Professional Documents
Culture Documents
CCN Seminar: Abdus Sarif Ahmed 1RV07EC002
Uploaded by
Sarif Ahmed0 ratings0% found this document useful (0 votes)
14 views14 pagesThis document discusses Ethernet and the MAC sublayer protocol. It describes the DIX and IEEE 802.3 frame formats, including fields like preamble, destination/source addresses, type/length fields, and checksum. It also explains the minimum frame length requirement and binary exponential backoff algorithm used for collision avoidance.
Original Description:
Original Title
CCN Seminar
Copyright
© Attribution Non-Commercial (BY-NC)
Available Formats
PPTX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis document discusses Ethernet and the MAC sublayer protocol. It describes the DIX and IEEE 802.3 frame formats, including fields like preamble, destination/source addresses, type/length fields, and checksum. It also explains the minimum frame length requirement and binary exponential backoff algorithm used for collision avoidance.
Copyright:
Attribution Non-Commercial (BY-NC)
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
14 views14 pagesCCN Seminar: Abdus Sarif Ahmed 1RV07EC002
Uploaded by
Sarif AhmedThis document discusses Ethernet and the MAC sublayer protocol. It describes the DIX and IEEE 802.3 frame formats, including fields like preamble, destination/source addresses, type/length fields, and checksum. It also explains the minimum frame length requirement and binary exponential backoff algorithm used for collision avoidance.
Copyright:
Attribution Non-Commercial (BY-NC)
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
You are on page 1of 14
CCN Seminar
ABDUS SARIF AHMED
1RV07EC002
Ethernet MAC Sublayer Protocol
• Ethernet is mainly a protocol that controls the
way data is transmitted over a local area network.
• IEEE 802.3 standard is commonly referred to as
ethernet.
• Because of differences in packet formation
and physical construction associated with each
standard,the networking community currently
follows the original Ethernet standard
implementation by the DIX suffix .
Ethernet MAC Sublayer Protocol
Frame Formats (a)DIX Ethernet
(b)IEEE 802.3
Ethernet MAC Sublayer Protocol
DIX frame format
• The frame starts with Preamble of 8 bytes
pattern being 10101010.Manchester encoding is
done on this pattern for synchronisation
purpose.
• Destination and source addresses on this frame
is of 6 bytes each.The high order bit in the
destination address is 0 for ordinary addresses
and 1 for group addresses(multicast).
• The destination address consisting of all 1 bits is
reserved for broadcast.
Ethernet MAC Sublayer Protocol
• The addresses can also be local and global.
• Local addresses are assigned by each network
administrator with no significance outside the
local network.
• Global addresses are assigned centrally by
IEEE to ensure that no two stations have the
same global address.
• The type field tells the receiver what to do
with the frame.
• The data field can be from 0 to 1500 bytes.
Ethernet MAC Sub Layer Protocol
• When a transceiver detects a collision,it
truncates the current frame and so stray bits
appear on the cable all the time.
• To distinguish valid frames from garbage,the
frames must be atleast 64 bytes long from
destination address to checksum including
both.
• The pad field is used to fill out the frame to
minimum size when data portion is less than
46 bytes.
Ethernet MAC Sub Layer Protocol
•Minimum frame length
Ethernet and MAC sublayer protocol
• Important reason for having minimum frame length is
to prevent a station from completing the
transmission of a short frame before the first bit has
even reached the far end of the cable where it may
collide with another frame.
• When a station(say A) is transmitting frame to
another station(say B) and if there is a collision
station B aborts its transmission and generates a 48
bit noise burst to warn all other satations.
• At about time 2τ the sender sees the noise burst and
aborts its transmission too and waits for a random
time before trying again.
Ethernet and MAC sublayer protocol
• To prevent wrong interpretation by the sender all
frames must take more than 2τ time to reach the
receiver.
• As the network speed goes up the minimum
frame length must go up or maximum cable
length must come down proportionately.
• The checksum field is 32 bit and is required to
detect the errors.The most common checksum
algorithm is cyclic redundancy check(CRC).
Ethernet and MAC sublayer protocol
• When IEEE standardised Ethernet,the
committee made two changes to the DIX
format:
(1)Preamble field is reduced to 7 bytes and
the last byte is used for a Start of Frame
delimiter.
(2)The type field is changed into a Length
field and the operation to be done on the frame
is given by a small header to the data portion.
Binary Exponential Backoff Algorithm
• Proper randomization is done when a collision occurs
using binary exponential backoff algorithm.
• After a collision time is divided into discrete slots each
length being equal to the worst case round trip
propagation time(2τ).
• After first collision,each station waits either 0 or 1 slot
times before trying again.If after collisions, the two
stations take the same random number, they will
collide again.
• In general after i collisions,a random number between
0 and 2i -1 is chosen by each station and that number
of slots is skipped.
Binary Exponential Backoff Algorithm
• After 10 collisions the randomization interval is
frozen at a maximum of 1023 slots and after 16
collisions the controller reports failure.
• Binary exponential backoff algorithm is chosen to
dyanamically adapt to the number of stations
trying to send.
• If the randomization interval for all collisions is
made 1023 then there is very less chance of
stations colliding for second time but it
introduces delay.
Binary Exponential Backoff Algorithm
• If each station always delayed for either 0 or 1
slot,then if n sations try to send once,they would
collide over and over again until (n-1) of them
picked 1 and the remaining station picked 0.
• By having the randomization interval grow
exponentially as more and more consecutive
collisions occur,the algorithm ensures a low
delay when only few stations collide and if many
stations collide, the collision is resolved in a
reasonable interval.
Binary Exponential Backoff Algorithm
• Since the mere absense of collisions does not
guarantee that bits were not garbled by noise
spikes on the cable, for reliable communication
the destination must verify the checksum and
send back an acknowledgement frame to the
sender.
• The acknowlegement frame would have to fight
for channel time just like the data frame
You might also like
- CCNA Interview Questions You'll Most Likely Be Asked: Job Interview Questions SeriesFrom EverandCCNA Interview Questions You'll Most Likely Be Asked: Job Interview Questions SeriesNo ratings yet
- T8 EthernetDocument51 pagesT8 Ethernetutkarsh.shrivastav202002No ratings yet
- Ethernet: - IEEE-Institute of Electrical and ElectronicsDocument27 pagesEthernet: - IEEE-Institute of Electrical and ElectronicsRekha V RNo ratings yet
- 5 EthernetDocument40 pages5 EthernetSourava Kumar BeheraNo ratings yet
- Ieee Standard 802 For Lans and MansDocument27 pagesIeee Standard 802 For Lans and MansSulthana ShajiNo ratings yet
- CN Mod2Document61 pagesCN Mod2Vignesh H VNo ratings yet
- Ethernet: Oakton Community College CIS 238Document16 pagesEthernet: Oakton Community College CIS 238Gangadhar MamadapurNo ratings yet
- CCNAv3.3 108Document27 pagesCCNAv3.3 108Tung HoangNo ratings yet
- Ethernet & IEEE Standards: Lecture-9Document47 pagesEthernet & IEEE Standards: Lecture-9Abhiram DonNo ratings yet
- Difference Between Ethernet 2 Frame and 802.3 FrameDocument2 pagesDifference Between Ethernet 2 Frame and 802.3 FrameRajat SethNo ratings yet
- Distributed Queue Dual Bus: ELEC3030 (EL336) Computer NetworksDocument12 pagesDistributed Queue Dual Bus: ELEC3030 (EL336) Computer NetworksAshish6300No ratings yet
- Bluetooth Wireless LAN TechnologyDocument43 pagesBluetooth Wireless LAN TechnologyAhmad F. MahmoodNo ratings yet
- CISCO CCNA1 Chapter 9 Ethiopian Digital LibraryDocument4 pagesCISCO CCNA1 Chapter 9 Ethiopian Digital LibraryOz GNo ratings yet
- Computer Networks - Shared Media AccessDocument115 pagesComputer Networks - Shared Media AccessAmir QayyumNo ratings yet
- Unit 5Document145 pagesUnit 5sdhNo ratings yet
- 1.A. Sonet Frame 1.B. Atm Cell 1.C. Ip Packet 1.D. Fiber Channel FrameDocument17 pages1.A. Sonet Frame 1.B. Atm Cell 1.C. Ip Packet 1.D. Fiber Channel Frameరాహుల్ దేవ్No ratings yet
- Ethernet: An Introduction: Fast Ethernet Operates 10 Times Faster, I.e., at 100 Mbps. Recently, There HasDocument4 pagesEthernet: An Introduction: Fast Ethernet Operates 10 Times Faster, I.e., at 100 Mbps. Recently, There Hasaksagar22No ratings yet
- CCNA1 M8 Ethernet SwitchingDocument14 pagesCCNA1 M8 Ethernet SwitchingAdriana StoianNo ratings yet
- 2076 Ashwin: Question-Set SolutionDocument24 pages2076 Ashwin: Question-Set SolutionSaurav NeupaneNo ratings yet
- Computer Networks (CS425) : IEEE 802.3 and EthernetDocument3 pagesComputer Networks (CS425) : IEEE 802.3 and EthernetAnish VeettiyankalNo ratings yet
- Unit II Media Access Control Ethernet: Presentation By: Kaythry P. Assistant Professor, ECE SSN College of EngineeringDocument47 pagesUnit II Media Access Control Ethernet: Presentation By: Kaythry P. Assistant Professor, ECE SSN College of Engineeringdolly100% (1)
- Chapter 5 - Local Area Network TechnologyDocument35 pagesChapter 5 - Local Area Network Technologyfnata AiNo ratings yet
- Network+ Important StuffDocument19 pagesNetwork+ Important StuffribsterNo ratings yet
- Channel Access MethodsDocument27 pagesChannel Access MethodsmandviNo ratings yet
- Ethernet CNDocument23 pagesEthernet CNgayathripanchumarthi30No ratings yet
- 10 GbeDocument181 pages10 Gbealeksandar7No ratings yet
- IEEE11Document52 pagesIEEE11api-3703205No ratings yet
- CCNA Exploration 1 Module 9Document2 pagesCCNA Exploration 1 Module 9shagydoo89100% (1)
- CCNAv3.3 106Document58 pagesCCNAv3.3 106Tung HoangNo ratings yet
- CCNA Exploration 1 Module 9 Exam Answers Version 40Document4 pagesCCNA Exploration 1 Module 9 Exam Answers Version 40ivestshisolNo ratings yet
- Mod 2 - 802.3Document12 pagesMod 2 - 802.3Scaria AlexNo ratings yet
- Why Is Medium Access Control Needed?Document11 pagesWhy Is Medium Access Control Needed?RevathimuthusamyNo ratings yet
- BluetoothDocument28 pagesBluetoothMona ReddyNo ratings yet
- Fast Ethernet and Gigabit EthernetDocument35 pagesFast Ethernet and Gigabit EthernetWaqar AsmatNo ratings yet
- Chapter-5 Local Area NetworkDocument39 pagesChapter-5 Local Area NetworkAarti SavaliyaNo ratings yet
- Networks NotesDocument5 pagesNetworks NotesSukhwinderNo ratings yet
- Chapter Five: Local Area Networking TechnologyDocument38 pagesChapter Five: Local Area Networking TechnologyAbera BrhanuNo ratings yet
- Point-To-Point vs. Shared Channel Communication in LansDocument22 pagesPoint-To-Point vs. Shared Channel Communication in LansCarlos RiveraNo ratings yet
- Lec 03 Data Link ControlDocument22 pagesLec 03 Data Link Controlmi hNo ratings yet
- 3 Underlying TechnologiesDocument49 pages3 Underlying TechnologiesTutun JuhanaNo ratings yet
- 5 Ethernet 2Document38 pages5 Ethernet 2insaanNo ratings yet
- Ethernet: Mrs.R.Shanthi Prabha M.SC., M.Phil., Assistant Professor, DEPARTMENT OF Computer ScienceDocument31 pagesEthernet: Mrs.R.Shanthi Prabha M.SC., M.Phil., Assistant Professor, DEPARTMENT OF Computer Scienceshanthi prabha100% (1)
- Ethernet (802.3) : Sep. 16. 2005 CS 440 Lecture Notes 1Document14 pagesEthernet (802.3) : Sep. 16. 2005 CS 440 Lecture Notes 1james smithNo ratings yet
- A. PhysicalDocument17 pagesA. PhysicalYash KuncolienkerNo ratings yet
- Chapter 4Document8 pagesChapter 4Ahsen KamalNo ratings yet
- Wired Lans and Ethernet: 01204325: Data Communication and Computer NetworksDocument53 pagesWired Lans and Ethernet: 01204325: Data Communication and Computer NetworksshaniraNo ratings yet
- Examenes Cisco Modulo 9Document5 pagesExamenes Cisco Modulo 9kethylqNo ratings yet
- Part 6 - Local Area Network TechnologyDocument35 pagesPart 6 - Local Area Network TechnologyRoberaNo ratings yet
- 12 Ethernet SlidesDocument17 pages12 Ethernet SlidesDung ĐặngNo ratings yet
- EthernetDocument13 pagesEthernetAbhishek gargNo ratings yet
- 1.1 EthernetDocument55 pages1.1 Ethernetag_krishNo ratings yet
- Ccna Exploration 1 Final Exam AnswersDocument10 pagesCcna Exploration 1 Final Exam AnswersAbhishek KunalNo ratings yet
- 4b Ethernet - Medium Access Control SublayerDocument61 pages4b Ethernet - Medium Access Control SublayerThamizh VendhanNo ratings yet
- FM Tranciever AppsDocument7 pagesFM Tranciever Appsinsomnium86No ratings yet
- Cs6551 Computer Networks: Unit - IiDocument86 pagesCs6551 Computer Networks: Unit - IiP.Veera LakshmiNo ratings yet
- Unit-2 ANP MSDocument69 pagesUnit-2 ANP MSKeep learningNo ratings yet
- Switching ConceptsDocument95 pagesSwitching ConceptspathakneelNo ratings yet
- Intel Annual Report 2021: Form 10-K (NASDAQ:INTC)Document10 pagesIntel Annual Report 2021: Form 10-K (NASDAQ:INTC)WigglepikeNo ratings yet
- Raymond RevillaDocument4 pagesRaymond RevillaKaguraNo ratings yet
- Applicatin Letter: Thank You in Advance Sincerely Yours Sign - Aimiro Ashenafi DechaDocument4 pagesApplicatin Letter: Thank You in Advance Sincerely Yours Sign - Aimiro Ashenafi DechaAlemNo ratings yet
- Report On VHDL ProjectDocument47 pagesReport On VHDL ProjectVandana JainNo ratings yet
- First Floor Evacuation PlanDocument1 pageFirst Floor Evacuation PlanModular Design TeamNo ratings yet
- NTang - Kilog Lite 2015 - 13 12 16Document29 pagesNTang - Kilog Lite 2015 - 13 12 16Kazi AlimNo ratings yet
- Idt AssignmentDocument11 pagesIdt AssignmentMohammed AfnanNo ratings yet
- Electrical Engineering Fundamentals - V. Del Toro PDFDocument62 pagesElectrical Engineering Fundamentals - V. Del Toro PDFRawat Heera21% (14)
- BERT SlidesDocument62 pagesBERT Slidessshahid183No ratings yet
- ME PED-Scheme & Syllabus 2018Document21 pagesME PED-Scheme & Syllabus 2018Angamuthu AnanthNo ratings yet
- DM LogDocument192 pagesDM LogJasmine HodousNo ratings yet
- Lesson 1: Classification of ComputerDocument11 pagesLesson 1: Classification of ComputerLuigiNo ratings yet
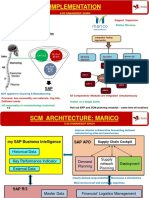
- S-55 Implementation RamandeepMarico SCMDocument2 pagesS-55 Implementation RamandeepMarico SCMSandeep KhatriNo ratings yet
- 8051mc Notes PDFDocument49 pages8051mc Notes PDFtinisusan100% (1)
- Neni Kurnia Andrianingsih - Submit Jurnal STAK 2023 (Bhs Inggris)Document23 pagesNeni Kurnia Andrianingsih - Submit Jurnal STAK 2023 (Bhs Inggris)novan arifulNo ratings yet
- Considering Jakarta Smart City, When Technology Responds To Community NeedsDocument2 pagesConsidering Jakarta Smart City, When Technology Responds To Community NeedsNafis ZamanNo ratings yet
- DeviceDocument6 pagesDeviceSurinder Pal SinghNo ratings yet
- Stock Price Prediction Using Deep Learning Algorithm and Its Comparison With Machine Learning AlgorithmsDocument11 pagesStock Price Prediction Using Deep Learning Algorithm and Its Comparison With Machine Learning AlgorithmsnotkurusboyNo ratings yet
- Four Metaphors We Need To Understand Assessment: Robert J. MislevyDocument36 pagesFour Metaphors We Need To Understand Assessment: Robert J. MislevyErven Jay EscobilloNo ratings yet
- AX Retail-Functional-80638-Material PDFDocument184 pagesAX Retail-Functional-80638-Material PDFDrissa SessoumaNo ratings yet
- Aseprite Quick Reference - Cheat SheetDocument1 pageAseprite Quick Reference - Cheat SheetMarito Barakus0% (1)
- Section 7: OBJECTIVES: at The End of The Section, The Student Is Expected To Be Able ToDocument8 pagesSection 7: OBJECTIVES: at The End of The Section, The Student Is Expected To Be Able ToYT PremoneNo ratings yet
- Adjustable Auto On Off Delay Timer Circuit Using IC555Document10 pagesAdjustable Auto On Off Delay Timer Circuit Using IC5551062221903No ratings yet
- RHEL 8.3 - Deploying Red Hat Enterprise Linux 8 On Public Cloud PlatformsDocument102 pagesRHEL 8.3 - Deploying Red Hat Enterprise Linux 8 On Public Cloud PlatformsPrernaNo ratings yet
- Mass Stream D 6300 960067Document6 pagesMass Stream D 6300 960067bau.bau.bau.bauuNo ratings yet
- 10E-5 Status Signals XLRTEH4300G033850Document1 page10E-5 Status Signals XLRTEH4300G033850Miller Andres ArocaNo ratings yet
- Pre Upgrade COP 00029 SGN ReadmeDocument5 pagesPre Upgrade COP 00029 SGN ReadmeFlavio AlonsoNo ratings yet
- Cloud Phone: September 2020Document4 pagesCloud Phone: September 2020AswiniieNo ratings yet
- PED 121: Technology For Teaching & Learning 2: Course ModuleDocument53 pagesPED 121: Technology For Teaching & Learning 2: Course Modulecloud beaumont100% (5)
- SWAT 3 - Tactical Game of The Year Edition - Manual - PCDocument95 pagesSWAT 3 - Tactical Game of The Year Edition - Manual - PCAnonymous utXYfMAXNo ratings yet