Professional Documents
Culture Documents
19bcs2848 Exp 5 SWL
Uploaded by
19bcs2856Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
19bcs2848 Exp 5 SWL
Uploaded by
19bcs2856Copyright:
Available Formats
Course Name: Securing Window & Linux Lab Course Code: CSB-472
Experiment:2.1
Aim: To research the Various System Vulnerabilities for the target machine (Internet - access CVE database
of vulnerabilities)
Software Required: 1) Google to find CVE (at Mitre Corp.) 2) CVE database 3) Packet Storm Website
Description: A vulnerability in security refers to a weakness or opportunity in an information system that
cybercriminals can exploit and gain unauthorized access to a computer system. Vulnerabilities weaken
systems and open the door to malicious attacks. Vulnerabilities and risks differ in that vulnerabilities are
known weaknesses. They are the identified gaps that undermine the security efforts of an organization’s IT
systems. Risks, on the other hand, are potentials for loss or damage when a threat exploits a vulnerability. A
common equation for calculating it is Risk = Threat x Vulnerability x Consequence.
The Common Vulnerabilities and Exposures (CVE) system provides a reference-method for publicly known
information-security vulnerabilities and exposures. The National Cybersecurity FFRDC, operated by the Mitre
Corporation, maintains the system, with funding from the National Cyber Security Division of the United
States Department of Homeland Security.
The Security Content Automation Protocol uses CVE, and CVE IDs are listed on MITRE's system as well as
in the US National Vulnerability Database.
MITRE Corporation's documentation defines CVE Identifiers (also called "CVE names", "CVE numbers",
"CVE-IDs", and "CVEs") as unique, common identifiers for publicly known information-security
vulnerabilities in publicly released software packages. Historically, CVE identifiers had a status of "candidate"
("CAN-") and could then be promoted to entries ("CVE-"), however this practice was ended some time ago
and all identifiers are now assigned as CVEs. The assignment of a CVE number is not a guarantee that it will
become an official CVE entry (e.g. a CVE may be improperly assigned to an issue which is not a security
vulnerability, or which duplicates an existing entry).
CVEs are assigned by a CVE Numbering Authority (CNA);[3] there are three primary types of CVE number
assignments:
1.) The Mitre Corporation functions as Editor and Primary CNA
Name: Shubham Bharti UID: 19BCS2848
Course Name: Securing Window & Linux Lab Course Code: CSB-472
2.) Various CNAs assign CVE numbers for their own products (e.g. Microsoft, Oracle, HP, Red Hat, etc.)
3. ) A third-party coordinator such as CERT Coordination Center may assign CVE numbers for products
not covered by other CNAs
When investigating a vulnerability or potential vulnerability it helps to acquire a CVE number early on. CVE
numbers may not appear in the MITRE or NVD CVE databases for some time (days, weeks, months or
potentially years) due to issues that are embargoed (the CVE number has been assigned but the issue has not
been made public), or in cases where the entry is not researched and written up by MITRE due to resource
issues. The benefit of early CVE candidacy is that all future correspondence can refer to the CVE number.
CVEs are for software that has been publicly released; this can include betas and other pre-release versions if
they are widely used. Commercial software is included in the "publicly released" category, however custom-
built software that is not distributed would generally not be given a CVE. Additionally services (e.g. a Web-
based email provider) are not assigned CVEs for vulnerabilities found in the service (e.g. an XSS vulnerability)
unless the issue exists in an underlying software product that is publicly distribute.
Implementation/ Output:
1. Open a browser and go to CVE Website: cve.mitre.org.
2. Now click on the “Search CVE List” & add the Domain name of any website you want to check for the
vulnerabilities & submit.
Name: Shubham Bharti UID: 19BCS2848
Course Name: Securing Window & Linux Lab Course Code: CSB-472
3. Now click on
4. Then click on the “certificate is secure” to see the SSL certificate details
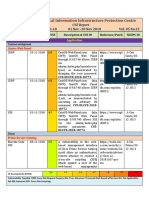
CVE-id Name ID/Description
CVE-2023-22680 Cuchd.in When using the RemoteIpFilter
with requests received from a
reverse proxy via HTTP that
include the X-Forwarded-Proto
header set to https, session cookies
created by Apache Tomcat 11.0.0-
M1 to 11.0.0.-M2, 10.1.0-M1 to
10.1.5, 9.0.0-M1 to 9.0.71 and
8.5.0 to 8.5.85 did not include the
secure attribute.
CVE-2023-22680 Myntra.com Auth. (admin+) Stored Cross-Site
Scripting (XSS) vulnerability in
Altanic No API Amazon Affiliate
plugin <= 4.2.2 versions.
Name: Shubham Bharti UID: 19BCS2848
Course Name: Securing Window & Linux Lab Course Code: CSB-472
CVE-2022-4369 Amazon.in The WP-Lister Lite for
https://hostedscan.com/scans
WordPress plugin before 2.4.4
does not sanitize and escapes a
parameter before outputting it
back in the page, leading to a
Reflected Cross-Site Scripting
which can be used against high-
privilege users such as admin.
CVE-2023-22895 hostedscan.com The bzip2 crate before 0.4.4 for
Rust allow attackers to cause a
denial of service via a large file
that triggers an integer overflow in
mem.rs. NOTE: this is unrelated to
the https://crates.io/crates/bzip2-rs
product
CVE-2023-28708 ajio.com When using the RemoteIpFilter
with requests received from a
reverse proxy via HTTP that
include the X-Forwarded-Proto
header set to https, session cookies
created by Apache Tomcat 11.0.0-
M1 to 11.0.0.-M2, 10.1.0-M1 to
10.1.5, 9.0.0-M1 to 9.0.71 and
8.5.0 to 8.5.85 did not include the
secure attribute. This could result
in the user agent transmitting the
session cookie over an insecure
channel.
Name: Shubham Bharti UID: 19BCS2848
Course Name: Securing Window & Linux Lab Course Code: CSB-472
OUTPUT:
Name: Shubham Bharti UID: 19BCS2848
Course Name: Securing Window & Linux Lab Course Code: CSB-472
Name: Shubham Bharti UID: 19BCS2848
You might also like
- VLab Demo - Using ASM For Web Vulnerabilities - V12.0.0.01Document21 pagesVLab Demo - Using ASM For Web Vulnerabilities - V12.0.0.01Marcos ValleNo ratings yet
- JWT HandbookDocument89 pagesJWT Handbookncarlsonf100% (4)
- Lab 3Document4 pagesLab 3Shiv PatelNo ratings yet
- National Critical Information Infrastructure Protection CentreDocument4 pagesNational Critical Information Infrastructure Protection CentreRavi SankarNo ratings yet
- 16 31 May21 CVEDocument268 pages16 31 May21 CVEAkshat SinghNo ratings yet
- PentestTools WebsiteScanner ReportDocument7 pagesPentestTools WebsiteScanner ReportMario Sernaque RumicheNo ratings yet
- Synacktiv Danfoss Storeview Multiple VulnerabilitiesDocument6 pagesSynacktiv Danfoss Storeview Multiple VulnerabilitieskepakkoNo ratings yet
- Lightspeed Cache Vulnerability PaperDocument14 pagesLightspeed Cache Vulnerability PaperMajedNo ratings yet
- Arnaldy 2020Document5 pagesArnaldy 2020rahul49cloudNo ratings yet
- JUL2023 CPU - Supply Chain Suite Patch Availability DocumentDocument8 pagesJUL2023 CPU - Supply Chain Suite Patch Availability DocumentNarsimulu AkulaNo ratings yet
- Hacking Module 11Document53 pagesHacking Module 11Chye HengNo ratings yet
- WCT - F0o7foDocument238 pagesWCT - F0o7fokamidikamalakarNo ratings yet
- Multiple VulnerabilitiesDocument4 pagesMultiple VulnerabilitiesJDaemon7No ratings yet
- In The Wake of Solarwinds CompromiseDocument10 pagesIn The Wake of Solarwinds Compromisealfred.x.andrewsNo ratings yet
- AnalyticsDocument9 pagesAnalyticszpyq123No ratings yet
- Research Blogs FeedDocument22 pagesResearch Blogs FeedHéctor Javier HerreraNo ratings yet
- Active Page ServerDocument18 pagesActive Page ServerZain Alabeeden AlarejiNo ratings yet
- Pentest Report - Casebox 1Document35 pagesPentest Report - Casebox 1SheloqNo ratings yet
- Owning Big Brother: (Or How To Crack Into Axis IP Cameras)Document18 pagesOwning Big Brother: (Or How To Crack Into Axis IP Cameras)mohantamilNo ratings yet
- (Divi Report) Daptatech RepDocument5 pages(Divi Report) Daptatech RepcarlosNo ratings yet
- Website Vulnerability Scanner Report (Light)Document4 pagesWebsite Vulnerability Scanner Report (Light)MasBaNo ratings yet
- Vulnerabilities June 30, 2020Document21 pagesVulnerabilities June 30, 2020Himel ArhamNo ratings yet
- IamNobody - WreathDocument30 pagesIamNobody - WreathAstral XerveNo ratings yet
- Securing Kubernetes ChecklistDocument10 pagesSecuring Kubernetes ChecklistSandro MeloNo ratings yet
- Cryptography in The Web The Case of Cryptographic Design Flaws inDocument9 pagesCryptography in The Web The Case of Cryptographic Design Flaws inSaurav JajodiaNo ratings yet
- OKWSDocument14 pagesOKWSor2jdi8lNo ratings yet
- A Survey of Web Security: Aviel D. Rubin Daniel E. Geer JRDocument8 pagesA Survey of Web Security: Aviel D. Rubin Daniel E. Geer JRNirmal Raj DeivasigamaniNo ratings yet
- File and Resource AttacksDocument61 pagesFile and Resource AttacksAbdul Mateen UkkundNo ratings yet
- XML External Entity: Via Mp3 File Upload On WordpressDocument14 pagesXML External Entity: Via Mp3 File Upload On WordpressNafiz NahiyanNo ratings yet
- Scan Report PDFDocument6 pagesScan Report PDFJulian MartinezNo ratings yet
- Patch Auditing in Infrastructure As A Service Clouds: Lionel Litty David LieDocument11 pagesPatch Auditing in Infrastructure As A Service Clouds: Lionel Litty David LiepulaksayNo ratings yet
- Msbs ControlsDocument21 pagesMsbs Controlssobi_zubi0No ratings yet
- IBM Final Case StudyDocument6 pagesIBM Final Case StudyRonnisNo ratings yet
- Using Declarative Information in Web Application Frameworks To Improve SecurityDocument185 pagesUsing Declarative Information in Web Application Frameworks To Improve SecurityKevin DenverNo ratings yet
- Github Actions CICD PipelineDocument13 pagesGithub Actions CICD PipelineVamsi ChowdaryNo ratings yet
- An Exhaustive Survey On Security Concerns and Solutions at Different Components of VirtualizationDocument38 pagesAn Exhaustive Survey On Security Concerns and Solutions at Different Components of Virtualizationjaime_parada3097No ratings yet
- Unit VDocument85 pagesUnit VRaghavendra Vithal GoudNo ratings yet
- Building Secure High-Performance Web Services With OKWS: Maxwell Krohn, MIT Computer Science and AI LaboratoryDocument14 pagesBuilding Secure High-Performance Web Services With OKWS: Maxwell Krohn, MIT Computer Science and AI LaboratoryalkalacidNo ratings yet
- Web Browser SecurityDocument16 pagesWeb Browser Securityعبدالرحيم اودين0% (1)
- Azure - Windows Server - Host Scan - 2024 Jan q5trvkDocument410 pagesAzure - Windows Server - Host Scan - 2024 Jan q5trvkeshensanjula2002No ratings yet
- Udemy Dump 2Document111 pagesUdemy Dump 2Gani RKNo ratings yet
- Website Vulnerability Scanner Report (Light)Document6 pagesWebsite Vulnerability Scanner Report (Light)alex681219No ratings yet
- Vuln ScanDocument12 pagesVuln ScanBrijendra Pratap SinghNo ratings yet
- Ceh Chap8 QuizletDocument2 pagesCeh Chap8 QuizletlynnverbNo ratings yet
- Virtualization Security Issues and Mitigations in Cloud Computing IcciiDocument13 pagesVirtualization Security Issues and Mitigations in Cloud Computing IcciidfaillaNo ratings yet
- Website Vulnerability Scanner Sample Report OptimizedDocument11 pagesWebsite Vulnerability Scanner Sample Report OptimizedPauloNo ratings yet
- Technical White Paper On Web Application FirewallDocument14 pagesTechnical White Paper On Web Application FirewallAla EddineNo ratings yet
- Browser Security Lessons From Google Chrome GoogleDocument9 pagesBrowser Security Lessons From Google Chrome GoogleVaishnaviNo ratings yet
- Id Vul Id Description LinkDocument3 pagesId Vul Id Description LinkIytzaz BarkatNo ratings yet
- WAF / ModSec + OWASP CRSDocument61 pagesWAF / ModSec + OWASP CRSAdzmely MansorNo ratings yet
- PEN-200 Lab ReportDocument8 pagesPEN-200 Lab ReportSilver UchihaNo ratings yet
- Ai Web Report 1 1Document25 pagesAi Web Report 1 1Suraj TheekshanaNo ratings yet
- PENTEST-Introduction To Web PentestDocument10 pagesPENTEST-Introduction To Web Pentestvlatko.lazarevskiNo ratings yet
- Top Ten: Web Hacking TechniquesDocument49 pagesTop Ten: Web Hacking Techniquesjavier cardenasNo ratings yet
- Vmware & Security: Vmsafe: Bob Van Der Werf Sr. Systems Engineer VmwareDocument15 pagesVmware & Security: Vmsafe: Bob Van Der Werf Sr. Systems Engineer VmwaresusantsahaniNo ratings yet
- Surplus M2 UAT New - W2 - Report - 2023 07 15 - 17 36 31Document3 pagesSurplus M2 UAT New - W2 - Report - 2023 07 15 - 17 36 31ashok_abclNo ratings yet
- Vol 6 Issue 5 M 07 PDFDocument6 pagesVol 6 Issue 5 M 07 PDFMynutsa SmellyNo ratings yet
- Websecenter-Web Security For The EnterpriseDocument12 pagesWebsecenter-Web Security For The EnterpriseitandroidNo ratings yet
- Confining The Apache Web Server With Security-Enhanced LinuxDocument12 pagesConfining The Apache Web Server With Security-Enhanced LinuxI srcNo ratings yet
- ETHICAL HACKING GUIDE-Part 3: Comprehensive Guide to Ethical Hacking worldFrom EverandETHICAL HACKING GUIDE-Part 3: Comprehensive Guide to Ethical Hacking worldNo ratings yet
- Python Based Recognition of SignDocument10 pagesPython Based Recognition of Sign19bcs2856No ratings yet
- SW&L 19bcs2848 Exp7Document5 pagesSW&L 19bcs2848 Exp719bcs2856No ratings yet
- Ex 7Document4 pagesEx 719bcs2856No ratings yet
- 19bcs2848 SWL 1.4Document5 pages19bcs2848 SWL 1.419bcs2856No ratings yet
- 19bcs2848 RTS-1.3Document4 pages19bcs2848 RTS-1.319bcs2856No ratings yet
- Research Proposal Report (Ragama)Document29 pagesResearch Proposal Report (Ragama)Antony Njure MathengeNo ratings yet
- Открыть Httpspark University.s3.Amazonaws.comstanford Cryptoslides04 Using Block v2 Annotated.pdf 4Document54 pagesОткрыть Httpspark University.s3.Amazonaws.comstanford Cryptoslides04 Using Block v2 Annotated.pdf 4Ярослав КсенофонтовNo ratings yet
- Lecture 5Document10 pagesLecture 5AHMED DARAJNo ratings yet
- Complaint DetailDocument2 pagesComplaint DetailShankar PolakeNo ratings yet
- The Concept of "At Work"Document17 pagesThe Concept of "At Work"Gerel Ann Lapatar TranquilleroNo ratings yet
- 2nd Year Cyber Security NotesDocument3 pages2nd Year Cyber Security NotespriyankaNo ratings yet
- IZat Nayab Raj PDFDocument5 pagesIZat Nayab Raj PDFNaziaNo ratings yet
- Report Study On Anti VirusDocument87 pagesReport Study On Anti VirusJainam GargNo ratings yet
- Internet Security Report - Q4Document37 pagesInternet Security Report - Q4ravin.jugdav678No ratings yet
- Cyber TortDocument21 pagesCyber TortAnonymous nkGJvo3nGJ100% (1)
- A Survey of Man in The Middle AttacksDocument26 pagesA Survey of Man in The Middle AttacksAsoUmeNo ratings yet
- Social Media and Its Effects On Society 2469 9837 1000166Document1 pageSocial Media and Its Effects On Society 2469 9837 1000166Rynjeff Lui-PioNo ratings yet
- Pranil - CSA - Lab Assignment 3Document4 pagesPranil - CSA - Lab Assignment 3Pranil ChoudhariNo ratings yet
- Chapter 17 SlidesDocument19 pagesChapter 17 SlidesLipsa SahooNo ratings yet
- Email Security Appliance Admin Guide PDFDocument1,164 pagesEmail Security Appliance Admin Guide PDFDeepankar MitraNo ratings yet
- Q13-Cyber Security Threats, Vulnerabilities and AttacksDocument3 pagesQ13-Cyber Security Threats, Vulnerabilities and AttacksDzenrhe ParanNo ratings yet
- CV - Muhammad Rehan AtharDocument2 pagesCV - Muhammad Rehan AtharSachal SarmastNo ratings yet
- Unit-3 Digital Forensics MCQ Bank - HMGDocument7 pagesUnit-3 Digital Forensics MCQ Bank - HMG36-TYCM-I-Anushka Naik0% (1)
- CNS Unit IV PDFDocument80 pagesCNS Unit IV PDFKartheeNo ratings yet
- CHAPTER 10 Audit in CIS EnvironmentDocument56 pagesCHAPTER 10 Audit in CIS EnvironmentJenalyn OreñaNo ratings yet
- UntitledDocument3 pagesUntitledDarius A. LopezNo ratings yet
- Hybrid Encryption of Cipher Text With Verifiable Delegation Using Cloud ComputingDocument25 pagesHybrid Encryption of Cipher Text With Verifiable Delegation Using Cloud ComputingahimasNo ratings yet
- Eset Nod 32 LicensesDocument2 pagesEset Nod 32 LicensesMinhas ArshadNo ratings yet
- PG Certification in Cyber Security and Ethical HackingDocument13 pagesPG Certification in Cyber Security and Ethical HackingSap BasisNo ratings yet
- Computer Security GoalsDocument72 pagesComputer Security GoalsAnkur Agrawal100% (2)
- AhnLab Hackshield Brochure PDFDocument4 pagesAhnLab Hackshield Brochure PDFsyais7No ratings yet
- Importance of Network SecurityDocument2 pagesImportance of Network SecurityLuck JayNo ratings yet
- One Time Password Authentication Integration Approach: IndroductionDocument2 pagesOne Time Password Authentication Integration Approach: Indroductionpuneet mishraNo ratings yet
- Cloud Tech Associate Advanced SecurityDocument163 pagesCloud Tech Associate Advanced SecurityJuntos PodCastNo ratings yet