-to-Site VPN Private IP VPN to AWS Transit Gateway, and 4) MACsec Security in AWS Direct Connect. It provides configuration steps for the first option of AWS Site-to-Site VPN to an Amazon VPC, which achieves encryption by combining the secure IPSec VPN tunnel with the low latency of AWS Direct Connect.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 5
1.
AWS Site-to-Site VPN to an Amazon VPC
Traffic Encryption Options in
2. AWS Site-to-Site VPN to a Transit Gateway (Public VIF)
AWS Direct Connect
3. AWS Site-to-Site VPN Private IP VPN to AWS Transit Gateway
4. MACsec Security in AWS Direct Connect
Reviewed for technical accuracy October 13, 2022
© 2022, Amazon Web Services, Inc. or its affiliates. All rights reserved. AWS Reference Architecture
Configuration steps
AWS Site-to-Site VPN to an Amazon VPC 1
Create an AWS Direct Connect connection. For
dedicated connections, set up a cross-connect
This method achieves traffic encryption by combining the benefits of the end-to-end secure IPSec connection, with between the AWS device and your device (or partner
device) at the location. For hosted connections, you
low latency and consistent network experience of AWS Direct Connect when reaching resources in your Amazon VPC. must accept the hosted connection before you can
use it.
Once the connection is established, create an AWS
2 Direct Connect public virtual interface (VIF) over the
AWS Region AWS Direct Connect existing connection. Configure your customer
public VIF gateway to bring up the VIF.
Once the border gateway protocol (BGP) peer on the
VPC AWS Site-to-Site VPN 3 VIF is established, AWS advertises its public IP range
10.0.0.0/16 to the customer gateway device over the public VIF.
Subnet route Create an AWS Site-to-Site VPN to the virtual
Availability Zone 1 4 private gateway associated to the virtual private
workload subnet 1 Destination Target cloud (VPC). AWS provides two AWS VPN endpoints
10.0.0.0/24 attached to the virtual private gateway, which have
10.0.0.0/16 local
corporate network public IP addresses that are reachable over the public
E 192.168.0.0/16 vgw-id 192.168.0.0/16 VIF.
Configure your customer gateway with the VPN
AWS Direct Connect location 5 parameters to bring up the AWS Site-to-Site VPN
connection.
Amazon EC2 instance Sample traffic flow
C B A client located in the corporate network needs to
A A reach the IP address of an Amazon EC2 instance in
Direct the VPC, so the traffic is routed through the
D Connect customer gateway (CGW).
Availability Zone 2 virtual private AWS customer or customer
gateway device partner device gateway The customer gateway determines that the best
workload subnet 2 B route to the VPC is through the AWS Site-to-Site
10.0.1.0/24 VPN tunnel. The traffic is then encrypted based on
cryptographic parameters for the IPSec tunnel,
with the destination of the encrypted packet being
the Site-to-Site VPN endpoint public IP address.
Subnet route
The customer gateway determines that the best
EC2 instances Destination Target C route to the AWS VPN endpoint public IP address
10.0.0.0/16 local is through the Direct Connect public VIF.
192.168.0.0/16 vgw-id The AWS VPN endpoint receives the encrypted
D IPSec traffic and decrypts it. Because the original IP
destination address is the Amazon EC2 instance in
the VPC, the traffic is routed through the VPC
fabric to the EC2 instance.
Reviewed for technical accuracy October 13, 2022 Return traffic from the EC2 instance to the client
© 2022, Amazon Web Services, Inc. or its affiliates. All rights reserved. AWS Reference Architecture E located in the corporate network follows a reverse
but identical path.
Configuration steps
AWS Site-to-Site VPN to AWS Transit Gateway (Public VIF) 1
Create an AWS Direct Connect connection. For
dedicated connections, proceed to set up a cross-
This method achieves traffic encryption by combining the benefits of the end-to-end secure IPSec connection, with the low latency connect between the AWS device and your device
and consistent network experience of AWS Direct Connect when reaching resources in your Amazon VPCs through AWS Transit (or partner device) at the location. For hosted
connections, you must accept the connection
Gateway. This approach is suitable for customers that need to reach multiple VPCs in their AWS environment. before you can use it.
Once the connection is established, create an AWS
2 Direct Connect public virtual interface. Configure
AWS Region Spoke VPC A route AWS Direct Connect your customer gateway to bring up the VIF.
public VIF Once the BGP peer on the VIF is established, AWS
spoke VPC A Destination Target 3 advertises its public IP range to the customer
10.0.0.0/16 10.0.0.0/16 local AWS Site-to-Site VPN gateway device over the public VIF.
Availability Zone A Create an AWS Site-to-Site VPN and choose your
0.0.0.0/0 tgw-id 4
workload subnet AWS Transit Gateway instance as the VPN
10.0.1.0/24 concentrator for the AWS side.
F
Configure the customer gateway with the VPN
5 parameters to bring up the AWS VPN connection
EC2 instance corporate
VPC and route traffic destined to the Transit Gateway
Transit Gateway association network through the AWS VPN connection.
subnet AWS Transit Gateway 192.168.0.0/16
10.0.0.0/24 E AWS Direct Connect location Sample traffic flow
C A client located in the corporate network needs to
Spoke VPC route A route network traffic to the IP address of an
elastic network interface CIDR Attachment Amazon EC2 instance in the spoke VPC A, and
B
A routes the traffic through the customer gateway.
192.168.0.0/16 S2S VPN
spoke VPC B Direct The customer gateway determines that the best
VPN route B
10.1.0.0/16 Connect route to the VPC is through the AWS Site-to-Site
D AWS customer or customer
Availability Zone B CIDR Attachment VPN tunnel. The traffic is then encrypted based on
device Partner device gateway
Transit Gateway VPN cryptographic parameters for the IPSec tunnel,
10.0.0.0/24 Spoke VPC A
subnet attachment with the destination of the encrypted packet being
10.1.0.0/24 10.1.0.0/24 Spoke VPC B the AWS VPN endpoint public IP address.
VPC The customer gateway determines that the best
elastic network interface association
C route to the AWS VPN endpoint public IP address
is through the Direct Connect public VIF.
Workload subnet Spoke VPC B route
10.1.1.0/24 The AWS VPN endpoint attached to the Transit
Destination Target D Gateway receives the encrypted IPSec traffic and
10.1.0.0/16 local forwards it to the Transit Gateway.
EC2 instance The traffic is decrypted, forwarded to the spoke
0.0.0.0/0 tgw-id E VPC A, and routed to the Amazon EC2 instance.
Return traffic from the EC2 instance to the
Reviewed for technical accuracy October 13, 2022 F corporate network follows a reverse but identical
© 2022, Amazon Web Services, Inc. or its affiliates. All rights reserved. AWS Reference Architecture path.
Configuration steps
AWS Site-to-Site VPN Private IP VPN to AWS Transit Gateway 1
Create an AWS Direct Connect connection. For
dedicated connections, proceed to set up the cross-
AWS Site-to-Site VPN Private IP VPN connections are created over Direct Connect using private IP addresses, enabling enhanced connect between the AWS device and your device
(or partner device) at the location. For hosted
security and network privacy at the same time. Private IP VPNs are deployed on top of Transit VIFs and Direct Connect gateways as connections, you must accept the hosted
underlying transport. connection before you can use it.
Once the connection is established, create a Direct
2 Connect transit virtual interface (VIF) and Direct
AWS Region
Spoke VPC A route Connect gateway. Configure your customer
gateway to bring up the VIF.
spoke VPC A Destination Target
10.0.0.0/16 Associate your AWS Transit Gateway to the Direct
10.0.0.0/16 local
AWS Site-to-Site VPN 3 Connect gateway, specifying the Transit Gateway
Availability Zone A CIDR block as the allowed prefix on this
0.0.0.0/0 tgw-id attachment - make sure this CIDR block does not
workload subnet
10.0.0.0/24 overlap with any VPC CIDR block or on-premises
D
CIDR range.
corporate data center
Create the AWS Site-to-Site VPN using the Direct
192.168.0.0/16 4
EC2 instance AWS Transit Gateway Connect gateway and Transit VIF as underlying
Transit Gateway C AWS Direct Connect transport.
subnet location
VPN route Bring up the AWS Site-to-Site VPN tunnels and
10.0.1.0/28 5 route traffic destined to the Transit Gateway via
CIDR Attachment the AWS Site-to-Site VPN connection.
VPN B
elastic network interface 10.0.0.0/16 spoke VPC A attachment Sample traffic flow
10.1.0.0/16 spoke VPC B transit A
spoke VPC B A client located in the corporate network needs to
10.1.0.0/16 Spoke VPC route
gateway
association Direct Connect
VIF
customer
A route network traffic to the IP address of an
Direct
Connect router gateway Amazon EC2 instance in the spoke VPC A, and
Availability Zone B CIDR Attachment gateway routes the traffic through the customer gateway.
Transit Gateway 192.168.1.0/16 S2S VPN The customer gateway determines that the best
subnet B route to the VPC is via the AWS Site-to-Site VPN
10.1.1.0/28
connection. The traffic flows through the IPSec
tunnels with the selected encryption method,
using the Transit VIF and Direct Connect gateway
elastic network interface
as underlying transport network.
workload subnet
Spoke VPC B route
The traffic arrives to the Transit Gateway. As per
10.1.0.0/24
Destination Target C the Transit Gateway VPN route table, the traffic is
forwarded to the spoke VPC A, and then routed to
10.1.0.0/16 local the EC2 instance.
EC2 instance
0.0.0.0/0 tgw-id The return traffic from the EC2 instance to the
D client located in the corporate network follows a
reverse but identical path as described in steps A-C.
Reviewed for technical accuracy October 13, 2022
© 2022, Amazon Web Services, Inc. or its affiliates. All rights reserved. AWS Reference Architecture For more information about Private IP VPNs, see
Introducing AWS Site-to-Site Private IP VPNs.
Configuration steps
MACsec Security in AWS Direct Connect 1
To configure MACsec in an AWS Direct Connect
dedicated connection, ensure that the device at
This method achieves encryption of traffic using MACsec security (IEEE 802.1AE), delivering a native, near line-rate, and your end supports MACsec. Additionally, the Direct
Connect location also must support MACsec.
point-to-point encryption for 10 Gbps and 100 Gbps links. With MACsec, you won’t need to create VPN connections on
Create a 10G/100G AWS Direct Connect dedicated
top of your Direct Connect links to encrypt the traffic. 2 connection, choosing the option for a MACsec
enabled port.
Create a Connection Key Name (CKN)/ Connectivity
AWS Region 3
Spoke VPC A route Association Key (CAK) pair for the MACsec secret
AWS Direct Connect key, making sure that the key-pair is compatible
spoke VPC A Destination Target transit VIF with your device (or Partner device).
10.0.0.0/16
10.0.0.0/16 local Associate the CKN/CAK pair with the connection
Availability Zone A
4 via the AWS Console, AWS Command Line
0.0.0.0/0 tgw-id Interface (CLI), or API.
workload subnet
10.0.1.0/24 E Set up the cross-connect and complete the
5 physical connection to your device (or Partner
VPC
corporate network device). Update the device at your end with the
association
EC2 instance 192.168.0.0/16 CKN/CAK pair.
Transit Gateway AWS Transit Gateway
Create a transit VIF to a Direct Connect gateway
subnet AWS Direct Connect 6 on the new MACsec-enabled connection,
10.0.0.0/24 location
Spoke VPC route C associated with your AWS Transit Gateway.
D B
CIDR Attachment Sample traffic flow
Elastic network interface A A client located in the corporate network needs to
192.168.0.0/16 DX gateway A route network traffic to the IP address of an EC2
cross-connect MACsec
spoke VPC B encrypted instance in the spoke VPC A, and routes the traffic
10.1.0.0/16 Direct Connect route (MACsec encrypted)
AWS customer or to the customer gateway.
AWS Direct device
customer
CIDR Attachment Connect partner device gateway
Availability Zone B VPC The customer gateway determines that the best
Transit Gateway association 10.0.0.0/24 spoke VPC A gateway B route to the VPC is via the transit VIF, indicating
subnet the traffic should be sent over the Direct Connect
10.1.0.0/24 10.1.0.0/24 spoke VPC B connection.
gateway
association Because MACsec is enabled, the traffic between
NOTE: C the customer gateway and AWS Transit Gateway
elastic network interface
Spoke VPC B route The connection between the customer or partner device is encrypted.
workload subnet at the AWS Direct Connect Location and the on-
As per the Transit Gateway Direct Connect route
10.1.1.0/24 Destination Target premises customer gateway is only MACsec enabled if D table, the traffic is forwarded to the spoke VPC A,
the Layer-2 circuit was extended all the way.
10.1.0.0/16 local and then routed to the EC2 instance.
EC2 instance 0.0.0.0/0 tgw-id If the Layer-2 circuit terminates on the customer or Return traffic from the EC2 instance to the client
partner device at the AWS Direct Connect Location, the E located in the corporate network follows a reverse
responsibility for that segment of the circuit lies with but identical path, as described in steps A-D.
the customer or partner.
Reviewed for technical accuracy October 13, 2022 For more information about MACsec in AWS Direct
© 2022, Amazon Web Services, Inc. or its affiliates. All rights reserved. AWS Reference Architecture Connect, see Adding MACsec security to AWS Direct
Connect connections.
You might also like
- Aws Networking FundamentalsDocument322 pagesAws Networking FundamentalsAryan NNo ratings yet
- Virtual WAN DocumentationDocument596 pagesVirtual WAN DocumentationShun KamNo ratings yet
- COAX G.HN Access Multiplexer ManualDocument323 pagesCOAX G.HN Access Multiplexer ManualcardenasccNo ratings yet
- Architecting On AWSDocument44 pagesArchitecting On AWSAmit Sharma50% (2)
- AWS NetworkingDocument11 pagesAWS NetworkingLeandro OnetoNo ratings yet
- AWS VPC NotesDocument3 pagesAWS VPC NotesJoel WhiteNo ratings yet
- NC-WR744G: AC1200 Wireless Dual Band RouterDocument3 pagesNC-WR744G: AC1200 Wireless Dual Band RouterJuan Luis Meroño CanovasNo ratings yet
- Hybrid Connectivity To Transit Gateway RaDocument9 pagesHybrid Connectivity To Transit Gateway RaguilhermeNo ratings yet
- Vmware Cloud On Aws Networking RaDocument4 pagesVmware Cloud On Aws Networking RabtquahNo ratings yet
- AWS Amazon VPC Connectivity Options PDFDocument31 pagesAWS Amazon VPC Connectivity Options PDFShantanu MukherjeeNo ratings yet
- Aws VPCDocument30 pagesAws VPCjyotiraditya0709.be21No ratings yet
- AWS NetworkingDocument5 pagesAWS NetworkingAshu TuliNo ratings yet
- SD Wan Deployment Models RaDocument5 pagesSD Wan Deployment Models RaSelma SelmiNo ratings yet
- Webinar 1530 SlidesDocument24 pagesWebinar 1530 SlidesRanjan PrakashNo ratings yet
- Networking in AWSDocument32 pagesNetworking in AWSJuan Carlos Lauri PonteNo ratings yet
- 02 - Networking-in-AWS-Immersion-DayDocument32 pages02 - Networking-in-AWS-Immersion-DaypraveenwebartsNo ratings yet
- AWS Multiple Region Multi VPC ConnectivityDocument5 pagesAWS Multiple Region Multi VPC ConnectivityRavi NakarmiNo ratings yet
- AWS FaqDocument101 pagesAWS FaqsrivasthavNo ratings yet
- VPC SectionDocument21 pagesVPC SectionRAHUL NKNo ratings yet
- Amazon VPC Faqs: General QuestionsDocument27 pagesAmazon VPC Faqs: General Questionsnavvicky082079No ratings yet
- Get The Most, From The Best!!Document48 pagesGet The Most, From The Best!!Mangesh AbnaveNo ratings yet
- Inspection Deployment Models With AWS Network Firewall RaDocument7 pagesInspection Deployment Models With AWS Network Firewall RaSheloqNo ratings yet
- AWS VPC (Virtual Private Cloud) VPCDocument2 pagesAWS VPC (Virtual Private Cloud) VPCsreekanth kNo ratings yet
- AWS Solution Architect Module 2Document9 pagesAWS Solution Architect Module 2Sarbajit PatraNo ratings yet
- 4 - Network Cloud ServicesDocument79 pages4 - Network Cloud ServicesSWR AutomaçãoNo ratings yet
- AWS Private Links: Wednesday, June 9, 2021 5:32 PMDocument2 pagesAWS Private Links: Wednesday, June 9, 2021 5:32 PMRajan Babu SNo ratings yet
- AWS Advanced Networking - Specialty Sample Exam QuestionsDocument4 pagesAWS Advanced Networking - Specialty Sample Exam Questionsraghs4uNo ratings yet
- 05 Cloud-Based High-Performance Network Architecture DesignDocument51 pages05 Cloud-Based High-Performance Network Architecture DesignAlaa FarghalyNo ratings yet
- Aws VPCDocument3 pagesAws VPCSam MccallNo ratings yet
- Amazon Web Services - Three-NIC BIG-IP VEDocument20 pagesAmazon Web Services - Three-NIC BIG-IP VEsaidov19No ratings yet
- VPC DarkDocument1 pageVPC DarkRathod ChintuNo ratings yet
- 17 - Transit GatewayDocument8 pages17 - Transit Gatewaynaveen.anjeriNo ratings yet
- Aws VPC Interview QuestionsDocument5 pagesAws VPC Interview QuestionsDee PauNo ratings yet
- What Is Amazon VPC?: VPC Providing A Certain Level of Isolation Between The Different Organizations Using The ResourcesDocument3 pagesWhat Is Amazon VPC?: VPC Providing A Certain Level of Isolation Between The Different Organizations Using The ResourcesSreekar Varma100% (1)
- Network Cloud Service - Virtual Private CloudDocument17 pagesNetwork Cloud Service - Virtual Private CloudRoel CuevaNo ratings yet
- BRKACIv-2696-Multicloud Conectivity With ACIDocument33 pagesBRKACIv-2696-Multicloud Conectivity With ACIpaulo_an7381No ratings yet
- 16 Transit VPCDocument9 pages16 Transit VPCYNo ratings yet
- 3 Peering A Simple VPC Peering Tutorial - DEV CommunityDocument15 pages3 Peering A Simple VPC Peering Tutorial - DEV Communitycongdonglinux123No ratings yet
- How Do I Build A Global Transit Network On AWS?Document3 pagesHow Do I Build A Global Transit Network On AWS?Atif HassanNo ratings yet
- 02) VPC - Peering-Transit Gateway-EndpointDocument20 pages02) VPC - Peering-Transit Gateway-Endpointhanuman challisa100% (1)
- Product Comparison OPTDocument7 pagesProduct Comparison OPTRobson belchiorNo ratings yet
- Practical No. 3: Study of Networking in CloudDocument8 pagesPractical No. 3: Study of Networking in CloudG2018 Choudhari NikitaNo ratings yet
- Vforum2019 - Seoul - Junepark - DatamigrationDocument34 pagesVforum2019 - Seoul - Junepark - DatamigrationMunhee HanNo ratings yet
- Virtual Private Cloud: Presented By: P Sai Rama Krishna Aws Tranie @techwingDocument11 pagesVirtual Private Cloud: Presented By: P Sai Rama Krishna Aws Tranie @techwingmythicaltechies111No ratings yet
- Exploring The Fundamentals of AWS Networking SVC205Document94 pagesExploring The Fundamentals of AWS Networking SVC205Anirban Roy BarmanNo ratings yet
- Aws Application Load Balancer Integration VMC Aws Reference ArchitectureDocument1 pageAws Application Load Balancer Integration VMC Aws Reference Architecturevijaykumar jena100% (1)
- Establish Connection Between AWS and Azure - Project3Document10 pagesEstablish Connection Between AWS and Azure - Project3Studies MyNo ratings yet
- Cisco Based Transit VPCDocument24 pagesCisco Based Transit VPCmarc1249No ratings yet
- VPC Peering: Amazon Virtual Private CloudDocument7 pagesVPC Peering: Amazon Virtual Private Cloudsurya prakashNo ratings yet
- Virtual Private Cloud (Amazon VPC) : Naresh I Technologies Amazon Web Services Avinash Reddy TDocument33 pagesVirtual Private Cloud (Amazon VPC) : Naresh I Technologies Amazon Web Services Avinash Reddy Tma3gr8No ratings yet
- Bhavani PresentationDocument13 pagesBhavani Presentationlaxmi bhavaniNo ratings yet
- 3 Networking in AWSDocument34 pages3 Networking in AWSMiguel López100% (1)
- Network Cloud Services - Virtual Private CloudDocument193 pagesNetwork Cloud Services - Virtual Private CloudMarco MarcoNo ratings yet
- How Netflix Is Using IPv6 To Enable Hyperscale Networking NFX301Document82 pagesHow Netflix Is Using IPv6 To Enable Hyperscale Networking NFX301VettipaiyanNo ratings yet
- 1.1 VPC - Course - SlidesDocument89 pages1.1 VPC - Course - SlidesNgọc Duy VõNo ratings yet
- 4Document115 pages4bal_thakreNo ratings yet
- 2019 0705-NET Slide-DeckDocument97 pages2019 0705-NET Slide-Deckmasterlinh2008No ratings yet
- Amazon Web Services - Virtual Private Cloud (VPC) : Richard Frisby Jimmy McgibneyDocument53 pagesAmazon Web Services - Virtual Private Cloud (VPC) : Richard Frisby Jimmy Mcgibneyshaikshavali 91No ratings yet
- Aws Csa VPC R 1.0Document20 pagesAws Csa VPC R 1.0RobinNo ratings yet
- Amazon VPCDocument2 pagesAmazon VPCMounika RNo ratings yet
- Running HybridDocument24 pagesRunning HybridAllan HuangNo ratings yet
- Amazon Web Services in Action, Third Edition: An in-depth guide to AWSFrom EverandAmazon Web Services in Action, Third Edition: An in-depth guide to AWSNo ratings yet
- An Analysis of The Handover Latency Components in Mobile Ipv6Document11 pagesAn Analysis of The Handover Latency Components in Mobile Ipv6shahidNo ratings yet
- CCNA Guide To Cisco Networking: Chapter 12: Frame RelayDocument46 pagesCCNA Guide To Cisco Networking: Chapter 12: Frame RelayhemantNo ratings yet
- RTP TutorialDocument85 pagesRTP Tutorialainugiri100% (3)
- MTCNA RistiaDocument5 pagesMTCNA RistiaArif WahyudiNo ratings yet
- E COMMERCE Notes 1 and 2 (BBA)Document23 pagesE COMMERCE Notes 1 and 2 (BBA)Shiva100% (3)
- Cisco IPSec VPN Configuration - IPSec For VPNDocument19 pagesCisco IPSec VPN Configuration - IPSec For VPNsmsomeksa7No ratings yet
- 5.2.1 Packet Tracer - Configure Basic EIGRP With IPv6 Routing - ITExamAnswersDocument5 pages5.2.1 Packet Tracer - Configure Basic EIGRP With IPv6 Routing - ITExamAnswersIwanNo ratings yet
- Wi Fi Analyzer User GuideDocument14 pagesWi Fi Analyzer User GuideNelson ChiuNo ratings yet
- Data Com CH 13 MaykieDocument2 pagesData Com CH 13 MaykieMaykie W.A.No ratings yet
- IMS-ZXUN CSCF-BC-EN-Theoretical Basic-System Introduction-1-PPT-201010-42Document42 pagesIMS-ZXUN CSCF-BC-EN-Theoretical Basic-System Introduction-1-PPT-201010-42BSSNo ratings yet
- Cisco IOS Voice Troubleshooting and Monitoring GuideDocument653 pagesCisco IOS Voice Troubleshooting and Monitoring GuideFlavio WisnevskiNo ratings yet
- T Rec G.987.2 201001 S!!PDF eDocument30 pagesT Rec G.987.2 201001 S!!PDF eChinh DelNo ratings yet
- 2PAA113566-6000 en AC 800M 6.0 AC 800M DriveBusDocument80 pages2PAA113566-6000 en AC 800M 6.0 AC 800M DriveBusgicntNo ratings yet
- FM 4500 MOBI User Manual v1.4Document53 pagesFM 4500 MOBI User Manual v1.4Juan PerezNo ratings yet
- Getip PHPDocument1 pageGetip PHPtiberiubabetNo ratings yet
- Ackcio Digital Brochure 2019Document20 pagesAckcio Digital Brochure 2019ANTONIO LOZANO100% (1)
- MSTP Tutorial Part I and II - LapukhovDocument20 pagesMSTP Tutorial Part I and II - LapukhovPaul SigeiNo ratings yet
- Final Ip PackingDocument27 pagesFinal Ip PackingAhmed ElMasryNo ratings yet
- 02 - OCI Deep Dive Day 1 - v5.3Document90 pages02 - OCI Deep Dive Day 1 - v5.3jay karandikarNo ratings yet
- ThinkMo CCIE EI Lab v1.0 Module2 Section 1 Part3 Version 4.1 PDFDocument35 pagesThinkMo CCIE EI Lab v1.0 Module2 Section 1 Part3 Version 4.1 PDFlawnz gardenz100% (1)
- New PE Mikrotik Configuration With ModemDocument17 pagesNew PE Mikrotik Configuration With ModemPCL PNINo ratings yet
- Week 3 Lab 2 Assignment-1Document10 pagesWeek 3 Lab 2 Assignment-1Wenyang WuNo ratings yet
- SJ-20110927140159-001-ZXA10 20C300 (V1.3) 20GPON 20optical 20access 20convergence 20equipment 20LCT 20guide 388169 NetnumenDocument307 pagesSJ-20110927140159-001-ZXA10 20C300 (V1.3) 20GPON 20optical 20access 20convergence 20equipment 20LCT 20guide 388169 NetnumenEdivaldo VianaNo ratings yet
- Lecture 1Document29 pagesLecture 1Phạm Sơn BìnhNo ratings yet
- Wireless Part 1Document67 pagesWireless Part 1Rupesh KumarNo ratings yet
- FortiGate-224B OverviewDocument46 pagesFortiGate-224B OverviewdinuNo ratings yet
- EthernetIP 3HAC050998 enDocument78 pagesEthernetIP 3HAC050998 en王磊No ratings yet
- 19.1.5 Lab Implement An Ipv6 DMVPN Phase 3 Spoke To Spoke TopologyDocument14 pages19.1.5 Lab Implement An Ipv6 DMVPN Phase 3 Spoke To Spoke Topologyhassa nestor theraNo ratings yet