Professional Documents
Culture Documents
Cisco CCNA Security Chapter 1 Exam
Uploaded by
raul29030 ratings0% found this document useful (0 votes)
11 views5 pagesCopyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
11 views5 pagesCisco CCNA Security Chapter 1 Exam
Uploaded by
raul2903Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 5
Cisco CCNA Security, chapter 1 Exam.
Questions and answers 100% correct.
1. What are the basic phases of attack that can be used by a virus or worm in sequential
order?
paralyze, probe, penetrate, persist, and propagate
probe, penetrate, persist, propagate, and paralyze
penetrate, persist, propagate, paralyze, and probe
persist, propagate, paralyze, probe, and penetrate
2. Which two are characteristics of DoS attacks?
They always precede access attacks.
They attempt to compromise the availability of a network, host, or application.
They are difficult to conduct and are initiated only by very skilled attackers.
They are commonly launched with a too
Examples include smurf attacks and ping of death attacks.
3. Users report to the helpdesk that icons usually seen on the menu bar are randomly
appearing on their computer screens. What
displaying these random graphics?
An access attack has occurred.
A virus has infected the computers.
A DoS attack has been launched against the network.
The computers are subject to a reconnaissance attack.
4. What are three types of access attacks?
buffer overflow
ping sweep
port redirection
trust exploitation
port scan
Internet information query
5. What occurs during a spoofing attack?
One device falsifies data to gain access to privileged information.
Large amounts of network traffic are sent to a target device to make reso
unavailable to intended users.
Improperly formatted packets are forwarded to a target device to cause the target
system to crash.
A program writes data beyond the allocated memory to enable the execution of
malicious code.
Cisco CCNA Security, chapter 1 Exam.
Questions and answers 100% correct.
What are the basic phases of attack that can be used by a virus or worm in sequential
paralyze, probe, penetrate, persist, and propagate
probe, penetrate, persist, propagate, and paralyze
penetrate, persist, propagate, paralyze, and probe
persist, propagate, paralyze, probe, and penetrate
Which two are characteristics of DoS attacks? (Choose two.)
They always precede access attacks.
They attempt to compromise the availability of a network, host, or application.
They are difficult to conduct and are initiated only by very skilled attackers.
They are commonly launched with a tool called L0phtCrack.
Examples include smurf attacks and ping of death attacks.
Users report to the helpdesk that icons usually seen on the menu bar are randomly
appearing on their computer screens. What could be a reason that computers are
displaying these random graphics?
An access attack has occurred.
A virus has infected the computers.
A DoS attack has been launched against the network.
The computers are subject to a reconnaissance attack.
What are three types of access attacks? (Choose three.)
Internet information query
What occurs during a spoofing attack?
One device falsifies data to gain access to privileged information.
Large amounts of network traffic are sent to a target device to make reso
unavailable to intended users.
Improperly formatted packets are forwarded to a target device to cause the target
A program writes data beyond the allocated memory to enable the execution of
Cisco CCNA Security, chapter 1 Exam.
What are the basic phases of attack that can be used by a virus or worm in sequential
They attempt to compromise the availability of a network, host, or application.
They are difficult to conduct and are initiated only by very skilled attackers.
Users report to the helpdesk that icons usually seen on the menu bar are randomly
could be a reason that computers are
Large amounts of network traffic are sent to a target device to make resources
Improperly formatted packets are forwarded to a target device to cause the target
A program writes data beyond the allocated memory to enable the execution of
6. What is a characteristic of a Trojan Horse?
A Trojan Horse can be carried in a virus or worm.
A proxy Trojan Horse opens port 21 on the target system.
An FTP Trojan Horse stops anti
A Trojan Horse can be hard to detect because it closes when the application that
launched it closes.
7. Which phase of worm mitigation requires
the network to slow down or stop the worm and prevent currently infected hosts from
targeting and infecting other systems?
containment phase
inoculation phase
quarantine phase
treatment phase
8. Which two statements are characteristics of a virus?
A virus typically requires end
A virus has an enabling vulnerability, a propagation mechanism, and a payload.
A virus replicates itself by independently exploiting vulnerabilities
A virus provides the attacker with sensitive data, such as passwords.
A virus can be dormant and then activat
9. What is a ping sweep?
A ping sweep is a network scanning tech
range of IP addresses.
A ping sweep is a software application that enables the capture of all network
packets sent across a LAN.
A ping sweep is a scanning technique that examines a range of TCP or UDP p
numbers on a host to detect listening services.
A ping sweep is a query and response protocol that identifies information about a
domain, including the addresses assigned to that domain.
10. Which type of security threat can be described as software that attaches to another
program to execute a specific unwanted function?
virus
worm
proxy Trojan horse
Denial of Service Trojan horse
11. A disgruntled employee is using Wireshark to discover administrative Telnet
usernames and passwords.
Denial of Service
What is a characteristic of a Trojan Horse?
A Trojan Horse can be carried in a virus or worm.
A proxy Trojan Horse opens port 21 on the target system.
An FTP Trojan Horse stops anti-virus programs or firewalls from functioning.
A Trojan Horse can be hard to detect because it closes when the application that
Which phase of worm mitigation requires compartmentalization and segmentation of
the network to slow down or stop the worm and prevent currently infected hosts from
targeting and infecting other systems?
containment phase
Which two statements are characteristics of a virus? (Choose two.)
A virus typically requires end-user activation.
A virus has an enabling vulnerability, a propagation mechanism, and a payload.
A virus replicates itself by independently exploiting vulnerabilities
A virus provides the attacker with sensitive data, such as passwords.
A virus can be dormant and then activate at a specific time or date.
A ping sweep is a network scanning technique that indicates the live hosts in a
range of IP addresses.
A ping sweep is a software application that enables the capture of all network
packets sent across a LAN.
A ping sweep is a scanning technique that examines a range of TCP or UDP p
numbers on a host to detect listening services.
A ping sweep is a query and response protocol that identifies information about a
domain, including the addresses assigned to that domain.
Which type of security threat can be described as software that attaches to another
program to execute a specific unwanted function?
proxy Trojan horse
Denial of Service Trojan horse
A disgruntled employee is using Wireshark to discover administrative Telnet
usernames and passwords. What type of network attack does this describe?
Denial of Service
virus programs or firewalls from functioning.
A Trojan Horse can be hard to detect because it closes when the application that
compartmentalization and segmentation of
the network to slow down or stop the worm and prevent currently infected hosts from
A virus has an enabling vulnerability, a propagation mechanism, and a payload.
A virus replicates itself by independently exploiting vulnerabilities in networks.
A virus provides the attacker with sensitive data, such as passwords.
e at a specific time or date.
nique that indicates the live hosts in a
A ping sweep is a software application that enables the capture of all network
A ping sweep is a scanning technique that examines a range of TCP or UDP port
A ping sweep is a query and response protocol that identifies information about a
Which type of security threat can be described as software that attaches to another
A disgruntled employee is using Wireshark to discover administrative Telnet
What type of network attack does this describe?
port redirection
reconnaissance
trust exploitation
12. What occurs during the persist phase of a worm attack?
identification of vulnerable targets
modification of system files and registry settings to ensure that the attack code is
running
transfer of exploit code through an attack vector
extension of the attack to vulnerable neighboring targets
13. What are the three major components of a worm attack?
enabling vulnerability
infecting vulnerability
payload
penetration mechanism
probing mechanism
propagation mechanism
14. A network administrator detects unknown sessions involving port 21 on the
network. What could be causing this security breach?
An FTP Trojan Horse is executing.
A reconnaissance attack is occurring.
A denial of service attack is occurring.
Cisco Security Agent is testing the network.
15. What are three goals of a port scan attack?
disable used ports and services
determine potential vulnerabilities
identify active services
identify peripheral configurations
identify operating systems
discover system passwords
16. How is a Smurf attack conducted?
by sending a large number of packets, overflowing the allocated buffer memory
of the target device
by sending an echo request in an IP packet larger than the maximum packet size
of 65,535 bytes
by sending a large number of ICMP requests to directed broadcast addresses
from a spoofed source address on t
by sending a large number of TCP SYN packets to a target device from a
spoofed source address
trust exploitation
What occurs during the persist phase of a worm attack?
identification of vulnerable targets
modification of system files and registry settings to ensure that the attack code is
er of exploit code through an attack vector
extension of the attack to vulnerable neighboring targets
What are the three major components of a worm attack? (Choose three.)
enabling vulnerability
infecting vulnerability
penetration mechanism
probing mechanism
propagation mechanism
A network administrator detects unknown sessions involving port 21 on the
What could be causing this security breach?
An FTP Trojan Horse is executing.
A reconnaissance attack is occurring.
A denial of service attack is occurring.
Cisco Security Agent is testing the network.
What are three goals of a port scan attack? (Choose three.)
disable used ports and services
determine potential vulnerabilities
identify active services
identify peripheral configurations
identify operating systems
discover system passwords
How is a Smurf attack conducted?
by sending a large number of packets, overflowing the allocated buffer memory
by sending an echo request in an IP packet larger than the maximum packet size
by sending a large number of ICMP requests to directed broadcast addresses
from a spoofed source address on the same network
by sending a large number of TCP SYN packets to a target device from a
spoofed source address
modification of system files and registry settings to ensure that the attack code is
(Choose three.)
A network administrator detects unknown sessions involving port 21 on the
by sending a large number of packets, overflowing the allocated buffer memory
by sending an echo request in an IP packet larger than the maximum packet size
by sending a large number of ICMP requests to directed broadcast addresses
by sending a large number of TCP SYN packets to a target device from a
17. Which access attack method involves a software program attempting to discover a
system password by using an electronic
buffer overflow attack
port redirection attack
Denial of Service attack
brute-force attack
IP spoofing attack
packet sniffer attack
18 Which two network security solutions can be used to mitigate DoS attacks?
two.)
virus scanning
data encryption
anti-spoofing technologies
intrusion protection systems
applying user authentication
19. Which phase of worm mitigation involves terminating the worm process, removing
modified files or system settings that the worm introduced, and patching the
vulnerability that the worm used to exploit
containment
inoculation
quarantine
treatment
20. Which characteristic best describes the network security Compliance domain as
specified by the ISO/IEC?
the integration of security into applications
an inventory and classification scheme for information assets
the restriction of access
data
the process of ensuring conformance wit
standards, and regulations
21. Which statement describes phone freaking?
A hacker uses password
dialup account.
A hacker gains unauthorized access to networks via wireless access points.
A hacker mimics a tone using a whistle to make free long
analog telephone network.
A hacker uses a program that automatically scans telephone numbers within a
local area, dialing each one in search of computers, bulletin board systems, and
fax machines.
Which access attack method involves a software program attempting to discover a
system password by using an electronic dictionary?
buffer overflow attack
port redirection attack
Denial of Service attack
force attack
tack
packet sniffer attack
Which two network security solutions can be used to mitigate DoS attacks?
spoofing technologies
intrusion protection systems
applying user authentication
Which phase of worm mitigation involves terminating the worm process, removing
modified files or system settings that the worm introduced, and patching the
vulnerability that the worm used to exploit the system?
Which characteristic best describes the network security Compliance domain as
specified by the ISO/IEC?
the integration of security into applications
an inventory and classification scheme for information assets
the restriction of access rights to networks, systems, applications, functions, and
the process of ensuring conformance with security information policies,
standards, and regulations
Which statement describes phone freaking?
A hacker uses password-cracking programs to gain access to a computer via a
A hacker gains unauthorized access to networks via wireless access points.
A hacker mimics a tone using a whistle to make free long-distance calls on an
analog telephone network.
gram that automatically scans telephone numbers within a
local area, dialing each one in search of computers, bulletin board systems, and
Which access attack method involves a software program attempting to discover a
Which two network security solutions can be used to mitigate DoS attacks? (Choose
Which phase of worm mitigation involves terminating the worm process, removing
modified files or system settings that the worm introduced, and patching the
Which characteristic best describes the network security Compliance domain as
rights to networks, systems, applications, functions, and
h security information policies,
cracking programs to gain access to a computer via a
A hacker gains unauthorized access to networks via wireless access points.
distance calls on an
gram that automatically scans telephone numbers within a
local area, dialing each one in search of computers, bulletin board systems, and
22. Which two statements describe access attacks?
Port redirection attacks use a network adapter card in promiscuous mode to
capture all network packets that are sent across a LAN.
Password attacks can be implemented using brute
Horses, or packet sniffers.
Buffer overflow attacks write data beyond the allocated buffer memory to
overwrite valid data or exploit systems to execute malicious code.
Port scanning attacks scan a range of TCP or UDP port numbers on a host to
detect listening services.
Trust exploitation attacks can use a laptop acting as a rogue access point to
capture and copy all network traffic in a public location on a wireles
Which two statements describe access attacks? (Choose two.)
Port redirection attacks use a network adapter card in promiscuous mode to
capture all network packets that are sent across a LAN.
Password attacks can be implemented using brute-force attack methods, Tro
Horses, or packet sniffers.
Buffer overflow attacks write data beyond the allocated buffer memory to
overwrite valid data or exploit systems to execute malicious code.
Port scanning attacks scan a range of TCP or UDP port numbers on a host to
detect listening services.
Trust exploitation attacks can use a laptop acting as a rogue access point to
capture and copy all network traffic in a public location on a wireles
Port redirection attacks use a network adapter card in promiscuous mode to
force attack methods, Trojan
Buffer overflow attacks write data beyond the allocated buffer memory to
overwrite valid data or exploit systems to execute malicious code.
Port scanning attacks scan a range of TCP or UDP port numbers on a host to
Trust exploitation attacks can use a laptop acting as a rogue access point to
capture and copy all network traffic in a public location on a wireless hotspot.
You might also like
- Wireless and Mobile Hacking and Sniffing TechniquesFrom EverandWireless and Mobile Hacking and Sniffing TechniquesNo ratings yet
- CompTIA Network Plus Training Kit Exam N10-005Document704 pagesCompTIA Network Plus Training Kit Exam N10-005bibivee50% (2)
- CEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021From EverandCEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021No ratings yet
- Ethical Hacking TrainingDocument31 pagesEthical Hacking TrainingKhoi DangNo ratings yet
- A Java Based Network Intrusion Detection System (IDS)Document14 pagesA Java Based Network Intrusion Detection System (IDS)Santosh ParsaNo ratings yet
- Think HackerDocument10 pagesThink HackerDarryl RheaNo ratings yet
- J1939 PresentationDocument46 pagesJ1939 Presentationjrsimma90% (10)
- Test - Palo Alto Networks Certified Network Security Engineer (PCNSE) : Exam Practice QuestionsDocument19 pagesTest - Palo Alto Networks Certified Network Security Engineer (PCNSE) : Exam Practice QuestionsgurungeNo ratings yet
- TCP IP VulnerabilitiesDocument17 pagesTCP IP VulnerabilitiesHemant Sudhir WavhalNo ratings yet
- How to Defeat Advanced Malware: New Tools for Protection and ForensicsFrom EverandHow to Defeat Advanced Malware: New Tools for Protection and ForensicsNo ratings yet
- Ethical HackingDocument109 pagesEthical HackingRameswar ReddyNo ratings yet
- Certified Ethical Hacker (CEH) Preparation Guide: Lesson-Based Review of Ethical Hacking and Penetration TestingFrom EverandCertified Ethical Hacker (CEH) Preparation Guide: Lesson-Based Review of Ethical Hacking and Penetration TestingRating: 5 out of 5 stars5/5 (4)
- Linux Malware Incident Response: A Practitioner's Guide to Forensic Collection and Examination of Volatile Data: An Excerpt from Malware Forensic Field Guide for Linux SystemsFrom EverandLinux Malware Incident Response: A Practitioner's Guide to Forensic Collection and Examination of Volatile Data: An Excerpt from Malware Forensic Field Guide for Linux SystemsNo ratings yet
- Penetration Testing Fundamentals -1: Penetration Testing Study Guide To Breaking Into SystemsFrom EverandPenetration Testing Fundamentals -1: Penetration Testing Study Guide To Breaking Into SystemsNo ratings yet
- Thinking Like A HackerDocument10 pagesThinking Like A HackerDharmsen SoniNo ratings yet
- Common Windows, Linux and Web Server Systems Hacking TechniquesFrom EverandCommon Windows, Linux and Web Server Systems Hacking TechniquesNo ratings yet
- The Certified Ethical Hacker Exam - version 8 (The concise study guide)From EverandThe Certified Ethical Hacker Exam - version 8 (The concise study guide)Rating: 3 out of 5 stars3/5 (9)
- Answers To Ethical Hacker Interview QuestionsDocument5 pagesAnswers To Ethical Hacker Interview Questionstsultim bhutiaNo ratings yet
- Organisational Systems Security: TOPIC 1: Potential Threats To ICT Systems and OrganizationDocument46 pagesOrganisational Systems Security: TOPIC 1: Potential Threats To ICT Systems and Organizationfate99No ratings yet
- NetScaler MasterClass - September 11Document105 pagesNetScaler MasterClass - September 11Cosmin StrezaNo ratings yet
- Ccna SecurityDocument81 pagesCcna SecurityBrahim El-Asri100% (1)
- CCIE Security Tech Lab WKBK v3.0 Ebook UpdatedDocument533 pagesCCIE Security Tech Lab WKBK v3.0 Ebook UpdatedHarish Balakrishnan86% (7)
- Cyberphobia: Identity, Trust, Security and the InternetFrom EverandCyberphobia: Identity, Trust, Security and the InternetRating: 3.5 out of 5 stars3.5/5 (9)
- Practicar Exam Ceh v9 - Prueba2Document28 pagesPracticar Exam Ceh v9 - Prueba2Miguel SorianoNo ratings yet
- Network SecurityDocument23 pagesNetwork SecurityNafisa AhmadNo ratings yet
- CCNA Security Ch01 Quiz AnswersDocument7 pagesCCNA Security Ch01 Quiz Answersdercole69No ratings yet
- Cisco CCNA SecurityDocument85 pagesCisco CCNA SecurityPaoPound HomnualNo ratings yet
- Computer Networks Interview QuestionsDocument12 pagesComputer Networks Interview Questionsapi-3768969100% (1)
- Ceragon - Ip20Document84 pagesCeragon - Ip20sisfNo ratings yet
- Huawei ERAN3 0 DRX Feature IntroductionDocument45 pagesHuawei ERAN3 0 DRX Feature IntroductionssssNo ratings yet
- Ccna Security Examen 1. 100%Document7 pagesCcna Security Examen 1. 100%wamrojasNo ratings yet
- Prueba Cap 1 CCNA SecurityDocument11 pagesPrueba Cap 1 CCNA SecurityGuillermo E Lobo PNo ratings yet
- Answer CCNA Security Chapter 1 Test - CCNAS v1.1: Probe, Penetrate, Persist, Propagate, and ParalyzeDocument10 pagesAnswer CCNA Security Chapter 1 Test - CCNAS v1.1: Probe, Penetrate, Persist, Propagate, and ParalyzeFranco SalernoNo ratings yet
- Cisco CCNA Security Module 1Document7 pagesCisco CCNA Security Module 1pollypolNo ratings yet
- CCNA Security Module 1 100%Document4 pagesCCNA Security Module 1 100%Akbal Larios100% (1)
- Cisco CCNA Security, Chapter 1 Exam. Cisco CCNA Security, Chapter 1 Exam. Cisco CCNA Security, Chapter 1 ExamDocument54 pagesCisco CCNA Security, Chapter 1 Exam. Cisco CCNA Security, Chapter 1 Exam. Cisco CCNA Security, Chapter 1 ExamAlexa JahenNo ratings yet
- CCNA Security - Chapter 1 Exam AnswersDocument6 pagesCCNA Security - Chapter 1 Exam Answersrockynaruto0% (1)
- CCNA Security Chapter 1Document4 pagesCCNA Security Chapter 1GoldenBoy96No ratings yet
- CCNA Security Chapter 1 AssessmentDocument5 pagesCCNA Security Chapter 1 Assessmentp6aes2008100% (2)
- CCNAS Chapter 1 CCNA Security 1Document10 pagesCCNAS Chapter 1 CCNA Security 1Sergiy KalmukNo ratings yet
- Capitulo 1 Ccna Security PDFDocument6 pagesCapitulo 1 Ccna Security PDFRafael RojasNo ratings yet
- CCNA Security v2.0 Chapter 1 Exam AnswersDocument5 pagesCCNA Security v2.0 Chapter 1 Exam AnswersRussell FernandezNo ratings yet
- Reconnaissance Scanning Gaining Access Maintaining Access Clearing TrackDocument11 pagesReconnaissance Scanning Gaining Access Maintaining Access Clearing TrackAlejo LomNo ratings yet
- Cisco CCNA Security All ExamsDocument79 pagesCisco CCNA Security All ExamsLiuwal MuñozNo ratings yet
- CCNAS Module 1 100%Document6 pagesCCNAS Module 1 100%jagaBBNo ratings yet
- 13 17 AnswerDocument31 pages13 17 Answers2187022No ratings yet
- Categories of AttacksDocument4 pagesCategories of AttacksQais Saif QassimNo ratings yet
- Final EndpointDocument11 pagesFinal Endpointoslervillamar06No ratings yet
- Ccna S 2.0Document116 pagesCcna S 2.0loffy hackerNo ratings yet
- Networks and Network SecurityDocument10 pagesNetworks and Network SecurityashishNo ratings yet
- Preguntas Tres Primeros Capitulos Netacad Prueba 1 CCNP3 en InglesDocument27 pagesPreguntas Tres Primeros Capitulos Netacad Prueba 1 CCNP3 en InglesPatricioNo ratings yet
- Habtamu ZelekeDocument9 pagesHabtamu Zelekeናዝራዊ አማኑኤል ጌታቸውNo ratings yet
- 06 - System SecurityDocument43 pages06 - System SecurityMạnh NguyễnNo ratings yet
- Network Security AssignmentDocument4 pagesNetwork Security Assignmentbamie AhmedNo ratings yet
- Exam CEHv10Document30 pagesExam CEHv10Benyhi Deyvi Mantilla FloresNo ratings yet
- Ccna Sec 1.2 ExasDocument27 pagesCcna Sec 1.2 Exasesquirla300No ratings yet
- Source Code Analysis of Worms: Bapu0201@stcloudstate - Edu, Roar0301@stcloudstate - EduDocument12 pagesSource Code Analysis of Worms: Bapu0201@stcloudstate - Edu, Roar0301@stcloudstate - EduEmanuel DiegoNo ratings yet
- Guia Resuelta CEHv9Document37 pagesGuia Resuelta CEHv9Vik PalapaNo ratings yet
- Broadband Network Virus Detection System Based On Bypass MonitorDocument4 pagesBroadband Network Virus Detection System Based On Bypass MonitorJohn GacheruNo ratings yet
- Trusted Digital Circuits: Hardware Trojan Vulnerabilities, Prevention and DetectionFrom EverandTrusted Digital Circuits: Hardware Trojan Vulnerabilities, Prevention and DetectionNo ratings yet
- Penetration Testing Fundamentals-2: Penetration Testing Study Guide To Breaking Into SystemsFrom EverandPenetration Testing Fundamentals-2: Penetration Testing Study Guide To Breaking Into SystemsNo ratings yet
- List Anti Rootkit & AntiVirus For Ubuntu, Linux & BSD (Edition 2018)From EverandList Anti Rootkit & AntiVirus For Ubuntu, Linux & BSD (Edition 2018)No ratings yet
- Modeling Computer Attacks: An Ontology For Intrusion DetectionDocument23 pagesModeling Computer Attacks: An Ontology For Intrusion DetectionTertelie Vasile IonNo ratings yet
- Configuring Answers and Answer GroupsDocument44 pagesConfiguring Answers and Answer GroupsSajjan KumarNo ratings yet
- IptablesDocument31 pagesIptableskosukeNo ratings yet
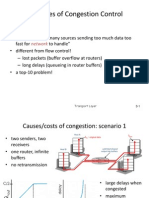
- Computer Networks Chapter 3 Transport Layer - Part I NotesDocument7 pagesComputer Networks Chapter 3 Transport Layer - Part I NotesderguenhartNo ratings yet
- Soal MTCNA Yang Sering KeluarDocument30 pagesSoal MTCNA Yang Sering Keluarirfanmaulana20No ratings yet
- NetEngine AR600 AR6000 Series QoS FeatureDocument65 pagesNetEngine AR600 AR6000 Series QoS FeatureEDWIN GREGORIO MARIN VARGASNo ratings yet
- XPort DS-220314Document6 pagesXPort DS-220314snobic9379No ratings yet
- SharePoint 2013 Build GuideDocument70 pagesSharePoint 2013 Build GuideAngel de BeitíaNo ratings yet
- Principles of Congestion ControlDocument11 pagesPrinciples of Congestion ControlSubhash SagarNo ratings yet
- Internet of Things (Cp5292) UNIT-1 Introduction To IotDocument7 pagesInternet of Things (Cp5292) UNIT-1 Introduction To Iot2021 Batch First YearNo ratings yet
- Interoperability and Vulnerabilities in VOIP Protocol (SIP, H.323)Document7 pagesInteroperability and Vulnerabilities in VOIP Protocol (SIP, H.323)rachanamanitNo ratings yet
- SecurityDocument57 pagesSecurityYovxy MaNo ratings yet
- SoC Module Desc2013Document57 pagesSoC Module Desc2013AndyNo ratings yet
- Duplicate Oracle Duplicate Oracle Database With RMANDatabase With RMANDocument7 pagesDuplicate Oracle Duplicate Oracle Database With RMANDatabase With RMANCesar EduardoNo ratings yet
- 1LAB000592 Transformer Service CoreSense Hydrogen and Moisture Sensor Operating Instruction en Rev E Jan 2017Document60 pages1LAB000592 Transformer Service CoreSense Hydrogen and Moisture Sensor Operating Instruction en Rev E Jan 2017wmqelmen8978No ratings yet
- Computer Networks MCQ QuestionsDocument8 pagesComputer Networks MCQ QuestionsRez HabloNo ratings yet
- Network Protocol 3 PDFDocument4 pagesNetwork Protocol 3 PDFEdison Jr. GaudicosNo ratings yet
- Modules 5 ExamDocument8 pagesModules 5 ExamJayz JoeNo ratings yet
- Soal MikrotikDocument3 pagesSoal MikrotikChung ChinNo ratings yet
- User Manual: Modbus Slave / Modbus TCP Master - ConverterDocument26 pagesUser Manual: Modbus Slave / Modbus TCP Master - ConverterJunaid ArsahdNo ratings yet
- Application Note: Humidity ModulesDocument23 pagesApplication Note: Humidity ModulesEnoNo ratings yet
- Fortisandbox - Administration GuideDocument221 pagesFortisandbox - Administration GuideErnesto BubriskiNo ratings yet