Professional Documents
Culture Documents
Narbik Ccie R&s Advanced Workbook v4.0 Vol 2
Uploaded by
Abdul Hamid100%(5)100% found this document useful (5 votes)
761 views971 pagesFor CCIE R&S preparation, from narbik
Original Title
Narbik Ccie r&s Advanced Workbook v4.0 Vol 2
Copyright
© © All Rights Reserved
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this Document100%(5)100% found this document useful (5 votes)
761 views971 pagesNarbik Ccie R&s Advanced Workbook v4.0 Vol 2
Uploaded by
Abdul HamidYou are on page 1of 971
Advanced
CCIE Routing & Switching
4.0
www.MicronicsTraining.com
Narbik Kocharians
CCIE #12410
R&S, Security, SP
VOL-IT
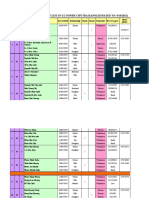
Table of Content:
Subject
Topology
3560 Switching
Lab 1 Basic 3560 configuration - I
Lab 2 Basic 3560 configuration - II
Lab 3 Configuring Trunks
Lab 4 Configuring EtherChannels
Lab 5 Advanced STP Configuration
Lab 6 Multiple Spanning-tree (802.15)
Lab 7 Configuring Private VLANs
Lab 8 QinQ Tunneling
Lab 9 Fallback Bridging
Frame-relay
Lab 1 Hub-n-Spoke Using Frame Map Statements
Lab 2 Hub-n-Spoke Frame-relay Point-to-point
Lab 3 Mixture of P2P and Multipoint
Lab 4 Multipoint Frame-relay W/O Frame maps
Lab 5 Frame-relay and Authentication
Lab 6 Frame-relay End-to-End Keepalives
Lab 7 Tricky Frame-relay Configuration
Lab 8 Frame-relay Multilinking
Lab 9 Back-to-Back Frame-relay connection
ODR
Lab 1 On Demand Routing
RIPy2
Lab 1 RIPv2 and Frame-relay
Lab 2 RIPv2 Authentication
Lab 3 Advanced RIPy2 Mini Mock Lab
EIGRP
Lab 1 Eigrp configuration
Lab 2 Advanced Eigrp Stub Configuration
Lab 3 Kigep & Default-information
Lab 4 Eigrp Filtering
Table of Content:
Subject
OSPF
Lab 1 Advertising Networks
Lab 2 Optimization of OSPF & Adjusting Timers
Lab 3 OSPF Authentication
Lab 4 OSPK Cost
Lab 5 OSPF Summarization
Lab 6 Virtual-links and GRE Tunnels
Lab 7 OSPF Stub, T/Stub, and NSSAs
Lab 8 OSPF Filtering
Lab 9 Additional OSPF Filtering
Lab 10 Redirecting Traffic in OSPF
Lab 11 Database Overload Protection
Lab 12 OSPF Non-Broadcast Networks
Lab 13 OSPF Broadcast Networks
Lab 14 OSPF Point-to-Point Networks
Lab 15 OSPF Point-to-Multipoint Networks
Lab 16 OSPF Point-to-Multi Network - II
Lab 17 OSPF P-to-M Non-Broadcast Net
Lab 18 OSPF and NBMA
Lab 19 Forward Address Suppression
Lab 20 OSPF NSSA no-redistribution & Injection
of default routes
BGP.
Lab 1 Establishing Neighbor Adjacency
Lab 2 Route Reflectors
Lab 3 Conditional Adv & Back door
Lab 4 Route Dampening
Lab 5 Route Aggregation
Lab 6 The community Attribute
Lab 7 BGP Cost Community
Lab 8 BGP & Load Balancing —1
Lab 9 BGP Load Balancing - II
Lab 10 BGP Unequal Cost Load Balancing
Lab 11 BGP Local Preference —T
Lab 12 BGP Local Preference — I
Lab 13 The AS-Path Attribute
Lab 14 The Weight Attribute
Lab 15 MED
Lab 16 Filtering Using ACLs & Prefix-lists
Lab 17 Regular Expressions
Vol-l
Lab 18 Adv BGP Configurations
Vol-l
Lab 19 Administrative Distance
Volt
Lab 20 BGP Confederation
Vol-I
Lab 21 BGP Hiding Local AS Number
Vol-T
Lab 22 BGP Allowas-in
Vol-l
Policy Based Routing
Lab 1 PBR based on Source IP address
Vol-l
Redistribution
Lab 1 Basics of Redistribution-I
Vol-l
Lab 2 Basics of Redistribution-II
Vol-l
Lab 3 Advanced Redistribution
Vol-I
Lab 4 Routing Loops
Vol-l
IP SLA
Lab LIP SLA.
Vol-T
Lab 2 Reliable Static Routing using IP SLA.
Vol-l
Lab 3 Reliable Conditional Default Route
Injection using IP SLA
Vol-I
Lab 4 Object Tracking in HSRP Using SLA
Vol-T
Lab 5 Object Tracking
Vol-l
GRE Tunnels
Lab 1 Basic Configuration of GRE Tunnels
Vol-I
Lab 2 Configuration of GRE Tunnels IT
Vol-I
Lab 3 Configuration of GRE Tunnels III
Vol-l
Lab 4 GRE & Recursive loops
Vol-I
Qos
Lab 1 MLS QOS
Vol-ll
Lab 2 DSCP Mutation
Vol-Il
Lab 3 DSCP-CoS Mapping
Vol-Il
Lab 4 CoS-DSCP Mapping
Vol-II
Lab 5 IP-Precedence-DSCP Mapping
Vol-Il
Lab 6 Individual rate Policin;
Vol-ll
Lab 7 Policed DSCP
Vol-II
Lab 8 Aggregate Policer
Vol-Il
Lab 9 Priority Queuin;
Voll
Lab 10 Custom Queuing
Vol-Il
Lab 11 WFQ
Vol-II
Lab 12 RSVP.
Vol-Il
Lab 13 Match Access-group
Voll
Lab 14 Match Destination & Source Add MAC
Vol-II
Lab 15 Match Input-Interface
Vol-Il
Lab 16 Match FR-de & Packet Length
Vol-ll
Lab 17 Match IP Precedence vs. Match Precedence
Vol-Il
Lab 18 Match Protocol HTTP URL, MIME & Host
Vol-II
Lab 19 Match Fr-dlei
Vol-Il
Lab 20 Frame-relay Traffic Shaping
Vol-ll
Lab 21 Frame-relay Traffic-shaping — II
Vol-Il
Lab 22 Frame-relay Fragmentation
Vol-Il
Lab 23 Frame-relay PIPQ
Vol-IL
Lab 24 Frame-relay DE
Vol-Il
Lab 25 Frame-relay and Compression
Vol-II
Lab 26 CBWFQ
Vol-Il
Lab 27 CBWFQ- IT
Vol-ll
Lab 28 Converting Custom Queuing to CBWFQ
Vol-Il
Lab 29LLQ
Vol-Il
Lab 30 CAR
Vol-I
Lab 31 Class Based Policing — I
Vol-ll
Lab 32 CB Policing— 11
Vol-I
Lab 33 WRED & CB WRED
Vol-Il
NAT
Lab 1 Static NAT Configuration
Vol-Il
Lab 2 Advanced Static NAT Configuration
Vol-II
Lab 3 Configuration of Dynamic NAT - I
Vol-Il
Lab 4 Configuration of Dynamic NAT — IT
Voll
Lab 5 Configuration of Dynamic NAT - II
Vol-II
Lab 6 NAT and Load Balancin;
Vol-Il
Lab 7 Configuring PAT
Voll
Lab 8 Configuring PAR
Vol-Il
Lab 9 Configuring Static NAT Redundancy W/HSRP
Vol-II
Lab 10 Stateful Translation Failover With HSRP.
Vol-II
Lab II Translation of the Outside Source
Voll
Lab 12NAT ona Stick
Vol-II
IP Services
Lab 1 DHCP Configuration
Vol-Il
Lab 2 HSRP Configuration
Vol-Il
Lab 3 VRRP Configuration
Vol-IL
Lab 4 GLBP Configuration
Vol-Il
Lab 5 IRDP Configuration
Vol-I
Lab 6 Configuring DRP
Vol-ll
Lab 7 Configuring WCCP
Vol-ll
Lab 8 Core Dump Using FTP
Vol-I
Lab 9 HTTP Connection Management
Vol-Il
Lab 10 Configuting NTP
Vol-I
Lab 11 More IP Stuff
Vol-Il
IP Prefix-List
Lab 1 Prefix-Lists
Vol-Il
IPv6
Lab 1 Configuring Basic IPv6
Voll
Lab 2 Configuring OSPFv3
Vol-II
Lab 3 Configuring OSPFv3 Multi-Area
Vol-Il
Lab 4 Summarization of Internal & External N/W
Voll
Lab 5 OSPFV3 Stub, T/Stub and NSSA networks
Vol-Il
‘ost and Auto-cost
Vol-II
Lab 7 Tunneling IPv6 Over IPv4
Vol-II
Lab 8 Kigep and IPv6
Vol-ll
Security
Lab 1 Basic Router Security Configuration
Vol-ll
Lab 2 Standard Named Access List
Vol-II
Lab 3 Controlling Telnet Access and SSH
Vol-Il
Lab 4 Extended Access List IP and ICMP
Vol-II
Lab 5 Extended Access List OSPF & Eigrp
Vol-Il
Lab 6 Using MQC as a Filtering tool
Voll
Lab 7 Extended Access List With Established
Vol-Il
Lab 8 Dynamic Access List
Vol-ll
Lab 9 Reflexive Access-Lists
Vol-I
Lab 10 Access-list & Time Range
Vol-Il
Lab 11 Configuring Basic CBAC
Vol-II
Lab 12 Configuring CBAC
Vol-I
Lab 13 Configuring CBAC & Java Blocking
Voll
Lab 14 Configuring PAM
Vol-Il
Lab 15 Configuring uRPF
Vol-ll
Lab 16 Configuring Zone Based Firewall
Vol-II
Lab 17 Control Plane Policing
Vol-Il
Lab 18 Configuring 10S IPS
Vol-II
Lab 19 Attacks
Vol-Il
Lab 20 AAA Authentication
Vol-ll
Multicasting
Lab 1 Configuring IGMP
Voll
Lab 2 Dense Mode
Vol-II
Lab 3 Static RP Configuration
Vol-I
Lab 4 Auto-RP.
Vol-II
Lab 5 Auto-RP Filtering & Listener
Vol-ll
Lab 6 Configuring BSR
Vol-Il
Lab 7 Configuring MSDP
Vol-Il
Lab 8 Anycast RP
Vol-ll
Lab 9 MSDP/MP-BGP.
Vol-I
Lab 10 Configuring SSM
Vol-ll
Lab 11 Helper-Map
Vol-II
Lab 12 Bidirectional PIM
Vol-Il
MPLS & L3VPNs
Lab 1 Configuring Label Distribution Protocol
Voll
Lab 2 Static & RIPy?2 Routing in a VPN
Vol-II
Lab 3 OSPF Routing ina VPN
Vol-Il
Lab 4 Backdoor links & OSPF
Voll
Lab 5 Eigrp Routing in a VPN
Vol-Il
Lab 6 BGP Routing in a VPN
Vol-II
Lab 7 Complex VPNs and Filters
Vol-II
Switch -1 Switch-2
FO/1 FO/1
Fo/2 Fo/2
FO/3 FO/3
FO/4 FO/4
FO/5 FO/5
Fo/é FO/6é
FOr" FO/14
Fo/12 > Switch-3
FO/13 Fo/12
F0/13
The Serial connection between R1 and R3
so DTE
DCE con
The Serial connection between R4 and RS
SO __BIE
DCE
CCTE R&S by Narbik Kocharians
Frame-relay Switch connections
CCTE R&S by Narbik Kocharians
Frame-relay DLCI connections:
Local DLCI
Connecting to:
F0/21-22
ee-bz/0d
Advanced
CCIE Routing & Switching
4.0
www.MicronicsTraining.com
Narbik Kocharians
CCIE #12410
R&S, Security, SP
Qos
Lab Setup:
> Configure FO/19 interface of SWI and SW2 as a Dot!Q trunk,
> Configure SW1 and SW2 in VTP domain called TST
Configure FO/1 and F0/2 interface of SW1 in VLAN 100.
> Configure F0/3 interface of SW2 as a Dot! Q trunk.
> Configure FO/1 interface of R3 as a DotlQ trunk for VLAN 100,
You can copy and paste the initial configuration from the init directory
IP addressing:
Router Interface / IP address
RI FO/O=10.1.1.1 24
R2 FO/0 = 10.1.1.2 (24
R3 FO/1.100 = 10.1.1.3 /24
Task 1
Assign a hostname of SW1 to Switeh 1 and a hostname of SW2 to Switch 2. Shutdown
all ports on these switches.
Qn Switch 1
Switch (config) {Host SW1
SW1(config)#Int range £0/1-24
SWI (config-if-range) #Shut
itch 2
(config) #Host SW2
(config) #Int range £0/1-24
(conf ig-if-range) #Shut
Task 2
Configure SW1’s port FO/2 such that it marks All ingress traffic with a CoS marking of 2
For vetification purpose, R3 should be configured to match on CoS values of 0-7
ingress on its FO/1.100 sub-interface.
In this step R3 is configured to match on incoming CoS values of 0 — 7, this is done so the policy can be
tested and verified.
On R3
R3 (config) #class-map cos0
R3 (config-cmap) #match CoS
R3 (config) #elass-map cos1
R3(config-cmap) #match CoS
R3 (config) #class-map cos2
3 (config-cmap) #match CoS
R3 (config) #elass-map cos3
R3(config-cmap) #match CoS
R3 (config) #elass-map cos4
R3(config-cmap) #mateh CoS 4
R3 (config) #elass-map cos5
R3(config-cmap) #match CoS 5
R3 (config) #elass-map cos6
R3(config-cmap) #match CoS 6
config) #elass-map cos7
R3(config-cmap) #match CoS 7
R3 (config) #Policy-map TST
R3 (config-pmap) #Class cos
R3(config-pmap) {Class cos]
R3 (config-pmap) #Class cos2
R3 (config-pmap) #Class cos3
R3(config-pmap) #Class cos4
R3 (config-pmap) #Class cos5
R3 (config-pmap) #Class cosé
R3 (config-pmap) #Class cos7
R3 (config) #Int FO/1.100
R3 (config-subif) #Service-policy in TST
On SW1
By default, QOS is disabled and the switch will NOT modify the CoS, IP-Precedence or the DSCP
values of received traffic. To verify:
SW1#Show mls qos
ges is disanies 4
QoS ip packet dscp rewrite is enabled
The following command enables MLS QOS; to perform any kind of QOS configuration, MLS QOS.
must be enabled,
SW1 (config) #MLS Qos
To fy the configuration:
On SW1
SW1#Show mls qos
cosiisiemanisa
QoS ip packet dscp rewrite is enabled
To continue with the configuration:
SW1 (config) #int FO/1
The following command assigns a default CoS value of 2 to untagged traffic received through this
interface,
SW1(config-if}#mls qos cos 2
To fy the configuration:
On SW1
SW1#Show mls qos inter £0/1
FastEthernet0/1
trust state: not trusted
trust mode: not trusted
trust enabled £1.
CoS override: d
Mutation »
Trust device: no
qos mode: port-b
To test the configuration
On RI
R1#Ping 10.1.1.3
Type pe sequence to abs .
Sending 5, 100-byte ICMP Echos to 10
ttt!
Success rate is 80 percent (4/5), round-trip min/avg/max
To vei
On R3
R3#Show policy-map interface | S cos0
Class-map: cos0
4 packets, 472 bytes
5 minute offered rate 0 bps
Match: cos 0
R3#Show policy-map interface | $ cos2
Class-map: cos2 (match-all)
0 packets, 0 bytes
5 minute offered rate
Match: cos 2
Note, even though the interface is configured with “Mls qos cos 2” the traffic coming in on that
interface is NOT affected. To mark ALL traffic with a CoS marking of 2, which means all traffic
regardless of their marking, the port must be configured to override the existing CoS.
‘The “mls qos cos” command on its own does NOTHING, it should be combined with either the “Mls
gos cos override” or “Mls qos trust cos”, When its combined with *MLS qos trust cos”, ONLY the
untagged traffic is affected, but if is combined with “MLS qos cos override”, then, all traffic (Tagged
or untagged) is affected.
The following command configures the switch port to trust the CoS value in ALL incoming traffic
through F0/2 interface, the “Mls qos cos override” command will be tested later:
SW (config) #int FO/L
SW1(config-if)#mls qos trust cos
To fy the configuration:
On SWI
sW1#Sh mls qos interface £0/1
FastEthernet0/1
trust state: trust cos
trust mode: trust cos
trust enabled flag: ena
COS override: dis
default cos: 2
DSCP Mutation Map: Default DSCP Mutation Map
Trust device: none
qos mode: port-based
o test the configuration:
On R3
R3#Clear counters
Clear "show interface" counters on a faces [confir
Press Enter to allow the counters to be cleared
OnR1
R1#Ping 10.1.1.3
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 10,1.1.3, timeout is 2 seconds:
ey
Success rate is 100 percent (5/5), round-trip min/avg/max = 1/1/4 ms
To verify the tes
On R3
R34Sh policy-map inter | § cos0
Class-map: cos0 (match~all)
, 0 bytes
5 minute offered rate 0 bps
R3#Show policy-map interface | $ cos2
Note the output of the above show command reveals that all traffic that sourced from RI is marked
with a CoS value of 0; the reason for this outcome is because SW1 is configured with “Mls qos” global
configuration command, therefore, the switch will mark all untagged incoming traffic through its F0/1
interface with a CoS value of 2.
Task 3
Configure SW! and R1 as follows:
+ FO/l interface of SW1 should be configured as a Dotlq trunk.
* Disable “Mls QOS” and remove the “Mls qos cos 2” command from F0/1
interface of SWI
Configure F0/0.100 sub-interface on R1, this sub-interface should be configured
based on the following
. R1’s F0/0,100 interface should be configured as trunk for VLAN 100
+ RI's F0/0,100 should be assigned an IP address of 10.1.1.1 /24
+ RI's F0/0,100 should be configured to mark all egress traffic with a CoS
value of 6,
On SW1
SW1 (config) #int FO/L
SW1(config-if) #Default inter £0/1
fig)#int FO/1
fig-if)#swi trunk enc do
nfig-if} #swi mode trunk
SW1 (config) #NO Mls qos
To fy the configuration
On SW1
sil#Show int trunk
Port Mode Encapsulation Status Native vlan
F on 802.14 trunking 1
on 802.14 trunking
Vlans allowed on trunk
1-4094
11-4094
Vlans allowed and active in management domain
1,100
1,100
Vlans in spanning tree forwarding state and not pruned
one
1,100
Rl (config) #Default inter F0/0
Rl (config-if) #int F0/0.100
R1(config-subif) #encap dot1 100
Ri (config-subif)#ip addr 10.1.1.1 255.255.255.0
Rl (config) #Policy-map TST
Rl (config-pmap) #class class-default
Rl (config-pmap-c) #set cos 6
R1(config-pmap-c) #int F0/0.100
Rl (config-subif) #service-policy out TST
To the configuration:
On R3
R3#Clear counters
OnR1
R1fPing 10.1.1.3 rep 60
ype escape sequence t
Sending 60, 100-byte s to 10.1.1.3, timeout is 2 seconds:
POPPEPEPEP PPE reer ee eeeeeeeriey
Success rate is 100 percent (60/60), round-trip min/avg/max = 1/1/4 ms
On R3
R3#Sh policy-map inter | S cos60
Note traffic generated by R1 has a CoS marking of 6.
Task 4
SW1 should be configured to trust the CoS marking of any traffic coming through its
FO/1 interface.
On SW1
SW1 (config) #mls qos
config) #int FO/1
fig-if)#mls qos trust Cos
To test the configuration
On R3
R3#Clear counters
On RI
R1Ping 10.1.1.3 repeat 60
Type escape sequence to abort.
Sending 60 MP Ec 3, timeout is 2 seconds:
Vereeeeenenny rereetreneens VIPEVtreneenreetenny
Success rate is 100 percent (60/60), round-trip min/avg/max = 1/1/4 ms
Note the output of the following show command reveals that the traffic retained its CoS marking.
On R3
R3#Show policy-map interface | S$ cosé
-all)
080 bytes
5 minute offered rate 0 bps
Task 5
Configure R1, R2 & SW1 using the following policy:
1. If the ingress traffic from R2 is NOT marked with a CoS value, SW1 should be
configured to mark that traffic with a CoS value of 0.
If the ingress traffic from R1 is NOT tagged, SW1 should be configured to rewrite
the CoS value to 1, however, if the traffic is tagged, SW1 should NOT rewrite the
CoS value of the incoming traffic.
To configure the first policy:
Since the “Mls Qos” command is configured on SW1, when traffic without a CoS marking enters any
port on SW1, that traffic is marked with a CoS value of 0, therefore, SW1 does NOT need to be
configured for this policy:
To verify and test the first policy:
OnR3
R3#Clear counter
OnR2
R2#Ping 10.1.1.3 rep 60
Type escape sequence to abort.
Sending 60, 100-byte ICMP Echos to timeout is 2 seconds:
Pererereny rere rereny
Success rate is 100 percent (60/60), round-trip min/avg/max = 1/1/4 ms
On R3
Since the traffic generated by R2 did not haye a CoS marking, the traffic will arrive with a CoS
marking of zero,
R3#Show policy-map interface | S$ cosé
te offered rate 0 bps
R3#Show policy-map interface | S cos0
5 minute offered rate 0
To configure the second policy:
The “Mls qos trust cos” command that was configured in the previous task will trust the CoS value in
the incoming traffic and will NOT rewrite the CoS value; since the task stats that the untagged traffic
should be re-written to a CoS value of 1, whereas, the tagged traffic should NOT be affected at all, the
following should be configured:
To test the configuration:
ons
R3#Clear counters
On SWI
SW1 (config) #Int FO/1
SW1(config-if)#mls qos cos 1
The above command ONLY affects the untagged traffic, since RI’s FO/I interface is configured as a
truck link, this configuration should NOT have any affect. The following show command reveals this
information
OnRI
R1#Ping 10.1.1.3 repeat 10
Type escape sequence to abort.
Sending 10, 100-byte ICMP Bchos to 10.1.1.3, timeout is 2 seconds:
Pereeteeny
Success rate is 100 percent (10/10), round-trip min/avg/max = 1/1/4 ms
On R3
The output of the following show command reveals that the traffic from R1 retained its CoS value of 6:
R348h policy-map inter | s cosé
To test the untagged traffic:
OnR1
Rl (config) #int FO/0.100
Rl (config-subif) #eneap dotl 100 native
NOTE: In the above and the following configuration, VLAN 100 is configured to be the Native VLAN
so the traffic arrives with NO tagging:
On SW1
SWl(config-if) #int FO/1
SW1(config-if)#swi trunk native vlan 100
To see SW1’s configurati
On SW1
sW1#Sh run int F0/1 | B interface
FastEthernet0/1
s port trunk encapsulatii
s port trunk native vlan 100
switchport mode trunk
mls gos cos 1
mls gos trust cos
To verify the configuration:
On SW1
SW1#Sh interface trunk
Port Mode Encapsulation Status
20/19 on 802.1q trunking
(The rest of the output is omitted)
On R3
R3#Clear_ counters
OnR1
R1#Ping 10.1.1.3 rep 100
Type escape sequence to abort.
ding 100, 100-byte ICMP Echos to 10.1.1.3, timeout i
Veeerererenes POCPECePeCOePeeeeee rere eeeeeeeceereeereeeenreregy
reeererers rerererenes
Success rate is 100 percent (100/100), round-trip min/avg/max = 1/1/4 ms
On R3
R3#Show policy-map interface | $ cosé
Clas
0 packets, 0 bytes
5 minute offered rate 0 bps
0 packets,
te offered rate 0 bps
R3#Show policy-map interface | S$ cosl
(ma:
The following shows R1’s policy-map configuration:
On RI
R1#Show policy-map TST
Policy Map TST
Task 6
SW2 should be configured such that it marks all traffic from any router/s connected to
SWI (Tagged or Untagged) with a CoS value of 7. DO NOT configure R1, R2 or SW1 to
accomplish this task
On SW2
SWi2 (config) MLS Qos
NOTE: This configuration is performed on the trunk link of SW2 so it can affect all traffic coming
from SW1; this affects the traffic that has marking, the traffic that does NOT have any marking,
tagged or untagged:
SW2 (config) #int FO/19
SW2(config-if)#mls qos cos 7
(config-if) #mls qos cos override
To fy the configuration:
On SW2
SW2#Sh mls qos inter £0/19
FastEthernet0/19
trust state: not trusted
trust mode: not trusted
trust enabled flag: ena
COS override: ena
default Cos: 7
DSCP Mutation Map: Default DSCP Mutation Map
Tru: device: none
gos mode: port-based
To test the configuration:
On R3
R3#Clear counter
On RI
R1#Ping 10.1.1.3 rep 100
pe sequence to abort
g 100, 100-byte ICMP Echos to 10.1.1.3, timeout onds:
rerererenenty PEPEOCCePOeeeeeeeeeeerereteeererend reerenren
Success rate is 100 percent (100/100), round-trip min/avg/max = 1/1/4 ms
On R3
Note the traffic matched to CoS 7
Show policy-map interface | S cos7
(match-all)
, 11800 bytes
5 minute offered rate 0 bps
On R2
R2#Ping 10.1.1.3 rep 200
‘Type escape sequence to abort.
Sending 200, 100-byte ICMP Echos to 10.1.1.3, timeout is 2 seconds:
POCUCEPePeCCeCeCe UP eee ee eee reeeeeeeeeeereeeeeeeeeeeeeeeeeereeeereeregy
PEPEPEeenerer PUPIEPEEO PP ereeeeeeeneereneeneer Pereereny
Hererreenerer POEPOPPPereOererernireennreer
Success rate is 100 percent (200/200), round-trip min/avg/max = 1/1/4 ms
On R3
R3#Show policy-map interface
5 minute offered rate 0 bps
Note all traffic regardless of their marking are marked with a CoS value of 7.
Task 7
Erase the startup configuration on R1-3 and SW1 & SW2 and reload these routers and
switches before proceeding to the next lab,
VIP Domain
1sT
Trunk F019
Lab Setup:
The lab topology and setup is based on the previous lab, with the exception of R3’s
configuration and the FO/3 interface of SW2; R3’s FO/1 interface should be configured
with an IP address of 10.1.1.3 /24 and the F0/3 interface of SW2 should be configured in
VLAN 100.
‘You can copy and paste the initial configuration from the init directory
Task1
Configure an MQC on R1 such that all packets going out of its F0/0 interface are marked
with a DSCP value of 1. For verification purpose, R3’s FO/1 interface should be
configured to match on DSCP 0-7 for all ingress traffic. Ensure that “Mls qos” is
disabled on both switches.
On Both Switch
Siix#Sh mls gos
QoS ip packet dscp rewrite is enabled
The following configuration on R1 marks all egress traffic with a DSCP value of 1:
OnR1
Rl (config) #Policy-map TST
Rl (config-pmap) #elass class-default
Ri (config-pmap-c) #set ip dsep 1
Ri (config) #int F0/0
Rl (config-if) #Service-policy out TST
On R3
‘The following configuration is done for verification and testing purposes:
R3 (config) #Class-map DSCPO
R3(config-cmap) #match ip dsep
R3 (config) #Class-map DSCP1
R3(config-cmap) #match ip dscp
R3 (config) #Class-map DSCP2
R3(config-cmap) #match ip dsep
R3 (config) #Class-map DSCP3
R3(config-cmap) #match ip dsep
R3 (config) #Class-map DSCP4
R3(config-cmap) #match ip dscp
R3 (config) #Class-map DSCP5
R3(config-cmap) #match ip dscp
R3 (config) #Class-map DSCP6
R3(config-cmap) match ip dsep
R3 (config) #Class-map DSCP7
R3(config-cmap) #mateh ip dsep
R3 (config) 4policy-map TST
R3 (config-pmap) #Class DSCPO
R3 (config-pmap) #Class DSCP1
R3(config-pmap) #Class DSCP2
R3(config-pmap) #Class DSCP3
R3(config-pmap) #Class DSCP4
R3(config-pmap) #Class DSCP5
R3 (config-pmap) #Class DSCP6
R3 (config-pmap) #Class DSCP7
R3 (config) #int FO/1
R3 (config-if) #service-policy in TST
To test the configuration:
OnR1
R1#Ping 10.1.1.3 rep 10
Type escape sequence to abort.
Sending 10, 100-byte ICMP Echos to 10.1.1.3, timeout is 2 seconds:
VEPEPttees
Success rate is 90 percent (9/10), round-trip min/avg/max = 1/1/4 ms
On R3
R3#Sh Policy-map inter | S DSCP1
Note since “Mls qos” is disabled on both switches, the packets traversing the switches will retain their
marking.
Task 2
Configure $W2 such that if the incoming traffic is marked with DSCP 1, they are
overwritten to a DSCP value of 60. DO NOT configure a class-map or Policy-map to
accomplish this task. Use R3 to verify the configuration.
DSCP Mutation can be configured to accomplish this task; there are five steps in configuring DSCP
mutation, and they are as follows:
Step 1:
Mis qos MUST be enabled:
On SW2
SW2 (config) #M1s qos
To verify the configuration of this step:
On SW2
Si2#Show mls QoS
QoS ip packet dscp rewrite is enabled
Step 2:
In this step a custom DSCP-Mutation map is configured, remember that if this custom mapping is
NOT configured, the default DSCP-Mutation map will be used, the default DSCP-Mutation map ean
be changed and it is configured as one to one, meaning that the incoming DSCP value will always
match to the same outgoing DSCP value:
In this step a custom DSCP-Mutation map named TST is configured, this custom DSCP-Mutation
maps the incoming DSCP value (in this case 1) to an outgoing DSCP value of 6
‘o see the default D: jutation map:
sW2#Show mls qos map dscp-mutation
Dsep-dsep mutation map:
efault DSCP Mutation Map:
Note the d1: column (highlighted in yellow) specifies the most significant digit of the DSCP value of
incoming packets, whereas, the d2: row (highlighted in blue) specifies the least significant digit of the
DSCP value of incoming packets.
‘The intersection of the d1 and d2 values (this is the body of the output) provides the DSCP value of the
outgoing packets.
NOTE: the output of the above show command reveals that the incoming DSCP value of 1, is re-
written to the outgoing DSCP value of 1.
Let’s configure a custom DSCP-Mutation map called TST that maps the incoming DSCP value of 1 to
an outgoing DSCP value of 60:
SW2 (config) #M1s qos map dscp-mutation TST 1 to 60
To verify the configuration:
On SW2
SW2#Show mls qos map dscp-mutation TST
Dsep-dscp mutation map:
TST:
Step 3:
In this step, the custom DSCP-Mutation map called TST is applied to the F0/19 interface (Trunk
interface) of SW2
Swi2 (config) #int FO/19
SW2(config-if)#mls qos dscp-mutation TST
To fy the configuration:
On SW2
Svi2#Show mls qos int F0/19 | Inc DSCP
DSCP Mutation Map: TST
Reenbe, if the “Mls qos trust DSCP” is NOT configured, the configuration will NOT have any
affect on the packets:
To see the trust trust state (What’s being trusted) of the F0/19 interface:
On SW:
Si2#Show mls qos int FO/19 | Inc trust state
trust state: not trusted
On SW2
SW2 (config) #int FO/19
$W2(config-if)#mls gos trust dscp
To verify the configuration:
On SW2
Si2#Show mls qos int FO/19 | Inc trust state
trust state: trust dscp
NOTE: If CoS was trusted, the output of the above command would have stated “trust state: trust
CoS”, since ONLY DSCP is trusted, the trust state is DSCP.
Step 5:
Ensure that the DSCP re-writes are enabled, if this is disabled, then, the DSCP marking will NOT be
re-written,
To verify if the DSCP re-writes are enable
On SW2
Shi2#Show mls qos
is enabled
If the DSCP re-writes are disabled, then, the DSCP marking in the outgoing packets will NOT be re-
written, There are times that this feature must be disable, to disable this feature, the “NO mls qos
rewrite ip dsep” global command can be used.
To prepare R3 for verification purpose
OnR3
The following configuration is required for testing and verification.
R3 (config) #Class-map DSCP60
config-cmap) #match ip dscp 60
R3 (config) #policy-map TST
R3 (config-pmap) #Class DSCP60
Remember, the policy-map TST is already applied.
To verify the configuration:
On SW2
R3#Show policy-map TST
To test the configuration:
On R3
R3fclear counters
OnRi
R1#Ping 10.1.1.3 rep 60
escape sequence to abort.
nding 60, 100-byte ICMP Echos to 10.1.1.3, timeout i,
Herren rere rerens
Success rate is 100 percent (60/60), round-trip min/avg/max = 1/1/4 ms
On R3
R3#Show policy-map interface | S$ DSCP60
(match-all)
, 6840 bytes
5 minute offered rate 0 bps
Task 3
Configure the “Default interface F0/1” command on R3 before proceeding to the next
lab.
Lab 3—DSCP-CoS Mapping
10.4.1,0/24 VIPDomain
1st
wss9.20
Trunk Forts ron Fanon
4044.0 124
Lab Setup:
® Based on lab 1
You can copy and paste the initial configuration from the init directory
Task 1
For testing and verification of this lab configure R3 to match on incoming CoS marking
of 0-7 using an MQC and applying it ingress on F0/1.100 interface.
On R3
R3 (config) #class-map COsO
R3(config-cmap) #match CoS 0
R3 (config) #elass-map COS1
R3 (config-cmap) #match CoS 1
R3 (config) #elass-map COS2
R3 (config-cmap) #match CoS 2
R3 (config) #elass-map COS3
R3(config-cmap) #match CoS 3
R3 (config) #elass-map COS4
R3(config-cmap) #match CoS 4
R3 (config) #class-map COSS
R3(config-cmap) #match CoS 5
R3 (config) #elass-map COS6
3 (config-cmap) #match CoS 6
R3 (config) #elass-map COS7
R3 (config-cmap) #match CoS 7
R3 (config) #Policy-map TST
R3(config-pmap) #Class COSO
R3 (config-pmap) #Class COS1
R3(config-pmap) #Class Cos2
R3 (config-pmap) #Class COs3
R3 (config-pmap) #Class COS4
R3 (config-pmap) #Class COs5
R3 (config-pmap) #Class COS6
fig-pmap) #Class COS7
R3
R3
config) #Int F0/1.100
(config-subif) #Service-policy in TST
Task 2
Configure RI such that it marks all outgoing packets with a DSCP value of 5.
On RI
R1 (config) #policy-map TST
R1(config-pmap) #elass class-default
Rl (config-pmap-c) #set ip dsep 5
R1 (config) #Int FO/0
Rl (config-if) #service-policy Out TST
Task 3
Configure $W2 such that it maps the DSCP value of 5 in incoming packets to a CoS
value of 6.
Before configuring this task, the default DSCP-CoS mapping should be displayed, using the following
command:
On SW2
sw2#Sh mls qos map
Dsep-cos map:
al: azo
00 00 00 00
01 01 o1 1
02 02 02 02
03 03 04 04
05 05 05 05
06 06 06 06
07 07 07 07
Note the output of the above show command displays the default DSCP to CoS mapping, it means that
IE the “Mls qos trust dsep” command is configured, then, the DSCP marking of incoming packets are
mapped to outgoing CoS values according to the DSCP-CoS map.
The incoming DSCP values are shown in the di column and the d2 row, whereas, the outgoing CoS
values are identified in the body of this display, this is the intersection of di column and d2 row.
NOTE: Every eight DSCP values are mapped to a single CoS value. This mapping effects the entire
switch, and a custom mapping can NOT be configured. By default, incoming DSCP value of S is
rewritten to an outgoing CoS value of 0. To accomplish this task, we have to modify this mapping so the
incoming DSCP value of 5 is rewritten to an outgoing CoS value of 6.
To test & verify the default configur:
The following command MUST be configured, so the incoming DSCP values are trusted, if this is NOT
configured, the incoming DSCP values will NOT be rewritten to an outgoing CoS values.
On SW2
Swi2 (config) #int FO/19
SW2(config-if) #M1s gos trust DSCP
CCTE R&S by Narbik Kocharians Advanced CCIE R&S Work Book 4.0 Page 40 of 971
Svi2#Show mls qos int F0/19 | Inc trust state
trust state: trust dscp
To test the configur:
A ping is generated from R1 with a repeat count of 60 and verifies on R3:
OnR1
R1#Ping 10.1.1.3 repeat 60
‘Type escape sequence to abo:
Sending 60, 100-byte ICMP Echos to 10.1.1.3, timeout is 2 seconds:
SEPPEEeeneee Tle tee
Success rate is 98 percent (59/60), round-trip min/avg/max = 1/1/4 ms
On R3
R3#Sh policy-map interface | s Cos
Note DSCP 5 is mapped to CoS value of 0, this is because of the default mapping that is in use.
In the next step the default DSCP-CoS mapping is changed to map incoming DSCP value of 5 to an
outgoing CoS value of 6:
On SW2
SW2(config)#Mls qos map dscp-cos-5 to 6
Note the first value (5)45 the DSCP value in the incoming packets and the second value (6) is the CoS
value in the outgoing packets,
To test & verify the configuration:
On R3
R3#Clear counters
OnR1i
R1#Ping 10.1.1.3 repeat 60
ype escape sequenc :
Sending 60, 100-byte ICP to 10.1.1.3, timeout is 2 seconds:
TEEPE PEPePePePeeteneey Vetter HUPeereeeenegeeey
Success rate is 100 percent (60/60), round-trip min/avg/max = 1/1/4 ms
On R3
Note incoming packets that have a marking of DSCP 5 are mapped to outgoing CoS value of 6 and
NOT 0:
R3#Sh policy-map interface | s COSO
(match-al1)
, 0 bytes
5 minute offered rate 0 bps
R3#Sh policy-map interface |
(match=all)
, 7080 bytes
5 minute offered rate 0 bps
Match: cos 6
Task 4
DO NOT erase the startup configuration of the routers and the switches
10.44.0124 VIP Domain
1st
: worsan
Trunk Forts fos rao
Tank 3
40.44.0124
2
Task 1
> Remove the “service-policy input TST” command from F0/1.100 sub-interface
of R3.
> Remove the “Mls qos trust dsep” command from F0/19 interface of SW2.
You can copy and paste the initial configuration from the init directory
On R3
nfig)#int FO/1.100
nfig-subif) #No service-policy input TST
On SW2
$W2 (config) #Int FO/19
SW2(config-if)#No mls qos trust dsep
The configuration of the interfaces should resemble the following:
On SW2
Sw2#Sh run int F0/19
FastEthernet0/19
port trunk encapsulation dotiq
itchport mode trunk
SW2#Sh run int FO/3
FastEthernet0/3
port trunk encapsul
port mode trunk
Task 2
Configure F0/0 interface of R2 to match incoming traffic with marking of DSCP 0-7
and 56 using an MQC.
On R2
R2 (config) #Class-map DO
R2(config-cmap) #mateh ip dsep
R2 (config-cmap) #Class-map D1
R2(config-cmap) #match ip dsep
R2(config-cmap) #Class-map D2
R2(config-cmap) #match ip dscp
R2 (config-cmap) #Class-map D3
R2(config-cmap) #mateh ip dsep
R2(config-cmap) #Class-map D4
R2(config-cmap) #match ip dscp
R2(config-cmap) #Class-map D5
R2(config-cmap) #match ip dsep
R2 (conf ig-cmap) #Class-map D6
R2(config-cmap) #match ip dscp
R2 (config-cmap) #Class-map D7
R2(config-cmap) #match ip dscp 7
R2 (config-cmap) #Class-map D56
R2(config-cmap) #match ip dscp 56
R2 (config) #policy-map TST
R2 (config-pmap) #elass DO
R2 (config-pmap-c) #elass D1
R2 (config-pmap-c) #elass D2
R2 (config-pmap-c) #elass D3
R2 (config-pmap-c) #elass D4
R2 (config-pmap-c) #elass D5
R2 (conf ig-pmap-c) #elass Dé
R2 (config-pmap-c) #elass D7
R2 (config-pmap-c) #elass D56
R2 (config-pmap-c) #int F0/0
R2 (config-if) #service-policy in TST
Task 3
Configure the F0/3 interface of $W2 so that it marks all incoming traffic with a cos value
of 7 regardless of their existing marking
On SW2
SW2 (config) #int FO/3
SH fig-if)#mls qos cos 7
SWi2(config-if)#mls qos cos override
sk 4
Configure SW so that it maps the CoS value of 7 in incoming packets to a DSCP value
of 7 in the outgoing packets.
Before configuring this task we should display the default mapping, the following command reveals the
default mapping of CoS to DSCP:
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- HalfNelson PDFDocument2 pagesHalfNelson PDFradivojevicivan91100% (1)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- List of Power Metal BandsDocument8 pagesList of Power Metal BandslaviniandaNo ratings yet
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- A Monster in Paris JumpDocument9 pagesA Monster in Paris JumpZiggurathNo ratings yet
- 8 Teacher's Notes and Answer Keys: Classroom Practice WorksheetsDocument1 page8 Teacher's Notes and Answer Keys: Classroom Practice WorksheetsSilvia RuedaNo ratings yet
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Florence + The Machine - Blinding: em A5 (002200) Cm7 (032000) A5Document4 pagesFlorence + The Machine - Blinding: em A5 (002200) Cm7 (032000) A5Răzvan Constantin DincăNo ratings yet
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- Fender Mustang - v2 Manual PDFDocument14 pagesFender Mustang - v2 Manual PDFAndré Deniz Hanai100% (1)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Music Theory Secrets 94 Strategies For The Startin... - (Chapter 5 Scale Degree Names and Intervals)Document7 pagesMusic Theory Secrets 94 Strategies For The Startin... - (Chapter 5 Scale Degree Names and Intervals)Daniel BarónNo ratings yet
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Vals Nro. 2 de La Suite de Jazz: para Orquesta de CuerdasDocument3 pagesVals Nro. 2 de La Suite de Jazz: para Orquesta de CuerdasJo BedNo ratings yet
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- Greek Gods Infographic in Colorful Illustrative StyleDocument3 pagesGreek Gods Infographic in Colorful Illustrative StyleRey-ann VillanuevaNo ratings yet
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- William Smith: English None None NoneDocument2 pagesWilliam Smith: English None None NoneArthur NunesNo ratings yet
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- Big Fat Quiz of 2020Document36 pagesBig Fat Quiz of 2020Oisin GregorianNo ratings yet
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- David Kaplowitz's Odd Time PageDocument6 pagesDavid Kaplowitz's Odd Time PagedtalpoNo ratings yet
- Continuity and Differentiability ErrorlessDocument12 pagesContinuity and Differentiability Errorlessashmitaramoliya123No ratings yet
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Camp Rock Info PackDocument36 pagesCamp Rock Info PackLucas CockshottNo ratings yet
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Tong Hop CiputraDocument684 pagesTong Hop CiputraHai Tuan NguyenNo ratings yet
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- The Abington Journal 07-03-2013Document19 pagesThe Abington Journal 07-03-2013The Times LeaderNo ratings yet
- The-Last-of-the-MohicanArr - ViolinesDocument6 pagesThe-Last-of-the-MohicanArr - ViolinesJuan Pedro Medina García100% (1)
- Jingle Bells Partitur SATBDocument1 pageJingle Bells Partitur SATBFerdy G-men100% (3)
- Electric ResultDocument25 pagesElectric ResultBhanu Partap SharmaNo ratings yet
- The Rough Guide Mandarin Chinese Phrase BookDocument258 pagesThe Rough Guide Mandarin Chinese Phrase Bookอภิรักษ์ มานะกิจศิริสุทธิ93% (15)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- 3 QUICKSTART TUTORIAL FOR MOOG MODULAR VDocument25 pages3 QUICKSTART TUTORIAL FOR MOOG MODULAR VStefano Sintoni100% (1)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- Music 8 (Week 1)Document3 pagesMusic 8 (Week 1)ValerieNo ratings yet
- Lestat The Musical Sheet MusicDocument213 pagesLestat The Musical Sheet MusicChina Shaeffer100% (6)
- The Practicing MindDocument26 pagesThe Practicing MindJayne Spencer67% (3)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- Spanish Guitarist Daniel ForteaDocument2 pagesSpanish Guitarist Daniel ForteaLuis Alberto RameixNo ratings yet
- LjubljanaDocument47 pagesLjubljanaCristina RinaldiNo ratings yet
- Sally's Hobbies and FriendsDocument4 pagesSally's Hobbies and FriendsEvelina AguiarNo ratings yet
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (120)
- Mccormack John Collection PDFDocument27 pagesMccormack John Collection PDFarielsedanohaslenNo ratings yet
- Villa Lobos - FantasiaDocument6 pagesVilla Lobos - FantasiaBryan Canonigo100% (1)
- BachDouble 1002 (Guitar) PDFDocument2 pagesBachDouble 1002 (Guitar) PDFMarco Ignacio Toba100% (1)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)