Professional Documents
Culture Documents
CCIE Security Lab Exam Topics v4.0 System Hardening and Availability
Uploaded by
aliahmadqj0 ratings0% found this document useful (0 votes)
24 views3 pagesOriginal Title
CCIE Sec v4
Copyright
© © All Rights Reserved
Available Formats
DOCX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
24 views3 pagesCCIE Security Lab Exam Topics v4.0 System Hardening and Availability
Uploaded by
aliahmadqjCopyright:
© All Rights Reserved
Available Formats
Download as DOCX, PDF, TXT or read online from Scribd
You are on page 1of 3
CCIE Security Lab Exam Topics v4.
0
The following topics are general guidelines for the content likely to be included on the lab exam.
However, other related topics may also appear on any specific delivery of the exam. In order to
reflect better the contents of the exam and for clarity purposes, the exam topics may change at
any time without notice.
Candidates may be required to perform implementation, optimization and troubleshooting
actions in each of the exam topics sections and should also be comfortable with both IPv4 and
IPv6 concepts and application.
CCIE Security Lab Exam Topics v4.0
System Hardening and Availability
Routing plane security features (e.g. protocol authentication, route filtering)
Control Plane Policing
Control Plane Protection and Management Plane Protection
Broadcast control and switchport security
Additional CPU protection mechanisms (e.g. options drop, logging interval)
Disable unnecessary services
Control device access (e.g. Telnet, HTTP, SSH, Privilege levels)
Device services (e.g. SNMP, Syslog, NTP)
Transit Traffic Control and Congestion Management
Threat Identification and Mitigation
Identify and protect against fragmentation attacks
Identify and protect against malicious IP option usage
Identify and protect against network reconnaissance attacks
Identify and protect against IP spoofing attacks
Identify and protect against MAC spoofing attacks
Identify and protect against ARP spoofing attacks
Identify and protect against Denial of Service (DoS) attacks
Identify and protect against Distributed Denial of Service (DDoS) attacks
Identify and protect against Man-in-the-Middle (MiM) attacks
Identify and protect against port redirection attacks
Identify and protect against DHCP attacks
Identify and protect against DNS attacks
Identify and protect against MAC Flooding attacks
Identify and protect against VLAN hopping attacks
Identify and protect against various Layer2 and Layer3 attacks
NBAR
NetFlow
Capture and utilize packet captures
Intrusion Prevention and Content Security
IPS 4200 Series Sensor Appliance
(a) Initialize the Sensor Appliance
(b) Sensor Appliance management
(c) Virtual Sensors on the Sensor Appliance
(d) Implementing security policies
(e) Promiscuous and inline monitoring on the Sensor Appliance
(f) Tune signatures on the Sensor Appliance
(g) Custom signatures on the Sensor Appliance
(h) Actions on the Sensor Appliance
(i) Signature engines on the Sensor Appliance
(j) Use IDM/IME to the Sensor Appliance
(k) Event action overrides/filters on the Sensor Appliance
(l) Event monitoring on the Sensor Appliance
VACL/SPAN & RSPAN on Cisco switches
WSA
(a) Implementing WCCP
(b) Active Dir Integration
(c)Custom Categories
(d) HTTPS Config
(e) Services Configuration (Web Reputation)
(f) Configuring Proxy By-pass Lists
(g) Web proxy modes
(h) App visibility and control
Identity Management
Identity Based Authentication/Authorization/Accounting
(a) Cisco Router/Appliance AAA
(b) RADIUS
(c)TACACS+
Device Admin (Cisco IOS Routers, ASA, ACS5.x)
Network Access (TrustSec Model)
(a) Authorization Results for Network Access (ISE)
(b) 802.1X (ISE)
(c)VSAs (ASA / Cisco IOS / ISE)
(d) Proxy-Authentication (ISE/ASA/Cisco IOS)
Cisco Identity Services Engine (ISE)
(a) Profiling Configuration (Probes)
(b) Guest Services
(c)Posture Assessment
(d) Client Provisioning (CPP)
(e) Configuring AD Integration/Identity Sources
Perimeter Security and Services
Cisco ASA Firewall
(a) Basic firewall Initialization
(b) Device management
(c ) Address translation (nat, global, static)
(d) Access Control Lists
(e) IP routing/Route Tracking
(f) Object groups
(g) VLANs
(h) Configuring Etherchannel
(i) High Availability and Redundancy
(j) Layer 2 Transparent Firewall
(k) Security contexts (virtual firewall)
(l) Modular Policy Framework
(j) Identity Firewall Services
(k) Configuring ASA with ASDM
(l) Context-aware services
(m) IPS capabilities
(n) QoS capabilities
Cisco IOS Zone Based Firewall
(a) Network, Secure Group and User Based Policy
(b) Performance Tuning
(c) Network, Protocol and Application Inspection
Perimeter Security Services
(a) Cisco IOS QoS and Packet marking techniques
(b) Traffic Filtering using Access-Lists
(c)Cisco IOS NAT
(d) uRPF
(e) PAM - Port to Application Mapping
(f) Policy Routing and Route Maps
Confidentiality and Secure Access
IKE (V1/V2)
IPsec LAN-to-LAN (Cisco IOS/ASA)
Dynamic Multipoint VPN (DMVPN)
FlexVPN
Group Encrypted Transport (GET) VPN
Remote Access VPN
(a) Easy VPN Server (Cisco IOS/ASA)
(b) VPN Client 5.X
(c)Clientless WebVPN
(d) AnyConnect VPN
(e) EasyVPN Remote
(f) SSL VPN Gateway
VPN High Availability
QoS for VPN
VRF-aware VPN
MacSec
Digital Certificates (Enrollment and Policy Matching)
Wireless Access
(a) EAP methods
(b) WPA/WPA-2
(c)WIPS
You might also like
- CompTIA Security+ Study Guide with over 500 Practice Test Questions: Exam SY0-701From EverandCompTIA Security+ Study Guide with over 500 Practice Test Questions: Exam SY0-701No ratings yet
- Certifications: 1) EC-CouncilDocument4 pagesCertifications: 1) EC-CouncilAbhishek SantraNo ratings yet
- CV Martin VoelkDocument8 pagesCV Martin VoelkMonikaTheBestNo ratings yet
- Cisco Press - Network Security Technologies and SolutionsDocument620 pagesCisco Press - Network Security Technologies and SolutionsMaulana Arief WijayaNo ratings yet
- CV Martin VoelkDocument7 pagesCV Martin VoelkAbdul RahimNo ratings yet
- BlueCoat - Configuration and Management Guide - 5.xDocument241 pagesBlueCoat - Configuration and Management Guide - 5.xGonzaloSotoNo ratings yet
- 1Z0 997 21 - PDFVersionDocument44 pages1Z0 997 21 - PDFVersionGaurav Saxena100% (2)
- Fortigate /fortiwifi - 60C Series: Integrated Threat Management For Frontline LocationsDocument7 pagesFortigate /fortiwifi - 60C Series: Integrated Threat Management For Frontline LocationsAndy KwongNo ratings yet
- CV Martin VoelkDocument7 pagesCV Martin VoelkJoko HartonoNo ratings yet
- Nondisruptive Operations For ONTAP 9.5: May 2019 - SL10540 Version 2.1Document47 pagesNondisruptive Operations For ONTAP 9.5: May 2019 - SL10540 Version 2.1Robert BautistaNo ratings yet
- Cisco SolutionsDocument28 pagesCisco Solutionsprayukth100% (1)
- Cisco Network Foundation Protection OverviewDocument10 pagesCisco Network Foundation Protection OverviewRyanb378No ratings yet
- Serveraid M5014/M5015 Sas/Sata Controllers: User'S GuideDocument92 pagesServeraid M5014/M5015 Sas/Sata Controllers: User'S GuideAntonNo ratings yet
- Oscam Only+0963 Card+Omnikey 3121 TutorialDocument3 pagesOscam Only+0963 Card+Omnikey 3121 TutorialTiago SantosNo ratings yet
- FREE Cisco CCNP Security-SCOR-350-701Document10 pagesFREE Cisco CCNP Security-SCOR-350-701Riyas Binkader0% (1)
- 350 701 Scor PDFDocument4 pages350 701 Scor PDFDinesh ShahiNo ratings yet
- Summative Test 2 (Tle 7 & 8)Document4 pagesSummative Test 2 (Tle 7 & 8)JoelmarMondonedo100% (1)
- CCIE Security Lab Exam Topics v4.0Document5 pagesCCIE Security Lab Exam Topics v4.0Rohit SharmaNo ratings yet
- CCIE ® Security v3.0 Written Exam Topics: Eneral EtworkingDocument5 pagesCCIE ® Security v3.0 Written Exam Topics: Eneral Etworkingshiva.yaragal100% (1)
- CCIE Security Lab Exam v4.0 ChecklistDocument18 pagesCCIE Security Lab Exam v4.0 ChecklistBimal Roy MehtaNo ratings yet
- Implementing Cisco Network Security Exam (210-260) : Security Concepts Common Security PrinciplesDocument4 pagesImplementing Cisco Network Security Exam (210-260) : Security Concepts Common Security PrinciplesMangesh AbnaveNo ratings yet
- CCIE Security Lab Exam v3Document11 pagesCCIE Security Lab Exam v3João VictorNo ratings yet
- 350 701 SCOR v1.1Document4 pages350 701 SCOR v1.1You YouNo ratings yet
- CIT2251 CCNA Security SyllabusDocument4 pagesCIT2251 CCNA Security SyllabusHomerKhanNo ratings yet
- Exam Sections and Sub-Task Objectives: 1.00 Implement Layer 2 TechnologiesDocument9 pagesExam Sections and Sub-Task Objectives: 1.00 Implement Layer 2 TechnologiesryanadzimaNo ratings yet
- CCIE TemasDocument5 pagesCCIE TemasRoxanna SalcieNo ratings yet
- CCIE DC Course Content DownloadDocument8 pagesCCIE DC Course Content DownloadAnubhavNayakNo ratings yet
- CCNP 350-601 Data Centre Course OutlineDocument3 pagesCCNP 350-601 Data Centre Course OutlineSubasish BiswalNo ratings yet
- CV Martin VoelkDocument7 pagesCV Martin VoelkAbdullah HabibNo ratings yet
- Infa Admin TrainingDocument2 pagesInfa Admin TrainingacechinmayNo ratings yet
- CCIE Security v6 Learning MatrixDocument23 pagesCCIE Security v6 Learning MatrixFaizan Ul HaqNo ratings yet
- Ccna Security: Exam DescriptionDocument5 pagesCcna Security: Exam DescriptionAsha KatolNo ratings yet
- Course TopicsDocument7 pagesCourse TopicsSeanNo ratings yet
- v6 CcieDocument23 pagesv6 Ccieshadab umairNo ratings yet
- FortiGate 1240BDocument6 pagesFortiGate 1240Bw0lfmast3rNo ratings yet
- ArcSight Supported ProductsDocument3 pagesArcSight Supported ProductsSzu-Khiam OoiNo ratings yet
- 1-Introduction To Networks: The Open Systems Interconnection SpecificationsDocument12 pages1-Introduction To Networks: The Open Systems Interconnection Specificationsfatemeh sameniNo ratings yet
- 400 251 CciesecurityDocument5 pages400 251 CciesecurityMichael O'ConnellNo ratings yet
- CCIE Security - Syllabus PDFDocument7 pagesCCIE Security - Syllabus PDFNETWORKERS HOMENo ratings yet
- HP ArcSight SmartConnectors Supported ProductsDocument3 pagesHP ArcSight SmartConnectors Supported ProductssalamsalarNo ratings yet
- Security Consultant Resume Template-72182Document7 pagesSecurity Consultant Resume Template-72182Tecnología Fácil (TecnoFacilMX)No ratings yet
- ASA SFR Overview and DesignDocument27 pagesASA SFR Overview and Designzamis aliNo ratings yet
- Dccor 1.1Document4 pagesDccor 1.1Erick GitahiNo ratings yet
- SSG5 SSG20Document4 pagesSSG5 SSG20ScribdUser250No ratings yet
- Domain Domain Number Written Exam Percentage (%) Written Exam Study HoursDocument14 pagesDomain Domain Number Written Exam Percentage (%) Written Exam Study HoursRupesh AinarkarNo ratings yet
- Implementing Cisco IOS Network SecurityDocument2 pagesImplementing Cisco IOS Network SecuritySteven SwansonNo ratings yet
- Routing Route Maps Prefix List PBR Route Redistribution MplsDocument24 pagesRouting Route Maps Prefix List PBR Route Redistribution MplsSudhakar PrabhuNo ratings yet
- Enterprise Network Services Design (IPv6)Document1 pageEnterprise Network Services Design (IPv6)note10 naxoshkNo ratings yet
- Cisco: 210-260 ExamDocument20 pagesCisco: 210-260 ExamTanveer AkhtarNo ratings yet
- Implementing and Administering Cisco Solutions (CCNA) : Related Certificate Course ID Related Exam Audience HoursDocument6 pagesImplementing and Administering Cisco Solutions (CCNA) : Related Certificate Course ID Related Exam Audience HoursChristina FingtonNo ratings yet
- ArcSight Supported ProductsDocument3 pagesArcSight Supported ProductsDragos LunguNo ratings yet
- Cisco Prime Support DevicesDocument181 pagesCisco Prime Support DevicesjoNo ratings yet
- Baudelaire, Aghomo NoumedemDocument6 pagesBaudelaire, Aghomo Noumedemashish ojhaNo ratings yet
- Christopher T. Ruggieri: Summary of QualificationsDocument5 pagesChristopher T. Ruggieri: Summary of QualificationsAshwani kumarNo ratings yet
- H3C SecPath F100-C-A3 Next Generation Firewall DatasheetDocument7 pagesH3C SecPath F100-C-A3 Next Generation Firewall DatasheetNMĐG Chơ Long - Yang TrungNo ratings yet
- Cyberoam CR15 I NGDocument2 pagesCyberoam CR15 I NGravinaiduNo ratings yet
- 2015년 교육안내문Document169 pages2015년 교육안내문waitslipknotbleedNo ratings yet
- Contact Us: Get All The Support You NeedDocument3 pagesContact Us: Get All The Support You NeedBilal LatifNo ratings yet
- PG Diploma in IT InfrastructureDocument5 pagesPG Diploma in IT InfrastructureJoseph NgatungaNo ratings yet
- ASA Pre-8.3 To 8.3 NAT Configuration Examples Firewalling Cisco Support CommunityDocument28 pagesASA Pre-8.3 To 8.3 NAT Configuration Examples Firewalling Cisco Support CommunitySatish KatakamNo ratings yet
- HP ArcSight SmartConnectors Supported ProductsDocument3 pagesHP ArcSight SmartConnectors Supported ProductsANNguyenNo ratings yet
- CISSP Fast Track Master: CISSP Essentials for Exam Success - Exam Cram Notes: 1st Edition - 2024From EverandCISSP Fast Track Master: CISSP Essentials for Exam Success - Exam Cram Notes: 1st Edition - 2024No ratings yet
- Wildcard Exercises AnswersDocument3 pagesWildcard Exercises AnswersRakeshNo ratings yet
- Configuring TACACS+: in This ChapterDocument12 pagesConfiguring TACACS+: in This ChapteraliahmadqjNo ratings yet
- Configuring RADIUS: in This ChapterDocument32 pagesConfiguring RADIUS: in This ChapteraliahmadqjNo ratings yet
- BGPDocument30 pagesBGPdnow4pNo ratings yet
- Configuring RADIUS: in This ChapterDocument32 pagesConfiguring RADIUS: in This ChapteraliahmadqjNo ratings yet
- Dot1x PDFDocument72 pagesDot1x PDFabijith13No ratings yet
- A A ADocument6 pagesA A AsmoothmatrixNo ratings yet
- DHCP ConfigurationDocument16 pagesDHCP ConfigurationGopi ChowdaryNo ratings yet
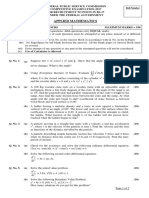
- Applied Maths-2017 UpdatedDocument2 pagesApplied Maths-2017 UpdatedMuhammad Ishtiaq100% (1)
- History of Pakistan and India 2015 PDFDocument2 pagesHistory of Pakistan and India 2015 PDFLaraib ZahidNo ratings yet
- SnoodhcpDocument20 pagesSnoodhcpAbdo KasraouiNo ratings yet
- Hindu Muslim ConflictDocument192 pagesHindu Muslim ConflictWaqas AyubNo ratings yet
- A Short History of Muslim Rule in India (Ishwari Parsad) PDFDocument852 pagesA Short History of Muslim Rule in India (Ishwari Parsad) PDFaliahmadqjNo ratings yet
- Configure Cisco Jabber For MACDocument16 pagesConfigure Cisco Jabber For MACAnonymous gKDNMqS6No ratings yet
- 200 125 Ccna v3Document7 pages200 125 Ccna v3Azaz Dobiwala100% (1)
- 100 105 Icnd1 v3 PDFDocument4 pages100 105 Icnd1 v3 PDFanon_348665676No ratings yet
- Cooperative Multi-Tasking in The C LanguageDocument10 pagesCooperative Multi-Tasking in The C LanguageDanielTheGreatAuNo ratings yet
- ReadmeDocument2 pagesReadmeAngelito AcostaNo ratings yet
- ReadmeDocument6 pagesReadmenicole valentina malagon cardonaNo ratings yet
- Attrib - Edit File Attributes - Windows CMD - SS64Document3 pagesAttrib - Edit File Attributes - Windows CMD - SS64gupta_gk4uNo ratings yet
- Configuring Automated Maintenance TasksDocument7 pagesConfiguring Automated Maintenance TasksShah RashidNo ratings yet
- Traps - Latest Release: Peter Lechman, Jakub JiricekDocument20 pagesTraps - Latest Release: Peter Lechman, Jakub JiricekYura ZverNo ratings yet
- Apollo OPT X: Extending Otn/Packet Switching To The Network EdgeDocument2 pagesApollo OPT X: Extending Otn/Packet Switching To The Network Edgerobert adamsNo ratings yet
- Gujarat Technological University Branch: Cyber Security (59) Subject Name: Malware Analysis SUBJECT CODE: 2725908 Semester: IiDocument3 pagesGujarat Technological University Branch: Cyber Security (59) Subject Name: Malware Analysis SUBJECT CODE: 2725908 Semester: IiRenugadevi NavaneethakrishnanNo ratings yet
- Read Me First Experts Updated v6fDocument3 pagesRead Me First Experts Updated v6fDavidSawNo ratings yet
- Lab 4Document21 pagesLab 4Geoff0% (1)
- OLT GX3500-S2 Datasheet - ENDocument2 pagesOLT GX3500-S2 Datasheet - ENkentmultanNo ratings yet
- Using MPLS Auto-Bw in MPLS NetworksDocument11 pagesUsing MPLS Auto-Bw in MPLS NetworksThang Doan Minh100% (2)
- Commandes Installation DspaceDocument7 pagesCommandes Installation DspaceAbdelkader GhezNo ratings yet
- Mecanografia SenaDocument6 pagesMecanografia SenaSebastián Díaz RiveraNo ratings yet
- Penawaran LagoonAvenue - AiscommDocument3 pagesPenawaran LagoonAvenue - AiscommGay delikkeNo ratings yet
- Novela Cantaclaro Romulo Gallegos PDFDocument4 pagesNovela Cantaclaro Romulo Gallegos PDFSofia OchoaNo ratings yet
- WWW Devicemanuals EuDocument129 pagesWWW Devicemanuals EuSamordeithNo ratings yet
- Binary To Octal:: Clar, Steve E. Exercise 1Document3 pagesBinary To Octal:: Clar, Steve E. Exercise 1Steve ClarNo ratings yet
- Hostingultraso Com Dedicated-Server ColombiaDocument8 pagesHostingultraso Com Dedicated-Server Colombiamansi bishtNo ratings yet
- Ueye SDK Manual EnuDocument215 pagesUeye SDK Manual EnukrakraoNo ratings yet
- Allama Iqbal Open University, Islamabad (Department of Computer Science) WarningDocument4 pagesAllama Iqbal Open University, Islamabad (Department of Computer Science) Warninggulzar ahmadNo ratings yet
- Olusola Aminat Ayomide: A Seminar Report On Mobile Based Network Monitoring SystemDocument8 pagesOlusola Aminat Ayomide: A Seminar Report On Mobile Based Network Monitoring SystemlekanNo ratings yet
- Perfil Mandatório Windows 10Document79 pagesPerfil Mandatório Windows 10Fabio Borges de FreitasNo ratings yet
- WorkCentre 7830-7835 071.Xxx To 073.Xxx Upgrade Instructions v1Document9 pagesWorkCentre 7830-7835 071.Xxx To 073.Xxx Upgrade Instructions v1Ruben Moncada RugelNo ratings yet