0% found this document useful (0 votes)
95 views27 pagesUnderstanding Penetration Testing Basics
Uploaded by
abdosabaai1Copyright
© © All Rights Reserved
We take content rights seriously. If you suspect this is your content, claim it here.
Available Formats
Download as PPT, PDF, TXT or read online on Scribd
0% found this document useful (0 votes)
95 views27 pagesUnderstanding Penetration Testing Basics
Uploaded by
abdosabaai1Copyright
© © All Rights Reserved
We take content rights seriously. If you suspect this is your content, claim it here.
Available Formats
Download as PPT, PDF, TXT or read online on Scribd
- Introduction to Penetration Testing
- What is a Penetration Test?
- Why Conduct a Penetration Test?
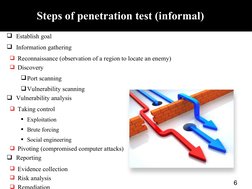
- Steps of Penetration Test (Informal)
- White Hat, Black Hat, Gray Hat
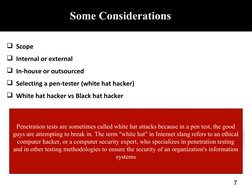
- Some Considerations
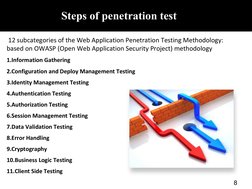
- Detailed Steps of Penetration Test
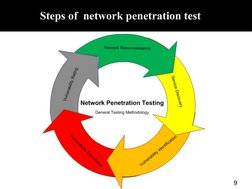
- Steps of Network Penetration Test
- General Steps of Penetration Test
- Introduction to Penetration Testing Tools
- Kali Linux
- Installing Kali Linux
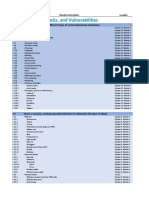
- Penetration Testing Tools
- Maltego
- WHOIS Service
- Vega
- Hydra: Brute Force Attack
- References