Professional Documents
Culture Documents
Unit 2 Computer Security Threats and Protections
Uploaded by
Afraa7 AnjumOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Unit 2 Computer Security Threats and Protections
Uploaded by
Afraa7 AnjumCopyright:
Available Formats
Unit 2
Computer Security Threats
Miss Afraah Anjum
Topics Of Today's
Discussion
Basics Consequences
Threats
Of Of
that can
Computer Ignoring Your
Harm Your Computer
Security Computer Security
How Do Bad Guys How To Protect
Compromise Your Computer Security Your
Computer Actions Computers
Security
Miss Afraah Anjum
Computer Security
Basics
• What is Computer Security?
• Computer Security is the protection of computing systems and the
data that they store or access.
• Very little in computing is inherently secure, you must protect
yourself!
• Software cannot protect itself
• Networks can be protected better than software
Miss Afraah Anjum
Computer Security
Basics
Primary Reasons To Secure Your Computer
To prevent theft of or damage to the
hardware
To prevent theft of or damage to information
To prevent disruption of service
Photo credit: perspec_photo88 / Foter / CC BY-SA
/
https://www.flickr.com/photos/111692634@N04/11407095883
Miss Afraah Anjum
Computer Security
Basics
Key Areas Of Concern of Computer Security
• Confidentiality - Only authorized users can access the data resources and
information.
• Integrity - Only authorized users should be able to modify the data when
needed.
• Availability - Data should be available to users when needed.
• Authentication - The computer system should be able to verify the identity of
a
user.
Miss Afraah Anjum
Consequences Of
Ignoring Computer
Security
Miss Afraah Anjum
Consequences Of
Ignoring Computer
Security
Loss Of Confidential Data
Loss In Productivity
Identity Theft
Compromised Data Integrity
Unavailability Of Access To Data Or Computer
Network
Lawsuits & Judicial Actions
Termination Of Employment
Miss Afraah Anjum
Types Of
Computer
Security Threats
Miss Afraah Anjum
Types Of Computer Security
Threats
Interruption
• An asset of the system becomes lost, unavailable, or
unusable
• Attack on availability
• Destruction of
Interruption
hardware
• Cutting of a communication
line
• Disabling the file management
system
A
B
Miss Afraah Anjum
Types Of Computer Security
Threats
Interception
• An unauthorized party gains access to an
asset
• Attack on confidentiality
• Wiretapping to capture data in a
Interception
network
• Illicit copying of files or
programs
A B
Miss Afraah Anjum
Types Of Computer Security
Threats
Modification
• An unauthorized party not only gains access but tampers with an
asset
• Attack on integrity
• Changing values in a data
Modification
file
• Altering a program so that it performs
differently
• Modifying the content of messages
being A B
transmitted in a network
C
Miss Afraah Anjum
Types Of Computer Security
Threats
Fabrication
An unauthorized party inserts counterfeit objects into the
system
Attack on authenticity
Insertion of spurious messages in a
Fabrication
network
Addition of records to a
file
A B
Miss Afraah Anjum
Types Of Computer Security
Threats
Hardware
• Threats include accidental and
deliberate
damage
Software
• Threats include deletion, alteration,
& damage
• Backups of the most recent versions
can maintain high availability
Photo credit: The Preiser Project / Foter / CC BY
https://www.flickr.com/photos/thepreiserproject/12102280105/
Miss Afraah Anjum
Types Of Computer Security
Threats
Data
• Involves files
• Security concerns for availability, secrecy, and integrity
• Statistical analysis can lead to determination of individual
in
formation which threatens privacy
Miss Afraah Anjum
How Do Bad Guys
Compromise Your
Computer
Security
Miss Afraah Anjum
How Do Bad Guys Compromise Your
Computer Security
1. Social Engineering
Social engineering is a non-technical method of intrusion hackers
use that relies heavily on human interaction and often involves
tricking people into breaking normal security procedures.
Types Of Social Engineering
• Baiting
• Phishing
• Pretexting
Photo credit: Don Hankins / Foter / CC BY
https://www.flickr.com/photos/23905174@N00/1594411528/
Miss Afraah Anjum
How Do Bad Guys Compromise Your
Computer Security
2.Reverse Social Engineering Attack
In this kind of cyberattack, the attacker convinces a
user
that they have a problem and that the attacker
has a solution to the problem.
3.Virus
Virus is a program that replicates. It spreads from
file to
file on your system infecting them.
4.Worm
A worm is a standalone program that doesn’t require
user intervention to spread. Worms don’t infect
existing files – they spread copies of themselves
instead.
Photo credit: Don Hankins / Foter / CC BY
https://www.flickr.com/photos/23905174@N00/1594411528/
Miss Afraah Anjum
How Do Bad Guys Compromise Your
Computer Security
5.Trojan
Trojan horses pose as useful software, such as a legitimate
program. Instead of being well-behaved software, a Trojan
opens a backdoor on your system.
6.Ransomware
• Ransomware is a malicious program that performs the
following malicious activities after infecting a computer.
• Makes the system non-functional unless the victim agrees to pay a
ransom.
• Encrypts the computer’s data and demands a ransom to release it to
the victim.
Photo credit: Don Hankins / Foter / CC BY
https://www.flickr.com/photos/23905174@N00/1594411528/
Miss Afraah Anjum
How Do Bad Guys Compromise Your
Computer Security
7.Spyware
A common computer security threat, spyware is a class
of malicious program that secretly steals your personal
information and sends it to advertisers or hackers.
8. Rogue Antivirus
A rogue antivirus, also known as scareware, is a fake
program that disguises itself as a genuine software but
performs
malicious activities in user’s machine.
Photo credit: Don Hankins / Foter / CC BY
https://www.flickr.com/photos/23905174@N00/1594411528/
Miss Afraah Anjum
How Do Bad Guys Compromise Your
Computer Security
9.Rootkit
A rootkit is a program (or a collection of programs)
that in itself is not harmful, but helps viruses and
malware hide from antivirus software.
Photo credit: Don Hankins / Foter / CC BY
https://www.flickr.com/photos/23905174@N00/1594411528/
Miss Afraah Anjum
Top Computer
Security Actions
Miss Afraah Anjum
Top Computer Security
Actions
1.Patch, Patch, Patch!
Set up your computer for automatic software and operating system updates. An
unpatched machine is more likely to have software vulnerabilities that can be
exploited.
2.Install Security Software
When installed, the software should be set to scan your files and update your virus
definitions on a regular basis.
3.Choose Strong Passwords
Choose strong passwords with letters, numbers, and special characters to
create a mental image or an acronym that is easy for you to remember. Create
a different password for each important account, and change passwords
regularly.
Miss Afraah Anjum
Top Computer Security
Actions
4.Backup, Backup, Backup!
Backing up your machine regularly can protect you from the unexpected. Keep a few
months'
worth of backups and make sure the files can be retrieved if needed.
5.Control access to your machine
Don't leave your computer in an unsecured area, or unattended and logged on,
especially in public places. The physical security of your machine is just as important as
its technical security
6.Use email and the Internet safely
Ignore unsolicited emails, and be wary of attachments, links and forms in emails that
come from people you don't know, or which seem "phishy." Avoid untrustworthy (often
free) downloads from freeware or shareware sites.
Miss Afraah Anjum
Top Computer Security
Actions
7. Protect sensitive data
Reduce the risk of identity theft. Securely remove sensitive data files from your hard drive,
which is also recommended when recycling or repurposing your computer. Use the
encryption tools built into your operating system to protect sensitive files you need to
retain.
8.Use desktop firewalls
Macintosh and Windows computers have basic desktop firewalls as part of their
operating systems. When set up properly, these firewalls protect your computer files
from being scanned
9.Use secure connections.
When connected to the Internet, your data can be vulnerable while in transit. Use
remote connectivity and secure file transfer options when off campus
Miss Afraah Anjum
How Quick
Heal Takes
Care
Of Your
Computer
Security
Miss Afraah Anjum
How Can Quick Heal
Help
Miss Afraah Anjum
You might also like
- Threats and VulnerabilitiesDocument9 pagesThreats and VulnerabilitiesSimbaNo ratings yet
- Chapter_Four_CSDocument74 pagesChapter_Four_CSAschalew AyeleNo ratings yet
- HIGH SCHOOL ICT MalwareDocument20 pagesHIGH SCHOOL ICT MalwareArlo 2No ratings yet
- Netwok Secuity 1Document190 pagesNetwok Secuity 1summ39784No ratings yet
- Computer Security and Safety, Ethics, and PrivacyDocument41 pagesComputer Security and Safety, Ethics, and Privacygoogley71No ratings yet
- Lecture 4. Com - EthicsDocument11 pagesLecture 4. Com - Ethicsokello jacob juniorNo ratings yet
- Lecture 16 & 17Document21 pagesLecture 16 & 17Hussnain HussnainNo ratings yet
- L1 Intro Infosec sp22Document48 pagesL1 Intro Infosec sp22Liz ChenNo ratings yet
- COSC 6301 - Computer Security Threats - and - VulnerabilitiesDocument52 pagesCOSC 6301 - Computer Security Threats - and - VulnerabilitiesmailtosiscoNo ratings yet
- Security Unit 5: Neha IjazDocument11 pagesSecurity Unit 5: Neha Ijazneha ijazNo ratings yet
- LIJO BC PresentationDocument19 pagesLIJO BC Presentationarundev1986No ratings yet
- Chapter 1Document52 pagesChapter 1Wafaa AlshaikhiNo ratings yet
- Lecture 1 - Intro To Software SecurityDocument32 pagesLecture 1 - Intro To Software SecurityKing KongNo ratings yet
- Cybersecurity, Risk Management, and Financial CrimeDocument12 pagesCybersecurity, Risk Management, and Financial CrimeNico NathanaelNo ratings yet
- Bab5 Digital Security, Ethics, and Privacy Threats, Issues and DefensesDocument44 pagesBab5 Digital Security, Ethics, and Privacy Threats, Issues and Defensesciaaq00No ratings yet
- Chapter 8 - Securing Information SystemsDocument28 pagesChapter 8 - Securing Information SystemsIrvan 69No ratings yet
- Threats and AttacksDocument21 pagesThreats and AttacksMichaelaNo ratings yet
- CEH Module 01: Introduction To Ethical HackingDocument37 pagesCEH Module 01: Introduction To Ethical HackingAhmad Mahmoud100% (9)
- Ethical Hacking (Sem Vi) : Presented By: Ms. Drashti ShrimalDocument11 pagesEthical Hacking (Sem Vi) : Presented By: Ms. Drashti ShrimalSunny PandeyNo ratings yet
- KLD PPT Information Assurance and Security 2024Document18 pagesKLD PPT Information Assurance and Security 2024rikrianoNo ratings yet
- Insiderthreats 150305131515 Conversion Gate01Document14 pagesInsiderthreats 150305131515 Conversion Gate01Anoop PattatNo ratings yet
- 3600 Lecture2 Need For SecurityDocument42 pages3600 Lecture2 Need For SecurityHYAB ENGINEERINGNo ratings yet
- Computer Security and Safety, Ethics, and PrivacyDocument3 pagesComputer Security and Safety, Ethics, and PrivacypremsbylowiNo ratings yet
- Network SecurityDocument26 pagesNetwork SecurityturiagabaNo ratings yet
- Risk and security solutions overviewDocument10 pagesRisk and security solutions overviewBree ElaineNo ratings yet
- Ethics and Information Security ThreatsDocument5 pagesEthics and Information Security Threatsanon_461820450No ratings yet
- Differences Between Traditional Security, Computer Security and Information SecurityDocument8 pagesDifferences Between Traditional Security, Computer Security and Information SecurityShweta DishwarNo ratings yet
- Security and ThreatsDocument44 pagesSecurity and ThreatsfathiahNo ratings yet
- 2 - Security Policies, Security ControlsDocument18 pages2 - Security Policies, Security ControlsNilaa RaghunathanNo ratings yet
- Cyber security fundamentalsDocument17 pagesCyber security fundamentalsDivyansh BajpaiNo ratings yet
- SecurityDocument24 pagesSecuritythuya minzinNo ratings yet
- Application Security - Unit 3 PDFDocument146 pagesApplication Security - Unit 3 PDFViswantahNo ratings yet
- Fundamentals of Computer SecurityDocument5 pagesFundamentals of Computer SecurityRosen LPNo ratings yet
- Topic 5.0 Basic Security - Part 1Document26 pagesTopic 5.0 Basic Security - Part 1محمدجوزيايNo ratings yet
- Reviewer APC 5 (AutoRecovered)Document8 pagesReviewer APC 5 (AutoRecovered)Jhon Angelo M. PintorNo ratings yet
- FALLSEM2021-22 CSE3501 ETH VL2021220101428 Reference Material I 04-10-2021 Mod 2 System Security-1 JeyDocument50 pagesFALLSEM2021-22 CSE3501 ETH VL2021220101428 Reference Material I 04-10-2021 Mod 2 System Security-1 Jeyharita sakkaravarthiNo ratings yet
- Icdl It Security QRG - v1.0Document4 pagesIcdl It Security QRG - v1.0AkshitNo ratings yet
- Week 11 SECURITY AND CONTROLDocument53 pagesWeek 11 SECURITY AND CONTROLeugenemwangi08No ratings yet
- Materi 3bDocument47 pagesMateri 3bakhmad ismailNo ratings yet
- Information Security Issues, Threats, Solution & StandradsDocument46 pagesInformation Security Issues, Threats, Solution & StandradsmasteranshulNo ratings yet
- Lecture 2 Security ThreatsDocument56 pagesLecture 2 Security ThreatsWycliff Jonathan KituriNo ratings yet
- FALLSEM2023-24 BCSE353E ETH VL2023240100875 2023-05-23 Reference-Material-IDocument50 pagesFALLSEM2023-24 BCSE353E ETH VL2023240100875 2023-05-23 Reference-Material-Idsa dsaNo ratings yet
- Sec AwarenessDocument7 pagesSec Awarenesslorenadelejero14No ratings yet
- 2 BAB 6 Ethical and Security in Information SystemDocument28 pages2 BAB 6 Ethical and Security in Information SystemDBS2 Isma Andika F1032No ratings yet
- CH 01Document33 pagesCH 01Darwin VargasNo ratings yet
- 2023 - 10 - 04 - Defensive Operations - Part BDocument66 pages2023 - 10 - 04 - Defensive Operations - Part BjcsaldanhaNo ratings yet
- Computer & Network Security: Course OverviewDocument18 pagesComputer & Network Security: Course Overviewemad helalNo ratings yet
- Data Security, Privacy and IntegrityDocument19 pagesData Security, Privacy and Integrityhao zhangNo ratings yet
- Chapter 22Document80 pagesChapter 22Kushagra TiwaryNo ratings yet
- ZT - Secure The Journey To Cloud - Webinar SeriesDocument63 pagesZT - Secure The Journey To Cloud - Webinar SeriespedirstuffNo ratings yet
- Discovering Computers CH 5 - UpdatedDocument50 pagesDiscovering Computers CH 5 - UpdatedKevin Dalipe100% (1)
- CH1 IntroductionDocument40 pagesCH1 IntroductionbautilmenlynsaNo ratings yet
- Case Study Cybersecurity in AddictionDocument18 pagesCase Study Cybersecurity in AddictionAgha Salman HaiderNo ratings yet
- Computer and Information Security 2Document30 pagesComputer and Information Security 2Jehad MogyNo ratings yet
- Seminar CyberDocument20 pagesSeminar Cyberyasaswi sonyNo ratings yet
- Network Security MeasuresDocument29 pagesNetwork Security MeasuresMohd RafeeqNo ratings yet
- Cybersecurity Risks and Data Breach PreventionDocument12 pagesCybersecurity Risks and Data Breach PreventionBluesNo ratings yet
- Layers of Cyber Security FinalDocument9 pagesLayers of Cyber Security FinalSyed SalmanNo ratings yet
- Introduction To Cyber SecurityDocument13 pagesIntroduction To Cyber SecurityBagus SWP100% (1)
- Your System's Sweetspots: CEO's Advice on Basic Cyber Security: CEO's Advice on Computer ScienceFrom EverandYour System's Sweetspots: CEO's Advice on Basic Cyber Security: CEO's Advice on Computer ScienceNo ratings yet
- Raghavender Pinreddy: Career SummaryDocument4 pagesRaghavender Pinreddy: Career SummaryAnonymous 9WyPyismNo ratings yet
- Glenmark Pharma ERP CaseDocument4 pagesGlenmark Pharma ERP CaseNitin PaiNo ratings yet
- Introduction PDFDocument38 pagesIntroduction PDFMaria Sevciuc100% (1)
- MITMDocument2 pagesMITMAlpha MaleNo ratings yet
- Commvault Complete Backup and Recovery DatasheetDocument2 pagesCommvault Complete Backup and Recovery DatasheetitnetmanNo ratings yet
- Subsystem Specification - Model TextDocument6 pagesSubsystem Specification - Model Textshankar1505No ratings yet
- CV Meal-Cerdas Iki LoboDocument1 pageCV Meal-Cerdas Iki LoboIki LoboNo ratings yet
- NDLI CLUB Registration Process: Website: Https://club - Ndl.iitkgp - Ac.in/club-Home Support EmailDocument27 pagesNDLI CLUB Registration Process: Website: Https://club - Ndl.iitkgp - Ac.in/club-Home Support EmaildanielrubarajNo ratings yet
- NIM Nama Mahasiswa Jur Topik Jalur Penulisan KDDSN Pemb 1 Nama Pem 1 KDDSN Pemb 2 Nama Pemb 2 Judul Indonesia Judul Inggris Hari Tanggal Jam RuangDocument1 pageNIM Nama Mahasiswa Jur Topik Jalur Penulisan KDDSN Pemb 1 Nama Pem 1 KDDSN Pemb 2 Nama Pemb 2 Judul Indonesia Judul Inggris Hari Tanggal Jam RuangAtqia AuliaNo ratings yet
- IDXPF User Guide EnUSDocument28 pagesIDXPF User Guide EnUSKushal SharmaNo ratings yet
- Linux, AWS, and DevOps FundamentalsDocument4 pagesLinux, AWS, and DevOps Fundamentalsranjeetsingh2908No ratings yet
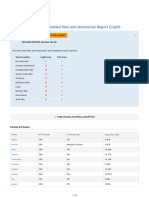
- URL Fuzzer - Discover Hidden Files and Directories Report (Light)Document2 pagesURL Fuzzer - Discover Hidden Files and Directories Report (Light)Segah Beste ÖnerNo ratings yet
- Certified Services Associate Lab GuideDocument78 pagesCertified Services Associate Lab GuideDulce Alvarado100% (2)
- Performance For AWS Snowball - AWS SnowballDocument3 pagesPerformance For AWS Snowball - AWS SnowballNoneNo ratings yet
- Kurikulum MIT Cyber Security A5Document1 pageKurikulum MIT Cyber Security A5Yasser FaridNo ratings yet
- Com - Yy.hiyo Com-Yy-Hiyo 2019 11 28 23 56Document260 pagesCom - Yy.hiyo Com-Yy-Hiyo 2019 11 28 23 56nisa safitriNo ratings yet
- IP Multicast: Next Steps To Make It RealDocument25 pagesIP Multicast: Next Steps To Make It RealsabeNo ratings yet
- Ab Q Bank WebDocument6 pagesAb Q Bank WebitmmxxiNo ratings yet
- Contact Us Today At: Or: México CityDocument2 pagesContact Us Today At: Or: México CityThuyaNo ratings yet
- Mocktest Research 8292920292Document6 pagesMocktest Research 8292920292PRVLNo ratings yet
- Erp PresentationDocument43 pagesErp PresentationShalini ShaluNo ratings yet
- RT 4105 B 112017Document4 pagesRT 4105 B 112017SwatiNo ratings yet
- List of Error CodesDocument13 pagesList of Error CodesAli AhmadNo ratings yet
- JPM Cio Survey 2020Document106 pagesJPM Cio Survey 2020stuNo ratings yet
- P2P DesignDocument10 pagesP2P DesignAvinash PatilNo ratings yet
- SQL DBA Learning SyllabusDocument6 pagesSQL DBA Learning SyllabuspraveenmpkNo ratings yet
- Ls-Dyna Manual Volume II r14Document2,097 pagesLs-Dyna Manual Volume II r14sulongge98No ratings yet
- Data Analyst Roadmap - 2023Document9 pagesData Analyst Roadmap - 2023kripali sharmaNo ratings yet
- AWS S3-Dev GuideDocument885 pagesAWS S3-Dev GuideLenvion LNo ratings yet
- Sharda Bia10e Tif 01Document11 pagesSharda Bia10e Tif 01Kong KasemsuwanNo ratings yet