Professional Documents
Culture Documents
Information System Auditing and Assurance: Accounting Information Systems, 4th. Ed
Information System Auditing and Assurance: Accounting Information Systems, 4th. Ed
Uploaded by
Lian ChuaOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Information System Auditing and Assurance: Accounting Information Systems, 4th. Ed
Information System Auditing and Assurance: Accounting Information Systems, 4th. Ed
Uploaded by
Lian ChuaCopyright:
Available Formats
James A. Hall Accounting Information Systems, 4th. Ed.
Chapter Auditing & Assurance
17
CHAPTER 17
INFORMATION SYSTEM AUDITING AND ASSURANCE
As more and more accounting and business systems were automated, it became more and more evident that the field of auditing had to change. As the systems being audited increased their use of technology, new techniques for evaluating them were required. This chapter focuses on computer or information systems (IS) auditing. It begins with a discussion of how the auditing profession has expanded in response to the spread of technology. The objectives of this chapter are: ! to understand the general purpose of an audit and to have a firm grasp of the basic conceptual elements of the audit process; to know the difference between internal and external auditing and to be able to explain the relationship between these two types of auditing; to understand how auditing objectives and tests of control are determined by the control structure of the firm that is being audited; to be familiar with the audit objective and tests of control for each of the nine general control areas; to understand the auditing techniques that are used to verify the effective functioning of application controls; and to understand the auditing techniques used to perform substantive tests in a CBIS environment.
Study Notes Prepared by H. M. Savage
South-Western Publishing Co., 2004
Page 17-1
James A. Hall Accounting Information Systems, 4th. Ed.
Chapter Auditing & Assurance
17
Notes I. Attest Services versus Assurance Services
Because AIS is a prerequisite to the auditing course on many campuses, it is understandable that you not be too sure of the nature and purpose of an aud it. This introduction is, of necessity, brief. It will not take the place of your auditing course. But it is a start. Read carefully to distinguish between traditional auditing (the attest function) and the emerging field of assurance services. Fig. 17-1, on page 861, is a schem atic of the relationship. A. W hat is a Financial Audit? Auditing is a form of independent attestation (or verification) performed by an expert who expresses an opinion about the fairness of a co mpa nys financial statements. Independence is of great importance since it is fundamental to stakeholder confidence in the audit opinion. Conduct of an audit involves studying the client organization, evaluating the internal controls of the system to see how it works, and evaluating the information in the system. B. Auditing Standards You are familiar with GAAP, Generally Accepted Accounting Principles. These must be followed by companies required by SEC regulation to provide financial statements. In order for users to be confident that the audit did examine the books thoroughly, the external auditor must follow GA AS, Gen erally Accepted Auditing Standards. This section introduces GAAS, in particular, the Statements on Auditing Standards issued by the AICPA as needed, since 1972. Early in the text you were introduced to SAS 78. Read carefully the discussion related to Table 17-1, on page 863. C. External Auditing versus Internal Auditing Many of the same tasks are often carried out by external auditors and by individuals who are employees of the client. These employees who are involved in audit-related activities are called internal auditors. Although employed by the client firm, many duties can be conducted with a reasonable level of objectivity if the internal auditors report to the audit committee of the board of trustees, and not to the controller, who is responsible for the accounting system. Rather than representing the interests of
Study Notes Prepared by H. M. Savage
South-Western Publishing Co., 2004
Page 17-2
James A. Hall Accounting Information Systems, 4th. Ed.
Chapter Auditing & Assurance
17
Notes
external stakeholders, they serve the best interests of the client organ ization itself. Your text presents the standard definition of auditing and discusses the key elements. This is brief but good. D. W hat is an Information T echnology (IT) Aud it? IT auditing refers to the part of an audit that involves the computerized elements of an accounting information system. It is here that the elements of auditing are present. Note in particular, the discussion of aud it objectives. See Table 17-2, on page 866. E. The Struc ture of an IT Aud it Fig. 17-2, on page 867, is a schem atic of an IT audit showing three phases: aud it planning, tests of con trols (tests of the system), and substantive testing (tests of the data in the system). Each of these phases is comprised of several steps. The discussion is clear.
II.
Assessing Audit Risk and Designing Tests of Controls
Several co ncerns face an a uditorthat material errors do exist in the accounting system and that the audit will not detect them. The text discusses audit riskthe probability that an auditor will render a clean audit opinion when material errors exist. A. Aud it Risk Comp onents There are three basic components of audit risk:
! ! !
inherent risk, control risk, and detection risk.
There are two b asic types of aud it tests: tests of con trols, which determine whether the internal controls are operating correctly (i.e., these are tests of the accounting system), and substantive tests, which determine whether the data fairly reflects the organizations financial affairs (i.e., these are tests of the accounting information in the system).
Study Notes Prepared by H. M. Savage
South-Western Publishing Co., 2004
Page 17-3
James A. Hall Accounting Information Systems, 4th. Ed.
Chapter Auditing & Assurance
17
Notes
B. Relationship between Tests of Controls and Substantive T ests The results of the tests of controls have great impact on the extent of substantive testing required. If the internal controls system is judged to be stron g, less substantive testing is needed. Or, if the controls are deemed to be weak, more testing m ust be d one to judge the data.
III.
Tests of General Controls
This section of the text follows the framework develop ed in Chapter 15 with regard to general controls. The next section focuses on application controls. But first, you must understand the concept of an audit objective. A. Developing Audit Objectives The ob jective(s) of any audit test relates to the exposure s that may threaten the organizations activities an d the internal co ntrols that are in place. The approach that will be taken will relate risk, control, the audit objective, and the appropriate aud it procedure. Significant professiona l judgm ent is required in practice. Table 17-3, on pages 870-01, summarizes exposures and controls in a CBIS environment. Use this as your guide for reading the related narrative. For each area of control, the objectives and procedures are presented. B. Testing Operating System Controls Recall the objectives of operating system that we discussed in Chapter 15. The relevant control techniques are intended to verify that policies are strong enough to protect the operating system. T hese controls ap pear quite rigorous. Bu t one d isaster will make you a believer. The aud it objectives and aud it procedures are p resented for ea ch of five areas: access privileges, p assw ord policy, virus control, aud it trail con trols, and fault tolerance. C. Testing Data M anagement Controls Data managem ent controls are com prised of backup con trols and access controls. The need for bo th should be clear.
Study Notes Prepared by H. M. Savage
South-Western Publishing Co., 2004
Page 17-4
James A. Hall Accounting Information Systems, 4th. Ed.
Chapter Auditing & Assurance
17
Notes
D. Testing Organizational Structure Co ntrols W e have discussed several times the fact that the location of separation of duties shifts in the CBIS environment. This is reflected in the tests examined here. E. Testing System D evelo pme nt Controls This type of control is extremely important for confidence in the output of the system. N ot only must procedures be followed throughout the SDLC , but the system m ust have been justified and documented. The review of SDLC documentation is a good check on the process itself. F. Testing System M aintenance C ontro ls The seventh stage of the SDLC is system maintenance. During the systems life, things often need to be changed. Just as the recording of financial transac tions sho uld only happen if authorized, changes in an existing system, i.e., system maintenance, should occur only with proper authorization and under strict controlin order to protect system integrity. The techniques discussed assume some programming knowledge. G. Testing Co mpu ter Center Se curity The objectives of computer center security should be obvious, by now. T he tests that must be made will not be very exciting, but without the computer center, most firms would be unable to conduct business and would soon close their doors. This is true both from physical construction and b ackup po wer to full scale disaster recovery. Note the imp ortance given to critical applications, first discussed in Chapter 15 . The disaster recovery plan must be tested often because of changes in the organization, the environment, the system, and the personnel involved. H. Testing Internet and Intranet Controls There is little po int in com municating electronically if the information is not transferred correctly or if it can be easily intercepted. Communication controls are designed to assure accurate communication, prevent unauthorize d acc ess, and make any data that is intercepted worthless.
Study Notes Prepared by H. M. Savage
South-Western Publishing Co., 2004
Page 17-5
James A. Hall Accounting Information Systems, 4th. Ed.
Chapter Auditing & Assurance
17
Notes
I. Testing Electronic Da ta Interchange Co ntrols The value of ED I has been d iscussed before. If it is of benefit to trad ing partners, it is worth pro tecting. Authorization, validation, and access are key factors. W ith the absence of a paper trail, the issue of the aud it trail deserves special attention. J. Testing Person al Co mpu ter Co ntrols The problems inherent in the personal computer enviro nment should not be underestimated . The re is a connection with end -user controls that were discussed in Chapter 16. The text focuses on three areas of concern that are of special importance in the perso nal compu ter environm ent: access, segregation of duties, backup, and systems development and ma intenanc e. Read this carefully. Yo u will work in organizations littered with personal computers.
IV.
Testing Computer Applications
The last area of exposure to be considered involves app lication controls. All that has been covered up to now related to gen eral co ntrols. Application controls fall into two classes: tests of application controls, and tests of the transaction details and account balances. The latter are substantive tests and are covered in the next section of the chapter. Tests of controls are considered below. W hen com puterized, or automated , accounting systems first made their entrance into the business world, auditors were frequently faced with a black box that they did not understand but which processed much of the data about which they were asked to voice an opinion. Initially they audited around the computer by observing input and observing output and checking for mutual consistency. Although adeq uate, it was nonetheless inefficient. Also, the evaluation of the internal contro l system wa s hampered. It was o ften impossible to trace an aud it trail through the automated parts of the system. If an application had a material effect on the financial statements, auditing around the computer may not have been acceptable. The second approach to auditing computer systems has been called auditing through the compu ter. It requires the ability to trace transaction paths from input to output through all parts of the systemmanual and automated. The flow of data must be verified as it moves through the system, and the contents of machine readable files must be examined. Internal contro ls are tested as they operate on th e data. The black box is gone.
Study Notes Prepared by H. M. Savage
South-Western Publishing Co., 2004
Page 17-6
James A. Hall Accounting Information Systems, 4th. Ed.
Chapter Auditing & Assurance
17
Notes
The current trend is toward auditing with the co mputer, using the computer as a tool of the audit. The comp uter is used as a tool for examining the data, accessing the files, retrieving records at will, extracting statistical samples, and performing test calculations. Use of the computer has made feasible a great many procedures which would otherwise have been impractical from a clerical standpoint. The major problem that this last method creates is that practicing auditors are required to have extensive and up-to-date knowledge of computer systems. It is difficult to stay ab reast of changes in technology. This has created a new demand for continuing professional education. A. Black Box Approach No te the ad vantag es and disadvantag es of this approach. B. W hite Box Approach Auditing through the computer can be called the white box approach to contrast it to the black box approach. A numb er of tests of controls are discussed. T he purposes of these different tests will help you appreciate the concerns faced by an auditor. C. W hite Box Testing Techniques Five proven procedures are described:
! ! ! ! !
test data method base case system evaluation, tracing, integrated test facility, and parallel simulations.
These are very complex techniques. Focus on the key objectives. The first three are variations of the same method. They all work through the computer. The last two actually use the computer as a tool of the auditauditing with the computer. D. The Integrated Test Facility The integrated test facility builds auditability into the system. Both the logic of the application and the controls are tested during normal operation. The com puter is now p art of the audit processthe audit is being done with the computer. Focus on the advantage s and disadvantag e of this method . You will learn more about it in your auditing course.
Study Notes Prepared by H. M. Savage
South-Western Publishing Co., 2004
Page 17-7
James A. Hall Accounting Information Systems, 4th. Ed.
Chapter Auditing & Assurance
17
Notes
E. Parallel Simulation Parallel simulation, as the name implies, imitates the app lication under review . It must be written to perform the same steps as the application so that results can be comp ared. If the real system and the parallel yield the same output, then you would have confidence that the real system is OK.
V.
Substantive Testing Techniques
The second major type of audit tests, after the tests of co ntrols, are the substantive tests which are used to verify the $$$$ on the financial statements and in the accounts. Several examples are given in the text. Because these tests evaluate the data in the system , there must be w ays to get at it. A. The Imb edd ed A udit M odule The imbed ded aud it modu le is a set of specially written computer instructions built into the client software to extract specified types of data for later testing. Read through the advantages and disad vantag es carefully. B. Generalized Audit Software Gen eralized au dit software refers to a number of programs developed as tools for auditors. Because of the need to repeatedly perform ba sic audit tasks, many public accounting firms have created such packages. The text describes the type of functions built in. Concentrate on the tasks that can be performed by G AS, not the ac cess to file structures.
Review Questions for Chapter 17: 1-29 Discussion Questions for Chapter 17: 1-16
Study Notes Prepared by H. M. Savage
South-Western Publishing Co., 2004
Page 17-8
You might also like
- Solution Manual For Information Technology Auditing 4th Edition by HallDocument20 pagesSolution Manual For Information Technology Auditing 4th Edition by HallZenn Maia Guerrero0% (1)
- Auditing Information Systems: Enhancing Performance of the EnterpriseFrom EverandAuditing Information Systems: Enhancing Performance of the EnterpriseNo ratings yet
- Chiquita FARC Accounting Expert ReportDocument68 pagesChiquita FARC Accounting Expert ReportPaulWolfNo ratings yet
- Answer Key in Applied Auditing by Cabrera 2006 EditionDocument271 pagesAnswer Key in Applied Auditing by Cabrera 2006 EditionGwyneth Ü Elipanio100% (14)
- Chapter 5 Is Audit As Review ManagementDocument7 pagesChapter 5 Is Audit As Review ManagementSteffany RoqueNo ratings yet
- Information Systems Auditing: The IS Audit Testing ProcessFrom EverandInformation Systems Auditing: The IS Audit Testing ProcessRating: 1 out of 5 stars1/5 (1)
- The Operational Auditing Handbook: Auditing Business and IT ProcessesFrom EverandThe Operational Auditing Handbook: Auditing Business and IT ProcessesRating: 4.5 out of 5 stars4.5/5 (4)
- A Guide to Effective Internal Management System Audits: Implementing internal audits as a risk management toolFrom EverandA Guide to Effective Internal Management System Audits: Implementing internal audits as a risk management toolRating: 3 out of 5 stars3/5 (5)
- PlanningDocument121 pagesPlanningThessaloe B. FernandezNo ratings yet
- ACCA F8 Audit and Assurance Revision Notes 2017 PDFDocument84 pagesACCA F8 Audit and Assurance Revision Notes 2017 PDFJudithNo ratings yet
- CH 01 Solution Manual Information Technology Auditing 2nd Ed James Hall - EDP Auditing Class - Jakarta State UniversityDocument21 pagesCH 01 Solution Manual Information Technology Auditing 2nd Ed James Hall - EDP Auditing Class - Jakarta State UniversitySjifa Aulia80% (10)
- Chapter 1 IT AuditDocument20 pagesChapter 1 IT AuditMr Siwada S ThabeloNo ratings yet
- ICT Assignment 1Document4 pagesICT Assignment 1AndiNo ratings yet
- (SM) Chapter 1Document20 pages(SM) Chapter 1randomlungs121223No ratings yet
- 965QG Volume 4 Auditing in An IT Environment 2Document53 pages965QG Volume 4 Auditing in An IT Environment 2Jerwin ParallagNo ratings yet
- Quick Guide To Auditing in An IT EnvironmentDocument8 pagesQuick Guide To Auditing in An IT EnvironmentKarlayaanNo ratings yet
- QG To IT Audit 9.1Document81 pagesQG To IT Audit 9.1Rhad EstoqueNo ratings yet
- Auditing, Assurance and Internal ControlDocument11 pagesAuditing, Assurance and Internal ControlaminoacidNo ratings yet
- Chapter 5 - Auditing Information Technology-Based ProcessesDocument4 pagesChapter 5 - Auditing Information Technology-Based ProcessesMichael AnibanNo ratings yet
- Nama: Anissa Dinar Paraswansa NIM: 12030122410010 Chapter 11 Internal Control and COSO FrameworkDocument6 pagesNama: Anissa Dinar Paraswansa NIM: 12030122410010 Chapter 11 Internal Control and COSO FrameworkAnissa DinarNo ratings yet
- Chapter 3: Introduction To Information Technology AuditDocument7 pagesChapter 3: Introduction To Information Technology AuditLeila MorataNo ratings yet
- Solution Manual For Information Technology Auditing 3rd Edition by HallDocument36 pagesSolution Manual For Information Technology Auditing 3rd Edition by Hallmanequin.design8haoij100% (46)
- Discussion Questions:: Lecture Week: 10 Chapter 13: Auditing & GovernanceDocument4 pagesDiscussion Questions:: Lecture Week: 10 Chapter 13: Auditing & GovernanceOdria ArshianaNo ratings yet
- Chapter 1auditing and Internal ControlReview Questions1Document2 pagesChapter 1auditing and Internal ControlReview Questions1spellblade del mariaNo ratings yet
- System Audit: Foundations of Information System AuditingDocument4 pagesSystem Audit: Foundations of Information System AuditingmercatuzNo ratings yet
- Test 2 PDFDocument134 pagesTest 2 PDFJeejuNo ratings yet
- Jurnal IS - Audit - ProcessDocument4 pagesJurnal IS - Audit - ProcessLyle Walt0% (1)
- Chapter 5 - Heirarchy of Ic PDFDocument7 pagesChapter 5 - Heirarchy of Ic PDFDaisy ContinenteNo ratings yet
- INFORMATIONS SYSTEMS AUDIT NOTES MucheluleDocument59 pagesINFORMATIONS SYSTEMS AUDIT NOTES MuchelulevortebognuNo ratings yet
- Preliminary ReviewDocument6 pagesPreliminary ReviewLet it beNo ratings yet
- Gelinas Tutorial Chapter 7Document6 pagesGelinas Tutorial Chapter 7Michael ReillyNo ratings yet
- IT AuditDocument86 pagesIT AuditLuis Ibaviosa Lorenzo100% (3)
- Rais12 SM Ch11Document24 pagesRais12 SM Ch11Vito Nugraha Soerosemito100% (1)
- A 6.4 Audit Unit 6Document8 pagesA 6.4 Audit Unit 6Gaurav MahajanNo ratings yet
- DRAFTDocument10 pagesDRAFTNatala WillzNo ratings yet
- Act 3202 Week 5 Internal Control EvaluationDocument7 pagesAct 3202 Week 5 Internal Control EvaluationJasmin BasimNo ratings yet
- Test 5Document111 pagesTest 5JeejuNo ratings yet
- AuditingDocument7 pagesAuditingashraf ayoubNo ratings yet
- IT Audit Basics The IS Audit Process by S. Anantha Sayana, CISA, CIADocument4 pagesIT Audit Basics The IS Audit Process by S. Anantha Sayana, CISA, CIAMaria Alexandra Campoverde PesantezNo ratings yet
- NissctxtDocument3 pagesNissctxtMahmoodNo ratings yet
- Accounting Information Systems Romney 13th Edition Solutions ManualDocument26 pagesAccounting Information Systems Romney 13th Edition Solutions ManualDavidKingprza100% (35)
- Bit006 Accounting Information Systemcontrol&Substantive TestingDocument4 pagesBit006 Accounting Information Systemcontrol&Substantive TestingGabriel PatronNo ratings yet
- 17Document43 pages17abmyonisNo ratings yet
- C Is A 100 Practice QuestionDocument100 pagesC Is A 100 Practice Questionmadunix100% (1)
- Law On Partnership and Corporation Study GuideDocument18 pagesLaw On Partnership and Corporation Study GuideKelvinIvanLorenzoVelascoNo ratings yet
- Rais12 SM CH11Document24 pagesRais12 SM CH11Hero BirawanNo ratings yet
- Cisa 100 PracticequestionDocument102 pagesCisa 100 PracticequestionNerma NermaNo ratings yet
- Audting II AnsDocument12 pagesAudting II Ansfikremaryam hiwiNo ratings yet
- 28-M.behroz - Audit Term ReportDocument13 pages28-M.behroz - Audit Term Reportbehroz khanNo ratings yet
- Chapter 1 Introduction On Is AuditDocument5 pagesChapter 1 Introduction On Is AuditSteffany RoqueNo ratings yet
- Auditing, Assurance, and Internal Control: Review QuestionsDocument18 pagesAuditing, Assurance, and Internal Control: Review QuestionsJoris YapNo ratings yet
- A Comparative Analysis of The Effectiveness of Internal Control System in A Computerized Accounting SystemDocument71 pagesA Comparative Analysis of The Effectiveness of Internal Control System in A Computerized Accounting SystemDaniel ObasiNo ratings yet
- SM-15-new CHAPTER 15Document41 pagesSM-15-new CHAPTER 15psbacloudNo ratings yet
- Chapter 15 SMDocument15 pagesChapter 15 SMAvreile RabenaNo ratings yet
- Chapter FiveDocument9 pagesChapter Fivebilanxaji1No ratings yet
- Audit Programs and Establishing The Audit UniverseDocument7 pagesAudit Programs and Establishing The Audit Universewisnu mahardikaNo ratings yet
- Cisa100practicequestion 140116123310 Phpapp02Document102 pagesCisa100practicequestion 140116123310 Phpapp025669738019No ratings yet
- Information Systems Auditing: The IS Audit Study and Evaluation of Controls ProcessFrom EverandInformation Systems Auditing: The IS Audit Study and Evaluation of Controls ProcessRating: 3 out of 5 stars3/5 (2)
- IS Auditor - Process of Auditing: Information Systems Auditor, #1From EverandIS Auditor - Process of Auditing: Information Systems Auditor, #1No ratings yet
- Information Systems Auditing: The IS Audit Follow-up ProcessFrom EverandInformation Systems Auditing: The IS Audit Follow-up ProcessRating: 2 out of 5 stars2/5 (1)
- Auditing Information Systems and Controls: The Only Thing Worse Than No Control Is the Illusion of ControlFrom EverandAuditing Information Systems and Controls: The Only Thing Worse Than No Control Is the Illusion of ControlNo ratings yet
- Strategy Mapping: An Interventionist Examination of a Homebuilder's Performance Measurement and Incentive SystemsFrom EverandStrategy Mapping: An Interventionist Examination of a Homebuilder's Performance Measurement and Incentive SystemsNo ratings yet
- IRR Ra 9165 and AmendmentDocument35 pagesIRR Ra 9165 and AmendmentThessaloe B. FernandezNo ratings yet
- Job Recommendation LetterDocument1 pageJob Recommendation LetterThessaloe B. FernandezNo ratings yet
- 1st Batch Cases Hum RightsDocument14 pages1st Batch Cases Hum RightsThessaloe B. FernandezNo ratings yet
- Juvenile Justice Welfare Act of 2006Document57 pagesJuvenile Justice Welfare Act of 2006Thessaloe B. FernandezNo ratings yet
- Patents To Non Reg PropertiesDocument67 pagesPatents To Non Reg PropertiesThessaloe B. FernandezNo ratings yet
- Social Legislation-SSS Act Cases-DigestDocument1 pageSocial Legislation-SSS Act Cases-DigestThessaloe B. FernandezNo ratings yet
- Transcript Sec 5 7 July 28 LectureDocument6 pagesTranscript Sec 5 7 July 28 LectureThessaloe B. FernandezNo ratings yet
- Social Legislation-SSS Act CasesDocument19 pagesSocial Legislation-SSS Act CasesThessaloe B. FernandezNo ratings yet
- Human Rights Law Reviewer For Finals - Andalecio, John Dom S. - Arellano LawDocument35 pagesHuman Rights Law Reviewer For Finals - Andalecio, John Dom S. - Arellano LawThessaloe B. FernandezNo ratings yet
- Rules and Jurisprudence On The Use of AliasDocument17 pagesRules and Jurisprudence On The Use of AliasThessaloe B. FernandezNo ratings yet
- Logic First Batch-1Document35 pagesLogic First Batch-1Thessaloe B. FernandezNo ratings yet
- People vs. AragonDocument1 pagePeople vs. AragonThessaloe B. FernandezNo ratings yet
- 13 - 19 CasesDocument2 pages13 - 19 CasesThessaloe B. FernandezNo ratings yet
- Lleek Sheng Vs Ca G.R. No. 115402, July 15, 1998: Purpose of Notice of Lis Pendens and When It May Be CancelledDocument3 pagesLleek Sheng Vs Ca G.R. No. 115402, July 15, 1998: Purpose of Notice of Lis Pendens and When It May Be CancelledThessaloe B. FernandezNo ratings yet
- Page 2 of About 680Document2 pagesPage 2 of About 680Thessaloe B. FernandezNo ratings yet
- Us-Conversion CycleDocument3 pagesUs-Conversion CycleThessaloe B. FernandezNo ratings yet
- Billing/Accounts Receivable/ Cash Receipts ProcessDocument2 pagesBilling/Accounts Receivable/ Cash Receipts ProcessThessaloe B. FernandezNo ratings yet
- Rules of Freedom WallDocument2 pagesRules of Freedom WallThessaloe B. FernandezNo ratings yet
- Company Accounts and Auditing Practices PDFDocument604 pagesCompany Accounts and Auditing Practices PDFசுப்பிரமணிய தமிழ்100% (2)
- Internal Factors, External Factors and Earnings Management: Moderating Effects of Auditor Industry SpecializationDocument18 pagesInternal Factors, External Factors and Earnings Management: Moderating Effects of Auditor Industry SpecializationSetiawan RinaldiNo ratings yet
- Haldiram Foods International LTD Annual Report 2005Document10 pagesHaldiram Foods International LTD Annual Report 2005Nishant SinghNo ratings yet
- AA - Question PackDocument28 pagesAA - Question PackLeroyNo ratings yet
- Team Project-Financial AccountingDocument10 pagesTeam Project-Financial Accountingsameed mateenNo ratings yet
- Revised Audit ReportDocument2 pagesRevised Audit ReportJheza Mae PitogoNo ratings yet
- Auditing TheoryDocument11 pagesAuditing Theoryh3swg6inl8wkNo ratings yet
- Accounting Information Systems 14Th Edition Romney Test Bank Full Chapter PDFDocument21 pagesAccounting Information Systems 14Th Edition Romney Test Bank Full Chapter PDFmary.wiles168100% (19)
- The Impact of Auditor'S Opinion On Earnings Management: Evidence From RomaniaDocument13 pagesThe Impact of Auditor'S Opinion On Earnings Management: Evidence From RomaniaThương ĐỗNo ratings yet
- Audit Reports: ©2008 Prentice Hall Business Publishing, Auditing 12/e, Arens/Beasley/Elder 3 - 1Document37 pagesAudit Reports: ©2008 Prentice Hall Business Publishing, Auditing 12/e, Arens/Beasley/Elder 3 - 1tiex hereNo ratings yet
- Auditing and Assurance Strathmore University Notes and Revision KitDocument287 pagesAuditing and Assurance Strathmore University Notes and Revision KitAx NgNo ratings yet
- XBRL Document in Respect Consolidated Financial Statement-11022022Document177 pagesXBRL Document in Respect Consolidated Financial Statement-11022022Bhagwan BachaiNo ratings yet
- 4.136 T.Y.B.Com. Semester V and VI PDFDocument30 pages4.136 T.Y.B.Com. Semester V and VI PDFVishal JainNo ratings yet
- Auditing TheoryDocument7 pagesAuditing TheoryMarian MartinezNo ratings yet
- Bos 60629Document6 pagesBos 60629ROCKSPYNo ratings yet
- Big 4Document21 pagesBig 4mohhmameddNo ratings yet
- Auditing: AssignmentDocument8 pagesAuditing: AssignmentBhavnaNo ratings yet
- BS AnalysisDocument116 pagesBS AnalysisDolly BadlaniNo ratings yet
- Chapter 5 - AUDIT PLANNINGDocument8 pagesChapter 5 - AUDIT PLANNINGAljean Castro DuranNo ratings yet
- Tax Auditor Cover LetterDocument8 pagesTax Auditor Cover Letterfvntkabdf100% (2)
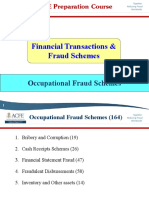
- 02 - Occupational Fraud Schemes 2019Document114 pages02 - Occupational Fraud Schemes 2019abdul syukur100% (1)
- Audit Process (Pre-Engagement Activities Notes)Document44 pagesAudit Process (Pre-Engagement Activities Notes)TinoManhangaNo ratings yet
- Ethics, Fraud, and Internal Control: Accounting Information Systems, 7eDocument44 pagesEthics, Fraud, and Internal Control: Accounting Information Systems, 7eZac VanessaNo ratings yet
- Govbri - ReviewerDocument185 pagesGovbri - ReviewerFabia, Micah B.No ratings yet
- DLF LIMITED Auditors ReportDocument6 pagesDLF LIMITED Auditors ReportAvinash MulikNo ratings yet
- 2017 About Face 2017 Audit Protocol FinalDocument92 pages2017 About Face 2017 Audit Protocol FinalHUGO VASQUEZNo ratings yet
- At.3220 - Other Assurance Engagements and Related ServicesDocument12 pagesAt.3220 - Other Assurance Engagements and Related ServicesDenny June CraususNo ratings yet