Professional Documents
Culture Documents
02 - Fairgame Rundown
Uploaded by
carkloun0 ratings0% found this document useful (0 votes)
7 views62 pagesCopyright
© © All Rights Reserved
Available Formats
PPTX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
7 views62 pages02 - Fairgame Rundown
Uploaded by
carklounCopyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
You are on page 1of 62
RPISEC
Fairgame Rundown
Fall 2022
RPISEC - 09/30/2022 RPISEC 1
Fairgame
• Fairgame is an introductory CTF
• Runs until winter break
• Covers five subjects:
– pwn - binary exploitation
– re - reverse engineering
– crypto - cryptography
– web - web applications
– misc - puzzles, steganography, party tricks, etc.
RPISEC - 09/30/2022 RPISEC 2
Tooling
• VM installation was covered at INTROSEC
• Includes a variety of useful tools
• Get it here: http://tools.rpis.ec/
• We’ll also assume you have some basic experience with the
Linux command line
– All important commands are shown, though!
RPISEC - 09/30/2022 RPISEC 3
Conventions
$ commands are shown like this
RPISEC - 09/30/2022 RPISEC 4
misc
• misc chals cover a variety of topics
• Finding the right angle is key
RPISEC - 09/30/2022 RPISEC 5
misc100?
- Our misc100 is somewhere on Slack this year (:
- ...so we'll look at misc200 instead
- (it's definitely not just the normal misc100)
RPISEC - 09/30/2022 RPISEC 6
misc200 - “Flag? What Flag?”
• Download misc100.tar.gz
• This is a gzipped tarball
– gzip compresses files
– tar puts files into a single archive - a “tarball”
• Basically the .zip of Linux
RPISEC - 09/30/2022 RPISEC 7
misc200 - “Flag? What flag?”
• We’re told it’s an ext2 disk image
• ext2 is a predecessor of ext4
• We can mount the image to browse its contents like a flash
drive
RPISEC - 09/30/2022 RPISEC 8
misc200 - “Flag? What Flag?”
• Extract it with:
tar -xf misc100.tar.gz
• -x to extract
• -f to specify the file
RPISEC - 09/30/2022 RPISEC 9
misc200 - “Flag? What Flag?”
RPISEC - 09/30/2022 RPISEC 10
misc200 - “Flag? What flag?”
• One file comes out, misc100.img
• .img files are usually disk images
– Basically a snapshot of a storage device
• We can find out what kind of image it is with:
file misc100.img
• The file command tries to identify a file
RPISEC - 09/30/2022 RPISEC 11
misc200 - “Flag? What flag?”
• First, make a directory to mount to:
mkdir mnt
RPISEC - 09/30/2022 RPISEC 12
misc200 - “Flag? What flag?”
• Then, mount the image:
sudo mount -o loop misc100.img mnt
• mount requires root powers, hence the sudo
• Root password on the Tools VM is rpisec
• Now you can browse the files within:
cd mnt
RPISEC - 09/30/2022 RPISEC 13
misc200 - “Flag? What flag?”
• Let’s look around a bit
ls
• You’ll see the following files:
bin dev etc lib linuxrc lost+found proc sbin tmp usr var
• So this is a disk image of some Linux system
RPISEC - 09/30/2022 RPISEC 14
misc200 - “Flag? What flag?”
• ...but where’s the flag?
• Let’s take a closer look!
ls -la
• -l to show files in a list
• -a to show all files
RPISEC - 09/30/2022 RPISEC 15
misc200 - “Flag? What flag?”
• There’s a file called .flag in there!
– Files with a . in front are hidden by default
• So, what is it?
file .flag
• It’s gzip compressed data
• We can extract it with...gzip, of course
• The mounted image is read-only, though, so we’ll move the
file first.
RPISEC - 09/30/2022 RPISEC 16
misc200 - “Flag? What flag?”
cp .flag /tmp/flag.gz
cd /tmp
gunzip flag.gz
• Now we have a file called flag
file flag
• It’s a .tar again!
tar -xf flag
RPISEC - 09/30/2022 RPISEC 17
misc200 - “Flag? What flag?”
• The .tar contained a file called flag, so it overwrote itself
• Now we can just…
cat flag
RPISEC - 09/30/2022 RPISEC 18
misc200 - “Flag? What flag?”
• This sort of challenge becomes very easy once you’re used to
the terminal
• Always try to figure out what is you’re looking at!
– file
– binwalk
RPISEC - 09/30/2022 RPISEC 19
web
• web challenges deal with...web stuff
– Pretty much anything with a browser
• Split into two big categories:
– Client-side: attacking the browser
– Server-side: attacking the server
RPISEC - 09/30/2022 RPISEC 20
web100 - “Client Page”
• web100 presents us with a login screen
• First, we should examine the page!
• In Firefox, hit ctrl+u to view the page’s source
RPISEC - 09/30/2022 RPISEC 21
web100 - “Client Page”
• auth.js sounds interesting!
• Click on it to view the file
RPISEC - 09/30/2022 RPISEC 22
web100 - “Client Page”
• Oh no! Client-side authentication!
– The login is checked in your browser…
– ...and not on the server
• users sounds pretty interesting...
RPISEC - 09/30/2022 RPISEC 23
web100 - “Client Page”
• Open the dev console with F12 or ctrl-shift-I
• Now we can look at users by typing…
users
• It’s an array of two things, so view the first one:
users[0]
• Looks like a username and password to me!
• Log in and get the flag
RPISEC - 09/30/2022 RPISEC 24
web100 - “Client Page”
• That was easy.
• The rest are harder!
• Web challenges cover a lot of territory:
– SQL injection to abuse badly written database queries
– XSS (cross-site-scripting) to make other users run code
– Uploading malicious files and viewing those we shouldn’t
RPISEC - 09/30/2022 RPISEC 25
crypto
• crypto challenges fall into two camps:
– Classic ciphers, which are extremely weak
∘ Caesar ciphers
∘ Vigenere ciphers
– Modern ciphers, but with a deliberate mistake
∘ RSA
∘ DES
RPISEC - 09/30/2022 RPISEC 26
crypto100 - “Classic”
• This one is a classical cipher
– The title is a pretty big hint
– The cipher clearly didn’t hide the flag
vbqw{0bt1u_rkj_d0j_i0_we0t1u}
• So, we just need to identify the cipher
RPISEC - 09/30/2022 RPISEC 27
crypto100 - “Classic”
• Tools exist online for all of these
• Two of my suggestions:
– https://gchq.github.io/CyberChef/
– https://cryptii.com/
RPISEC - 09/30/2022 RPISEC 28
crypto100 - “Classic”
• It was a Caesar cipher.
– A=K
– Shift of 10
RPISEC - 09/30/2022 RPISEC 29
crypto100 - “Classic”
• Classical ciphers can be broken easily:
– Guessing all the keys (Caesar)
– Exploiting language patterns (Vigenere)
∘ E shows up way more than Z
• Attacking modern ciphers like this does not work:
– Huge keys, expensive operations
– The universe dies before you find the flag
• Crypto challenges will always have a trick
– Implementation errors, bad parameters, etc.
RPISEC - 09/30/2022 RPISEC 30
re and pwn
• re and pwn are two sides of the same coin
– re: figure out how a system works
– pwn: figure out how a system breaks
RPISEC - 09/30/2022 RPISEC 31
re100 - “Milk Run”
• Reversing is an incredibly deep subject
– static analysis!
– dynamic analysis!
– decompilation!
• Fortunately, re100 is pretty simple
– The program has a secret.
– We want the secret.
– Hey, isn’t this basically web100?
RPISEC - 09/30/2022 RPISEC 32
re100 - “Milk Run”
• First, try running the program
./re100
• We type some gibberish, it says no
RPISEC - 09/30/2022 RPISEC 33
re100 - “Milk Run”
• A great place to start is strings
• Shows readable text in a file
strings re100
• That’s a lot of text...
RPISEC - 09/30/2022 RPISEC 34
re100 - “Milk Run”
• We don’t want to read all of that
• We can use grep to filter it down
– grep takes a string to look for
strings re100 | grep flag
• The | is a pipe
– strings writes some stuff
– grep reads that stuff
• And there’s the flag!
RPISEC - 09/30/2022 RPISEC 35
re100 - “Milk Run”
• re is a huge puzzle
• There are many powerful tools out there:
– IDA/Ghidra/Binary Ninja/r2 for pulling apart a program
– strings and hexdump to peek at data
– objdump to find function names
– gdb to see what happens at runtime
RPISEC - 09/30/2022 RPISEC 36
pwn100 - “Rewards Program”
• pwn is what our motto is all about:
– Break it
– Hack it
– Own it
RPISEC - 09/30/2022 RPISEC 37
pwn100 - “Rewards Program”
• First, run the program
chmod +x rewards-program
./rewards-program
• It asks for your name. Type something short.
RPISEC - 09/30/2022 RPISEC 38
pwn100 - “Rewards Program”
• Darn :(
RPISEC - 09/30/2022 RPISEC 39
pwn100 - “Rewards Program”
• What if we had a longer name?
• Let’s say our name is…
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
RPISEC - 09/30/2022 RPISEC 40
pwn100 - “Rewards Program”
• That’s...interesting
RPISEC - 09/30/2022 RPISEC 41
pwn100 - “Rewards Program”
• Our input made some weird stuff happen:
– It messed up the point counter
∘ 1094795585 is not 0
– It crashed the whole program!
∘ Segfault!
• (we accessed invalid memory)
• We just broke it
RPISEC - 09/30/2022 RPISEC 42
pwn100 - "Rewards Program"
• The program stores our name next to the point counter
int points = 0;
char foo[20];
• But it only has room for 20 characters
• Our name was 32 characters long
RPISEC - 09/30/2022 RPISEC 43
pwn100 - “Rewards Program”
• This is a buffer overflow
– The program didn’t have room for our name
• 20 bytes of A's fit correctly
• The next 4 bytes clobbered the point counter
• The rest screwed up C's bookkeeping
RPISEC - 09/30/2022 RPISEC 44
pwn100 - “Rewards Program”
• So, how exactly did we get 1094795585 points?
• Let’s look at that number in a different way:
– Decimal: 1094795585
– Hex: 0x41414141
• That looks familiar.
• What was A in ASCII, again?
RPISEC - 09/30/2022 RPISEC 45
pwn100 - “Rewards Program”
• 0x41 = ‘A’
• 0x41414141 = ‘AAAA’
• So, what if we want 322424845 points?
RPISEC - 09/30/2022 RPISEC 46
pwn100 - “Rewards Program”
• Just go from decimal to hex:
– Decimal: 322424845
– Hexadecimal: 0x1337D00D
• very leet, d00d
• That’s hard to type!
– 0x13 is “device control 3”
– 0x0D is a carriage return
– 0xD0 is a Unicode Ð
RPISEC - 09/30/2022 RPISEC 47
pwn100 - “Rewards Program”
• python is great for this.
– Specifically, python 2, because it's nicer for binary data
– This prints out AAAAAAAAAAAAAAAA - sixteen A’s
python2 -c "print 'A'*16"
• We can pipe that into the program like this:
python2 -c "print 'A'*16" | pwn100
RPISEC - 09/30/2022 RPISEC 48
pwn100 - “Rewards Program”
• Experiment with this until you just barely corrupt the counter
RPISEC - 09/30/2022 RPISEC 49
pwn100 - “Rewards Program”
• We needed 21 A’s to change our points to 65
– Decimal: 65
– Hexadecimal: 0x41
• So, let’s send 20 A’s, then 1337D00D!
python2 -c "print 'A'*20 + '\x13\x37\xd0\x0d'" | pwn100
RPISEC - 09/30/2022 RPISEC 50
pwn100 - “Rewards Program”
• Hang on, that gave us 231749395 points
– Decimal: 231749395
– Hexadecimal: 0x0dd03713
• It’s...backwards?
RPISEC - 09/30/2022 RPISEC 51
pwn100 - “Rewards Program”
• The program’s variables are stored on the stack.
• The stack grows downward, from the largest address.
• In pwn100, it looks something like this:
– reward points (4 bytes)
– name (20 bytes)
• name is before reward points in memory
RPISEC - 09/30/2022 RPISEC 52
pwn100 - “Rewards Program”
• If we make our name too long, it messes up the points
counter.
• This goes from low to high memory
• The first byte is the least significant byte
– 21 A’s gave us 65 points, remember?
RPISEC - 09/30/2022 RPISEC 53
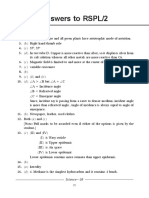
pwn100 - “Rewards Program”
• 20 A’s + \x0d:
– 0x0000000D
• 20 A’s + \x0d\d0:
– 0x0000D00D
• 20 A’s +\x0d\xd0\x37:
– 0x0037D00D
• 20 A’s + \0d\xd0\x37\x13:
– 0x1337D00D
RPISEC - 09/30/2022 RPISEC 54
pwn100 - “Rewards Program”
• So, by putting the four bytes in reverse order...
python2 -c "print 'A'*20 + '\x0d\xd0\x37\x13'" |
nc chals.fairgame.rpis.ec 5001
• ...we have the right number of points!
RPISEC - 09/30/2022 RPISEC 55
pwn100 - “Rewards Program”
• Now we just need to do it remotely.
• Most pwn challenges work like this
– Can’t just give you the program with the flag!
– Remember re100?
• We’ll use netcat, or nc for short
nc chals.fairgame.rpis.ec 5001
• Try talking to the program again
RPISEC - 09/30/2022 RPISEC 56
pwn100 - “Rewards Program”
• Last step: pipe Python’s output into nc!
python2 -c "print 'A'*20 + '\x0d\xd0\x37\x13'" |
nc chals.fairgame.rpis.ec 5001
• (all on one line)
RPISEC - 09/30/2022 RPISEC 57
pwn100 - “Rewards Program”
• It worked!
• ...wait, we can’t do anything
• The program executes a shell when you win
• We can’t type anything
– nc is getting its input from Python
– Python isn’t doing anything with keyboard input
• This sucks
RPISEC - 09/30/2022 RPISEC 58
pwn100 - “Rewards Program”
• Solution:
(python2 -c "print 'A'*20 + '\x0d\xd0\x37\x13'"; cat) |
nc chals.fairgame.rpis.ec 5001
• This executes python2, then cat
• cat will just repeat whatever we type
– ...which gets piped into netcat!
RPISEC - 09/30/2022 RPISEC 59
pwn100 - “Rewards Program”
• pwn is a staple of CTFs
• Creativity and patience are a must
• Too many techniques to count!
RPISEC - 09/30/2022 RPISEC 60
Review
We’ve covered the basics of five CTF categories:
• misc - the potpourri category
• web - browser and web server tricks
• crypto - uncovering ciphered data
• re - figuring out how a program works
• pwn - figuring out how to break a program
RPISEC - 09/30/2022 RPISEC 61
Coming Soon...
● Next week: web!
● Get involved with RPISEC @ https://rpis.ec/contact
○ Slack can be found on https://rpisec.slack.com
■ Come chat with RPISEC members and alumni!
○ Mailing list invite can be found on contact page
RPISEC - 09/30/2022 RPISEC 62
You might also like
- WorkingConnections2004 (IntermediateSecurity)Document194 pagesWorkingConnections2004 (IntermediateSecurity)api-3802795No ratings yet
- CAD ToolsDocument28 pagesCAD Toolscedo_ronaldo44No ratings yet
- QuickTime Toolkit Volume One: Basic Movie Playback and Media TypesFrom EverandQuickTime Toolkit Volume One: Basic Movie Playback and Media TypesNo ratings yet
- VMD Visualization Scripting TopoToolsDocument59 pagesVMD Visualization Scripting TopoToolssatish lukkaNo ratings yet
- RP2040 Assembly Language Programming: ARM Cortex-M0+ on the Raspberry Pi PicoFrom EverandRP2040 Assembly Language Programming: ARM Cortex-M0+ on the Raspberry Pi PicoNo ratings yet
- DEFCON 21 DePerry Ritter Femtocell UpdatedDocument84 pagesDEFCON 21 DePerry Ritter Femtocell UpdatedIon SmetaniucNo ratings yet
- Router Backdoor Powerpoint ConvertionDocument34 pagesRouter Backdoor Powerpoint ConvertionjpiratedNo ratings yet
- Graphics Gems III (IBM Version): Ibm VersionFrom EverandGraphics Gems III (IBM Version): Ibm VersionRating: 3.5 out of 5 stars3.5/5 (3)
- MySQLConf2007 CapacityDocument54 pagesMySQLConf2007 CapacityjspawNo ratings yet
- Recovering Lost Mpio Disks in AIXDocument10 pagesRecovering Lost Mpio Disks in AIXChristian FisherNo ratings yet
- Introduction To RISC-VDocument31 pagesIntroduction To RISC-VsantydNo ratings yet
- 03 Building Custom SocsDocument30 pages03 Building Custom Socsmuhammadakhtar201No ratings yet
- W00tsec Unpacking Firmware Images From Cable ModemsDocument10 pagesW00tsec Unpacking Firmware Images From Cable ModemsSebastian QuaroneNo ratings yet
- Batch Farm OverviewDocument28 pagesBatch Farm OverviewFoad WMNo ratings yet
- Black Hat 2006 Therm Optic ExploitDocument61 pagesBlack Hat 2006 Therm Optic ExploitSpyDr ByTeNo ratings yet
- Week1 CLOUDDocument38 pagesWeek1 CLOUDroderickvicenteNo ratings yet
- Slides 1Document23 pagesSlides 1ju jiNo ratings yet
- toner-deaf-hexacon-2022-releaseDocument60 pagestoner-deaf-hexacon-2022-releasemihaita.stefan1988No ratings yet
- HiDocument6 pagesHiCole ZubacNo ratings yet
- Mksysb Sin CD Ni TapeDocument11 pagesMksysb Sin CD Ni TapeLemcosmoNo ratings yet
- LogfileDocument6 pagesLogfileempiresNo ratings yet
- DavixDocument48 pagesDavixchepimancaNo ratings yet
- RISC, CISC, and Assemblers!: Hakim Weatherspoon CS 3410, Spring 2011Document31 pagesRISC, CISC, and Assemblers!: Hakim Weatherspoon CS 3410, Spring 2011Aakash KumarNo ratings yet
- IntelAcademic IoT Lab 02 Linux SideDocument22 pagesIntelAcademic IoT Lab 02 Linux SideAnwar Mar'ieNo ratings yet
- BH Ad 12 Stealing From Thieves Saher SlidesDocument52 pagesBH Ad 12 Stealing From Thieves Saher SlidesMohamed SaherNo ratings yet
- Avaya - Iscd - V4.0 - Fiat GroupDocument12 pagesAvaya - Iscd - V4.0 - Fiat GroupSwane CarolNo ratings yet
- Atari 2600 Programming For Newbies by Andrew Davie: AtariageDocument172 pagesAtari 2600 Programming For Newbies by Andrew Davie: AtariageArkinuxNo ratings yet
- C Programming "°º - Calypso - º°"Document148 pagesC Programming "°º - Calypso - º°"Pradeep TiwariNo ratings yet
- BRKDCN-2025Document145 pagesBRKDCN-2025daxtin.davonNo ratings yet
- Logfile PreviousDocument109 pagesLogfile Previousmason bowerNo ratings yet
- 01 - ReconocimientoDocument19 pages01 - ReconocimientoRicardoNo ratings yet
- Centralized Logins With NIS: Eric Stolten Tim Meade Mark SidnamDocument16 pagesCentralized Logins With NIS: Eric Stolten Tim Meade Mark SidnamSuhas SalveNo ratings yet
- How To Write Malware and Learn How To Fight It!Document40 pagesHow To Write Malware and Learn How To Fight It!Wesley HaripoNo ratings yet
- LogfileDocument18 pagesLogfileKerem Tuna AkçaNo ratings yet
- Cryptography Session 2020 v1Document98 pagesCryptography Session 2020 v1GlmNo ratings yet
- 8 Inch Hexaboard Demonstration and Test SetupDocument3 pages8 Inch Hexaboard Demonstration and Test Setup吳新業No ratings yet
- Synopsys Tutorial v11 PDFDocument64 pagesSynopsys Tutorial v11 PDFJinu M GeorgeNo ratings yet
- 08 Robot Sensor MotorDocument29 pages08 Robot Sensor MotoraDun iDeiNo ratings yet
- Linux Performance Analysis New Tools and Old Secrets: Brendan GreggDocument75 pagesLinux Performance Analysis New Tools and Old Secrets: Brendan GreggPocho GomezNo ratings yet
- W00tsec: Unpacking Firmware Images From Cable ModemsDocument10 pagesW00tsec: Unpacking Firmware Images From Cable ModemsJoe SapientNo ratings yet
- Algodoo v2.1.0 Win32 January 03 2023 logDocument7 pagesAlgodoo v2.1.0 Win32 January 03 2023 logJacob TibonNo ratings yet
- CVE-2012-1889: Security Update AnalysisDocument27 pagesCVE-2012-1889: Security Update AnalysisHigh-Tech BridgeNo ratings yet
- Programming The Raspberry PiDocument41 pagesProgramming The Raspberry Piheap50% (2)
- Introduction to ROS ProgrammingDocument43 pagesIntroduction to ROS ProgrammingCésar MoralesNo ratings yet
- SystemCompatibilityReport ProjectAnalysisDocument57 pagesSystemCompatibilityReport ProjectAnalysisadrin gaeiniNo ratings yet
- Siegecast Cobalt Strike BasicsDocument53 pagesSiegecast Cobalt Strike BasicsZERO 900100% (1)
- RAM Forensics - 2Document37 pagesRAM Forensics - 2Ana Beatriz FonsecaNo ratings yet
- Test The Web Server: UpdateDocument14 pagesTest The Web Server: UpdatePrabhu DoraiNo ratings yet
- SystemCompatibilityReport ProjectAnalysisDocument173 pagesSystemCompatibilityReport ProjectAnalysisSunil KumarNo ratings yet
- Time Finder MirrorDocument10 pagesTime Finder Mirroryugi17No ratings yet
- Hands-On Training - Riverbed Services Platform: Version 1.0 - Feb 2009Document13 pagesHands-On Training - Riverbed Services Platform: Version 1.0 - Feb 2009neoaltNo ratings yet
- Log FileDocument6 pagesLog FileJoyfulness EphaNo ratings yet
- Lecture 1: Introduction: Ucsd Ece 111 Prof. Bill Lin Winter 2019Document29 pagesLecture 1: Introduction: Ucsd Ece 111 Prof. Bill Lin Winter 2019Sivasubramanian ManickamNo ratings yet
- Horror On The Bus Horror On The BusDocument36 pagesHorror On The Bus Horror On The BusAlNo ratings yet
- Y Vasin Dahua IP Camera Where To Look What To PokeDocument29 pagesY Vasin Dahua IP Camera Where To Look What To PokeDavid AlvesNo ratings yet
- Atari 2600 ProgrammingDocument64 pagesAtari 2600 ProgrammingRicaTheSickNo ratings yet
- SRILM Kurulum TutorialDocument20 pagesSRILM Kurulum TutorialSeçkin ÖzbekNo ratings yet
- Netwrix Auditor Installation Configuration GuideDocument316 pagesNetwrix Auditor Installation Configuration GuidecarklounNo ratings yet
- Supporting Choice, Creating Opportunity Rules of ConductDocument5 pagesSupporting Choice, Creating Opportunity Rules of ConductcarklounNo ratings yet
- Ciam?: Extensibility - Scalability and Usability - Security - Privacy and ComplianceDocument2 pagesCiam?: Extensibility - Scalability and Usability - Security - Privacy and CompliancecarklounNo ratings yet
- Netwrix Auditor Installation Configuration GuideDocument316 pagesNetwrix Auditor Installation Configuration GuidecarklounNo ratings yet
- Cloud Enabling Public ServicesDocument18 pagesCloud Enabling Public ServicescarklounNo ratings yet
- Apache Guacamole project moves to ASFDocument1 pageApache Guacamole project moves to ASFcarklounNo ratings yet
- Copia de Financial SampleDocument64 pagesCopia de Financial SampleAlejandro Garcia GarayNo ratings yet
- Captain (RTD) Yahya M.A. Ondigo: Social Poisonous Habits" and A DVD With A Lecture He Gave With The TitleDocument1 pageCaptain (RTD) Yahya M.A. Ondigo: Social Poisonous Habits" and A DVD With A Lecture He Gave With The Titlecarkloun100% (1)
- Data Integration For BI: TIBCO Jaspersoft ETLDocument2 pagesData Integration For BI: TIBCO Jaspersoft ETLcarklounNo ratings yet
- JasperReports Server CP Install GuideDocument90 pagesJasperReports Server CP Install GuideDavid FombellaNo ratings yet
- "Ladders OF LIFE", A Muslim Divination From THE MAE RAS CollectionDocument11 pages"Ladders OF LIFE", A Muslim Divination From THE MAE RAS CollectioncarklounNo ratings yet
- SharePoint Online Office 365 Administration - DemoDocument98 pagesSharePoint Online Office 365 Administration - DemocarklounNo ratings yet
- Spo QS PDFDocument6 pagesSpo QS PDFEric HamisiNo ratings yet
- The Buyer's Guide To Business Intelligence (BI) Software: 2019 EditionDocument30 pagesThe Buyer's Guide To Business Intelligence (BI) Software: 2019 EditioncarklounNo ratings yet
- Product Details for 42CrMo4 SteelDocument2 pagesProduct Details for 42CrMo4 SteelGABRIEL IORDACHINo ratings yet
- Biological Buffer SystemDocument4 pagesBiological Buffer SystemSharm Jarin-AlonzoNo ratings yet
- 1 Graphic Matroids: C D e F C D H eDocument6 pages1 Graphic Matroids: C D e F C D H eAndreeaIoanaNo ratings yet
- Chapter 3 Musculoskeletal System Part 1Document55 pagesChapter 3 Musculoskeletal System Part 1kamalab04No ratings yet
- Band Pass Filter Lab, A Discussion of The Mechanism of Op-AmpsDocument6 pagesBand Pass Filter Lab, A Discussion of The Mechanism of Op-AmpsJoe O'Hara100% (2)
- Ashpasol SupremeDocument2 pagesAshpasol SupremeAlex K.No ratings yet
- Science 10 - Set 2 - DS 1Document10 pagesScience 10 - Set 2 - DS 1DhejehNo ratings yet
- Portable Appliance Testing (Pat) Report/Certificate: Copy Certificate Certificate Reference NumberDocument3 pagesPortable Appliance Testing (Pat) Report/Certificate: Copy Certificate Certificate Reference NumberPete KomorNo ratings yet
- VB Toolbar Tutorial: Create a Toolbar in Visual BasicDocument25 pagesVB Toolbar Tutorial: Create a Toolbar in Visual BasicRizemmaNo ratings yet
- The Effect of Error Correction On Learners' Ability To Write AccuratelyDocument18 pagesThe Effect of Error Correction On Learners' Ability To Write AccuratelyWiqoyil IslamaNo ratings yet
- Xitron Plugin For TrendsetterDocument16 pagesXitron Plugin For TrendsetterRogerio FerracinNo ratings yet
- Renewable and Sustainable Energy ReviewsDocument13 pagesRenewable and Sustainable Energy ReviewsMohammadreza MalekMohamadiNo ratings yet
- Readings: Decision AnalysisDocument44 pagesReadings: Decision AnalysisPierre Moreno SotoNo ratings yet
- HTML (Web Technology)Document59 pagesHTML (Web Technology)D-sumanNo ratings yet
- Ad 7780Document16 pagesAd 7780alcplmNo ratings yet
- Singh 2017Document22 pagesSingh 2017PutriMutiaRizkiNo ratings yet
- FFHDocument763 pagesFFHnilesh2215No ratings yet
- AGK 100 W Amerzine BW - CS - 11Document2 pagesAGK 100 W Amerzine BW - CS - 11David Ortiz de Zevallos100% (2)
- Aircraft Gas Turbine EnginesDocument9 pagesAircraft Gas Turbine EnginesmgskumarNo ratings yet
- Alexandra Elena Plesu (Bonet Ruiz) PHD ThesisDocument278 pagesAlexandra Elena Plesu (Bonet Ruiz) PHD ThesisThắng MinerNo ratings yet
- Bally 5500 SetUpandOperationDocument34 pagesBally 5500 SetUpandOperationFreder AngelNo ratings yet
- Mathematical ProgrammingDocument90 pagesMathematical ProgrammingHidden heiderNo ratings yet
- DISOCONT® Tersus Weighfeeder Instruction Manual bvh2407gbDocument338 pagesDISOCONT® Tersus Weighfeeder Instruction Manual bvh2407gbMizi KoNo ratings yet
- Mathcad - Drilled Shaft PDFDocument14 pagesMathcad - Drilled Shaft PDFHeak HorNo ratings yet
- Phylogenetic studies of Mammillaria provide new insightsDocument13 pagesPhylogenetic studies of Mammillaria provide new insightsA Man ZedNo ratings yet
- Improve The Efficiency of Boiler by Reduce The Moisture in Bagasse IJERTCONV6IS07115Document8 pagesImprove The Efficiency of Boiler by Reduce The Moisture in Bagasse IJERTCONV6IS07115PrateekNo ratings yet
- Pricing Determination Procedure PDFDocument62 pagesPricing Determination Procedure PDFTaslimNo ratings yet
- Apr24-3g CDocument4 pagesApr24-3g COscar Payan ViamonteNo ratings yet