Professional Documents
Culture Documents
Network Security
Uploaded by
Menuka PandeyOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Network Security
Uploaded by
Menuka PandeyCopyright:
Available Formats
Chapter 8
Network Security
Networks and Cryptography
ISO/OSI model
Conceptually, each host has peer at each layer and
peers communicate with peers at same layer (see
books on network for detail)
Link and End-to-End Protocols
Let hosts C0, …, Cn be such that Ci and Ci+1 are directly
connected, for 0 ≤i < n. A communications protocol
that has C0 and Cn as its endpoints is called an end-to-
end protocol. A communications protocol that has Cj
and Cj+1 as its endpoints is called a link protocol.
The difference between an end-to-end protocol and a
link protocol is that the intermediate hosts play no
part in an end-to-end protocol other than forwarding
messages. Whereas, a link protocol describes how
each pair of intermediate hosts processes each
message.
Link encryption: Each host enciphers message and “next hop” host can read it i.e. intermediate hosts
can read the message. For e.g. In PPP Encryption Control Protocol host gets message, deciphers it,
figures out where to forward it, enciphers it in appropriate key and forwards it. Here each host shares
key with neighbor and can be set on per-host or per-host-pair basis. Link encryption can protect headers
al
of packets and it is possible to hide source and destination but, source can be deduced from traffic
ep
flows.
itn
Source: www.csitnepal.com (Compiled by Tej Shahi) Page 1
cs
End-to-end encryption: Host enciphers message so host at other end of communication can read it i.e.
message cannot be read at intermediate hosts for e.g. TELNET protocol where messages between client,
server enciphered, and encipherment, decipherment occur only at these hosts. In this approach each
host shares key with destination and can be set on per-host or per-host-pair basis. This approach cannot
hide packet headers and attacker can read source, destination.
Security at Different Layers
The following figure shows the security at different layers
Security at the Application Layer: E-Mail
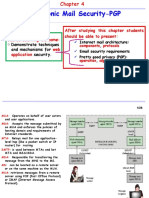
a) Pretty Good Privacy (PGP):
PGP is a public key encryption package to protect e-mail and data files. It lets you communicate
securely with people you've never met, with no secure channels needed for prior exchange of
keys. It's well featured and fast, with sophisticated key management, digital signatures, data
compression, and good ergonomic design. The actual operation of PGP is based on five services:
authentication, confidentiality, compression, e-mail compatibility, and segmentation.
al
- PGP provides authentication via a digital signature scheme.
- PGP provides confidentiality by encrypting messages before transmission
ep
- PGP compresses the message after applying the signature and before encryption. The
itn
Source: www.csitnepal.com (Compiled by Tej Shahi) Page 2
cs
idea is to save space.
- PGP encrypts a message together with the signature (if not sent separately) resulting into a
stream of arbitrary 8-bit octets. But since many e-mail systems permit only use of blocks
consisting of ASCII text, PGP accommodates this by converting the raw 8-bit binary streams
into streams of printable ASCII characters using a radix-64 conversion scheme. On receipt, the
block is converted back from radix-64 format to binary.
- To accommodate e-mail size restrictions, PGP automatically segments email messages that
are too long. However, the segmentation is done after all the housekeeping is done on the
message, just before transmitting it. So the session key and signature appear only once at the
beginning of the first segment transmitted. At receipt, the receiving PGP strips off all e-mail
headers and reassembles the original mail.
b) Privacy Enchanced Mail (PEM):
The figure below shows a typical network mail service. The U (user agent) interacts directly with
the sender. When the message is composed, the U hands it to the MT (message transport, or
transfer, agent). The MT transfers the message to its destination host, or to another MT, which in
turn transfers the message further. At the destination host, the MT invokes a user agent to deliver
the message.
U User
U U
A A A Agent
sMessage
MT MT MT
Transfer
A A A
An attacker can read electronic mail at any of the computers Agents
on which MTs handling the
message reside, as well as on the network itself. An attacker could also modify the message
without the recipient detecting the change. Because authentication mechanisms are minimal and
easily evaded, a sender could forge a letter from another and inject it into the message handling
system at any MT, from which it would be forwarded to the destination. Finally, a sender could
deny having sent a letter, and the recipient could not prove otherwise to a disinterested party.
al
These four types of attacks (violation of confidentiality, authentication, message integrity, and
ep
nonrepudiation) make electronic mail nonsecure. So IETF with the goal of e-mail privacy
develop electronic mail protocols that would provide the following services.
itn
Source: www.csitnepal.com (Compiled by Tej Shahi) Page 3
cs
1. Confidentiality, by making the message unreadable except to the sender and recipient(s)
2. Origin authentication, by identifying the sender precisely
3. Data integrity, by ensuring that any changes in the message are easy to detect
4. Nonrepudiation of origin (if possible)
The protocols were named Privacy-Enhanced Electronic Mail (or PEM).
PEM vs. PGP
– Use of different ciphers: PGP uses IDEA cipher but PEM uses DES in CBC mode.
– Use of certificate models: PGP uses general “web of trust” but PEM uses hierarchical
certification structure
– Handling end of line: PGP remaps end of line if message tagged “text”, but leaves them
alone if message tagged “binary” whereas PEM always remaps end of line.
Security at the Network Layer
- IPSec (Internet Protocol Security)
IPSec is a suite of authentication and encryption protocols developed by the Internet Engineering
Task Force (IETF) and designed to address the inherent lack of security for IP-based networks.
It is a collection of protocols and mechanisms that provide confidentiality, authentication,
message integrity, and replay detection at the IP layer. In the data transmission IPsec protect all
messages sent along a path. If the IPsec mechanisms reside on an intermediate host (for example,
a firewall or gateway), that host is called a security gateway.
IP IP+IPsec IP
dest gw2 gw1 src
security gateway
al
Security at the Transport Layer
ep
Secured Socket Layer (SSL)
itn
Source: www.csitnepal.com (Compiled by Tej Shahi) Page 4
cs
The Secure Socket Layer (SSL) is a standard developed by Netscape Corporation to provide
security in WWW browsers and servers. The current version, SSLv3, is the basis for an Internet
standard protocol under development. The newer protocol, the Transport Layer Security (TLS)
protocol, is compatible with SSLv3 and has only minor changes. It has not yet been adopted
formally.
SSL Main Goals
1. Cryptography security: One of the SSL protocol’s primary goals is to establish a secure
connection between two parties. A symmetric Encryption is used after an initial handshake to
define a secret key.
2. Reliability: The connection is reliable. Message transport includes a message integrity check
using a keyed MAC computed using secure hash functions.
3. Interoperability: Different applications should be able to successfully exchange
cryptographic parameters without knowledge of one another's code.
4. Extensibility: Provide a framework that allows new public-key and bulk encryption methods
to be incorporated as necessary. This will also achieve the goal of avoiding the need to
implement an entire new security library.
5. Relative efficiency: Cryptographic operations tend to be highly CPU intensive. For this
reason the SSL protocol has some options (such as caching and compression), which allow a
reduction in the number of connections that need to be established from scratch and a
reduction in network activity.
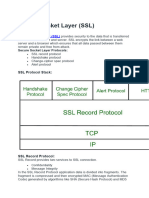
SSL Architecture
SSL, a set of protocols, uses TCP to provide reliable end to end service. SSLv3 consists of two
layers (see figure below) supported by numerous cryptographic mechanisms. The lower layer
called SSL Record Protocol provides the basic security services to various higher level protocols,
particularly HTTP. There are three higher level protocols that are defined as parts of SSL namely
SSL Handshake Protocol, the Change Cipher Spec Protocol, and Alert Protocol.
SSL works in terms of connections and sessions between
al
clients and servers. An SSL session is an association between
ep
two peers. An SSL connection is the set of mechanisms used
itn
Source: www.csitnepal.com (Compiled by Tej Shahi) Page 5
cs
to transport data in an SSL session. A single session may have many connections. Two peers
may have many sessions active at the same time, but this is not common.
Each party keeps information related to a session with each peer. The data associated with a
session includes the following information.
1. Session identifier: An arbitrary byte sequence chosen by the server to identify an active or
resumable session state
2. Peer certificate: X509.v3 certificate of the peer. This may be null.
3. Compression method: The algorithm used to compress data prior to encryption.
4. Cipher spec: Specifies the bulk data encryption algorithm (null, DES, etc.) and a MAC
algorithm (MD5 or SHA). It also defines attributes such as the hash_size.
5. Master secret: 48-byte secret shared between the client and server.
6. Is resumable: Defines whether the session can be used to initiate new connections.
A connection describes how data is sent to, and received from, the peer. Each party keeps
information related to a connection. Each peer has its own parameters. The information
associated with the connection includes the following.
1. Server and client random: Random data for server and client for each connection.
2. Server write MAC secret: Key for MAC operations on data written by the server.
3. Client write MAC secret: Key for MAC operations on data written by the client.
4. Server write key: Cipher key for encryption by the server and decryption by client.
5. Client write key: Cipher key for encryption by the client and decryption by server.
6. Initialization vectors (IV): When a block cipher in CBC mode is used, IV is maintained for
each key. This field is first initialized by the SSL handshake protocol then final ciphertext
block from each record is preserved for use with the next record.
7. Sequence numbers: Each party maintains separate sequence numbers for transmitted and
received messages for each connection. When a party sends or receives a change cipher
spec message, the appropriate sequence number is set to zero. Sequence numbers are of type
uint64 and may not exceed 264-1.
The SSL Handshake Protocol
al
This protocol, also called the key-exchange protocol, is responsible for establishing a secure
ep
session between two parties. The SSL handshake protocol can be divided to several important
stages:
itn
Source: www.csitnepal.com (Compiled by Tej Shahi) Page 6
cs
1. Authenticate the server to the client.
2. Negotiation of common cryptographic algorithms, that both server and client support.
3. Authenticate the client to the server (optional).
4. Using public-key encryption to exchange cryptography parameters (shared secrets).
5. Establish an encrypted SSL connection.
Firewalls
Firewall is hardware device or software applications that act as filters between a company’s
private network and the internet. It protects networked computers from intentional hostile
intrusion that could compromise confidentiality or result in data corruption or denial of service
by enforcing an access control policy between two networks.
The main purpose of a firewall system is to control access to or from a protected network (i.e., a
site). It implements a network access policy by forcing connections to pass through the firewall,
where they can be examined and evaluated. A firewall system can be a router, a personal
computer, a host, or a collection of hosts, set up specifically to shield a site or subnet from
protocols and services that can be abused from hosts outside the subnet. A firewall system is
usually located at a higher level gateway, such as a site's connection to the Internet, however
firewall systems can be located at lower-level gateways to provide protection for some smaller
collection of hosts or subnets. The main function of a firewall is to centralize access control. A
firewall serves as the gatekeeper between the untrusted Internet and the more trusted internal
networks. The earliest firewalls were simply routers.
Firewalls provide several types of protection:
al
- They can block unwanted traffic.
ep
- They can direct incoming traffic to more trustworthy internal systems.
itn
Source: www.csitnepal.com (Compiled by Tej Shahi) Page 7
cs
- They hide vulnerable systems, which can’t easily be secured from the Internet.
- They can log traffic to and from the private network.
- They can hide information like system names, network topology, network device
types, and internal user ID’s from the Internet.
- They can provide more robust authentication than standard applications might be
able to do.
al
ep
itn
Source: www.csitnepal.com (Compiled by Tej Shahi) Page 8
cs
You might also like
- Electronic Mail Security: Pretty Good Privacy (PGP)Document7 pagesElectronic Mail Security: Pretty Good Privacy (PGP)Remya RavindranNo ratings yet
- CRYPTOGRAPHY Notes Navin Kumar - 1Document25 pagesCRYPTOGRAPHY Notes Navin Kumar - 1IrshadNo ratings yet
- CCNP 2 VPN: 3.1.4 3.1.4 Characteristics of A Secure VpnsDocument15 pagesCCNP 2 VPN: 3.1.4 3.1.4 Characteristics of A Secure VpnsJayson AlbertoNo ratings yet
- Electronic Mail SecurityDocument20 pagesElectronic Mail SecurityAayatKhanNo ratings yet
- Unit 5 (Email Security)Document47 pagesUnit 5 (Email Security)Tisha NimjeNo ratings yet
- Unit 5 CNSDocument48 pagesUnit 5 CNScare pro100% (1)
- Unit-5 CNSDocument12 pagesUnit-5 CNSNikita KajalNo ratings yet
- Nis Unit Test 2Document5 pagesNis Unit Test 2Prajwal TilekarNo ratings yet
- Unit - 3Document41 pagesUnit - 3TamannaNo ratings yet
- DCN Unit 7Document40 pagesDCN Unit 7RazinNo ratings yet
- DS AssignmentDocument10 pagesDS AssignmentLILIAN KOMBANo ratings yet
- CNDocument2 pagesCNSurendar KumarNo ratings yet
- Network Security & CryptographyDocument7 pagesNetwork Security & CryptographySatya VaranasiNo ratings yet
- SMTP StandardDocument3 pagesSMTP Standardpajeje5059No ratings yet
- Unit VDocument48 pagesUnit VHANISHA SAALIHNo ratings yet
- Unit 5 CnsDocument20 pagesUnit 5 CnsSwetha SNo ratings yet
- VTU Network and Cyber Security Module-2 (15ec835, 17ec835) .Document36 pagesVTU Network and Cyber Security Module-2 (15ec835, 17ec835) .jayanthdwijesh h p80% (5)
- Cryptography and Network SecurityDocument16 pagesCryptography and Network SecuritysuryakasiNo ratings yet
- Is Chep-5Document39 pagesIs Chep-5Dhruv SojitraNo ratings yet
- Internet SecurityDocument18 pagesInternet SecurityJatin JainNo ratings yet
- Unit 5Document59 pagesUnit 5Shirly NNo ratings yet
- CNS Unit 5Document36 pagesCNS Unit 5aravind aravindNo ratings yet
- ASSIGNMENTDocument2 pagesASSIGNMENTNoeme Bichayda BeltranNo ratings yet
- Chapter 3 FinalDocument80 pagesChapter 3 FinalMihretu BekeleNo ratings yet
- CIT 612 Fundamentals of Computer Security: Mohammed A. Saleh 30 December 2009Document30 pagesCIT 612 Fundamentals of Computer Security: Mohammed A. Saleh 30 December 2009Herman KombaNo ratings yet
- Module 6 - Reading5 - InternetSecurityDocument7 pagesModule 6 - Reading5 - InternetSecurityChristopher AdvinculaNo ratings yet
- Topics To LearnDocument26 pagesTopics To LearnVidhya MohananNo ratings yet
- Mod4 Computer SecurityDocument16 pagesMod4 Computer SecurityJils ThomasNo ratings yet
- Chapter Two Part OneDocument53 pagesChapter Two Part Onesolomon berhanuNo ratings yet
- Email SecurityDocument7 pagesEmail SecuritysamuelNo ratings yet
- Networking Interview Q&ADocument5 pagesNetworking Interview Q&Asandeep singhNo ratings yet
- Network Security UNIT 4Document27 pagesNetwork Security UNIT 4smitcse2021No ratings yet
- Fibonacci Series PDFDocument4 pagesFibonacci Series PDFNinad SamelNo ratings yet
- 2 Marks CryptographyDocument13 pages2 Marks Cryptography219 DibyanshuKumarNo ratings yet
- Chapt4-E-mail Security-PGPDocument28 pagesChapt4-E-mail Security-PGPsomethingNo ratings yet
- Abstract and Full Paper On Network Security and CryptographyDocument10 pagesAbstract and Full Paper On Network Security and Cryptographyraaz_101No ratings yet
- Answer ShrutiDocument6 pagesAnswer ShrutiShruti KapoorNo ratings yet
- Ns 6Document35 pagesNs 6Harsha GangwaniNo ratings yet
- Latest Paper On CryptographyDocument14 pagesLatest Paper On Cryptographysundarrajan1068100% (7)
- C++ Tutorial - Sockets - Server & Client - 2015Document42 pagesC++ Tutorial - Sockets - Server & Client - 2015Charles Cesar Dias BarbosaNo ratings yet
- CS L05 Strategic Defense 1599311525486 PDFDocument46 pagesCS L05 Strategic Defense 1599311525486 PDFamitNo ratings yet
- 5-Network Security Applications - Email, IPSECDocument59 pages5-Network Security Applications - Email, IPSECep230842100% (1)
- Unit 3Document226 pagesUnit 3Rohit KoliNo ratings yet
- CryptographyDocument23 pagesCryptographyAnubhav KumarNo ratings yet
- Unit 5Document65 pagesUnit 5Vishal Kumar 1902712No ratings yet
- CNS - 2019Document27 pagesCNS - 2019Harikishna KN HkNo ratings yet
- Network Security and CryptographyDocument11 pagesNetwork Security and CryptographyRajesh Kumar JoshNo ratings yet
- QB104715Document4 pagesQB104715lingeshNo ratings yet
- Unit 5 - PGP, SmimeDocument43 pagesUnit 5 - PGP, Smimegadidheerajreddy.20.itNo ratings yet
- Unit-5 Application LayerDocument29 pagesUnit-5 Application LayerShatrughna BargeNo ratings yet
- Computer Networks: AssignmentDocument8 pagesComputer Networks: AssignmentJJ OLATUNJINo ratings yet
- Computer Security: Principles and Practice: Fourth Edition By: William Stallings and Lawrie BrownDocument30 pagesComputer Security: Principles and Practice: Fourth Edition By: William Stallings and Lawrie BrownJeremy David AlexanderNo ratings yet
- Crptography PPT-2Document48 pagesCrptography PPT-2vishnuvrNo ratings yet
- ECCDocument39 pagesECCYashwanth ReddyNo ratings yet
- ITNE 3013 Advanced Network and Information SecurityDocument4 pagesITNE 3013 Advanced Network and Information SecurityRupesh PandeyNo ratings yet
- Computer Network Assignment: Name: Islam, MD - Rashedul ID: 17-33685-1 Section: A Class Serial: 01Document2 pagesComputer Network Assignment: Name: Islam, MD - Rashedul ID: 17-33685-1 Section: A Class Serial: 01Rashedul IslamNo ratings yet
- The Guide of Implementing Chat Protocol: Study Case On Using The Socket Programming Concept and Object Oriented ProgrammingDocument9 pagesThe Guide of Implementing Chat Protocol: Study Case On Using The Socket Programming Concept and Object Oriented ProgrammingJournal of Computing100% (1)
- AdditionalDocument25 pagesAdditionalDeb Kant ChaudharyNo ratings yet
- Hacking Network Protocols: Unlocking the Secrets of Network Protocol AnalysisFrom EverandHacking Network Protocols: Unlocking the Secrets of Network Protocol AnalysisNo ratings yet
- (Authentication and Public Key Infrastructure (PKI) )Document14 pages(Authentication and Public Key Infrastructure (PKI) )Menuka PandeyNo ratings yet
- Digital SignatureDocument7 pagesDigital SignatureMenuka PandeyNo ratings yet
- Hashing and Message DigestDocument9 pagesHashing and Message DigestMenuka PandeyNo ratings yet
- Public Key CryptoDocument17 pagesPublic Key CryptoMenuka PandeyNo ratings yet
- FinalCopyADBMS PDFDocument8 pagesFinalCopyADBMS PDFMenuka PandeyNo ratings yet
- projectADBMS PDFDocument2 pagesprojectADBMS PDFMenuka PandeyNo ratings yet
- Data Integrity Auditing Without Private Key Storage For Secure Cloud StorageDocument3 pagesData Integrity Auditing Without Private Key Storage For Secure Cloud StorageInternational Journal of Trendy Research in Engineering and TechnologyNo ratings yet
- Message Authentication in Computationally Constrained EnvironmentDocument21 pagesMessage Authentication in Computationally Constrained Environmentriskbaskar88No ratings yet
- Data Encryption Standard (DES)Document74 pagesData Encryption Standard (DES)Dhanesh GoelNo ratings yet
- Block CiphersDocument25 pagesBlock CiphersAnkur Agrawal100% (1)
- Asa 91 VPN ConfigDocument472 pagesAsa 91 VPN Configсниматељ ЗоранNo ratings yet
- Secure DLMS/COSEM Communication For Next Generation Advanced Metering InfrastructureDocument7 pagesSecure DLMS/COSEM Communication For Next Generation Advanced Metering Infrastructurejayakrishna SNo ratings yet
- Acp-125 (F)Document125 pagesAcp-125 (F)jesayersNo ratings yet
- AES: An Advanced Cryptographic Approach With New Dimensions in The Field of Network SecurityDocument28 pagesAES: An Advanced Cryptographic Approach With New Dimensions in The Field of Network SecurityAntima ChandraNo ratings yet
- M Configuring Password Encryption 922Document6 pagesM Configuring Password Encryption 922Heera SinghNo ratings yet
- Part IV Debit Credit Application Security SpecificationDocument87 pagesPart IV Debit Credit Application Security SpecificationMai Nam Thang100% (1)
- Asterix Band 16 Asterix Bei Den Schweizern PDFDocument46 pagesAsterix Band 16 Asterix Bei Den Schweizern PDFJulia Jungle10% (10)
- Example of DESDocument10 pagesExample of DESkerya ibrahimNo ratings yet
- Entrust and You New VersionDocument40 pagesEntrust and You New VersionAhmad ShahinNo ratings yet
- 2.1 Crypto ClassicDocument9 pages2.1 Crypto ClassicAdit DutNo ratings yet
- Crypto Slides 14 PK Tutor.1x1 PDFDocument22 pagesCrypto Slides 14 PK Tutor.1x1 PDFttphgNo ratings yet
- Topic - 04 - Public Key Cryptography and MSG AuthDocument27 pagesTopic - 04 - Public Key Cryptography and MSG AuthHenry Fu KeatNo ratings yet
- Tacsi 2011Document76 pagesTacsi 2011Scarlet Mihaela IuliaNo ratings yet
- Algebra S-BOX SerpentDocument4 pagesAlgebra S-BOX SerpentghionoiucNo ratings yet
- Blockchain Glossary enDocument2 pagesBlockchain Glossary enRommel RosillonNo ratings yet
- Module 0Document96 pagesModule 0Mohan RaghuNo ratings yet
- SSL TLSDocument19 pagesSSL TLSDaniel YaoNo ratings yet
- NSC QUESTION BANK Unit 1Document7 pagesNSC QUESTION BANK Unit 1yuvaraaj aletiNo ratings yet
- 2.05 Application of Matrices in CryptographyDocument4 pages2.05 Application of Matrices in Cryptographysujhaz31No ratings yet
- CISSP Combined NotesDocument59 pagesCISSP Combined NotesAnonymous 9d1jFv100% (4)
- 7.1 HashCalcDocument5 pages7.1 HashCalcBolajiKoyiNo ratings yet
- Lecture 8: AES: The Advanced Encryption Standard Lecture Notes On "Computer and Network Security"Document93 pagesLecture 8: AES: The Advanced Encryption Standard Lecture Notes On "Computer and Network Security"Hamzah AkhtarNo ratings yet
- Feistel AlgorithmDocument38 pagesFeistel AlgorithmpkvlaserNo ratings yet
- Future Generation Computer Systems: Sherman S.M. Chow, Kim-Kwang Raymond Choo, Jinguang HanDocument2 pagesFuture Generation Computer Systems: Sherman S.M. Chow, Kim-Kwang Raymond Choo, Jinguang HanbashaeNo ratings yet
- CH13 Testbank Crypto6eDocument6 pagesCH13 Testbank Crypto6eHenna Shaina100% (1)