Professional Documents
Culture Documents
Grade Signature 1 2 3 4 5 6: Ens Practical List
Uploaded by
harikrishna0 ratings0% found this document useful (0 votes)
41 views1 pageThis document contains an index of practical assignments related to computer security. It lists 18 assignments including studying security services, mechanisms, and attacks. Other assignments involve performing encryptions and decryptions using various cryptographic techniques like the Caesar cipher, Monoalphabetic cipher, Playfair cipher, and Hill cipher. Additional assignments include preparing reports on block cipher modes of operation, the Data Encryption Standard, and asymmetric encryption. The final assignments involve configuring security and firewall settings in Windows operating systems.
Original Description:
lksamkja
Original Title
ENS Practical Index
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis document contains an index of practical assignments related to computer security. It lists 18 assignments including studying security services, mechanisms, and attacks. Other assignments involve performing encryptions and decryptions using various cryptographic techniques like the Caesar cipher, Monoalphabetic cipher, Playfair cipher, and Hill cipher. Additional assignments include preparing reports on block cipher modes of operation, the Data Encryption Standard, and asymmetric encryption. The final assignments involve configuring security and firewall settings in Windows operating systems.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
41 views1 pageGrade Signature 1 2 3 4 5 6: Ens Practical List
Uploaded by
harikrishnaThis document contains an index of practical assignments related to computer security. It lists 18 assignments including studying security services, mechanisms, and attacks. Other assignments involve performing encryptions and decryptions using various cryptographic techniques like the Caesar cipher, Monoalphabetic cipher, Playfair cipher, and Hill cipher. Additional assignments include preparing reports on block cipher modes of operation, the Data Encryption Standard, and asymmetric encryption. The final assignments involve configuring security and firewall settings in Windows operating systems.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 1
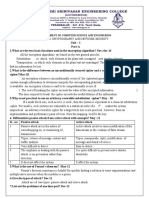
ENS PRACTICAL LIST
INDEX
Date of
Sr. No. Practical List Submission Grade Signature
1 To study various Security services.
2 To study various Security mechanisms.
3 To study various Security Attacks.
4 To study cryptanalysis.
5 Prepare report on various cryptographic technique.
Perform encryption of plain text and decryption of
6 cipher text of a using caesar cipher.
Perform encryption of a plain text and decryption of
7 cipher text using Monoaplhabetic cipher.
Perform encryption of a plain text and decryption of
cipher text using play fair cipher.
8
Perform encryption of a plain text and decryption of
a cipher text using polyalphabetic cipher
9
Perform encryption of a plain text and decryption of
cipher text using one time pad method
10
Perform encryption of a plain text and decryption of
cipher text using rectangular cipher
11
Perform encryption of a plain text and decryption of
cipher text using columnar cipher
12
Perform encryption of a plain text and decryption of
cipher text using Hill cipher
13
Prepare report on block cipher modes of operation.
14
15 Prepare report on single round of DES.
16 Prepare report on Asymmetric encryption
17 Configure Security in OS (Win XP / Win 7)
18 Configure firewall of (Winx XP/ Win 7)
You might also like
- Basic Ciphers: Ahmet Burak Can Hacettepe UniversityDocument37 pagesBasic Ciphers: Ahmet Burak Can Hacettepe UniversityOben Bessem GenolaNo ratings yet
- Lesson 3 Basic CryptographyDocument44 pagesLesson 3 Basic CryptographyEM Gaming0% (1)
- v10 Cheat PDFDocument49 pagesv10 Cheat PDFromaserge100% (1)
- Data Encryption Techniques and StandardsDocument59 pagesData Encryption Techniques and StandardsRajan Jamgekar100% (1)
- Cyber Security Course Syllabus: Day Topic / Contents Remarks 1 FNDocument3 pagesCyber Security Course Syllabus: Day Topic / Contents Remarks 1 FNsendhilNo ratings yet
- LabManual For Cryptography and Network SecurityDocument14 pagesLabManual For Cryptography and Network SecurityRajeshkannan Vasinathan100% (2)
- Cryptography and Network SecurityDocument8 pagesCryptography and Network SecuritySubhadip MajiNo ratings yet
- Network Security Lab ManualDocument46 pagesNetwork Security Lab ManualDANIELA CONDE HERRERANo ratings yet
- Cryptography and Network Security: List of PracticalDocument1 pageCryptography and Network Security: List of PracticalannuNo ratings yet
- InsindexDocument1 pageInsindexJayshree MevadaNo ratings yet
- CSS Lab Manual - 3Document1 pageCSS Lab Manual - 3Payal KhuspeNo ratings yet
- Gujarat Technological University: Diploma in Information TechnologyDocument3 pagesGujarat Technological University: Diploma in Information TechnologyK Nirmala AnantapurNo ratings yet
- Subject (Code) : Cryptography and Network Security (3161606) Class: BE III (Semester VI) - CSE / ITDocument2 pagesSubject (Code) : Cryptography and Network Security (3161606) Class: BE III (Semester VI) - CSE / ITdarshilgaming20102002No ratings yet
- 03B List of Experiments 2170709 INS Lab Manual 2017-18Document2 pages03B List of Experiments 2170709 INS Lab Manual 2017-18HarshKadiaNo ratings yet
- J 1417-Information Security (2014 Admn OnwardsDocument10 pagesJ 1417-Information Security (2014 Admn OnwardsLeslie QwerNo ratings yet
- CE348 Practical List 2019 FinalDocument1 pageCE348 Practical List 2019 FinalTANVI PATELNo ratings yet
- CS361 - CRNS - 22-23 - OBE Format - PracticalListDocument2 pagesCS361 - CRNS - 22-23 - OBE Format - PracticalListhelloNo ratings yet
- The New 1000 Franc NoteDocument13 pagesThe New 1000 Franc NoteGildardo Adolfo TovarNo ratings yet
- Ilovepdf MergedDocument13 pagesIlovepdf MergedPayal KhuspeNo ratings yet
- CSS Lab SyllabusDocument2 pagesCSS Lab Syllabus48Nara Amit GopalNo ratings yet
- CD 15B17CI576 Information Security LabDocument2 pagesCD 15B17CI576 Information Security Labpranav guptaNo ratings yet
- Chapter 10 - CryptographyDocument30 pagesChapter 10 - CryptographyPham Van LuongNo ratings yet
- 13-1 CH02.Cisco Network Security-FW, IPS, IPsec VPNsDocument92 pages13-1 CH02.Cisco Network Security-FW, IPS, IPsec VPNsSai PNo ratings yet
- NSC QUESTION BANK Unit 1Document7 pagesNSC QUESTION BANK Unit 1yuvaraaj aletiNo ratings yet
- CNS NotesDocument36 pagesCNS NotesAnjanaNo ratings yet
- Understanding IPSec (Modo de Compatibilidad)Document42 pagesUnderstanding IPSec (Modo de Compatibilidad)cordon162No ratings yet
- CNS 2 Mark FinalDocument10 pagesCNS 2 Mark FinalVijayakumar DNo ratings yet
- U21CS601 CT Unit 123 Part B QADocument13 pagesU21CS601 CT Unit 123 Part B QASanthosh kannaNo ratings yet
- Practicals Obj CODocument1 pagePracticals Obj COprafullaNo ratings yet
- Cs 12 Practical Term1Document18 pagesCs 12 Practical Term1Shreya AnandNo ratings yet
- Index: Sr. No. Title No Date SignDocument5 pagesIndex: Sr. No. Title No Date SignParthNo ratings yet
- SUB157380Document4 pagesSUB157380김동주No ratings yet
- Cryptography Question Bank Wihout AnswersDocument4 pagesCryptography Question Bank Wihout AnswerskingraajaNo ratings yet
- Lecture 9Document86 pagesLecture 9Alhussain DarbiNo ratings yet
- Information Security - PracticalDocument2 pagesInformation Security - PracticalDhruv SojitraNo ratings yet
- Net Security-Ch12 - IPS Operations and ImplementationDocument38 pagesNet Security-Ch12 - IPS Operations and Implementationyassin akkninnNo ratings yet
- B.Tech. Computer: Uka Tarsadia UniversityDocument6 pagesB.Tech. Computer: Uka Tarsadia UniversityPatelNo ratings yet
- Minor Project 19-20 PPT FormatDocument13 pagesMinor Project 19-20 PPT FormatSAI KUMAR N,CSE 16 Vel Tech, ChennaiNo ratings yet
- Advanced Encryption Standards (Aes)Document13 pagesAdvanced Encryption Standards (Aes)pulikondaNo ratings yet
- 03-Classical EncryptionDocument43 pages03-Classical Encryption6alal Ush100% (1)
- Question BankDocument8 pagesQuestion Bankvishal sahooNo ratings yet
- ISEHV7 Project ListDocument1 pageISEHV7 Project ListAppin NitinNo ratings yet
- 04 DSF VE1 - CryptographyDocument64 pages04 DSF VE1 - CryptographyBavindhran SonasundaranNo ratings yet
- Xavier Institute of Engineering: Lab ManualDocument55 pagesXavier Institute of Engineering: Lab ManualFarman HaiderNo ratings yet
- Homework 4: Explain The Following Terms Clearly With ExamplesDocument1 pageHomework 4: Explain The Following Terms Clearly With ExamplesAneelaMalikNo ratings yet
- Hands-On Ethical Hacking and Network DefenseDocument41 pagesHands-On Ethical Hacking and Network Defenseshabir AhmadNo ratings yet
- Question Bank: ObjectivesDocument7 pagesQuestion Bank: ObjectivesManjunath YadavNo ratings yet
- Lab5 IAA202Document4 pagesLab5 IAA202Đào Mạnh CôngNo ratings yet
- Practical ListDocument2 pagesPractical ListhelloNo ratings yet
- Question Paper With Some ProjectsDocument37 pagesQuestion Paper With Some ProjectsBASHYAM PNo ratings yet
- Cns QBDocument3 pagesCns QBDheepak NarsimhanNo ratings yet
- CCNA Security v5Document8 pagesCCNA Security v5Putri Isti ArifahNo ratings yet
- 2 Mark Questions Answers PDFDocument12 pages2 Mark Questions Answers PDFdurai muruganNo ratings yet
- Dhanalakshmi College of Engineering, ChennaiDocument12 pagesDhanalakshmi College of Engineering, ChennaiJayanthiVSNo ratings yet
- IASL Oral Question BankDocument8 pagesIASL Oral Question BankJeevjyot Singh ChhabdaNo ratings yet
- UntitledDocument22 pagesUntitledNarinder Singh KaboNo ratings yet
- Tugas Kelompok Teknologi Artificial Intelligence PresentasiDocument35 pagesTugas Kelompok Teknologi Artificial Intelligence PresentasiInas Rahma AlifiaNo ratings yet
- It8761 Set 4Document3 pagesIt8761 Set 4Saravana kumarNo ratings yet
- Practical Rust 1.x Cookbook: 100+ Solutions across Command Line, CI/CD, Kubernetes, Networking, Code Performance and MicroservicesFrom EverandPractical Rust 1.x Cookbook: 100+ Solutions across Command Line, CI/CD, Kubernetes, Networking, Code Performance and MicroservicesNo ratings yet