Professional Documents
Culture Documents
SSL V/S Set: By-Neelu Devi
Uploaded by
Khushi Gupta0 ratings0% found this document useful (0 votes)
44 views12 pagesSSL and SET are both security protocols for online transactions. [1] SSL establishes an encrypted link between a server and browser to securely transmit information. [2] It uses four protocols: the SSL record protocol divides and encrypts data; the handshake protocol establishes sessions in four phases; the change-cipher protocol switches the connection to encryption; and the alert protocol conveys warnings and errors. [3] SET is an open security specification designed for credit card transactions. It ensures security, confidentiality and uses digital certificates to authenticate participants like cardholders, issuers, merchants and acquirers.
Original Description:
ssl vs set
Original Title
SSL vs SET
Copyright
© © All Rights Reserved
Available Formats
PPTX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentSSL and SET are both security protocols for online transactions. [1] SSL establishes an encrypted link between a server and browser to securely transmit information. [2] It uses four protocols: the SSL record protocol divides and encrypts data; the handshake protocol establishes sessions in four phases; the change-cipher protocol switches the connection to encryption; and the alert protocol conveys warnings and errors. [3] SET is an open security specification designed for credit card transactions. It ensures security, confidentiality and uses digital certificates to authenticate participants like cardholders, issuers, merchants and acquirers.
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
44 views12 pagesSSL V/S Set: By-Neelu Devi
Uploaded by
Khushi GuptaSSL and SET are both security protocols for online transactions. [1] SSL establishes an encrypted link between a server and browser to securely transmit information. [2] It uses four protocols: the SSL record protocol divides and encrypts data; the handshake protocol establishes sessions in four phases; the change-cipher protocol switches the connection to encryption; and the alert protocol conveys warnings and errors. [3] SET is an open security specification designed for credit card transactions. It ensures security, confidentiality and uses digital certificates to authenticate participants like cardholders, issuers, merchants and acquirers.
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
You are on page 1of 12
SSL v/s SET
BY- NEELU DEVI
SSL
Secure Socket Layer (SSL) is that the normal security
technology for establishing associate encrypted link
between an internet server and a browser.
This link ensures that each one knowledge passed
between the online server and browsers stay
personal and integral.
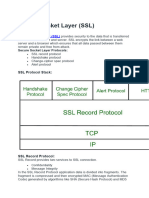
Secure Socket Layer Protocols
SSL record protocol
Handshake protocol
Change-cipher spec protocol
Alert protocol
SSL Record Protocol
SSL Record provides two services to SSL
connection.
Confidentiality
Message Integrity
In the SSL Record Protocol application data is
divided into fragments.
The fragment is compressed and then encrypted
MAC generated by algorithms like SHA is appended.
After that encryption of the data is done and in last
SSL header is appended to the data.
Handshake Protocol
Handshake Protocol is used to establish sessions.
Handshake protocol uses four phases to complete its
cycle.
Phase-1: In Phase-1 both Client and Server send hello-
packets to each other.
Phase-2: Server sends his certificate and Server-key-
exchange.
Phase-3: In this phase Client reply to the server by
sending his certificate and Client-exchange-key.
Phase-4: In Phase-4 Change-cipher suite occurred and
after this Handshake Protocol ends.
Change-cipher Protocol
This protocol uses the SSL record protocol. Unless
Handshake Protocol is completed, the SSL record
Output will be in a pending state.
After handshake protocol, the Pending state is
converted into the current state.
Change-cipher protocol consists of a single message
which is 1 byte in length and can have only one value.
This protocol’s purpose is to cause the pending state
to be copied into the current state.
Alert Protocol
This protocol is used to convey SSL-related alerts to
the peer entity. Each message in this protocol
contain 2 bytes.
The level is further classified into two parts:
Warning:
This Alert has no impact on the connection between sender
and receiver.
Fatal Error:
This Alert breaks the connection between sender and
receiver.
SET
SET is an open encryption and security specification
designed to protect credit card transactions on the
internet.
set is in effect a set of protocols for ensuring security
and confedentiality.
SET is a relatively new standard. It was first used in
feb 1996 and was proposed by visa and matercard.
Participants in SET
In the general scenario of online transactions, SET
includes similar participants:
Cardholder – customer
Issuer – customer financial institution
Merchant
Acquirer – Merchant financial
Certificate authority – Authority that follows certain
standards and issues certificates(like X.509V3) to all other
participants.
Advantages of SET
Privacy- uses 1024 bits public key cryptography
which renders the intercepted message unreadable.
integrity-hashing and signing ensures message sent
is unaltered.
authentication-ises digital certificates to ensures the
parties are really who they claim to be.
SSL v/s SET
You might also like
- Root Canal Cover UpDocument248 pagesRoot Canal Cover UpVictor Mendes97% (36)
- Lab SSLDocument7 pagesLab SSLJacinto BenaventeNo ratings yet
- Grade 6 PollutionDocument3 pagesGrade 6 PollutionNermine Mouallem75% (4)
- Clint-Roy Mukarakate Cyrptography Assignment 2Document6 pagesClint-Roy Mukarakate Cyrptography Assignment 2Clint MukarakateNo ratings yet
- SSL in Network and Web SecurityDocument6 pagesSSL in Network and Web Security2021ai55deNo ratings yet
- Web Security: Secure Socket Layer (SSL)Document6 pagesWeb Security: Secure Socket Layer (SSL)Lokesh Sai Kumar DasariNo ratings yet
- Secure Socket Layer Sec BDocument24 pagesSecure Socket Layer Sec BGurdeep SidhuNo ratings yet
- Unit - 3Document41 pagesUnit - 3TamannaNo ratings yet
- Sockets Layer (SSL) and The Follow-On (Subsequent) Internet Standard ofDocument8 pagesSockets Layer (SSL) and The Follow-On (Subsequent) Internet Standard ofFazeelur RahmanNo ratings yet
- Network NotesDocument16 pagesNetwork Notesboka987No ratings yet
- Wireless Ethical HackingDocument26 pagesWireless Ethical HackingGurdeep SidhuNo ratings yet
- Unit 4 - Presentation2Document28 pagesUnit 4 - Presentation2parthjethva1407No ratings yet
- Web SecurityDocument18 pagesWeb Securitykrii24u8No ratings yet
- C&NS UNIT-5pdfDocument28 pagesC&NS UNIT-5pdfDhanush GummidiNo ratings yet
- Cns Unit-Iv Web SecurityDocument12 pagesCns Unit-Iv Web SecurityAravind VNo ratings yet
- Information Security Unit3Document6 pagesInformation Security Unit3anushk jainNo ratings yet
- Transport Level Security PresentationDocument30 pagesTransport Level Security PresentationAhimbisibwe BakerNo ratings yet
- SSL and Millicent ProtocolsDocument15 pagesSSL and Millicent ProtocolsSoorya ColorblindNo ratings yet
- Interview Errors To AvoidDocument32 pagesInterview Errors To AvoidKashif MobeenNo ratings yet
- Security at The Transport LayerDocument5 pagesSecurity at The Transport LayerhemaNo ratings yet
- BRC-Transport-Level SecurityDocument40 pagesBRC-Transport-Level SecurityanshulNo ratings yet
- Vulnerabilities of The SSL Tls ProtocolDocument12 pagesVulnerabilities of The SSL Tls ProtocolManish AgarwalNo ratings yet
- Web SecurityDocument17 pagesWeb SecurityUchiha SasukeNo ratings yet
- Similarly God Won't Give Problems Without SolutionsDocument43 pagesSimilarly God Won't Give Problems Without Solutionsrh_rathodNo ratings yet
- CNS WBDocument45 pagesCNS WBPrakash RajNo ratings yet
- TlsDocument18 pagesTlsasd666dsaNo ratings yet
- Web Security 17L238Document30 pagesWeb Security 17L238Rakesh VenkatesanNo ratings yet
- Transport Layer SecurityDocument33 pagesTransport Layer SecurityFelix Enrique ParedesNo ratings yet
- Unit-6 Network Security and Public Key InfrastructureDocument36 pagesUnit-6 Network Security and Public Key Infrastructureshrestharojesh34No ratings yet
- Web SecurityDocument16 pagesWeb SecurityhussamNo ratings yet
- Web Security and Email SecurityDocument57 pagesWeb Security and Email Securityprajwol neupaneNo ratings yet
- Secure Sockets Layer (SSL) Protocol: by Steven GiovencoDocument22 pagesSecure Sockets Layer (SSL) Protocol: by Steven GiovencoThura Htet AungNo ratings yet
- Transport Layer Security: Module-1Document26 pagesTransport Layer Security: Module-1digital loveNo ratings yet
- SSL TlsDocument22 pagesSSL Tlsvice pyNo ratings yet
- UNIT-5: Web Security: Web Security Considerations, Secure Socket Layer (SSL) and Transport LayerDocument27 pagesUNIT-5: Web Security: Web Security Considerations, Secure Socket Layer (SSL) and Transport LayerhafeezaNo ratings yet
- DiniDocument20 pagesDiniiraj shaikhNo ratings yet
- Cyber and Security NotesDocument37 pagesCyber and Security NotesChandan B V GowdaNo ratings yet
- Module-2 NSDocument40 pagesModule-2 NSjahnavi.dmNo ratings yet
- CNS UNIT 5 NotesDocument36 pagesCNS UNIT 5 NotesDhrumil DasNo ratings yet
- Transport Layer Security (TLS)Document14 pagesTransport Layer Security (TLS)svmc bcaNo ratings yet
- Transport Layer Security (TLS)Document14 pagesTransport Layer Security (TLS)svmc bcaNo ratings yet
- SSL PresentationDocument10 pagesSSL Presentationtreesachandt100% (1)
- U4 4 Secured Socket LayerDocument22 pagesU4 4 Secured Socket LayerNeetishNo ratings yet
- Cryptography and Network SecurityDocument12 pagesCryptography and Network SecurityWiedy Tira PratamaNo ratings yet
- SSL ArchitectureDocument23 pagesSSL ArchitectureEswin Angel75% (4)
- Web SecurityDocument23 pagesWeb SecurityBruno BlayNo ratings yet
- ETIT NotesDocument14 pagesETIT NotesAniket BinewaleNo ratings yet
- Cryptography and Network Security: Fourth Edition by William StallingsDocument24 pagesCryptography and Network Security: Fourth Edition by William Stallingskstu1112No ratings yet
- SSL ArchitectureDocument3 pagesSSL ArchitectureRokonuzzamanNo ratings yet
- Network Fault Finding and Wireshark: - Analysing SSL/TLSDocument7 pagesNetwork Fault Finding and Wireshark: - Analysing SSL/TLSAlexHera89No ratings yet
- Secure Socket LayerDocument4 pagesSecure Socket LayerAkhilJaanuNo ratings yet
- Secure Socket LayerDocument14 pagesSecure Socket LayerbetoplapaNo ratings yet
- SSL Introduction With Sample Transaction and Packet Exchange - CiscoDocument8 pagesSSL Introduction With Sample Transaction and Packet Exchange - CiscoshivNo ratings yet
- Secure Socket Layer: M S.Bhiogade Patni Computer Services, Mumbai, IndiaDocument6 pagesSecure Socket Layer: M S.Bhiogade Patni Computer Services, Mumbai, Indiadidiey87No ratings yet
- VTU Network Security (10ec832) Unit-5 Notes.Document31 pagesVTU Network Security (10ec832) Unit-5 Notes.jayanthdwijesh h pNo ratings yet
- The Kerberos ProtocolDocument18 pagesThe Kerberos ProtocolJohn Wilson100% (1)
- Transport Layer SecurityDocument3 pagesTransport Layer Securityfawas hamdiNo ratings yet
- Expt 9 - C235Document7 pagesExpt 9 - C235ksbasdaNo ratings yet
- Chapter 17Document32 pagesChapter 17pravin_renold7435No ratings yet
- Secure Socket Layer Implementations A ReDocument6 pagesSecure Socket Layer Implementations A Refans 29No ratings yet
- SSL - Secure Sockets LayerDocument15 pagesSSL - Secure Sockets Layerhareem100No ratings yet
- DocxDocument1 pageDocxKhushi GuptaNo ratings yet
- Dayalbagh Educational Institute: Experiment 1-To Implement Half Adder by Using Basic and UniversalDocument41 pagesDayalbagh Educational Institute: Experiment 1-To Implement Half Adder by Using Basic and UniversalKhushi GuptaNo ratings yet
- Dayalbagh Educational Institute: Submitted To Miss Shalini AgarwalDocument36 pagesDayalbagh Educational Institute: Submitted To Miss Shalini AgarwalKhushi GuptaNo ratings yet
- Cryptography & Network Security Lab: Dayalbagh Educational InstituteDocument15 pagesCryptography & Network Security Lab: Dayalbagh Educational InstituteKhushi GuptaNo ratings yet
- Part BDocument10 pagesPart BKhushi GuptaNo ratings yet
- Raspberry: - by Khushi GuptaDocument18 pagesRaspberry: - by Khushi GuptaKhushi GuptaNo ratings yet
- A Business Plan For Starting Yummy Chocolate CompanyDocument26 pagesA Business Plan For Starting Yummy Chocolate CompanyKhushi GuptaNo ratings yet
- Nodemcu: Name-Kanchan Pal Course-B.VOC (IOT) ROLL NO:-1904700Document10 pagesNodemcu: Name-Kanchan Pal Course-B.VOC (IOT) ROLL NO:-1904700Khushi GuptaNo ratings yet
- COVID-19Document9 pagesCOVID-19Tony BernardNo ratings yet
- Psychometric Evaluation of The Albanian Version of Tosca 3 To Measure Shame and GuiltDocument6 pagesPsychometric Evaluation of The Albanian Version of Tosca 3 To Measure Shame and GuiltMirela Cojocaru StetcoNo ratings yet
- OCSPDocument3 pagesOCSPgayathrisanNo ratings yet
- ArulesDocument106 pagesArulesFadhilah Amin FathoniNo ratings yet
- E TickDocument23 pagesE Tickclaire redfieldNo ratings yet
- 2023 School Selection Form TemplateDocument2 pages2023 School Selection Form TemplatejessiequinieNo ratings yet
- Ribeiro Et Al 2003Document7 pagesRibeiro Et Al 2003baglamaNo ratings yet
- Britannia Industry Project MainDocument32 pagesBritannia Industry Project MainShanu Satheesan100% (1)
- Jee Main Physics Super ThirtyDocument170 pagesJee Main Physics Super ThirtyAnil KumarNo ratings yet
- Spare Parts List: Hydraulic BreakersDocument24 pagesSpare Parts List: Hydraulic BreakersJean MoralesNo ratings yet
- Solution Manual For Community Nutrition in Action An Entrepreneurial Approach 7th Edition by Boyle ISBN 1305637992 9781305637993Document14 pagesSolution Manual For Community Nutrition in Action An Entrepreneurial Approach 7th Edition by Boyle ISBN 1305637992 9781305637993jaredhernandezbazicwejqt100% (25)
- Hihway Materilas Ch5 PP 137 To 166 PDFDocument30 pagesHihway Materilas Ch5 PP 137 To 166 PDFharNo ratings yet
- Abhaya Mudra: "Abhaya" Means "Fearless". Abhaya Mudra Represents Protection, Peace, Benevolence, and Dispelling of FearDocument9 pagesAbhaya Mudra: "Abhaya" Means "Fearless". Abhaya Mudra Represents Protection, Peace, Benevolence, and Dispelling of FearIon ConstantinNo ratings yet
- Bungalow: Bill of QuantitiesDocument2 pagesBungalow: Bill of QuantitiesChia NgwahNo ratings yet
- Astro Tips & Techniques How To'sDocument8 pagesAstro Tips & Techniques How To'stsampounas100% (1)
- A 109 - A 109M - 16 PDFDocument9 pagesA 109 - A 109M - 16 PDFأسامة وحيد الدين رمضانNo ratings yet
- Propulsion of VLC C 19993990Document7 pagesPropulsion of VLC C 19993990hpss77No ratings yet
- R8T5 em Sa2Document4 pagesR8T5 em Sa2Saltanat OralNo ratings yet
- Xobni User ManualDocument31 pagesXobni User ManualBob Hails100% (1)
- PDF The Women of Lemuria Ancient Wisdom For Modern Times Nodrm CompressDocument60 pagesPDF The Women of Lemuria Ancient Wisdom For Modern Times Nodrm Compressguoxing weiNo ratings yet
- 09 Chapter 1Document43 pages09 Chapter 1Suchetana SenNo ratings yet
- Infiniteskills - Learning Ubuntu Linux (Download Torrent) - TPBDocument2 pagesInfiniteskills - Learning Ubuntu Linux (Download Torrent) - TPBAnuj KansalNo ratings yet
- The Negative Impact of Cigarette Smoking: Mapeh (Health) 8-Quarter 4Document60 pagesThe Negative Impact of Cigarette Smoking: Mapeh (Health) 8-Quarter 4JOHN FRITS GERARD MOMBAYNo ratings yet
- 2200 667 MR 2105 00006 - 01Document11 pages2200 667 MR 2105 00006 - 01ahmadhatakeNo ratings yet
- Problems On MergerDocument7 pagesProblems On MergerSUNILABHI_APNo ratings yet
- Science Grad9: Quarter 4 - Module 7 Heat, Work and EnergyDocument14 pagesScience Grad9: Quarter 4 - Module 7 Heat, Work and EnergyAinah DimasangcaNo ratings yet
- Earth Science SHS 12.2 Factors Controlling MetamorphismDocument14 pagesEarth Science SHS 12.2 Factors Controlling MetamorphismCamille AnibNo ratings yet
- ACX Junos CliDocument336 pagesACX Junos ClimelvynstgoNo ratings yet