Professional Documents
Culture Documents
Review of Code Clone Detection
Uploaded by
er.manishgoyal.ghudd0 ratings0% found this document useful (0 votes)
22 views4 pagesCode Clone Detection
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCode Clone Detection
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
22 views4 pagesReview of Code Clone Detection
Uploaded by
er.manishgoyal.ghuddCode Clone Detection
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 4
IJCSN International Journal of Computer Science and Network, Volume 3, Issue 2, April 2014
ISSN (Online) : 2277-5420 www.IJCSN.org
Impact Factor: 0.274
95
Review of Review of Review of Review of Code Code Code Code Clone Detection Clone Detection Clone Detection Clone Detection
1
Jyoti Khanna,
2
Rajvir Singh,
3
Ritu Garg
1, 2, 3
CSE Department, DeenBandhuChhotu Ram University of Science and Technology,
Murthal, Haryana, India
Abstract - Now a days Copy and Paste of code fragments has
been regularly practiced in development of software. Because of
limitations of time and lack of knowledge programmers use this
code strategy. This strategy is known as code cloning. Clones
may cause many problems. Probability of errors and the
maintenance cost is increased. Modification would be difficult
because of clones. So it needs to detect clones and remove them.
Keywords - Clone, Tokens, Abstract Syntax Tree, Count
Matrix, Count Vector.
1. Introduction
Many techniques are used in clone detection. Some
techniques are discussed below:
the maintenance cost and probability of bugs. So clones
needs to be detected and refactored. Many techniques have
been purposed Generally redundancy is found out in
software system. This redundancy is because of duplicate
fragments [1]. And these fragments are termed as clones.
Clones increase
for clone detection and are discussed below.
1.1 Types of clone [2]:
Code clones are divided into four types:
Type 1 or Exact clones: One fragment is exact copy of
another fragment except of white spaces and comments.
Type 2 or Renamed clones: one fragment is exact copy
of another fragment except of identifier names, spaces and
comments.
Type 3 or Modified clones: One fragment is copied to
another fragment except that some statements are added or
deleted.
Type 4 or semantic clones: One fragment is not
syntactical similar to another fragment but behavior of two
fragments are similar.
2. Techniques of Code Clones Detection
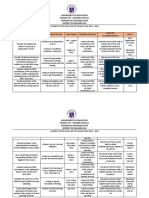
Table 1: Techniques of clone detection
Text Based Token Based Tree Based PDG
Based
In text
based
technique
program is
considered
as a
sequence of
statements.
Two
fragments
are declared
as clones if
they have
same
sequence
for
particular
statements.
In this
approach
programs are
transformed
into sequence
of tokens and
clones are
declared on
the basis of
matching
subsequence
of tokens.
In this
techniqueprograms
are converted into
syntax tree or
parse tree with the
help of parser of
the specific
language. Clones
are detected using
different
techniques
applying on tree.
In this
technique
program
dependency
graph is
built which
represent
data flow &
control
flow of the
program.
Isomorphic
matching
techniques
are applied
for clone
detection.
These
techniques
detect less
false clones,
low recall.
These
techniques
detect less
false clones
and low recall
but higher as
compared to
text based
techniques.
These techniques
have low precision
and low recall.
These
techniques
detect less
false clones
and high
recall.
Scalability
depends
upon the
method
applied for
these
techniques.
Scalability is
high
Scalability
depends upon
algorithm applied.
Scalability
is low
because
graph
matching
techniques
are costly.
Easy to
implement,
light weight
technique.
Fewer
Complexes.
To build tree is
very complex.
Matching
techniques
are
complex.
This
technique is
independent
of language.
This
technique is
independent
of language.
Parser used for
transformation is
language
dependent.
This
technique is
independent
of
language.
IJCSN International Journal of Computer Science and Network, Volume 3, Issue 2, April 2014
ISSN (Online) : 2277-5420 www.IJCSN.org
Impact Factor: 0.274
96
3. Literature Review:
Ira et al. [3] has used tree based technique to find the
clones in the code. Three subprocesses are used to detect
clones. First algorithm which is the basic algorithm detects
the subtree clones. Every subtree will be compared to
another subtree. And clones will be accepted on the basis
of similarity:
2*S/ (2*S+L+R)
S-no of Shared clones
L-no of different nodes in subtree1
R-no of different nodes in subtree2
The second algorithm is used to find out sequence of
clones. e.g. if subtrees are detected as clones in a
sequence by basic algorithm then rather than declaring
them as individual clones they would be considered as
single clone.
Third algorithm is used to find out more complex near-
miss clones. This method visits the parents of the already
detected clones and finds out whether parent is it near-
miss clones [3].
Using this technique clones are not only detected but
refactored also. Limitation of this technique is this is
unable to detect semantic clones.
Yong Yuan et al. [4] used token based approach to detect
the clones named as Boreas. Boreas purposes a novel
counting based method for characteristics matrices which
describes the program segments distinctively in an
effective manner to detect the clones. Boreas has
introduced three terms counting environments (CE), count
vectors (CV) and count matrix (CM) [5].
CE describes the pattern of variable CE is divided into
three stages. These stages are nave counting stage, in
statement counting stage and inter statement counting
stage. Naive stage consists of used variables. In in-
statement counting stage CE is used for the variables
where variables are used as if-predicates, array subscript
and where any operation is applied to the variables and
where it is defined by expression with constants. In inter
statement stage CE is used as the variable is in first level
loop, second level loop or deeper level loop.
CV with m dimensions is formed by using m CE. The ith
dimension of CV consists of no of counts of that variable
in ith CE. CV is also known as characteristics vector.
For n variable using m-dimensional CV m*n Count Matrix
is formed. These CM are the abstract form of code
fragments. Similarity of two fragments is measured by
production of their CMs similarity and similarity of their
CVs of the keyword and punctuation marks. Similarity of
two CVs is measured with the formula:
Prosim = 1/ (a + 1) + b / (a + 1)
Boreas is language independent and high scalable with
high speed means with less set up time and with less
comparison time.
Rochelle et al. [6] detects semantic clone using IOE
behavior. Semantic clones are also called by behavioral
clones [7]. To detect clones input output is includedas in
the [8] and their effects are also considered i.e. change in
heap state is also included. This approach works at java
code. In input value of parameters passed to function and
heaps state at invocation time of method. In output,
behavior is determined with the returned value of the
function, possible and persistent change into heap. This
Method includes four subprocesses: abstraction, filtering,
testing and collection.
In abstraction AST are formed to obtain list of two method
properties: method types and effects. In Filtering two
filters are used. First filters take method type i.e.
syntactical information as input and returns methods
having equivalent return type and parameters as candidate
clones. Second filter take semantic information as i/p and
refine candidate clones by eliminating the function with
different effects. Now after filtering, methods in any
equivalence class having same type and effects. In testing
phase dynamic behavior of the method is checked. The
dynamic behavior is checked using test files. In collection
phase Test driver for running the files is executed.
After all these process equivalent fragments or clones are
obtained.
Thierry Lavoie et al. [9] used levenshtein distance [10] to
find out the clones. This technique is combination of token
based [11] and metric based [12] clone detection
techniques. Metric trees and Manhattan distance are used
for accurate estimation of levenshtein distance.
Levenshtein distance is measure of similarity between
strings. It calculates no of insertion, deletion and swapping
of characters to transform string s1 into s2. In the first step
tokens are extracted from source code with lexical
analyzer. In the second step frequency vectors are built. A
unique id is provided to each token. Id is provided
dynamically, if any new item is discovered an available id
is provided to that token else corresponding vector of
token is incremented by one. Hashing Tables are used to
store vectors. In the next step metric tree are built using
frequency vectors. L1 metric i.e. Manhattan distance is
IJCSN International Journal of Computer Science and Network, Volume 3, Issue 2, April 2014
ISSN (Online) : 2277-5420 www.IJCSN.org
Impact Factor: 0.274
97
used for this purpose. Manhattan distance is chosen
because of the following reason:
L1 covers less space.
L1 is fast and high precision.
In the fourth step Metric tree is built with all the vectors.
Metric tree separate the search space and increase the
speed of insertion, range queries and nearest neighbors.
The last step is tree query step. In this step Manhattan
distance between two metric trees is measured. If two trees
have Manhattan distance less than threshold, then they
would be clones.
Dandan Kong et al.[13] used k-nearest algorithm to find
clones. The advantage of AST, control dependency graph
and k-nearest neighbor clustering algorithm [14] is taken
in this algorithm. Two fragments are defined as functional
equivalent if there exist two permutations p1, p2 such that
for
OC1 (p1 (I)) =OC2 (p2 (I))
where OC represents the output set of C1 and C2 code
fragments.
Firstly code is passed to lexical analyzer and syntax
analysis to obtain the control dependency information by
generating AST and PDG. Then functionally cohesive
code is obtained by nearest neighbor clustering algorithm.
Input and Output variables are identified [13]. Then
uncompilable code is transformed into executable
functions. The automated generated input is given to
function and dynamically tested. Then according to output
results generated on inputs equivalent functions are
grouped into same cluster.
4. Comparisons:
Table 2: Comparison of Techniques of different authors
Techniques Used Scalability Portability Complexity
Thierry Lavoie et
al. [9]
Combination of
Token based and
metric based
Less This technique is
applied on c
language
More complex
Ira et al. [3] Tree Based Less Parser used for
transformation, is
language dependent
More complex
Yong Yuan et al.
[4]
Token Based More Language
Independent
Less complex
Dandan Kong et
al.[13]
Combination of tree
based and Graph
based
Less Parser is language
dependent
More complex
Rochelle et al. [6] Based on behavior
of fragments
More This Technique is
applied for java
language
Less complex
5. Conclusion
Clones have many drawbacks. They increase the
maintenance cost and the probability of bugs. So clones
need to be removed. Clones cant be removed completely.
Many techniques have been used for clone detection till
now. Each technique has its own advantages and
limitations. Techniques are applied according to
requirements. Sometimes hybrid techniques are used.
More techniques can be proposed with less complexity and
high scalability.
6. Future Scope:
It will be tried to find out more and more clones to
decrease the no of false clones.There are many techniques
for clone detection, but very few are to refactor the clones.
So our future objective is to purpose a novel for clone
management having less complexity.
References
[1] Z. Li, S. Lu, S. Myagmar and Y. Zhou, CP-miner:
Finding copy-paste and related bugs in large-scale
software code, IEEE, 2006.
[2] C. K. Roy, J. R. Cordy, and R. Koschke. Comparison
and evaluation of code clone detection techniques and
tools: A qualitative approach, Sci. Comput. Program,
2009.
[3] Ira D. Baxter, Andrew Yahin, Leonardo Moura, Marcelo
SantAnna, Lorraine Bier, Clone Detection Using
Abstract Syntax Trees, IEEE, 2011.
[4] Yang Yuan,YaoGuo, Boreas: an accurate and scalable
token-based approach to code clone detection, In
IJCSN International Journal of Computer Science and Network, Volume 3, Issue 2, April 2014
ISSN (Online) : 2277-5420 www.IJCSN.org
Impact Factor: 0.274
98
Proceedings of the 27th IEEE/ACM International
Conference on Automated Software Engineering -
ASE,IEEE 2012.
[5] Y. Yuan and Y. Guo. CMCD: Count Matrix based Code
Clone Detection, APSEC.Thierry Lavoie, EttoreMerlo,
An accurate estimation of the Levenshtein distance
using metric trees and Manhattan distance, In 6th
International Workshop on Software Clones (IWSC),
IEEE, 2012.
[6] Rochelle Elva, Gary T. Leavens, Semantic Clone
Detection Using Method IOE-Behavior,InIWSC, Zurich,
Switzerland,IEEE, 2012.
[7] E. Juergens, F. Deissenboeck, and B. Hummel, Clone
detection beyond copy & paste, in Proc. of the 3rd
International Workshop on Software Clones, 2009.
[8] R. Elva and G. Leavens, Jsctracker: A semantic
clonedetection tool for Java code, University of Central
Florida, Department of EECS,University of Central
Florida,4000 Central Florida Blvd,Orlando, Florida,
32816, USA, Research paper CS-TR-12-04,March 2012,
http://www.eecs.ucf.edu/ leavens/tech-reports/UCF/CS-
TR-12-04/TR.pdf,2012.
[9] Thierry Lavoie, Ettore Merlo, An accurate estimation of
the Levenshtein distance using metric trees and
Manhattan distance, In 6th International Workshop on
Software Clones (IWSC) ,IEEE,2012.
[10] Lavoie and E. Merlo. Automated type-3 clone oracle
using levenshtein metric, 2011, ACM, 2011.
[11] T. Kamiya, S. Kusumoto, and K. Inoue. CCFinder: A
multilinguistic token-based code clone detection system
for large scale source code, IEEE, 2002
[12] E. Merlo, G. Antoniol, M. D. Penta, and F. Rollo. Linear
complexity object-oriented similarity for clone detection
and software evolution analysis. In Proceedings of the
International Conference on Software Maintenance -
IEEE Computer Society Press, IEEE, 2004
[13] Dandan Kong, Xiaohong Su, Shitang Wu, Tiantian
Wang and Peijun Ma, Detect Functionally Equivalent
Code Fragments via K-nearest, IEEE fifth International
Conference on Advanced Computational
Intelligence(ICACI) October 18-20,2012 Nanjing,
Jiangsu, China, 2012.
[14] C. Lung, X. Xu, M. Zaman, A. Srinivasan, Program
restructuring using clustering techniques, The Journal of
Systems and Software, 2006.
You might also like
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (400)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (345)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (121)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Electricity Act - 2003Document84 pagesThe Electricity Act - 2003Anshul PandeyNo ratings yet
- MORIGINADocument7 pagesMORIGINAatishNo ratings yet
- 2021S-EPM 1163 - Day-11-Unit-8 ProcMgmt-AODADocument13 pages2021S-EPM 1163 - Day-11-Unit-8 ProcMgmt-AODAehsan ershadNo ratings yet
- Exp. 5 - Terminal Characteristis and Parallel Operation of Single Phase Transformers.Document7 pagesExp. 5 - Terminal Characteristis and Parallel Operation of Single Phase Transformers.AbhishEk SinghNo ratings yet
- A Review Paper On Improvement of Impeller Design A Centrifugal Pump Using FEM and CFDDocument3 pagesA Review Paper On Improvement of Impeller Design A Centrifugal Pump Using FEM and CFDIJIRSTNo ratings yet
- 3412C EMCP II For PEEC Engines Electrical System: Ac Panel DC PanelDocument4 pages3412C EMCP II For PEEC Engines Electrical System: Ac Panel DC PanelFrancisco Wilson Bezerra FranciscoNo ratings yet
- Ludwig Van Beethoven: Für EliseDocument4 pagesLudwig Van Beethoven: Für Eliseelio torrezNo ratings yet
- HandloomDocument4 pagesHandloomRahulNo ratings yet
- Dry Canyon Artillery RangeDocument133 pagesDry Canyon Artillery RangeCAP History LibraryNo ratings yet
- CANELA Learning Activity - NSPE Code of EthicsDocument4 pagesCANELA Learning Activity - NSPE Code of EthicsChristian CanelaNo ratings yet
- Reverse Engineering in Rapid PrototypeDocument15 pagesReverse Engineering in Rapid PrototypeChaubey Ajay67% (3)
- Banjara EmbroideryDocument34 pagesBanjara EmbroideryKriti Rama ManiNo ratings yet
- Enerparc - India - Company Profile - September 23Document15 pagesEnerparc - India - Company Profile - September 23AlokNo ratings yet
- Sophia Program For Sustainable FuturesDocument128 pagesSophia Program For Sustainable FuturesfraspaNo ratings yet
- Phase 1: API Lifecycle (2 Days)Document3 pagesPhase 1: API Lifecycle (2 Days)DevendraNo ratings yet
- Bajaj Allianz InsuranceDocument93 pagesBajaj Allianz InsuranceswatiNo ratings yet
- Catalogo AWSDocument46 pagesCatalogo AWScesarNo ratings yet
- Hip NormDocument35 pagesHip NormAiman ArifinNo ratings yet
- Reflections On Free MarketDocument394 pagesReflections On Free MarketGRK MurtyNo ratings yet
- Wendi C. Lassiter, Raleigh NC ResumeDocument2 pagesWendi C. Lassiter, Raleigh NC ResumewendilassiterNo ratings yet
- Action Plan Lis 2021-2022Document3 pagesAction Plan Lis 2021-2022Vervie BingalogNo ratings yet
- KSU OGE 23-24 AffidavitDocument1 pageKSU OGE 23-24 Affidavitsourav rorNo ratings yet
- LMU-2100™ Gprs/Cdmahspa Series: Insurance Tracking Unit With Leading TechnologiesDocument2 pagesLMU-2100™ Gprs/Cdmahspa Series: Insurance Tracking Unit With Leading TechnologiesRobert MateoNo ratings yet
- Convention On The Rights of Persons With Disabilities: United NationsDocument13 pagesConvention On The Rights of Persons With Disabilities: United NationssofiabloemNo ratings yet
- Delta AFC1212D-SP19Document9 pagesDelta AFC1212D-SP19Brent SmithNo ratings yet
- Lending OperationsDocument54 pagesLending OperationsFaraz Ahmed FarooqiNo ratings yet
- Using Boss Tone Studio For Me-25Document4 pagesUsing Boss Tone Studio For Me-25Oskar WojciechowskiNo ratings yet
- 2.1 Components and General Features of Financial Statements (3114AFE)Document19 pages2.1 Components and General Features of Financial Statements (3114AFE)WilsonNo ratings yet
- ARUP Project UpdateDocument5 pagesARUP Project UpdateMark Erwin SalduaNo ratings yet
- Fernando Salgado-Hernandez, A206 263 000 (BIA June 7, 2016)Document7 pagesFernando Salgado-Hernandez, A206 263 000 (BIA June 7, 2016)Immigrant & Refugee Appellate Center, LLCNo ratings yet