Professional Documents
Culture Documents
McAfee - Conficker - Note To Customers
McAfee - Conficker - Note To Customers
Uploaded by
ajfaojfsaoaOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
McAfee - Conficker - Note To Customers
McAfee - Conficker - Note To Customers
Uploaded by
ajfaojfsaoaCopyright:
Available Formats
Alert
McAfee Avert Labs Protecting yourself from the Conficker worm
Lately we have seen lots of media coverage on how the Conficker worm is going to cause havoc on April 1st. The Conficker worm, formally named W32/Conficker.worm, started infecting systems late last year by exploiting a vulnerability in Microsoft Windows. Since then we have seen a couple of variants of this worm and lots of binaries that carry this malicious payload. Conficker.C is the latest variant; it will change the behavior of its call-home protocol on Wednesday, April 1st. Conficker may use this protocol to update itself to include some as-yet unknown functionality. McAfee already offers protection from this worm in its endpoint and network products. Microsoft has also issued a security update to patch the vulnerability that the Conficker family has used to propagate. The following information will give you an overview of the worm, the steps one can take to clean an infected system, and measures to prevent reinfection.
What is the Conficker worm?
The W32/Conficker worm exploits the MS08-067 vulnerability in Microsoft Windows Server Service. If the vulnerability is successfully exploited, it could allow remote code execution when file sharing is enabled. Machines should be patched and rebooted to protect against this worm's reinfecting the system after cleaning, which may require more that one reboot. Upon detecting this worm, reboot the system to clean memory correctly. May require more than one reboot. The worm often creates scheduled tasks to reactivate itself. The worm often uses autorun.inf files to reactivate itself.
We have identified thousands of binaries that carry this payload. Depending on the specific variant, the worm may spread via LAN, WAN, web, or removable drives and by exploiting weak passwords. Conficker disables several important system services and security products and downloads arbitrary files. Computers infected with the worm become part of an army of compromised computers and could be used to launch attacks on web sites, distribute spam, host phishing web sites, or carry out other malicious activities. Conficker.C is the most recent variant of this worm and is dependent on its predecessors, the .A and .B variants. Exposure to .C is limited to systems that are still infected with the earlier variants.
Symptoms
Blocks access to security-related sites Locks user out of directory Sends traffic through port 445 on non-Directory Service (DS) servers Denies access to admin shares Places autorun.inf files in recycled directory
Steps to remove Conficker and prevent reinfection
We recommend customers take the following steps to prevent the W32/Conficker.worm from spreading. 1. Clean the infected systems
Use anti-malware solutions such as ToPS for Endpoint to clean the infection. Use the behavioral detections techniques like buffer overflow protection in Host IPS to prevent future infections. This is important because Conficker can propagate via portable media such as infected USB drives. As the media are accessed, the system processes autorun.inf and executes the attack. For more information, read McAfee Avert Labs document Combating Conficker Worm.
2.
Identify systems at risk of infection
You need to identify which systems are at risk. This list includes systems that either are not patched against Microsoft vulnerability MS08-067 or do not have proactive protection controls to mitigate the vulnerability. McAfee Vulnerability Manager and ePolicy Orchestrator can identify systems that are vulnerable and not protected. 3. Limit the threats ability to propagate
By using network IPS in strategic points in your network you can quickly limit the ability of the threat to spread, allowing time for you to either update your client anti-virus signatures or modify policies to block the threat using the behavioral controls. 4. All computers must have Microsoft Security Update MS08-067 installed.
McAfee product coverage for Conficker worm
McAfee Product Coverage The signature (DAT) files include detection and repair for this worm ToPS Endpoint & ToPS Service Buffer overflow protection in scan engine and Generic Buffer Overflow in host IPS are expected to cover code-execution exploits. Host IPS also includes signature for Vulnerability in Server Service Could Allow Remote Code Execution (CVE-2008-4250) Includes coverage for Microsoft Server Service Remote Code Execution Vulnerability" Identifies nodes that have not been patched and denies them access to the network unless they are updated Includes coverage for MS08-067. Identifies machines vulnerable to infection by Conficker as well as machines infected by Conficker C
Network Security Platform (IntruShield)
McAfee Network Access Control (NAC)
McAfee Vulnerability Manager (MVM) McAfee Web Gateway (formerly Webwasher)
Includes signature to detect and block the worm at the gateway
Links and resources
Conficker removal tools and documentation Avert Stinger Tool for Removing Conficker Combating Conficker Worm: Steps to mitigate risks from Conficker McAfee Avert Labs blog entries on Conficker More Comments Regarding Conficker W32/Conficker: Much Ado About Nothing? McAfee Debuts Combating Threats Series What Have We Learned From Past Virus Infections?
New BackDoor Attacks Using PDF Documents Shrinking Patch TimelinesThe Need for HIPS Conficker Worm Using Metasploit Payload To Spread Further MS08-067 Woes McAfee Virus Information Library entries McAfee VIL: W32/Conficker.worm McAfee VIL: MS08-067Microsoft Windows Server Service Please contact your McAfee representative or channel partner with any questions. Call us at 888.847.8766, 24 hours a day, seven days a week.
About McAfee, Inc.
McAfee, Inc., the leading dedicated security technology company, headquartered in Santa Clara, California, delivers proactive and proven solutions and services that secure systems and networks around the world. With its unmatched security expertise and commitment to innovation, McAfee empowers businesses, the public sector, and service providers with the ability to block attacks, prevent disruptions, and continuously track and improve their security.
McAfee, Inc. 3965 Freedom Circle Santa Clara, CA 95054 888 847 8766 www.mcafee.com
McAfee and/or additional marks herein are registered trademarks or trademarks of McAfee, Inc. and/or its affiliates in the US and/or other countries. McAfee Red in connection with security is distinctive of McAfee brand products. All other registered and unregistered trademarks herein are the sole property of their respective owners. 2009 McAfee, Inc. All rights reserved.
You might also like
- ITN Module 16 STDDocument35 pagesITN Module 16 STDnurul husaifahNo ratings yet
- Ethical Hacking and Network DefenseDocument4 pagesEthical Hacking and Network DefenseCristian RamirezNo ratings yet
- Threat Intelligence Report Maze Ransomware Campaign Spoofs Italian Revenue Agency CorrespondenceDocument2 pagesThreat Intelligence Report Maze Ransomware Campaign Spoofs Italian Revenue Agency CorrespondenceNeenu SukumaranNo ratings yet
- Ds Virusscan85iDocument2 pagesDs Virusscan85iThom KunNo ratings yet
- Task 1 - SecurityDocument25 pagesTask 1 - SecurityMuheet zahidNo ratings yet
- ITC263 S Lesson5Document29 pagesITC263 S Lesson5lawerenceNo ratings yet
- CSS10-1ST Quarter - Week 5Document21 pagesCSS10-1ST Quarter - Week 5George Mar Bien AriolaNo ratings yet
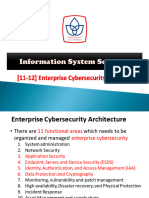
- PU Is Security - 12. Enterprise Cybersecurity ArchitectureDocument42 pagesPU Is Security - 12. Enterprise Cybersecurity ArchitecturealifaldindaNo ratings yet
- Researching Network Attacks and Security Audit ToolsDocument4 pagesResearching Network Attacks and Security Audit ToolsAxelle CarcacheNo ratings yet
- Types of Cyber Attacks E Book PDFDocument10 pagesTypes of Cyber Attacks E Book PDFDwaipayan MojumderNo ratings yet
- Sophos Best Practices For Securing Your Network WPDocument8 pagesSophos Best Practices For Securing Your Network WPankiuNo ratings yet
- Symantec™ Protection Engine For Network Attached Storag 8.1 Getting Started GuideDocument12 pagesSymantec™ Protection Engine For Network Attached Storag 8.1 Getting Started GuideRobertFeneaNo ratings yet
- 09hakin9 09 2012 EN EbookDocument49 pages09hakin9 09 2012 EN EbookcristianorpjNo ratings yet
- CiscoDocument73 pagesCiscoMohamed WahiebNo ratings yet
- CyberSecurity Report (Final)Document53 pagesCyberSecurity Report (Final)Pavan KumarNo ratings yet
- Chapter 7Document4 pagesChapter 7Khánh LyNo ratings yet
- 1.0 Computer Network Security Deployment RequirementsDocument12 pages1.0 Computer Network Security Deployment RequirementsMuhammad AdamNo ratings yet
- Why We Need Security For MacDocument6 pagesWhy We Need Security For MaceScan Anti-VirusNo ratings yet
- Tema 1.4 - Software MaliciosoDocument17 pagesTema 1.4 - Software Maliciosojuanchen2910No ratings yet
- Cns Assignment 2 17F106: FirewallsDocument4 pagesCns Assignment 2 17F106: FirewallsGautaman cricNo ratings yet
- "Firewall": A Seminar Report OnDocument15 pages"Firewall": A Seminar Report OnkumarNo ratings yet
- "Firewall": A Seminar Report OnDocument15 pages"Firewall": A Seminar Report OnkumarNo ratings yet
- "Firewall": A Seminar Report OnDocument15 pages"Firewall": A Seminar Report OnkumarNo ratings yet
- Lab - Researching Network Attacks and Security Audit ToolsDocument4 pagesLab - Researching Network Attacks and Security Audit ToolsAlvaro Avila QuirosNo ratings yet
- Lab 3Document4 pagesLab 3Shiv PatelNo ratings yet
- Important Question Ethical HackingDocument27 pagesImportant Question Ethical Hackingsuthojuakhil21No ratings yet
- Building Firewall Application To Enhance The Cyber Security: Research ProposalDocument21 pagesBuilding Firewall Application To Enhance The Cyber Security: Research ProposalruhanNo ratings yet
- CSS Unit-5Document28 pagesCSS Unit-5Vivek TripathiNo ratings yet
- Network OSDocument5 pagesNetwork OSEmmalyn TestaNo ratings yet
- Miercom Preso Interop NYC NGFW ATP 0900 1OCT2014Document39 pagesMiercom Preso Interop NYC NGFW ATP 0900 1OCT2014lugmarefNo ratings yet
- Palo AltoDocument5 pagesPalo AltoReyShandilyaNo ratings yet
- The Logicnow Cyber Threat Guide: Nine Types of Internet Threats and How To Stop ThemDocument44 pagesThe Logicnow Cyber Threat Guide: Nine Types of Internet Threats and How To Stop ThemsunbratNo ratings yet
- Avoid Being Affected by Rogue Security Software & Scareware: Mcafee Malware Support - Best Practices SeriesDocument4 pagesAvoid Being Affected by Rogue Security Software & Scareware: Mcafee Malware Support - Best Practices SeriesLuis Miguel Arce HuamanchumoNo ratings yet
- Kaspersky Small Office Security 2019 - Datasheet IIDocument2 pagesKaspersky Small Office Security 2019 - Datasheet IIelpirata666No ratings yet
- 300-206 Senss New QuestionsDocument26 pages300-206 Senss New QuestionsvelramsenNo ratings yet
- Network Security Testing - CoreDocument2 pagesNetwork Security Testing - Core7h3rAmNo ratings yet
- Datasheet EPP Panda SecurityDocument2 pagesDatasheet EPP Panda SecurityvietNo ratings yet
- 2-Network Defense FundamentalsDocument45 pages2-Network Defense FundamentalsMattNo ratings yet
- Firewalls: Web Technologies Assignment 2 First Term 2011-2012Document6 pagesFirewalls: Web Technologies Assignment 2 First Term 2011-2012sherrysherryNo ratings yet
- Module 16 - Network Security FundamentalsDocument26 pagesModule 16 - Network Security FundamentalsAnson SooNo ratings yet
- CITS1003 6 VulnerabilitiesDocument34 pagesCITS1003 6 VulnerabilitiesPhyo MinNo ratings yet
- Ransomware Prevention RecommendationsDocument2 pagesRansomware Prevention RecommendationsmufeedNo ratings yet
- Red Team TrainingDocument16 pagesRed Team TrainingFernando da Costa CorreaNo ratings yet
- Atomic Secured LinuxDocument5 pagesAtomic Secured Linuxjayarajan100% (1)
- Firewall Leak TestingDocument6 pagesFirewall Leak TestingdasxaxNo ratings yet
- Extra Security Concerns Can Install Macintosh Versions of Anti-Virus, Anti-Malware and Firewall ProgramsDocument3 pagesExtra Security Concerns Can Install Macintosh Versions of Anti-Virus, Anti-Malware and Firewall ProgramspetrutyNo ratings yet
- Ransomware - Ransomware Protection GuideDocument7 pagesRansomware - Ransomware Protection GuideDeep PNo ratings yet
- Chapter 5 To 6 PDF-1Document33 pagesChapter 5 To 6 PDF-1Tora SarkarNo ratings yet
- Thical Hacking ToolsDocument8 pagesThical Hacking Toolsmuna cliffNo ratings yet
- Cymulate's Vectors BrochureDocument3 pagesCymulate's Vectors BrochureShashibhushan ShettyNo ratings yet
- Practice: Safe and Efficient Use of The InternetDocument12 pagesPractice: Safe and Efficient Use of The InternethmsatNo ratings yet
- In The Wake of Solarwinds CompromiseDocument10 pagesIn The Wake of Solarwinds Compromisealfred.x.andrewsNo ratings yet
- The Basics of Virtualization SecurityDocument4 pagesThe Basics of Virtualization Securitygh0stwareNo ratings yet
- Update and Optimise Network Security: Inside This ReadingDocument7 pagesUpdate and Optimise Network Security: Inside This ReadingTarik ShiguteNo ratings yet
- Unit IVDocument15 pagesUnit IVmenakarameshNo ratings yet
- Securing The Endpoint:: A Guide To Endpoint Threats and Best PracticesDocument5 pagesSecuring The Endpoint:: A Guide To Endpoint Threats and Best PracticesSteve BrownNo ratings yet
- WeekDocument58 pagesWeekMaaz ChowdhryNo ratings yet
- Endpoint Security Solution GuideDocument21 pagesEndpoint Security Solution GuideGăûřăv Wolvarine ShăřmăNo ratings yet
- Ecommerce and Web Security (Cber 705) : Assignment # 1Document5 pagesEcommerce and Web Security (Cber 705) : Assignment # 1Mohit SangwanNo ratings yet
- List Anti Rootkit & AntiVirus For Ubuntu, Linux & BSD (Edition 2018)From EverandList Anti Rootkit & AntiVirus For Ubuntu, Linux & BSD (Edition 2018)No ratings yet
- Cơ Sở Toán Học Cho Mật Mã - Huỳnh Trọng ThưaDocument34 pagesCơ Sở Toán Học Cho Mật Mã - Huỳnh Trọng ThưaHồng HuyNo ratings yet
- Fundamentals of CNC Machining PDFDocument256 pagesFundamentals of CNC Machining PDFentityparadigm99No ratings yet
- WpfappdevDocument223 pagesWpfappdevuglys beauNo ratings yet
- Data Mining Applications in PDFDocument23 pagesData Mining Applications in PDFSHAIK CHAND PASHANo ratings yet
- Mergesort: 7/11/2019 Mitra Kabir, Dept. of CSE, DU 1Document9 pagesMergesort: 7/11/2019 Mitra Kabir, Dept. of CSE, DU 1Sadia AfreenNo ratings yet
- Unicycle Model and ControlDocument27 pagesUnicycle Model and ControlmatteoragniNo ratings yet
- Concept of Artificial IntelligenceDocument3 pagesConcept of Artificial IntelligenceavanthikancheriNo ratings yet
- A - An - The or Zero Article Basic Rules + Practice + KEYDocument1 pageA - An - The or Zero Article Basic Rules + Practice + KEYSam FairireNo ratings yet
- AKREDITASIDocument261 pagesAKREDITASIayamqNo ratings yet
- UbcpDocument39 pagesUbcpLivjot SandhuNo ratings yet
- Manual de Usuario FinalDocument125 pagesManual de Usuario FinalminagutiNo ratings yet
- UX-F5B Data Sheet: V 8 KV, I 350 Ma High-Frequency and High-Voltage Rectifier DiodeDocument5 pagesUX-F5B Data Sheet: V 8 KV, I 350 Ma High-Frequency and High-Voltage Rectifier DiodeFrancisco DiazNo ratings yet
- Nissan Patrol Y61 CAN Flash InformationDocument5 pagesNissan Patrol Y61 CAN Flash InformationObd King TgiNo ratings yet
- Schaum S Theory and Problems of State Space and Linear Systems PDFDocument246 pagesSchaum S Theory and Problems of State Space and Linear Systems PDFRajesh Gangwar100% (2)
- Simatic Loadable Driver For CP 341 Modbus ASCII Master With 32-Bit ExtensionsDocument77 pagesSimatic Loadable Driver For CP 341 Modbus ASCII Master With 32-Bit ExtensionsSukrija RazicNo ratings yet
- Introduccion Al Derecho Procesal Penal. 2° Edicion. Binder PDFDocument1,017 pagesIntroduccion Al Derecho Procesal Penal. 2° Edicion. Binder PDFŊayi ĞomezNo ratings yet
- Juniper Networks Design Fundamentals (JNDF)Document3 pagesJuniper Networks Design Fundamentals (JNDF)Amine InpticNo ratings yet
- Facelle Royale PDFDocument2 pagesFacelle Royale PDFJalenNo ratings yet
- DarkSoulsIII Cheat TableDocument95 pagesDarkSoulsIII Cheat TablePetterNo ratings yet
- Harmony Endpoint - DLPDocument2 pagesHarmony Endpoint - DLPGfact MailNo ratings yet
- Release Notes: Bintec Elmeg Ipsec Secure Client (Win32/64)Document2 pagesRelease Notes: Bintec Elmeg Ipsec Secure Client (Win32/64)NoeSaenzNo ratings yet
- Power Quality Improvement Using Statcom ThesisDocument4 pagesPower Quality Improvement Using Statcom Thesisbotav1nakak3100% (2)
- Network Layer Protocols: Arp, Ipv4, Icmp, Ipv6, and Icmpv6: Review QuestionsDocument2 pagesNetwork Layer Protocols: Arp, Ipv4, Icmp, Ipv6, and Icmpv6: Review Questionssathya100% (1)
- Stalking The Efficient Price - HasbrouckDocument24 pagesStalking The Efficient Price - HasbrouckChioh Wenn ShengNo ratings yet
- Oracle XML Publisher FundamentalsDocument442 pagesOracle XML Publisher Fundamentalspratyusha_3100% (1)
- Assessment Summary For Tecnolama Lift Landing DoorsetsDocument1 pageAssessment Summary For Tecnolama Lift Landing DoorsetsFaruk KorkmazNo ratings yet
- R Spatial CheatsheetDocument4 pagesR Spatial Cheatsheetatom108No ratings yet
- Scraping Book Python PDFDocument50 pagesScraping Book Python PDFPablo Pereda GonzalesNo ratings yet
- Introduction To Programming With LEADTOOLSDocument4 pagesIntroduction To Programming With LEADTOOLSBruno CavalcantiNo ratings yet
- Radio Electronics August 1989 PDFDocument100 pagesRadio Electronics August 1989 PDFPierDonneeNo ratings yet