Professional Documents
Culture Documents
Chapter 5
Uploaded by
yashthakare9267Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Chapter 5
Uploaded by
yashthakare9267Copyright:
Available Formats
Data Communication
UNIT 5: Transport Layer
Syllabus:
• Transport Service
• Elements Of Transport Protocols
• User Datagram Protocol - Transmission Control Protocol
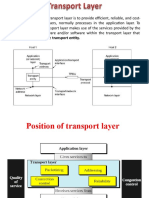
Transport Layer:
• The transport layer is a 4th layer from the top.
• The main role of the transport layer is to provide the communication services directly
to the application processes running on different hosts.
• The transport layer provides a logical communication between application processes
running on different hosts. Although the application processes on different hosts are
not physically connected, application processes use the logical communication
provided by the transport layer to send the messages to each other.
• The transport layer protocols are implemented in the end systems but not in the
network routers.
• A computer network provides more than one protocol to the network applications. For
example, TCP and UDP are two transport layer protocols that provide a different set of
services to the network layer.
• All transport layer protocols provide multiplexing/demultiplexing service. It also
provides other services such as reliable data transfer, bandwidth guarantees, and delay
guarantees.
• Each of the applications in the application layer has the ability to send a message by
using TCP or UDP. The application communicates by using either of these two
protocols. Both TCP and UDP will then communicate with the internet protocol in the
internet layer. The applications can read and write to the transport layer. Therefore, we
can say that communication is a two-way process.
Prof. Manasi Talele 1
Data Communication
Services Provided by The Transport Layer:
➢ End-to-end delivery:
• The transport layer transmits the entire message to the destination. Therefore, it
ensures the end-to-end delivery of an entire message from a source to the destination.
➢ Reliable delivery:
• The transport layer provides reliability services by retransmitting the lost and damaged
packets.
Prof. Manasi Talele 2
Data Communication
➢ The reliable delivery has four aspects:
• Error control
• Sequence control
• Loss control
• Duplication control
➢ Flow control
• Flow control is used to prevent the sender from overwhelming the receiver. If the
receiver is overloaded with too much data, then the receiver discards the packets and
asking for the retransmission of packets. This increases network congestion and thus,
reducing the system performance. The transport layer is responsible for flow control. It
uses the sliding window protocol that makes the data transmission more efficient as
well as it controls the flow of data so that the receiver does not become overwhelmed.
Sliding window protocol is byte oriented rather than frame oriented.
➢ Multiplexing
• The transport layer uses the multiplexing to improve transmission efficiency.
• Multiplexing can occur in two ways:
• Upward multiplexing: upward multiplexing means multiple transport layer
connections use the same network connection. To make more cost-effective, the
transport layer sends several transmissions bound for the same destination along the
same path; this is achieved through upward multiplexing.
Prof. Manasi Talele 3
Data Communication
• Downward multiplexing: downward multiplexing means one transport layer
connection uses the multiple network connections. Downward multiplexing allows the
transport layer to split a connection among several paths to improve the throughput.
This type of multiplexing is used when networks have a low or slow capacity.
➢ Addressing:
• According to the layered model, the transport layer interacts with the functions of the
session layer. Many protocols combine session, presentation, and application layer
protocols into a single layer known as the application layer. In these cases, delivery to
the session layer means the delivery to the application layer. Data generated by an
application on one machine must be transmitted to the correct application on another
machine. In this case, addressing is provided by the transport layer.
• The transport layer provides the user address which is specified as a station or port.
The port variable represents a particular TS user of a specified station known as a
transport service access point (TSAP). Each station has only one transport entity.
• The transport layer protocols need to know which upper-layer protocols are
communicating.
Prof. Manasi Talele 4
Data Communication
Elements Of Transport Protocols:
1. Addressing: Transport protocols utilize port numbers to address different applications
or services on a device. This addressing enables multiple services to run concurrently
on the same device and ensures that data is correctly delivered to the intended
application.
2. Segmentation and reassembly: Breaking down large data into smaller segments at
the sender's end for efficient transmission over the network. At the receiver's end,
these segments are reassembled into the original data.
3. Connection establishment and termination: In the case of connection-oriented
protocols like tcp, there's a process for setting up a connection, ensuring both ends are
ready for communication. Once data transmission is complete, the connection is
terminated.
4. Reliability mechanisms: TCP, for instance, employs acknowledgment mechanisms
and retransmission strategies to ensure reliable data delivery. It tracks sent data and
requires acknowledgments to confirm successful receipt or requests retransmission if
data is lost or corrupted.
5. Flow control: Managing the flow of data between sender and receiver to prevent
congestion or overwhelming the recipient. This involves techniques to adjust the rate
of data transmission based on the receiver's ability to process it.
6. Error detection and correction: Including checksums or other error-detection codes
within the data segments to identify any corruption during transmission. In some
cases, error correction methods are also employed to rectify errors.
Prof. Manasi Talele 5
Data Communication
7. Multiplexing/demultiplexing: Multiplexing is the process of combining data from
different applications into a single stream for transmission, while demultiplexing
separates this combined stream into individual streams for the respective applications
at the receiving end.
8. Protocol portioning: Tcp, for example, is divided into segments, each carrying a
sequence number. This helps in reordering segments at the receiver's end to
reconstruct the correct sequence of data.
What Is The TCP?
• The TCP stands for transmission control protocol. If we want the communication
between two computers and communication should be good and reliable. For example,
we want to view a web page, then we expect that nothing should be missing on the
page, or we want to download a file, then we require a complete file, i.e., Nothing
should be missing either it could be a text or an image. This can only be possible due
to the TCP. It is one of the most widely used protocols over the TCP/IP network.
Features Of TCP:
• Data delivery
TCP protocol ensures that the data is received correctly, no data is missing and in
order. If TCP protocol is not used, then the incorrect data can be received or out of
order. For example, if we try to view the web page or download a file without using
TCP, then some data or images could be missing.
• Protocol
Tcp is a connection-oriented protocol. Through the word connection-oriented, we
understand that the computers first establish a connection and then do the
communication. This is done by using a three-way handshake. In a three-way
handshake, the first sender sends the SYN message to the receiver then the receiver
sends back the SYN ACK message to confirm that the message has been received.
After receiving the SYN ACK message, the sender sends the acknowledgment
message to the receiver. In this way, the connection is established between the
computers. Once the connection is established, the data will be delivered. This
protocol guarantees the data delivery means that if the data is not received then the
TCP will resend the data.
Prof. Manasi Talele 6
Data Communication
What is the UDP?
• The UDP stands for user datagram protocol. Its working is similar to the TCP as it is
also used for sending and receiving the message. The main difference is that UDP is a
connectionless protocol. Here, connectionless means that no connection establishes
prior to communication. It also does not guarantee the delivery of data packets. It does
not even care whether the data has been received on the receiver's end or not, so it is
also known as the "fire-and-forget" protocol. It is also known as the "fire-and-
forget" protocol as it sends the data and does not care whether the data is received or
not. UDP is faster than TCP as it does not provide the assurance for the delivery of the
packets.
Features of UDP protocol:
• Transport layer protocol
• UDP is the simplest transport layer communication protocol. It contains a minimum
amount of communication mechanisms. It is considered an unreliable protocol, and it
is based on best-effort delivery services. UDP provides no acknowledgment
mechanism, which means that the receiver does not send the acknowledgment for the
received packet, and the sender also does not wait for the acknowledgment for the
packet that it has sent.
• Connectionless
• The UDP is a connectionless protocol as it does not create a virtual path to transfer the
data. It does not use the virtual path, so packets are sent in different paths between the
sender and the receiver, which leads to the loss of packets or received out of order.
Difference between TCP – UDP:
Prof. Manasi Talele 7
Data Communication
TCP UDP
Full form It stands for Transmission Control It stands for User Datagram
Protocol. Protocol.
Type of It is a connection-oriented protocol, It is a connectionless protocol,
connection which means that the connection which means that it sends the
needs to be established before the data without checking whether
data is transmitted over the network. the system is ready to receive or
not.
Reliable TCP is a reliable protocol as it UDP is an unreliable protocol as
provides assurance for the delivery of it does not take the guarantee for
data packets. the delivery of packets.
Speed TCP is slower than UDP as it UDP is faster than TCP as it
performs error checking, flow does not guarantee the delivery
control, and provides assurance for of data packets.
the delivery of
Header size The size of TCP is 20 bytes. The size of the UDP is 8 bytes.
Acknowledgment TCP uses the three-way-handshake UDP does not wait for any
concept. In this concept, if the sender acknowledgment; it just sends
receives the ACK, then the sender the data.
will send the data. TCP also has the
ability to resend the lost data.
Flow control It follows the flow control This protocol follows no such
mechanism mechanism in which too many mechanism.
packets cannot be sent to the receiver
at the same time.
Error checking TCP performs error checking by It does not perform any error
using a checksum. When the data is checking, and also does not
corrected, then the data is resend the lost data packets.
retransmitted to the receiver.
Applications This protocol is mainly used where a This protocol is used where fast
secure and reliable communication communication is required and
process is required, like military does not care about the
services, web browsing, and e-mail. reliability like VoIP, game
streaming, video and music
streaming, etc.
Prof. Manasi Talele 8
You might also like
- Introduction to Internet & Web Technology: Internet & Web TechnologyFrom EverandIntroduction to Internet & Web Technology: Internet & Web TechnologyNo ratings yet
- Hacking Network Protocols: Unlocking the Secrets of Network Protocol AnalysisFrom EverandHacking Network Protocols: Unlocking the Secrets of Network Protocol AnalysisNo ratings yet
- Lecture 5Document11 pagesLecture 5Rylan2911No ratings yet
- CHAPTER 9: Transport Layer: 9.0.1 WelcomeDocument26 pagesCHAPTER 9: Transport Layer: 9.0.1 Welcomecamys18No ratings yet
- CN Unit 5 Computer Network NotesDocument33 pagesCN Unit 5 Computer Network Notesgdsc.pragatiNo ratings yet
- CN Unit-Iv Notes - ExtraDocument28 pagesCN Unit-Iv Notes - Extrakhurram060123No ratings yet
- Transport LayerDocument9 pagesTransport LayerUnkown userNo ratings yet
- CN UNIT-IIIDocument17 pagesCN UNIT-IIIHari MNo ratings yet
- Unit 5: Transport LayerDocument17 pagesUnit 5: Transport LayerSagar wagleNo ratings yet
- Final Assignment Computer NetworksDocument12 pagesFinal Assignment Computer NetworksMasood MughalNo ratings yet
- TCP ProtocalDocument30 pagesTCP ProtocalNaresh PatnanaNo ratings yet
- CN 1Document7 pagesCN 1T024KOUSTAV CHATTERJEENo ratings yet
- Transport Layer STDDocument8 pagesTransport Layer STDMd Habibur RahmanNo ratings yet
- 5-Chapter Five - Transport LayerDocument21 pages5-Chapter Five - Transport LayerWONDYE DESTANo ratings yet
- Client/Server Paradigm: Mod 4 Process-To-Process DeliveryDocument29 pagesClient/Server Paradigm: Mod 4 Process-To-Process DeliverySUREDDY TANUJA MSCS2018No ratings yet
- Transport LayerDocument2 pagesTransport LayerAlam GarciaNo ratings yet
- Transport Layer ServicesDocument7 pagesTransport Layer ServicesashkingNo ratings yet
- Dev Sanskriti VishwavidyalayaDocument8 pagesDev Sanskriti VishwavidyalayaAnshika SharmaNo ratings yet
- 01 OverviewDocument56 pages01 OverviewPrathik KharviNo ratings yet
- Osi 3Document13 pagesOsi 3itachigood980No ratings yet
- CN UNIT 4 Transport LayerDocument32 pagesCN UNIT 4 Transport Layerharsharewards1No ratings yet
- Lecture 11Document17 pagesLecture 11تُحف العقولNo ratings yet
- Unit 3Document126 pagesUnit 3PrathameshNo ratings yet
- Unit - Iv: Transport LayerDocument55 pagesUnit - Iv: Transport LayerSundaram MuthuNo ratings yet
- 27 BCS53 2020121505394441Document27 pages27 BCS53 2020121505394441Pallavi BNo ratings yet
- Q1. Explain All Design Issues For Several Layers in Computer. What Is Connection Oriented and Connectionless Service?Document8 pagesQ1. Explain All Design Issues For Several Layers in Computer. What Is Connection Oriented and Connectionless Service?Shabbir KahodawalaNo ratings yet
- Unit IV Transport LAYERDocument27 pagesUnit IV Transport LAYERNagaraj VaratharajNo ratings yet
- CN3,4Document37 pagesCN3,4pendemvikas0915No ratings yet
- Communication and Networking - TERMSDocument7 pagesCommunication and Networking - TERMSjnoasj didsniafdsNo ratings yet
- Chapter 5Document52 pagesChapter 5Pratham SuhasiaNo ratings yet
- Transport LayerDocument8 pagesTransport LayerKrishna VamsiNo ratings yet
- Fundamentals To NetworkDocument14 pagesFundamentals To NetworkDinesh MathewNo ratings yet
- Networks: Network Protocols: Defines Rules and Conventions For Communication Between Network DevicesDocument5 pagesNetworks: Network Protocols: Defines Rules and Conventions For Communication Between Network DevicesSadia MunawarNo ratings yet
- DCN UNIT 1 To 5Document130 pagesDCN UNIT 1 To 5Amulya ReddyNo ratings yet
- IP Source RoutingDocument3 pagesIP Source RoutingVasit SinghNo ratings yet
- William Stallings Data and Computer CommunicationsDocument27 pagesWilliam Stallings Data and Computer Communicationspanimalar123No ratings yet
- Computer Networks (3150710) : Chapter 3: Transport Layer Weightage: 25%Document35 pagesComputer Networks (3150710) : Chapter 3: Transport Layer Weightage: 25%urmilNo ratings yet
- TCP IpDocument6 pagesTCP Ipkannanperu123No ratings yet
- Services Provided by The Transport LayerDocument16 pagesServices Provided by The Transport LayerCaptain AmericaNo ratings yet
- Computer Network-Transport LayerDocument19 pagesComputer Network-Transport LayerSheba ParimalaNo ratings yet
- Transport LayerDocument27 pagesTransport Layerkishanbharati2002No ratings yet
- Unit 3-1Document23 pagesUnit 3-1sanketmhetre018No ratings yet
- Cloud NetworkingDocument26 pagesCloud NetworkingHeliosNo ratings yet
- Submitted To: Submitted By: Mrs. Ruchi Nanda Diksha Mangal Kajal JainDocument13 pagesSubmitted To: Submitted By: Mrs. Ruchi Nanda Diksha Mangal Kajal Jainpooja guptaNo ratings yet
- CN-Mod4 Notes - DRVSDocument18 pagesCN-Mod4 Notes - DRVSNuthan RNo ratings yet
- Chapter 3Document60 pagesChapter 3Markib Singh AdawitahkNo ratings yet
- 962batransport Layer and UDPDocument7 pages962batransport Layer and UDPPranjalNo ratings yet
- Application Layer: TCP/IP LayersDocument5 pagesApplication Layer: TCP/IP LayersDARANo ratings yet
- Unit 5Document10 pagesUnit 5Dhanashri DevalapurkarNo ratings yet
- Module IV CNDocument34 pagesModule IV CNvishnu m jNo ratings yet
- Unit-5 ECE 3-2Document15 pagesUnit-5 ECE 3-2srinu vasNo ratings yet
- FALLSEM2023-24 ITA1006 TH VL2023240102674 2023-08-01 Reference-Material-IDocument32 pagesFALLSEM2023-24 ITA1006 TH VL2023240102674 2023-08-01 Reference-Material-IAnanya MachaniNo ratings yet
- Day16 TransportLayerDocument13 pagesDay16 TransportLayerAshu ChauhanNo ratings yet
- CN - Unit4.1 PDFDocument40 pagesCN - Unit4.1 PDFKanika TyagiNo ratings yet
- Transport Layer IssuesDocument19 pagesTransport Layer IssuesDarpan SharmaNo ratings yet
- CN UNIT-2 Transport Layer Protocols - UDP, TCPDocument34 pagesCN UNIT-2 Transport Layer Protocols - UDP, TCPKowsalya GNo ratings yet
- CN Unit 4Document25 pagesCN Unit 4dhosheka123No ratings yet
- Lesson 9: Protocols and Network StandardsDocument3 pagesLesson 9: Protocols and Network StandardsWinny Shiru MachiraNo ratings yet
- Transport Layer PDFDocument32 pagesTransport Layer PDFshankulNo ratings yet
- CCNA 3 Final Exam Answers v5.0 2015 100Document19 pagesCCNA 3 Final Exam Answers v5.0 2015 100ovidiu0702No ratings yet
- 3.2.2.4 Packet Tracer - Configuring TrunksDocument9 pages3.2.2.4 Packet Tracer - Configuring TrunksLibaniel Castrillon CarvajalNo ratings yet
- ONT LM241UW5 Datasheet - V1.2Document6 pagesONT LM241UW5 Datasheet - V1.2mnowarulalam2085No ratings yet
- CS6223: Distributed Systems: Distributed Time and Clock Synchronization (1) Physical TimeDocument34 pagesCS6223: Distributed Systems: Distributed Time and Clock Synchronization (1) Physical TimeMunish KharbNo ratings yet
- Sample Resume Fresher CCNA 1Document3 pagesSample Resume Fresher CCNA 1Amol Kore-Mali100% (2)
- OLT GPON 8 PuertosDocument3 pagesOLT GPON 8 PuertososgarsotoNo ratings yet
- Comandos IdirectDocument7 pagesComandos IdirectOscar MachadoNo ratings yet
- ACO 330 Homework 6Document2 pagesACO 330 Homework 6Malcolm WardNo ratings yet
- Xgs4600 Series: 28/48-Port Gbe L3 Managed Switch With 4 SFP+ UplinkDocument6 pagesXgs4600 Series: 28/48-Port Gbe L3 Managed Switch With 4 SFP+ UplinkWesley RuizNo ratings yet
- CCENT Certification All-In-One For Dummies: Cheat SheetDocument17 pagesCCENT Certification All-In-One For Dummies: Cheat SheetBayac Ramehr50% (2)
- Design NETWORK BASE SECURITY SURVEILLANCE SYSTEMDocument42 pagesDesign NETWORK BASE SECURITY SURVEILLANCE SYSTEMManuNo ratings yet
- B Implement MP BGP Control Plane v2Document32 pagesB Implement MP BGP Control Plane v2rstoikosNo ratings yet
- CSS TestDocument3 pagesCSS TestDanilo Cumpio100% (1)
- ZTE MF62 Virgin User GuideDocument18 pagesZTE MF62 Virgin User GuideFahriKudrihanNo ratings yet
- Network Access Control: Software and HarwareDocument2 pagesNetwork Access Control: Software and Harwareanurag_0290100% (1)
- DHCP Implementation Guide - 0.1Document18 pagesDHCP Implementation Guide - 0.1Manaf Al OqlahNo ratings yet
- GPRS Call Flow - v20021218Document36 pagesGPRS Call Flow - v20021218rookie.caozhongzeNo ratings yet
- Cisco NSO Transport SDN Function Pack Bundle User Guide Version 1 0 0 PDFDocument186 pagesCisco NSO Transport SDN Function Pack Bundle User Guide Version 1 0 0 PDFOuraNo ratings yet
- Network Attacks - A Deeper LookDocument35 pagesNetwork Attacks - A Deeper LookMd Zahid HossainNo ratings yet
- Network Topology & GNS3 LAB: David Rohleder Davro@ics - Muni.czDocument29 pagesNetwork Topology & GNS3 LAB: David Rohleder Davro@ics - Muni.czfaiza zafarNo ratings yet
- H3C WA6320 New Generation Access PointDocument14 pagesH3C WA6320 New Generation Access PointCarlos MartinezNo ratings yet
- Basic Storage ConceptsDocument31 pagesBasic Storage ConceptsChilambarasan Kaliyamoorthi100% (1)
- LaptopDocument4 pagesLaptopMuthu ChinnasaamyNo ratings yet
- Cwap-402 (2016) PDFDocument620 pagesCwap-402 (2016) PDFFunnyjohn007100% (3)
- BC - MTTMT-đã chuyển đổiDocument63 pagesBC - MTTMT-đã chuyển đổiHuong TruongNo ratings yet
- CCNA 1 Final v5.0 Exam Answers 2015 100Document50 pagesCCNA 1 Final v5.0 Exam Answers 2015 100ovidiu0702No ratings yet
- ASUS RT-AX82U Routeur Gaming Amazon - Co.uk Computers & AccessoriesDocument1 pageASUS RT-AX82U Routeur Gaming Amazon - Co.uk Computers & AccessoriesVladut MarianNo ratings yet
- Final AssignmentDocument71 pagesFinal AssignmentAmanDeep SainiNo ratings yet
- 1 s2.0 S2212420919310398 MainDocument34 pages1 s2.0 S2212420919310398 MainFish FriedNo ratings yet
- IMaster NCE-Campus V300R020C00 BrochureDocument8 pagesIMaster NCE-Campus V300R020C00 BrochureJosé JuárezNo ratings yet