Professional Documents
Culture Documents
White Paper - EDR - Targeted Attack Analytics
Uploaded by
ahmed gaafarOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
White Paper - EDR - Targeted Attack Analytics
Uploaded by
ahmed gaafarCopyright:
Available Formats
Targeted Attack
Analytics
Using Cloud-based Artificial Intelligence for
Enterprise-Focused Advanced Threat Protection
A Key Part of an Integrated Cyber Defense Platform
WHITE PAPER
Contents
Executive Summary . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .3
Symantec Holistic Analytics Approach . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .3
Highlighted analytic: Breach detection . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .4
Symantec EDR and TAA versus Traditional Breach Detection . . . . . . . . . . . . . . . . . . .4
Traditional Breach Detection . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .4
Symantec EDR + TAA. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .4
Global Customer Base Telemetry . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .5
Symantec Uncovers Return of Dragonfly . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .5
TAA Success . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .5
Symantec Expertise . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6
TAA Benefits . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6
Conclusion . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .6
WHITE PAPER | TARGETED ATTACK ANALYTICS 02
Executive Summary
As enterprise security teams shore up defenses against malware, ransomware, and other external threats, and use existing tools to patch
vulnerabilities, attackers are shifting their attack strategy from zero-day exploits (which have become too costly and complex) to ‘living off
the land’ techniques. In fact, the Symantec 2018 Internet Security Threat Report, Volume 23 (ISTR 23) notes that only 27 percent of the 140
Symantec-tracked attack groups used zero-day vulnerabilities.
Existing security prevention tools cannot block sophisticated, previously unknown living off the land attacks that use tools already on the
targeted system. By utilizing clean system tools and dropping in as few files as possible, attackers avoid being blocked or caught by traditional
scanners and security measures. Also, memory-only attacks are even more difficult to detect as they leave very little evidence in their wake.
The only defense is a more holistic approach, one that uses both global and local context informed by attack analytics, continuously
enhanced and bolstered with new analytics. The solution should address both inside and external actors.
Symantec big data analytics and targeted attack research, and Endpoint Detect and Response (EDR) supplement existing security tools,
enabling enterprises to expose previously unknown attacks. Only Symantec brings together rich telemetry, artificial intelligence, advanced
machine learning, and research expertise to identify hard-to-detect attacks with high confidence (both at the machine and enterprise levels).
Our massive, high-quality dataset, machine learning technologies, and collective research expertise gives Symantec customers unparalleled,
tailored, and prioritized incident notification with clear recommendations for response and remediation. Delivered as a cloud service, TAA
enables new and enhanced analytics to be continually delivered to our EDR customers (using Advanced Threat Protection: Endpoint) without
the need for on-going updates.
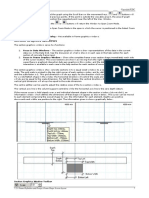
Symantec Holistic Analytics Approach
Cloud architecture Incident store
Cloud-based artificial intelligence deliver evolving analytics TAA provides descriptive, prioritized incidents including
without the need for intrusive product updates. recommended actions to drive incident resolution. TAA provides
the EDR console with more than an alert; the incident contains
Endpoint telemetry across termination points descriptive evidence along with recommended actions. Incidents
are generated in the cloud enabling updates and refinement over time.
Global telemetry data enhances the local enterprise view with
Symantec Endpoint Protection device visibility as well as all
Symantec endpoint, mobile, email, network, and web intelligence. Continuous feed to EDR and feedback
for retraining
Cloud ‘data lake’ The system includes a feedback loop.
Symantec amasses a staggering amount of telemetry; our • TAA identifies incidents with AI and advanced machine learning
authoritative data lake comprises nine trillion rows, and logs
• SOC analysts evaluate the insights
120,000 security events per second.
• Analysts feed back into the system, retraining to limit false
Analytic apps positives and reinforcing correct alerts
Analytics apps sift through the cloud data lake to identify targeted This human retraining of algorithms further refines the
attacks; these apps include Breach Analytics, PowerShell, Lateral analytics engine.
Movement, and Command and Control Beaconing.
Targeted Targeted
Buckeye Lazarus
DATA Auto Retrain
!
Produce/Sensor Telemetry LAKE
(File, network, process)
SEP, Email,
ProxySG, GIN TAA
API Incident Analytics
Gateway Store
Targeted Targeted Incidents
Unknown! Unknown! ATP Console
WHITE PAPER | TARGETED ATTACK ANALYTICS 03
Highlighted analytic: Breach detection
Symantec combines targeted attack analytics with research from our Attack Investigator Team (AIT) to find advanced attacks; our analytics
evolve to match new attack patterns. Breach detection is one example of how our analytics help stop deliberate incursions.
We analyze data from known compromised machines at the process and file level, and assess the standard tools used at the time of
compromise as well as network activity. We feed this telemetry to our learning model to train it on how a targeted incursion behaves. When
we see similar suspicious behavior, we can send incidents in real time to our EDR customers (via ATP: Endpoint console).
Lazarus
Features
Buckeye
built off
SEP telemetry
Our breach detection model is based on known
Machine-learning application and network behaviors that compromise
Clean model machines, enabling Symantec to alert customers on
machines exhibiting similar behaviors.
E-crime
Targeted Targeted Targeted Targeted
Buckeye Lazarus Unknown! Unknown!
Symantec EDR & TAA versus Traditional Breach Detection
Traditional Breach Detection
Traditional breach detection captures isolated scans from organization-wide termination points. Because this approach doesn’t provide
global visibility into emerging threats, customers must manually correlate these scans and integrate them with limited threat intelligence
sourced from external feeds. Also, because most organizations don’t have the expertise to design artificial-intelligence algorithms, nor skilled
threat researchers investigating attack groups, they incur threat visibility gaps, higher false positive rates, longer threat dwell times, and less
precise detections. Traditional breach detection can easily miss the most dangerous threats to your organization.
Isolated Scans Visibility
gaps
Too many
MANUAL CORRELATION False Positives
Endpoint Email Proxy
AND Longer threat
LIMITED INTELLIGENCE dwell times
Sandbox Anomalous
Sub-optimal
Login detections
Missing AI expertise and
Missing global context
skilled threat researchers
WHITE PAPER | TARGETED ATTACK ANALYTICS 04
Symantec EDR + TAA
By contrast, Symantec’s authoritative data lake collects event data from all our customer termination points including Symantec Endpoint
Protection, proxy, email, and cloud apps. Data scientists at our Center for Advanced Machine Learning continually develop new AI algorithms
that run on this data lake. These algorithms detect suspicious activity, which Symantec researchers review for our affected customers. When
Symantec finds a match, TAA creates a real-time incident—with a detailed analysis of the attacker, techniques, affected users, impacted
machines, and remediation guidance—and streams it to the EDR (ATP: Endpoint) console. This approach streamlines the efforts of incident
responders and enhances productivity for the entire SOC team.
Broad and
Deep Visibility
Endpoint
Massive, High Quality
Global Telemetry
Holistic, Detailed
Proxy Collection
INCIDENTS
STREAMED
DATA AI & Threat TO EDR
LAKE Research
CONSOLE
Expertise
Email Across the enterprise
Across all enterprises
Cloud Apps
Global Customer Base Telemetry
Symantec EDR with Targeted Attack Analytics parses global activity, the good and the bad, across all enterprises that comprise our telemetry
set. Our modeling adapts to new attack techniques automatically. Since it uses both local data and our global intelligence network, it
protects against more targeted attacks.
Symantec Uncovers Return of Dragonfly
• Original Dragonfly campaigns started in 2011, targeting energy companies
• TAA spotted a significant increase in new Dragonfly activity in 2017
• Attacks targeted dozens of energy companies
• Dragonfly gained access to operational networks, infiltrating power distribution on American soil
We believe this was the first time attackers could control U.S. power systems operationally.
WHITE PAPER | TARGETED ATTACK ANALYTICS 05
TAA Success
TREEHOPPER DRAGONFLY 2.0 THRIP SEEDWORM
Exposed by TAA: 3/2017 EXPOSED BY TAA: 5/2017 EXPOSED BY TAA: 1/2018 EXPOSED BY TAA: 2/2018
TARGET & MOTIVATION TARGET & MOTIVATION TARGET & MOTIVATION
TARGET & MOTIVATION
Government, Financial Energy Disruptive Government, Telecom, Energy
Activist, Government Espionage
Industrial espionage, extortion reconnaissance Espionage
Have a thorough understanding The group uses several The attackers have unique Seedworm (AKA MuddyWater)
of corporate networks, techniques to compromise exploitation and compromise is an espionage group that
targeting IP and other victims including watering techniques, using an offensive uses a custom backdoor
commercially sensitive holes, update hijacks, and Windows Management called W97M.Powermud (AKA
information. emails in conjunction with Instrumentation (WMI) POWERSTATS) that provides
exploits against six known technique known as ‘WMIGhost’ remote access.
vulnerabilities. or ‘Shadow.’
TAA FINDINGS TAA FINDINGS TAA FINDINGS TAA FINDINGS
Network reconnaissance. Covert communications Lateral movement. Initial compromise via
Network domain resources channel. Download and installation of download and installation
dumped to a file. Download of implant. malware implant. of malware implant.
Local reconnaissance to Enumeration of assets Network reconnaissance.
check running processes. on local system.
Symantec Expertise
Symantec’s analyst investigate and expose the most sophisticated and dangerous cyber attacks. The Attack Investigation Team tracks over
one hundred advanced attack groups; AIT has uncovered major targeted attacks including Regin, Stuxnet, and Dragonfly, and used its
expertise to automate discovery of new attacks.
The Symantec Center for Advanced Machine Learning makes use of the big data capability of our cloud data lake and over 70 years of
machine learning experience, creating and training new security AI algorithms and machine learning models.
This unique combination—massive, high-quality telemetry from across termination points (endpoints, web, emails, and cloud apps) and
hundreds of peerless researchers—gives us unmatched attack identification capabilities that are entirely analytics-based and attack- rather
than machine-centric.
TAA Benefits
TAA delivers unique benefits to Advanced Threat Protection customers including:
• Multiple incidence of attack detections combined with AI-driven and human analysis customized to each customer’s environment
• Cloud-based analytics that automatically adapt to new attack techniques
• Continuously delivered attack detections plus the ongoing addition of new attack analytics
• Holistic view of activity across the customer’s enterprise as well as across hundreds of millions of Symantec global customer control points
WHITE PAPER | TARGETED ATTACK ANALYTICS 06
Conclusion
The integration of Targeted Attack Analytics with EDR will solve your critical security challenges. EDR (ATP: Endpoint) customers combine
local and global telemetry, intelligence, and attack research to expose attacks that would otherwise evade detection.
ATP customers benefit from Symantec’s global visibility, world-class threat researchers, and data scientists to identify attacks in early stages.
As targeted attacks increase in sophistication and volume, enterprises need to reduce the overall number of incidents analysts have to
investigate and ensure responders are focused on the highest priority incidents.
Using TAA, EDR customers benefit from ongoing delivery of new attack analytics and generation of custom incidents, covering detailed
analysis of attacker methods, impacted machines, and remediation guidance—all at no additional cost.
Contact your Symantec Product Specialist or partner representative for more information
or to request a demo or trial.
Learn more about Symantec Endpoint Detection and Response:
https://www.symantec.com/products/endpoint-detection-and-response
Learn more about Symantec Integrated Cyber Defense:
https://www.symantec.com/theme/integrated-cyber-defense
About Symantec
Symantec Corporation (NASDAQ: SYMC), the world’s leading cyber security company, helps organizations, governments and people secure their most important data
wherever it lives. Organizations across the world look to Symantec for strategic, integrated solutions to defend against sophisticated attacks across endpoints, cloud and
infrastructure. Likewise, a global community of more than 50 million people and families rely on Symantec’s Norton and LifeLock product suites to protect their digital
lives at home and across their devices. Symantec operates one of the world’s largest civilian cyber intelligence networks, allowing it to see and protect against the most
advanced threats. For additional information, please visit www.symantec.com or connect with us on Facebook, Twitter, and LinkedIn.
350 Ellis St., Mountain View, CA 94043 USA | +1 (650) 527 8000 | 1 (800) 721 3934 | www.symantec.com
Copyright ©2018 Symantec Corporation. All rights reserved. Symantec, the Symantec Logo, and the Checkmark Logo are trademarks or registered 19A166470_SYMC_WP_ATP_TAA_EN_v1
trademarks of Symantec Corporation or its affiliates in the U.S. and other countries. Other names may be trademarks of their respective owners.
You might also like
- Security Operations Center - Analyst Guide: SIEM Technology, Use Cases and PracticesFrom EverandSecurity Operations Center - Analyst Guide: SIEM Technology, Use Cases and PracticesRating: 4 out of 5 stars4/5 (1)
- The State of Siem: Detection RiskDocument27 pagesThe State of Siem: Detection RiskAlexgasp GasparNo ratings yet
- Symantec Endpoint Detection and ResponseDocument4 pagesSymantec Endpoint Detection and ResponseKupusha CheteNo ratings yet
- CP AAD DatasheetDocument12 pagesCP AAD DatasheetPetar BajovicNo ratings yet
- 06 Art A User-Centric Machine Learning Framework For Cyber Security Operations CenterDocument3 pages06 Art A User-Centric Machine Learning Framework For Cyber Security Operations CenterlcoqzxnmNo ratings yet
- Rapid7 Insightvm Product Brief 1Document2 pagesRapid7 Insightvm Product Brief 1Ana Elisa Quintero CetinaNo ratings yet
- Rapid7 InsightVM Product BriefDocument2 pagesRapid7 InsightVM Product BriefIM ContosoNo ratings yet
- Visionary Innovation Leadership: Frost & Sullivan Best Practices AwardDocument10 pagesVisionary Innovation Leadership: Frost & Sullivan Best Practices AwardAparnaNo ratings yet
- EventTracker Security Center Product SheetDocument2 pagesEventTracker Security Center Product SheetManu PratapNo ratings yet
- APM For Security Forensics: Enhance Your IT Security With Post-Event Intrusion ResolutionDocument3 pagesAPM For Security Forensics: Enhance Your IT Security With Post-Event Intrusion Resolutionnicolepetrescu100% (1)
- Datasheet Aioniq 2022Document2 pagesDatasheet Aioniq 2022andini eldanantyNo ratings yet
- Network Detection and Response in The SOC SecuronixDocument7 pagesNetwork Detection and Response in The SOC SecuronixAvo AndrinantenainaNo ratings yet
- Practical Security ArborDocument2 pagesPractical Security ArborAnis AmouriNo ratings yet
- Master Sales Presentation V9Document18 pagesMaster Sales Presentation V9Sarthak ThakurNo ratings yet
- At A Glance - EDRDocument6 pagesAt A Glance - EDRahmed gaafarNo ratings yet
- A User-Centric Machine Learning Framework ForDocument7 pagesA User-Centric Machine Learning Framework ForSaikiranNo ratings yet
- Malicious Behavior Detection using Windows Audit LogsDocument10 pagesMalicious Behavior Detection using Windows Audit LogsUmmeHaniAsifNo ratings yet
- D3Security Splunk Integration NextGen SOARDocument5 pagesD3Security Splunk Integration NextGen SOARHuthaifaGhalebNo ratings yet
- Attaka, On Demand Vulnerability AssessmentDocument6 pagesAttaka, On Demand Vulnerability AssessmentFederico SeinedinNo ratings yet
- Artificial Intelligence (BIT705 Current and Emerging Technologies)Document3 pagesArtificial Intelligence (BIT705 Current and Emerging Technologies)Alexander LeblancNo ratings yet
- Module 3eDocument4 pagesModule 3ezackaryaskingNo ratings yet
- Awake Basic Training v1.1Document60 pagesAwake Basic Training v1.1Micja PavicNo ratings yet
- Practitioner's Guide To Building A Security Operations CenterDocument11 pagesPractitioner's Guide To Building A Security Operations Centervevrin100% (1)
- SoC Challenge 2Document8 pagesSoC Challenge 2Hansaka CostaNo ratings yet
- Kaspersky Presales Paper EDR and KATADocument21 pagesKaspersky Presales Paper EDR and KATAatherNo ratings yet
- Siem Faq PDFDocument2 pagesSiem Faq PDFFredrick Omondi JaberNo ratings yet
- Compromise Assessment - Datasheet_ControlledDocument2 pagesCompromise Assessment - Datasheet_Controlleddigitlabs.marketingNo ratings yet
- Cyberproof Azure-Security-Datasheet 822635Document2 pagesCyberproof Azure-Security-Datasheet 822635Lacky KrishnanNo ratings yet
- Juan Manuel Corchado - 2 - Presentación DeepSIEMDocument13 pagesJuan Manuel Corchado - 2 - Presentación DeepSIEMfelgamNo ratings yet
- A User-Centric Machine LearningDocument11 pagesA User-Centric Machine LearningNaresh KanigiriNo ratings yet
- Practitioner's Guide To Building A Security Operations Center (SOC)Document15 pagesPractitioner's Guide To Building A Security Operations Center (SOC)Abhirup GuhaNo ratings yet
- Devsecops Best PracticesDocument6 pagesDevsecops Best PracticesJean Pierre100% (1)
- A User-Centric Machine Learning Framework For Cyber Security Operations CenterDocument11 pagesA User-Centric Machine Learning Framework For Cyber Security Operations CenterKeerthik ReddyNo ratings yet
- Visualizing Threats: Keylines For Cyber Security: Corey Lanum, Cambridge Intelligence Louie Gasparini, Cyberflow AnalyccsDocument35 pagesVisualizing Threats: Keylines For Cyber Security: Corey Lanum, Cambridge Intelligence Louie Gasparini, Cyberflow AnalyccsKingston Maria InfantNo ratings yet
- Atp-Endpoint-En SymDocument5 pagesAtp-Endpoint-En SymAlber MunirNo ratings yet
- LR Security Intelligence Platform DatasheetDocument3 pagesLR Security Intelligence Platform Datasheetapi-308679666No ratings yet
- Deception Solution Overview: Deceive. Detect. DefendDocument4 pagesDeception Solution Overview: Deceive. Detect. DefendJimmy Alfaro HernandezNo ratings yet
- Darktrace: Best Practices For Small Teams: Data SheetDocument8 pagesDarktrace: Best Practices For Small Teams: Data SheetLuc CardNo ratings yet
- Darktrace: Best Practices For Small Teams: Data SheetDocument8 pagesDarktrace: Best Practices For Small Teams: Data SheetLuc CardNo ratings yet
- ET-SIEM-collateral 0217 CDocument2 pagesET-SIEM-collateral 0217 CManu PratapNo ratings yet
- MITRE - ATT& For CloudDocument8 pagesMITRE - ATT& For Cloudivan004No ratings yet
- Ds Small TeamsDocument8 pagesDs Small TeamsDonghan KimNo ratings yet
- SCADA Security OverviewDocument16 pagesSCADA Security Overviewtevexin998100% (1)
- SOC in A BoxDocument9 pagesSOC in A BoxA JosephNo ratings yet
- Post Breach Forensic StateDocument13 pagesPost Breach Forensic Statealfred.x.andrewsNo ratings yet
- Control Compliance Suite Vulnerability Manager enDocument6 pagesControl Compliance Suite Vulnerability Manager enFausy A. FríasNo ratings yet
- Symantec Intelligence Services: at A GlanceDocument4 pagesSymantec Intelligence Services: at A GlanceÂngelo AlfredoNo ratings yet
- Market Guide For Network Detection and Response: Lawrence Orans, Jeremy D'Hoinne, Josh ChessmanDocument15 pagesMarket Guide For Network Detection and Response: Lawrence Orans, Jeremy D'Hoinne, Josh Chessman123123123123123124215235No ratings yet
- IBM Security QRadar SIEM DatasheetDocument6 pagesIBM Security QRadar SIEM DatasheetHitesh RahangdaleNo ratings yet
- IT595 Final CapDocument10 pagesIT595 Final CapQuinter WandiaNo ratings yet
- Symantec Email Security Cloud With Skeptic WP enDocument11 pagesSymantec Email Security Cloud With Skeptic WP ensamson antonyNo ratings yet
- Configure and Test Network SecurityDocument25 pagesConfigure and Test Network SecurityparkbenchbruceNo ratings yet
- Datasheet Lastinfosec 2022Document2 pagesDatasheet Lastinfosec 2022romualdoNo ratings yet
- Panorama PDFDocument5 pagesPanorama PDFdhiraj.gaur9956No ratings yet
- IT Security Event Management: Yahya MehdizadehDocument14 pagesIT Security Event Management: Yahya Mehdizadehpvn_vora3634No ratings yet
- Qradar Solution BriefDocument2 pagesQradar Solution BriefWesley SampaioNo ratings yet
- 1 - A - Automate - Cybersecurity - Data - Triage - by - Leveraging - Human - Analysts - Cognitive - Process-5Document7 pages1 - A - Automate - Cybersecurity - Data - Triage - by - Leveraging - Human - Analysts - Cognitive - Process-5Stephen NjeriNo ratings yet
- What Is Endpoint Detection and Response (EDR) - McAfeeDocument7 pagesWhat Is Endpoint Detection and Response (EDR) - McAfeeajilani2014No ratings yet
- Cynet Solution BriefDocument17 pagesCynet Solution BriefRey RazNo ratings yet
- 06-21 SolutionBrief V10.disarmedDocument5 pages06-21 SolutionBrief V10.disarmedramramNo ratings yet
- Sedr Sizing Guide 4.5Document30 pagesSedr Sizing Guide 4.5ahmed gaafarNo ratings yet
- At A Glance - EDRDocument6 pagesAt A Glance - EDRahmed gaafarNo ratings yet
- See Enc PB101Document2 pagesSee Enc PB101ahmed gaafarNo ratings yet
- Symantec Endpoint Encryption Installation Guide 11 4 0Document84 pagesSymantec Endpoint Encryption Installation Guide 11 4 0ahmed gaafarNo ratings yet
- Deploying SEE Management Server To Be Internet Facing-1Document5 pagesDeploying SEE Management Server To Be Internet Facing-1ahmed gaafarNo ratings yet
- SB Deep Discovery AnalyzerDocument2 pagesSB Deep Discovery Analyzerahmed gaafarNo ratings yet
- Tunneling and Ipsec f5 Networks Tmos Tunneling and Ipsec ExampleDocument118 pagesTunneling and Ipsec f5 Networks Tmos Tunneling and Ipsec Exampleahmed gaafarNo ratings yet
- Nessus Scan Tuning GuideDocument34 pagesNessus Scan Tuning Guideahmed gaafarNo ratings yet
- Tenablesc API BestPracticesGuideDocument26 pagesTenablesc API BestPracticesGuideahmed gaafarNo ratings yet
- WedgeARP AMB v2.1 Training - Module A - PositioningDocument30 pagesWedgeARP AMB v2.1 Training - Module A - Positioningahmed gaafarNo ratings yet
- Configuring Ivanti Security Controls Data Model For Xtraction (v2023.1.1)Document14 pagesConfiguring Ivanti Security Controls Data Model For Xtraction (v2023.1.1)ahmed gaafarNo ratings yet
- WedgeARP AMB v2.1 Training - Module G - OperationsDocument59 pagesWedgeARP AMB v2.1 Training - Module G - Operationsahmed gaafarNo ratings yet
- Pcnse Study Guide PDFDocument344 pagesPcnse Study Guide PDFMahmud AbdullahNo ratings yet
- WedgeARP AMB v2.1 Training - Module F - Deployment and ConfigurationDocument84 pagesWedgeARP AMB v2.1 Training - Module F - Deployment and Configurationahmed gaafarNo ratings yet
- Wedge Absolute Real-Time Protection™ v2.1 Appliance Quick Start GuideDocument29 pagesWedge Absolute Real-Time Protection™ v2.1 Appliance Quick Start Guideahmed gaafarNo ratings yet
- Tenable General RequirementsDocument63 pagesTenable General Requirementsahmed gaafarNo ratings yet
- Manual Chapter: TrunksDocument8 pagesManual Chapter: Trunksahmed gaafarNo ratings yet
- IT - Group 3 ProjectDocument90 pagesIT - Group 3 ProjectAmanuel Kassa100% (1)
- Computer Networking Topologies and Transmission Media QuizDocument43 pagesComputer Networking Topologies and Transmission Media QuizSantosh PhatangareNo ratings yet
- 7 main statistical analysis types summarizedDocument1 page7 main statistical analysis types summarizedjoaonitNo ratings yet
- TD Osb AsincDocument217 pagesTD Osb AsincGabriel Abelha Dos SantosNo ratings yet
- Fox JetDocument125 pagesFox JetLuiz GustavoNo ratings yet
- Mahindra Bera Structural EngineersDocument5 pagesMahindra Bera Structural EngineersPartha Pratim RoyNo ratings yet
- Email ProtocolsDocument2 pagesEmail ProtocolsDaniel GRNo ratings yet
- Exploring Pre-Trained Text-to-Video Diffusion Models For Referring Video Object SegmentationDocument21 pagesExploring Pre-Trained Text-to-Video Diffusion Models For Referring Video Object Segmentationxepit98367No ratings yet
- Baixa Ae MalucoDocument7 pagesBaixa Ae MalucoSrCleaw 666No ratings yet
- Rapt 12Document16 pagesRapt 12tailieuxaydung2019No ratings yet
- 2019 Webroot Threat Report US OnlineDocument24 pages2019 Webroot Threat Report US OnlinePranav BhatNo ratings yet
- 10.2478 - Rput 2021 0025Document8 pages10.2478 - Rput 2021 0025Selam EbraNo ratings yet
- OS - MacOS 10.13 - OKI Macintosh Compatibility List - 1.8Document24 pagesOS - MacOS 10.13 - OKI Macintosh Compatibility List - 1.8Helton PereiraNo ratings yet
- Anil Kumar - Resume - AWS and DevOpsDocument2 pagesAnil Kumar - Resume - AWS and DevOpsanil kumar0% (1)
- Kasu-Final STPDocument48 pagesKasu-Final STPGiang ĐỗNo ratings yet
- LG-R101 Serial Communication: High Level Modbus Protocol ImplementationDocument2 pagesLG-R101 Serial Communication: High Level Modbus Protocol ImplementationIonel RacaruNo ratings yet
- Wisec2023 TuanDocument6 pagesWisec2023 TuanFrancisco J LopezNo ratings yet
- Web Design and Development FundamentalsDocument23 pagesWeb Design and Development FundamentalsFaryal FatimaNo ratings yet
- M BMTDocument20 pagesM BMTNORBELYSNo ratings yet
- KDC-X679 KDC-MP6025 KDC-MP625: Instruction ManualDocument40 pagesKDC-X679 KDC-MP6025 KDC-MP625: Instruction ManualJuan De la RivaNo ratings yet
- ESP-WROOM-32D/ESP32-WROOM-32U Datasheet: Espressif SystemsDocument25 pagesESP-WROOM-32D/ESP32-WROOM-32U Datasheet: Espressif SystemsVictor Hernandez MedinaNo ratings yet
- Applied Generative AI For Beginners Practical Knowledge 1703207445Document221 pagesApplied Generative AI For Beginners Practical Knowledge 1703207445kbossmarimba100% (2)
- Full Download Strategic Management Planning For Domestic and Global Competition 13th Edition Pearce II Solutions ManualDocument13 pagesFull Download Strategic Management Planning For Domestic and Global Competition 13th Edition Pearce II Solutions Manualboninablairvip100% (36)
- Tutorialspoint Examples: How To Use JSON Object in Java?Document2 pagesTutorialspoint Examples: How To Use JSON Object in Java?Khaliq Dawood BuxNo ratings yet
- Database Management System KCS 501Document2 pagesDatabase Management System KCS 501Sparsh SaxenaNo ratings yet
- X-B, X-C, X-E Computer 65456 1Document33 pagesX-B, X-C, X-E Computer 65456 1Isha PandeyNo ratings yet
- Document 2Document34 pagesDocument 2Samuel Fariña FariñaNo ratings yet
- Deep Learning For Sign Language RecognitionDocument4 pagesDeep Learning For Sign Language RecognitionInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- ES078Document199 pagesES078jeddijNo ratings yet
- Pagepro 5650en - All Active SolutionsDocument46 pagesPagepro 5650en - All Active Solutionsemilio559No ratings yet
- ChatGPT Millionaire 2024 - Bot-Driven Side Hustles, Prompt Engineering Shortcut Secrets, and Automated Income Streams that Print Money While You Sleep. The Ultimate Beginner’s Guide for AI BusinessFrom EverandChatGPT Millionaire 2024 - Bot-Driven Side Hustles, Prompt Engineering Shortcut Secrets, and Automated Income Streams that Print Money While You Sleep. The Ultimate Beginner’s Guide for AI BusinessNo ratings yet
- Scary Smart: The Future of Artificial Intelligence and How You Can Save Our WorldFrom EverandScary Smart: The Future of Artificial Intelligence and How You Can Save Our WorldRating: 4.5 out of 5 stars4.5/5 (55)
- ChatGPT Side Hustles 2024 - Unlock the Digital Goldmine and Get AI Working for You Fast with More Than 85 Side Hustle Ideas to Boost Passive Income, Create New Cash Flow, and Get Ahead of the CurveFrom EverandChatGPT Side Hustles 2024 - Unlock the Digital Goldmine and Get AI Working for You Fast with More Than 85 Side Hustle Ideas to Boost Passive Income, Create New Cash Flow, and Get Ahead of the CurveNo ratings yet
- Generative AI: The Insights You Need from Harvard Business ReviewFrom EverandGenerative AI: The Insights You Need from Harvard Business ReviewRating: 4.5 out of 5 stars4.5/5 (2)
- Artificial Intelligence: The Insights You Need from Harvard Business ReviewFrom EverandArtificial Intelligence: The Insights You Need from Harvard Business ReviewRating: 4.5 out of 5 stars4.5/5 (104)
- Mastering Large Language Models: Advanced techniques, applications, cutting-edge methods, and top LLMs (English Edition)From EverandMastering Large Language Models: Advanced techniques, applications, cutting-edge methods, and top LLMs (English Edition)No ratings yet
- ChatGPT Money Machine 2024 - The Ultimate Chatbot Cheat Sheet to Go From Clueless Noob to Prompt Prodigy Fast! Complete AI Beginner’s Course to Catch the GPT Gold Rush Before It Leaves You BehindFrom EverandChatGPT Money Machine 2024 - The Ultimate Chatbot Cheat Sheet to Go From Clueless Noob to Prompt Prodigy Fast! Complete AI Beginner’s Course to Catch the GPT Gold Rush Before It Leaves You BehindNo ratings yet
- AI Money Machine: Unlock the Secrets to Making Money Online with AIFrom EverandAI Money Machine: Unlock the Secrets to Making Money Online with AINo ratings yet
- The Master Algorithm: How the Quest for the Ultimate Learning Machine Will Remake Our WorldFrom EverandThe Master Algorithm: How the Quest for the Ultimate Learning Machine Will Remake Our WorldRating: 4.5 out of 5 stars4.5/5 (107)
- Who's Afraid of AI?: Fear and Promise in the Age of Thinking MachinesFrom EverandWho's Afraid of AI?: Fear and Promise in the Age of Thinking MachinesRating: 4.5 out of 5 stars4.5/5 (13)
- Midjourney Mastery - The Ultimate Handbook of PromptsFrom EverandMidjourney Mastery - The Ultimate Handbook of PromptsRating: 4.5 out of 5 stars4.5/5 (2)
- Artificial Intelligence: A Guide for Thinking HumansFrom EverandArtificial Intelligence: A Guide for Thinking HumansRating: 4.5 out of 5 stars4.5/5 (30)
- Power and Prediction: The Disruptive Economics of Artificial IntelligenceFrom EverandPower and Prediction: The Disruptive Economics of Artificial IntelligenceRating: 4.5 out of 5 stars4.5/5 (38)
- Artificial Intelligence: The Complete Beginner’s Guide to the Future of A.I.From EverandArtificial Intelligence: The Complete Beginner’s Guide to the Future of A.I.Rating: 4 out of 5 stars4/5 (15)
- The AI Advantage: How to Put the Artificial Intelligence Revolution to WorkFrom EverandThe AI Advantage: How to Put the Artificial Intelligence Revolution to WorkRating: 4 out of 5 stars4/5 (7)
- 100M Offers Made Easy: Create Your Own Irresistible Offers by Turning ChatGPT into Alex HormoziFrom Everand100M Offers Made Easy: Create Your Own Irresistible Offers by Turning ChatGPT into Alex HormoziNo ratings yet
- 2084: Artificial Intelligence and the Future of HumanityFrom Everand2084: Artificial Intelligence and the Future of HumanityRating: 4 out of 5 stars4/5 (81)
- Machine Learning: The Ultimate Beginner's Guide to Learn Machine Learning, Artificial Intelligence & Neural Networks Step by StepFrom EverandMachine Learning: The Ultimate Beginner's Guide to Learn Machine Learning, Artificial Intelligence & Neural Networks Step by StepRating: 4.5 out of 5 stars4.5/5 (19)
- Demystifying Prompt Engineering: AI Prompts at Your Fingertips (A Step-By-Step Guide)From EverandDemystifying Prompt Engineering: AI Prompts at Your Fingertips (A Step-By-Step Guide)Rating: 4 out of 5 stars4/5 (1)
- AI and Machine Learning for Coders: A Programmer's Guide to Artificial IntelligenceFrom EverandAI and Machine Learning for Coders: A Programmer's Guide to Artificial IntelligenceRating: 4 out of 5 stars4/5 (2)
- 100+ Amazing AI Image Prompts: Expertly Crafted Midjourney AI Art Generation ExamplesFrom Everand100+ Amazing AI Image Prompts: Expertly Crafted Midjourney AI Art Generation ExamplesNo ratings yet
- Make Money with ChatGPT: Your Guide to Making Passive Income Online with Ease using AI: AI Wealth MasteryFrom EverandMake Money with ChatGPT: Your Guide to Making Passive Income Online with Ease using AI: AI Wealth MasteryNo ratings yet
- 1200+ AI Prompts for Everyone.: Artificial Intelligence Prompt Library.From Everand1200+ AI Prompts for Everyone.: Artificial Intelligence Prompt Library.No ratings yet