0% found this document useful (0 votes)
727 views70 pagesOSI Model: Data Link & Physical Layers
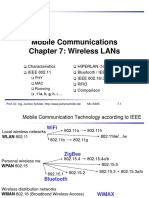
This document provides an overview of the network interface layer and data link layer of the OSI model. It discusses the functions of the physical and data link layers, including framing, synchronization, error control, flow control, and reliable delivery. It also describes popular data link layer protocol implementations, specifically Ethernet, Wi-Fi, and PPP. Common physical layer encoding and data link layer media access control, error control, flow control, and framing techniques used in Ethernet and Wi-Fi are also examined.
Uploaded by
kularatnCopyright
© Attribution Non-Commercial (BY-NC)
We take content rights seriously. If you suspect this is your content, claim it here.
Available Formats
Download as PPTX, PDF, TXT or read online on Scribd
0% found this document useful (0 votes)
727 views70 pagesOSI Model: Data Link & Physical Layers
This document provides an overview of the network interface layer and data link layer of the OSI model. It discusses the functions of the physical and data link layers, including framing, synchronization, error control, flow control, and reliable delivery. It also describes popular data link layer protocol implementations, specifically Ethernet, Wi-Fi, and PPP. Common physical layer encoding and data link layer media access control, error control, flow control, and framing techniques used in Ethernet and Wi-Fi are also examined.
Uploaded by
kularatnCopyright
© Attribution Non-Commercial (BY-NC)
We take content rights seriously. If you suspect this is your content, claim it here.
Available Formats
Download as PPTX, PDF, TXT or read online on Scribd