Professional Documents
Culture Documents
HUAWEI SecoClient User Access Guide
Uploaded by
ep230842Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
HUAWEI SecoClient User Access Guide
Uploaded by
ep230842Copyright:
Available Formats
HUAWEI SecoClient
7.0.2
User Access Guide
Issue 05
Date 2019-09-23
HUAWEI TECHNOLOGIES CO., LTD.
Copyright © Huawei Technologies Co., Ltd. 2020. All rights reserved.
No part of this document may be reproduced or transmitted in any form or by any means without prior
written consent of Huawei Technologies Co., Ltd.
Trademarks and Permissions
and other Huawei trademarks are trademarks of Huawei Technologies Co., Ltd.
All other trademarks and trade names mentioned in this document are the property of their respective
holders.
Notice
The purchased products, services and features are stipulated by the contract made between Huawei and
the customer. All or part of the products, services and features described in this document may not be
within the purchase scope or the usage scope. Unless otherwise specified in the contract, all statements,
information, and recommendations in this document are provided "AS IS" without warranties, guarantees
or representations of any kind, either express or implied.
The information in this document is subject to change without notice. Every effort has been made in the
preparation of this document to ensure accuracy of the contents, but all statements, information, and
recommendations in this document do not constitute a warranty of any kind, express or implied.
Huawei Technologies Co., Ltd.
Address: Huawei Industrial Base
Bantian, Longgang
Shenzhen 518129
People's Republic of China
Website: https://www.huawei.com
Email: support@huawei.com
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. i
HUAWEI SecoClient
User Access Guide Contents
Contents
1 Document Information...........................................................................................................1
2 Getting Started........................................................................................................................ 5
3 Installing the Software.......................................................................................................... 7
3.1 Installation Precautions......................................................................................................................................................... 8
3.2 Obtaining the Software Installation Package................................................................................................................9
3.3 Installing the Software in the Windows System........................................................................................................ 10
3.4 Installing the Software in the Mac OS.......................................................................................................................... 11
3.5 Installing the Software in the Linux System................................................................................................................ 12
4 Configuring a VPN Connection.......................................................................................... 14
4.1 Configuring an SSL VPN Connection............................................................................................................................. 15
4.2 Configuring an L2TP VPN Connection........................................................................................................................... 18
4.3 Configuring an L2TP over IPSec VPN Connection..................................................................................................... 23
4.4 Configuring a VPN Connection by Importing a Configuration File..................................................................... 30
5 Establishing a VPN Connection..........................................................................................33
5.1 Initiating a VPN Connection..............................................................................................................................................33
5.2 User Identity Authentication............................................................................................................................................. 34
5.2.1 User Name/Password Authentication........................................................................................................................ 35
5.2.2 Authentication by Importing the PKI Digital Certificate......................................................................................36
5.2.3 USB Key Authentication.................................................................................................................................................. 37
5.2.4 Two-Factor Authentication.............................................................................................................................................39
6 Optional Configurations...................................................................................................... 40
6.1 Uninstalling the SecoClient............................................................................................................................................... 40
6.2 Version Detection and Upgrade....................................................................................................................................... 41
6.3 Changing the Login Password.......................................................................................................................................... 42
6.4 Other Configurations........................................................................................................................................................... 42
7 Troubleshooting.....................................................................................................................45
7.1 Collecting InformationRequired for Troubleshooting............................................................................................... 45
7.1.1 Collecting an Error Report.............................................................................................................................................. 46
7.1.2 Exporting the Configuration File.................................................................................................................................. 48
7.2 Installation and Upgrade Faults...................................................................................................................................... 48
7.3 Connection Faults................................................................................................................................................................. 49
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. ii
HUAWEI SecoClient
User Access Guide Contents
7.4 Service Faults.......................................................................................................................................................................... 49
8 Appendix..................................................................................................................................52
8.1 Mobile Client.......................................................................................................................................................................... 52
8.2 Using Commands to Configure the Client in the Linux System........................................................................... 55
8.2.1 Starting the Client............................................................................................................................................................. 55
8.2.2 Configuring an SSL VPN Connection.......................................................................................................................... 56
8.2.3 Configuring an L2TP VPN Connection....................................................................................................................... 58
8.2.4 Configuring an L2TP over IPSec VPN Connection.................................................................................................. 60
8.3 VPN Configuration and Connection Templates.......................................................................................................... 63
8.3.1 SSL VPN Configuration and Connection Template................................................................................................ 63
8.3.2 L2TP VPN Configuration and Connection Template............................................................................................. 65
8.3.3 L2TP over IPSec VPN Configuration and Connection Template........................................................................66
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. iii
HUAWEI SecoClient
User Access Guide 1 Document Information
1 Document Information
Product Version
This document applies to the SecoClient products of 5.0.1 and later versions.
Intended Audience
This document is intended for mobile device users who need to establish VPN
connections through the SecoClient. You can complete the VPN connection
configuration on your mobile device by referring to Getting Started to access
resources on your enterprise network.
Products and Versions
Product Name Version Operating system
USG6000 V100R001C30SPCa0 ● Windows
0 or later ● Mac OS
V500R001C60SPC10 ● Linux (V500R005C10SPC300 and
0 or later later versions)
● iOS (V500R001C60SPC500 and
later versions)
● Android (V500R005C00SPC100 and
later versions)
USG6000E V600R006C00 or ● Windows
later ● Mac OS
● Linux (V600R006C00SPC300 and
later versions)
● iOS
● Android
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 1
HUAWEI SecoClient
User Access Guide 1 Document Information
Product Name Version Operating system
USG9500 V500R001C60SPC10 ● Windows
0 or later ● Mac OS
● Linux (V500R005C10SPC300 and
later versions)
● iOS (V500R001C60SPC500 and
later versions)
● Android (V500R005C00SPC100 and
later versions)
Eudemon200E-N V100R001C30SPCa0 ● Windows
0 or later ● Mac OS
V500R002C20SPC10 ● Linux (V500R005C10SPC300 and
0 or later later versions)
● iOS (V500R002C20SPC500 and
later versions)
● Android (V500R005C00SPC100 and
later versions)
Eudemon200E-G V600R006C00 or ● Windows
later ● Mac OS
● Linux (V600R006C00SPC300 and
later versions)
● iOS
● Android
Eudemon1000E- V100R001C30SPCa0 ● Windows
N 0 or later ● Mac OS
V500R002C20SPC10 ● Linux (V500R005C10SPC300 and
0 or later later versions)
● iOS (V500R002C20SPC500 and
later versions)
● Android (V500R005C00SPC100 and
later versions)
Eudemon1000E- V600R006C00 or ● Windows
G later ● Mac OS
● Linux (V600R006C00SPC300 and
later versions)
● iOS
● Android
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 2
HUAWEI SecoClient
User Access Guide 1 Document Information
Product Name Version Operating system
Eudemon8000E- V500R002C20SPC10 ● Windows
X 0 or later ● Mac OS
● Linux (V500R005C10SPC300 and
later versions)
● iOS (V500R002C20SPC500 and
later versions)
● Android (V500R005C00SPC100 and
later versions)
SVN5600 V200R003C10SPCa0 ● Windows
0 or later ● Mac OS
SVN5800 V200R003C10SPCa0 ● Windows
0 or later ● Mac OS
SVN5800-C V200R003C10SPCa0 ● Windows
0 or later ● Mac OS
SeMG9811 V500R002C20SPC10 ● Windows
0 or later ● Mac OS
● Linux (V500R005C10SPC300 and
later versions)
● iOS (V500R002C20SPC500 and
later versions)
● Android (V500R005C00SPC100 and
later versions)
NGFW Module V100R001C30SPCa0 ● Windows
0 or later ● Mac OS
V500R002C20SPC10 ● Linux (V500R005C10SPC300 and
0 or later later versions)
● iOS (V500R002C20SPC500 and
later versions)
● Android (V500R005C00SPC100 and
later versions)
USG6000V V500R003C00SPC10 ● Windows
0 or later ● Mac OS
● Linux (V500R005C10SPC300 and
later versions)
● iOS (V500R005C00SPC100 and
later versions)
● Android (V500R005C00SPC100 and
later versions)
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 3
HUAWEI SecoClient
User Access Guide 1 Document Information
Product Name Version Operating system
Eudemon1000E- V500R003C00SPC10 ● Windows
V 0 or later ● Mac OS
● Linux (V500R005C10SPC300 and
later versions)
● iOS (V500R005C00SPC100 and
later versions)
● Android (V500R005C00SPC100 and
later versions)
● The version mapping between the SecoClient in different operating systems and the
gateways listed in the preceding table has been fully tested and verified, and their
interworking is supported.
● The SecoClient is independent VPN access software and does not have a strong binding
relationship with the gateway. Therefore, the gateway versions other than those listed in
the preceding table may also be able to interwork with the SecoClient. The supporting
conditions are subject to the actual test results.
Change History
Issue 05 (2019-09-23)
Fifth official release, which matches SecoClient 7.0.2.
The SecoClient in Windows supports the Chinese cryptographic algorithm in SSL
VPN scenarios.
The SecoClient of the Windows version supports route overwrite in the SSL VPN
scenario.
The SecoClient of the Linux version supports endpoint security.
Issue 04 (2018-12-28)
Fourth official release, which matches SecoClient 6.0.3.
The SecoClient supports the Linux operating system.
Issue 03 (2018-12-10)
Third official release, which matches SecoClient 6.0.2.
Issue 02 (2018-06-30)
Second official release, which matches SecoClient 5.0.2.
Issue 01 (2018-06-26)
First official release, which matches SecoClient 5.0.1.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 4
HUAWEI SecoClient
User Access Guide 2 Getting Started
2 Getting Started
The SecoClient is VPN remote access client software provided by Huawei. It
provides secure and convenient access services for mobile device users to remotely
access resources on an enterprise network.
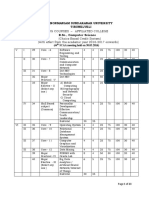
For users who use the software for the first time, refer to the task map in Figure1
to complete the configuration operations required for establishing a VPN
connection step by step.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 5
HUAWEI SecoClient
User Access Guide 2 Getting Started
Figure 2-1 Task map for mobile device users
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 6
HUAWEI SecoClient
User Access Guide 3 Installing the Software
3 Installing the Software
Before using the SecoClient to establish a VPN connection, ensure that the client
software is completely and correctly installed on your mobile device. If the
SecoClient has not been installed on your mobile device, do as follows to install it:
1. Before installing the software, read Installation Precautions to understand
the precautions and system configuration requirements for software
installation.
2. If your mobile device does not have the SecoClent software installation
package for the corresponding OS or the version of the installation package
does not meet the requirement, obtain the software installation package by
referring to Obtaining the Software Installation Package.
3. Currently, the SecoClent supports three types of OSs (Windows, Mac OS and
Linux), and different SecoClient software installation packages are provided
for them. If you have obtained the software installation package that matches
the OS of your mobile device, install the software by referring to the following
steps:
– Installing the Software in the Windows System
– Installing the Software in the Mac OS
– Installing the Software in the Linux System
3.1 Installation Precautions
Before installing and using the SecoClient, read the following content carefully to
understand the precautions for software installation and ensure that the system
configuration of your mobile device meets the requirements.
3.2 Obtaining the Software Installation Package
This section describes how to obtain the SecoClient client software installation
package. In an actual task scenario, the enterprise network administrator is
responsible for planning and deploying the software installation package and
informing mobile device users.
3.3 Installing the Software in the Windows System
The SecoClient provides separate software installation packages for 32-bit and 64-
bit Windows OSs. Select the correct installation package based on the OS
environment of your mobile device.
3.4 Installing the Software in the Mac OS
The SecoClient supports only the 64-bit Mac OS.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 7
HUAWEI SecoClient
User Access Guide 3 Installing the Software
3.5 Installing the Software in the Linux System
The SecoClient software installation packages for 32-bit and 64-bit Linux OSs are
provided. Select the correct installation package based on your OS.
3.1 Installation Precautions
Before installing and using the SecoClient, read the following content carefully to
understand the precautions for software installation and ensure that the system
configuration of your mobile device meets the requirements.
Precautions
● When installing or uninstalling the software, use the user name and password
with the administrator permission to log in to the OS.
● Do not install or use multiple VPN dial-up software programs on one mobile
device. Otherwise, the VPN dial-up software or OS may not work properly.
● If the SecoClient already exists on your mobile device, a message is displayed
during installation to prompt you to uninstall the SecoClient. You can delete
the installed client software of the earlier version as prompted and run the
installation program again to install the client software of the new version on
your hard disk.
System Configuration Requirements
Table 3-1 System Configuration Requirements of the SecoClient
System Configuration Requirement
OS Windows Mac OS Linux
OS version ● Windows Vista ● OS X 10.7.x ● Ubuntu-16.4
(32-bit/64-bit) ● OS X 10.8.x .04 (32-bit)
● Windows 7 (32- ● OS X 10.9.x ● Ubuntu-14.4
bit/64-bit) .04 (64-bit)
● OS X
● Windows 8 (32- 10.10.x
bit/64-bit)
● OS X
● Windows 8.1 10.11.x
(32-bit/64-bit)
● OS X
● Windows 10 10.12.x
(32-bit/64-bit)
● OS X
● Windows Server 10.13.x
2008 (32-bit/64-
bit) ● OS X
10.14.x
● Windows Server
2012 (32-bit/64-
bit)
Hardware resources The SecoClient has no special requirements for
software and hardware resources such as memory,
hard disk, and CPU resources of the OS.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 8
HUAWEI SecoClient
User Access Guide 3 Installing the Software
3.2 Obtaining the Software Installation Package
This section describes how to obtain the SecoClient client software installation
package. In an actual task scenario, the enterprise network administrator is
responsible for planning and deploying the software installation package and
informing mobile device users.
Before You Start
Before obtaining the software installation package, ensure that the OS
environment and version of your mobile device comply with the system
configuration requirements described in Installation Precautions and obtain the
software installation package that matches your OS environment.
Common Methods for Obtaining the Software Installation Package
1. Obtain the software installation package from the administrator of your
enterprise network and upload it to your mobile device.
2. Log in to Huawei technical support website to download the software
installation package by using the account that has the rights to download
the SecoClient software installation package.
– If you are an enterprise network user, you can use a registered account to
log in to http://support.huawei.com/enterprise, choose Enterprise
Networking > Security > Firewall & VPN Gateway > (Select a model),
and download the software installation package of the required version.
– If you are a carrier user, you can use a registered account to log in to
http://support.huawei.com/carrier, choose Software > Network >
Switch & Gateway > Switch & Gateway >(Select a model), and
download the software installation package of the required version.
3. If your enterprise network administrator deploys an SSL VPN virtual gateway
on the egress gateway of your enterprise network, you can use a browser to
log in to the SSL VPN virtual gateway web page to download the
software installation package. The procedure is described as follows:
a. Obtain user login information from your enterprise network
administrator.
Because there are multiple SSL VPN user authentication modes, the obtained
user login information and operations vary. Confirm the user authentication
mode with your enterprise network administrator.
● Local authentication and server authentication: Obtain the user name and
password.
● Certificate-anonymous authentication: Obtain and install the client
certificate.
● Certificate-challenge authentication: Obtain the client certificate and
password and install the client certificate.
b. Enter the virtual gateway address provided by your enterprise network
administrator in the browser of your mobile device to access the login
page of the SSL VPN virtual gateway.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 9
HUAWEI SecoClient
User Access Guide 3 Installing the Software
c. Enter the user name and password or select the installed certificate based
on the SSL VPN user authentication mode and press Enter.
d. If the login succeeds, the virtual gateway web page is displayed. Click
Options in the upper right corner of the web page. You can find the
SecoClient software installation package under Download Network
Extension Client.
e. Click Download network extension client to download the software
installation package corresponding to your OS.
Follow-Up Procedure
Currently, the SecoClent supports only two types of OSs (Windows and Mac OS),
and different SecoClient software installation packages are provided for them. If
you have obtained the software installation package that matches the OS of your
mobile device, install the software by referring to the following steps:
● Installing the Software in the Windows System
● Installing the Software in the Mac OS
● Installing the Software in the Linux System
Alternatively, you can go back to Getting Started and perform subsequent
configurations by referring to the task map.
3.3 Installing the Software in the Windows System
The SecoClient provides separate software installation packages for 32-bit and 64-
bit Windows OSs. Select the correct installation package based on the OS
environment of your mobile device.
Before You Start
Before installing the software, ensure that the OS environment and version of your
mobile device comply with the system configuration requirements described in
Installation Precautions.
Procedure
Step 1 Log in to the OS using an account that has the administrator permission.
Step 2 Double-click the downloaded installation package. The installation wizard is
displayed.
Step 3 The installation wizard prompts you to complete the installation task step by step.
● By default, the SecoClient is installed in the system disk. For example, if the system is
installed in drive C, the default installation path of the SecoClient is C:\Program Files
\SecoClient.
● When you install the SecoClient client for the first time, a message is displayed,
prompting you to install the network adapter driver. Follow the installation wizard to
complete the installation.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 10
HUAWEI SecoClient
User Access Guide 3 Installing the Software
Step 4 After the installation is complete, an application icon named SecoClient.exe is
generated on your desktop. You can double-click the icon to start the SecoClient.
----End
Follow-Up Procedure
● After installing the SecoClient, you can start Configuring a VPN Connection.
● If an error occurs during the installation, rectify the fault by referring to
Installation and Upgrade Faults.
● Alternatively, you can go back to Getting Started and perform subsequent
configurations by referring to the task map.
3.4 Installing the Software in the Mac OS
The SecoClient supports only the 64-bit Mac OS.
Before You Start
Before installing the software, ensure that the OS environment and version of your
mobile device comply with the system configuration requirements described in
Installation Precautions.
Procedure
Step 1 Log in to the Mac OS.
Step 2 Double-click the downloaded installation package. The system automatically
decompresses the package into a folder, which is in the same directory as the
installation package.
Step 3 Double-click the folder. The folder contains two files: Info.plist and
SecoClientInstaller.pkg. Double-click SecoClientInstaller.pkg to run the
installation program.
Step 4 The installation wizard prompts you to complete the installation task step by step.
● The SecoClient is installed in a fixed path by default, which cannot be manually
changed.
● Your system permission may be authenticated during installation, and the installation
continues only after the authentication succeeds. Enter the user name and password
that have the root permission to perform the installation.
Step 5 After the installation is complete, you can find the application program named
SecoClient.app in the application folder. You can double-click to start the
SecoClient.
When you start the SecoClient for the first time, use the root permission of the system to
escalate the permission. After the permission is escalated, you can run the program. Enter
the user name and password that have the root permission to escalate the permission.
----End
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 11
HUAWEI SecoClient
User Access Guide 3 Installing the Software
Follow-Up Procedure
● After installing the SecoClient, you can start Configuring a VPN Connection.
● If an error occurs during the installation, rectify the fault by referring to
Installation and Upgrade Faults.
● Alternatively, you can go back to Getting Started and perform subsequent
configurations by referring to the task map.
3.5 Installing the Software in the Linux System
The SecoClient software installation packages for 32-bit and 64-bit Linux OSs are
provided. Select the correct installation package based on your OS.
Before You Start
Before installing the software, ensure that the OS environment and version of your
mobile device comply with the system configuration requirements described in
Installation Precautions.
Procedure
The procedure for installing the SecoClient in the 32-bit operating system is the
same as that in the 64-bit operating system. The following uses the 64-bit
operating system as an example.
Step 1 Log in to the Linux system using an account that has the root permission.
Step 2 Save the downloaded installation package to the main folder (Computer > home
> sec).
Step 3 Start the Terminal. In the home/sec directory, run the ./installation package
name.run command as the root user to install the SecoClient.
root@sec-virtual-machine:~# cd ..
root@sec-virtual-machine:/# cd home/sec
root@sec-virtual-machine:/home/sec# ./secoclient-linux-64.xx.x.xx.run
install.sh
uninstall.sh
sysconfig.ini
qt.conf
bak/
component/
config/
driver/
Step 4 If the installation succeeds, the following information is displayed.
Starting SecoclientPromoteService daemon: SecoClientPromoteService.
*****The program has been install in directory SecoClient of your home Directory!*****
*****Enjoy!*****
Step 5 Click the SecoClient icon on the desktop to start the program.
----End
Follow-Up Procedure
● After installing the SecoClient, you can start Configuring a VPN Connection.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 12
HUAWEI SecoClient
User Access Guide 3 Installing the Software
● If an error occurs during the installation, rectify the fault by referring to
Installation and Upgrade Faults.
● Alternatively, you can go back to Getting Started and perform subsequent
configurations by referring to the task map.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 13
HUAWEI SecoClient
User Access Guide 4 Configuring a VPN Connection
4 Configuring a VPN Connection
The SecoClient supports two VPN connection configuration modes: manual mode
and configuration file mode.
The configuration mode depends on whether your enterprise network
administrator provides the VPN connection configuration file.
● If the administrator has provided the configuration file, you can directly
import the configuration file to configure the VPN connection. For details, see
Configuring a VPN Connection by Importing a Configuration File.
● If you do not have the configuration file, you can manually configure a VPN
connection on the SecoClient.
When you manually configure a VPN connection, the connection parameters
to be configured vary according to the type of the VPN to be connected.
Therefore, you need to confirm the type of the VPN to be connected with
your enterprise network administrator and obtain necessary connection
parameters.
After specifying the type of the VPN to be connected and obtaining necessary
connection parameters, configure the VPN connection by referring to the
following sections:
– Configuring an SSL VPN Connection
– Configuring an L2TP VPN Connection
– Configuring an L2TP over IPSec VPN Connection
4.1 Configuring an SSL VPN Connection
If you have confirmed with your enterprise network administrator that the type of
the VPN to be connected is SSL VPN, perform the steps in this section to configure
the VPN connection.
4.2 Configuring an L2TP VPN Connection
If you have confirmed with your enterprise network administrator that the type of
the VPN to be connected is L2TP VPN, perform the following steps to configure
the VPN connection.
4.3 Configuring an L2TP over IPSec VPN Connection
If you have confirmed with your enterprise network administrator that the type of
the VPN to be connected is L2TP over IPSec VPN, perform the following steps to
configure the VPN connection.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 14
HUAWEI SecoClient
User Access Guide 4 Configuring a VPN Connection
4.4 Configuring a VPN Connection by Importing a Configuration File
The configuration file is an .ini file generated by your enterprise network
administrator using the configuration file export function of the SecoClient. The
file contains all parameters required for creating a specific VPN connection. After
obtaining the configuration file, you can import the configuration file to the
SecoClient client to generate the configured VPN connection. This simplifies your
configuration.
4.1 Configuring an SSL VPN Connection
If you have confirmed with your enterprise network administrator that the type of
the VPN to be connected is SSL VPN, perform the steps in this section to configure
the VPN connection.
Before You Start
Before the configuration, check the following table to ensure that you have
obtained the connection parameters required for setting up an SSL VPN
connection.
You can also use the configuration and connection templates in Appendix to check
whether the obtained connection parameters are complete.
Table 4-1 SSL VPN connection parameters
Check Item Remarks
Are Proxy No If you do not use any proxy server when
Settings accessing the Internet, Proxy Settings are
needed? unnecessary.
Yes (System There are three proxy server scenarios. After
proxy is used.) selecting a proxy type, enter the address, port
number, account, and password. You can
Yes (HTTP/HTTPS obtain this information from your enterprise
proxy is used.) network administrator.
Yes (Socks5 proxy
is used.)
Connection Name Identifies an SSL VPN connection. You can set
it as required.
Description Indicates information about the connection,
such as the creator, creation time, and
connection purpose. You can set the
information as required.
Gateway Address Specifies the IP address of an SSL VPN virtual
gateway. Obtain this value from your
enterprise network administrator.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 15
HUAWEI SecoClient
User Access Guide 4 Configuring a VPN Connection
Check Item Remarks
Port Specifies the port number used to establish an
SSL VPN tunnel. Obtain this value from your
enterprise network administrator.
Tunnel Reliable ● Confirm the mode with your enterprise
Mode transmission network administrator.
mode ● The reliable transmission mode is
recommended when the network
Quick
environment is unstable. If the network
transmission
environment is stable, you are advised to
mode
use the quick transmission mode to improve
Auto-sensing data transmission efficiency. If you do not
mode know the network environment condition,
select the auto-sensing mode.
Route Overwrite When the route delivered by the peer gateway
NOTE is the same as the address prefix and subnet
This item is displayed only in the mask of the existing local route, if the route
Windows operating system. overwrite function is enabled, the route
delivered by the peer gateway overwrites the
existing route. This prevents network access
exceptions caused by local route conflicts.
By default, route overwrite function is enabled.
Chinese Cryptographic The client supports to use the chinese
Algorithm cryptographic algorithm to establish an SSL
NOTE VPN connection with the peer gateway.
This item is displayed only in the By default, the chinese cryptographic algorithm
Windows operating system.
function is disabled.
Certificate Authentication If you use certificate authentication to
NOTE establish an SSL VPN connection, select
This item is displayed only in the Certificate Authentication.
Linux operating system.
After Certificate Authentication is selected,
you can select a certificate for certificate
authentication.
Password This parameter specifies the login password
NOTE corresponding to the user name extracted from
This item is displayed only in the the certificate during certificate authentication.
Linux operating system.
This password can be set only when an SSL
VPN connection is set up using certificate
authentication and Certificate Authentication
is selected.
Procedure
Step 1 Select New Connection from the Connect drop-down list on the main interface
of the SecoClient.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 16
HUAWEI SecoClient
User Access Guide 4 Configuring a VPN Connection
Step 2 In the New Connection dialog box, select SSL VPN from the left navigation tree
and set connection parameter values.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 17
HUAWEI SecoClient
User Access Guide 4 Configuring a VPN Connection
Step 3 After the configurations are complete, click OK to return to the main interface of
the SecoClient. You can see that a VPN connection has been created successfully.
----End
Follow-Up Procedure
● After the preceding configurations are complete, you can try Establishing a
VPN Connection.
● Alternatively, you can go back to Getting Started and perform subsequent
configurations by referring to the task map.
4.2 Configuring an L2TP VPN Connection
If you have confirmed with your enterprise network administrator that the type of
the VPN to be connected is L2TP VPN, perform the following steps to configure
the VPN connection.
Before You Start
Before the configuration, check the following table to ensure that you have
obtained the connection parameters required for setting up the L2TP VPN
connection.
You can also use the configuration and connection templates in Appendix to check
whether the obtained connection parameters are complete.
Table 4-2 L2TP VPN connection parameters
Check Item Remarks
Proxy Settings
Are Proxy Settings No If you do not use any proxy server when
needed? accessing the Internet, Proxy Settings are
unnecessary.
Yes (Socks5 After setting the proxy type to Socks5
proxy is used.) proxy, enter the address, port number,
NOTE account, and password. You can obtain
L2TP VPN this information from your enterprise
tunnels network administrator.
support only
the Socks5
proxy.
L2TP Configuration
Connection Name Identifies an L2TP VPN connection. You
can set it as required.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 18
HUAWEI SecoClient
User Access Guide 4 Configuring a VPN Connection
Check Item Remarks
Description Indicates information about the
connection, such as the creator, creation
time, and connection purpose. You can
set the information as required.
LNS Server Address Specifies the IP address of an L2TP VPN
gateway. Obtain this value from your
enterprise network administrator.
Tunnel Configuration
Tunnel Name Identifies a device in the tunnel. Obtain
this value from your enterprise network
administrator.
Authentication CHAP Confirm the mode with your enterprise
Mode network administrator.
PAP
Enable Tunnel Deselected ● Confirm this option with your
Authentication enterprise network administrator.
Selected
● If Enable Tunnel Authentication is
selected, you need to enter the tunnel
authentication password. Obtain the
password from your enterprise
network administrator.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 19
HUAWEI SecoClient
User Access Guide 4 Configuring a VPN Connection
Check Item Remarks
Route Settings ● Confirm the settings with your
enterprise network administrator.
● There are three configuration options:
– Deselect Allow Internet access
after connection.
You can access intranet resources
but cannot access the Internet.
– Select Allow Internet access after
connection, but no IP address is
added to the IP address list.
You can access the intranet
resources that are on the same
network segment as the intranet
address allocated by the peer
gateway, the Internet, and LAN.
– Select Allow Internet access after
connection and add IP addresses
to the IP address list.
You can access the enterprise
intranet resources set in the IP
address list, intranet resources in
the same network segment as the
intranet IP address allocated by the
peer gateway, the Internet, and
LAN.
Obtain the IP addresses to be
added to the IP address list from
your enterprise network
administrator.
Procedure
Step 1 Select New Connection from the Connect drop-down list on the main interface
of the SecoClient.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 20
HUAWEI SecoClient
User Access Guide 4 Configuring a VPN Connection
Step 2 In the New Connection dialog box, select L2TP/IPSec from the left navigation
tree and set connection parameter values.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 21
HUAWEI SecoClient
User Access Guide 4 Configuring a VPN Connection
Step 3 After the settings are complete, click OK to return to the main interface of the
SecoClient. You can see that a VPN connection has been created successfully.
----End
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 22
HUAWEI SecoClient
User Access Guide 4 Configuring a VPN Connection
Follow-Up Procedure
● After the preceding configurations are complete, you can try Establishing a
VPN Connection.
● Alternatively, you can go back to Getting Started and perform subsequent
configurations by referring to the task map.
4.3 Configuring an L2TP over IPSec VPN Connection
If you have confirmed with your enterprise network administrator that the type of
the VPN to be connected is L2TP over IPSec VPN, perform the following steps to
configure the VPN connection.
Before You Start
Before the configuration, check the following table to ensure that you have
obtained the connection parameters required for setting up the L2TP over IPSec
VPN connection.
You can also use the configuration and connection templates in Appendix to check
whether the obtained connection parameters are complete.
Table 4-3 L2TP over IPSec VPN connection parameters
Check Item Remarks
Proxy Settings
Are Proxy Settings No If you do not use any proxy server
needed? when accessing the Internet, Proxy
Settings are unnecessary.
Yes (Socks5 proxy After setting the proxy type to Socks5
is used.) proxy, enter the address, port number,
NOTE account, and password. You can
L2TP over IPSec obtain this information from your
VPN tunnels enterprise network administrator.
support only the
Socks5 proxy.
L2TP Configuration
Connection Name Identifies an L2TP over IPSec VPN
connection. You can set it as required.
Description Indicates information about the
connection, such as the creator,
creation time, and connection
purpose. You can set the information
as required.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 23
HUAWEI SecoClient
User Access Guide 4 Configuring a VPN Connection
Check Item Remarks
LNS Server Address Specifies the IP address of an L2TP
VPN gateway. Obtain this value from
your enterprise network
administrator.
Tunnel Configuration
Tunnel Name Identifies a device in the tunnel.
Obtain this value from your enterprise
network administrator.
Authentication CHAP Confirm the mode with your
Mode enterprise network administrator.
PAP
Enable Tunnel Deselected ● Confirm the settings with your
Authentication enterprise network administrator.
Selected
● If Enable Tunnel Authentication
is selected, you need to enter the
tunnel authentication password.
Obtain the password from your
enterprise network administrator.
Enable IPSec Protocol This option is mandatory for L2TP
over IPSec VPN connections.
IPSec Identity Pre-shared Key If you select this mode, the pre-
Authentication shared key is required. Obtain this
Mode value from your enterprise network
administrator.
USB Key Digital If you select this mode, the USB PIN
Signature code is required. Obtain this value
Authentication from your enterprise network
NOTE administrator.
This option is
supported only in
the Windows OS.
IPSec Configuration
IPSec Server Address ● Specifies the IP address of an IPSec
VPN gateway. Obtain this value
from your enterprise network
administrator.
● If the L2TP VPN gateway and IPSec
VPN gateway are the same, select
Use LNS server address.
Encapsulation Tunnel Mode Confirm the mode with your
Mode enterprise network administrator.
Transmission
Mode
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 24
HUAWEI SecoClient
User Access Guide 4 Configuring a VPN Connection
Check Item Remarks
ESP Authentication Algorithm The value can be MD5, SHA1, or
SHA2-256. Confirm the algorithm
with your enterprise network
administrator.
ESP Encryption Algorithm The value can be DES, 3DES, or AES.
Confirm the algorithm with your
enterprise network administrator.
IKE Basic Configuration
Negotiation Mode Main Mode Confirm the mode with your
enterprise network administrator.
Aggressive Mode
ID Type ● Indicates the identity
authentication type for IKE
negotiation. The ID can be an IP
address or name.
● Confirm the type with your
enterprise network administrator.
Local Name ● This parameter is mandatory when
ID Type is set to Name.
Security Gateway Name
● Confirm the names with your
enterprise network administrator.
Authentication Algorithm The value can be MD5, SHA1, or
SHA2-256. Confirm the algorithm
with your enterprise network
administrator.
Encryption Algorithm The value can be DES-CBC, 3DES-
CBC, or AES-128/192/256. Confirm
the algorithm with your enterprise
network administrator.
DH Group ID The value can be Group1, Group2, or
Group5. Confirm the algorithm with
your enterprise network
administrator.
IKE Advanced Configuration
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 25
HUAWEI SecoClient
User Access Guide 4 Configuring a VPN Connection
Check Item Remarks
Enable PFS ● Indicates that the Perfect Forward
Secrecy (PFS) function is used
during IKE negotiation.
● After this function is enabled, you
need to set security parameters,
including Group1, Group2, and
Group5.
● Confirm the configuration with
your enterprise network
administrator.
SA Lifetime ● Specifies an interval at which the
IKE SA is updated, which reduces
the risk of IKE SA cracking and
improves security.
● Confirm the value with your
enterprise network administrator.
IPSec Advanced Configuration
SA Lifetime ● Specifies an interval at which the
IPSec SA is updated, which reduces
the risk of IPSec SA cracking and
improves security.
● Confirm the value with your
enterprise network administrator.
Route Settings Mode Config After the Mode Config parameter is
set, the actual effect depends on
whether the peer gateway supports
Mode Config (also called the tunnel
separation mode).
● If the peer gateway supports and is
configured with the Mode Config
mode:
● You can access intranet resources,
the Internet, and LAN.
● If the peer gateway does not
support the Mode Config mode or
the Mode Config mode is not
configured:
● You can access intranet resources
but cannot access the Internet or
LAN.
Confirm the configuration with your
enterprise network administrator.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 26
HUAWEI SecoClient
User Access Guide 4 Configuring a VPN Connection
Check Item Remarks
Allow Internet You can use either of the following
access after methods to set the parameters for
connection accessing the Internet after the
connection is set up:
● Select Allow Internet access after
connection, but no IP address is
added to the IP address list:
You can access the intranet
resources that are on the same
network segment as the intranet
address allocated by the peer
gateway, the Internet, and LAN.
● Select Allow Internet access after
connection and add IP addresses
to the IP address list:
You can access the enterprise
intranet resources set in the IP
address list, intranet resources in
the same network segment as the
intranet IP address allocated by the
peer gateway, the Internet, and
LAN.
Obtain the IP addresses to be
added to the IP address list from
your enterprise network
administrator.
Confirm the configuration with your
enterprise network administrator.
Procedure
Step 1 Select New Connection from the Connect drop-down list on the main interface
of the SecoClient.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 27
HUAWEI SecoClient
User Access Guide 4 Configuring a VPN Connection
Step 2 In the New Connection dialog box, select L2TP/IPSec from the left navigation
tree and set connection parameter values.
1. Set L2TP parameters.
2. Set IPSec parameters.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 28
HUAWEI SecoClient
User Access Guide 4 Configuring a VPN Connection
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 29
HUAWEI SecoClient
User Access Guide 4 Configuring a VPN Connection
Step 3 After the settings are complete, click OK to return to the main interface of the
SecoClient. You can see that a VPN connection has been created successfully.
----End
Follow-Up Procedure
● After the preceding configurations are complete, you can try Establishing a
VPN Connection.
● Alternatively, you can go back to Getting Started and perform subsequent
configurations by referring to the task map.
4.4 Configuring a VPN Connection by Importing a
Configuration File
The configuration file is an .ini file generated by your enterprise network
administrator using the configuration file export function of the SecoClient. The
file contains all parameters required for creating a specific VPN connection. After
obtaining the configuration file, you can import the configuration file to the
SecoClient client to generate the configured VPN connection. This simplifies your
configuration.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 30
HUAWEI SecoClient
User Access Guide 4 Configuring a VPN Connection
Before You Start
Confirm with your enterprise network administrator about the integrity and
accuracy of the configuration file. If some content in the configuration file is
missing or incorrect, the VPN connection cannot be set up.
Procedure
Step 1 Select New Connection from the Connect drop-down list on the main interface
of the SecoClient.
Step 2 In the New Connection dialog box, select Import from the left navigation tree.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 31
HUAWEI SecoClient
User Access Guide 4 Configuring a VPN Connection
Step 3 Click Import in the right pane, select the prepared configuration file, and click
Open.
Step 4 Click OK to return to the main interface of the SecoClient. You can see that a VPN
connection has been created successfully.
----End
Follow-Up Procedure
● After the preceding configurations are complete, you can try Establishing a
VPN Connection.
● Alternatively, you can go back to Getting Started and perform subsequent
configurations by referring to the task map.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 32
HUAWEI SecoClient
User Access Guide 5 Establishing a VPN Connection
5 Establishing a VPN Connection
After a VPN connection is configured, the connection name is displayed in the
Connection drop-down list on the main page of the SecoClient.
1. You can select the connection name and try Initiating a VPN Connection.
2. After a VPN tunnel is established, the peer gateway needs to authenticate
your identity. For details, see User Identity Authentication. After
authentication succeeds, your mobile device will obtain an intranet address.
Then, you can securely access intranet resources through the device.
Currently, the SecoClient supports the following user identity authentication
modes. The authentication mode that you can use depends on the
configuration on the peer gateway.
– User Name/Password Authentication
– Authentication by Importing the PKI Digital Certificate
– USB Key Authentication
– Two-Factor Authentication
Before establishing a VPN connection, confirm the identity authentication
mode with your enterprise network administrator and obtain necessary
authentication information such as the user name, password, and certificate
from the administrator.
5.1 Initiating a VPN Connection
After the VPN connection is configured, you can initiate a VPN connection and
establish a VPN tunnel.
5.2 User Identity Authentication
After you initiate a VPN connection request through the SecoClient, the peer
gateway returns a user identity authentication request. After authentication
succeeds, your mobile device will obtain an intranet address. Then, you can
securely access intranet resources through the device.
5.1 Initiating a VPN Connection
After the VPN connection is configured, you can initiate a VPN connection and
establish a VPN tunnel.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 33
HUAWEI SecoClient
User Access Guide 5 Establishing a VPN Connection
Before You Start
● Before initiating a VPN connection, ensure that the parameter settings in the
VPN connection configuration are complete and correct.
● If you configure a VPN connection by importing a configuration file, access
the configuration modification page and check that every mandatory item has
been set.
Procedure
Step 1 Select the configured VPN connection from the Connect drop-down list on the
main interface of the SecoClient.
Step 2 Click Connect to initiate a VPN connection request.
----End
Follow-Up Procedure
● After a VPN tunnel is established, the peer gateway needs to authenticate
your identity. For details, see User Identity Authentication. After
authentication succeeds, your mobile device will obtain an intranet address.
Then, you can securely access intranet resources through the device.
● If an error occurs during the connection, rectify the fault by referring to
Connection Faults.
● lternatively, you can go back to Getting Started and perform subsequent
configurations by referring to the task map.
5.2 User Identity Authentication
After you initiate a VPN connection request through the SecoClient, the peer
gateway returns a user identity authentication request. After authentication
succeeds, your mobile device will obtain an intranet address. Then, you can
securely access intranet resources through the device.
Currently, the SecoClient supports four user identity authentication modes. The
authentication modes require different authentication information. You need to
confirm the identity authentication mode with your enterprise network
administrator and obtain necessary authentication information such as the user
name, password, and certificate from the administrator.
If you have specified the identity authentication mode to be used and obtained
the corresponding authentication information, perform the following operations to
authenticate the user identity:
● User Name/Password Authentication
● Authentication by Importing the PKI Digital Certificate
● USB Key Authentication
● Two-Factor Authentication
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 34
HUAWEI SecoClient
User Access Guide 5 Establishing a VPN Connection
5.2.1 User Name/Password Authentication
User name/password authentication is the most commonly used authentication
mode.
Before You Start
Obtain the following information required for user name/password authentication
from your enterprise network administrator:
1. Valid user name
2. Password corresponding to the user name
You can also use the configuration and connection templates in Appendix to check
whether the obtained authentication information is complete.
The following table lists the support for user name/password authentication in
different OSs and VPN types.
Table 5-1 Support for user name/password authentication
VPN Type/OS Windows Mac OS Linux
SSL VPN Y Y Y
L2TP VPN √ Y Y
L2TP over IPSec VPN Y Y Y
Procedure
Step 1 Initiate a VPN connection request. The user name/password authentication page is
displayed.
Step 2 Enter the user name and password and click Login.
Step 3 If the authentication succeeds, the device successfully connects to the intranet.
The message "The Connection is successful" or "negotiation succeeded" is
displayed.
----End
Follow-Up Procedure
● If you need to perform two-factor authentication, see Two-Factor
Authentication.
● If the authentication or VPN connection fails, rectify the fault by referring to
Connection Faults.
● If your device successfully connects to the intranet, you can try to access
resources in the intranet. If the resources cannot be accessed, rectify the fault
by referring to Service Faults.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 35
HUAWEI SecoClient
User Access Guide 5 Establishing a VPN Connection
● Alternatively, you can return to Getting Started to view other content on the
task map.
5.2.2 Authentication by Importing the PKI Digital Certificate
You can install the PKI digital certificate provided by your enterprise network
administrator to your mobile device and log in to the VPN gateway through
certificate authentication. In SSL VPN scenarios, PKI digital certificate-anonymous
authentication and PKI digital certificate-challenge authentication are supported.
Before You Start
Obtain the following information required for PKI digital certificate authentication
from your enterprise network administrator:
1. Valid PKI digital certificate
2. Login password corresponding to the user name extracted from the certificate
(required only in PKI digital certificate-challenge authentication mode)
3. Login user name and password (required only in the L2TP over IPSec VPN
scenario)
You can also use the configuration and connection templates in Appendix to check
whether the obtained authentication information is complete.
The following table lists the support for PKI digital certificate authentication in
different OSs and VPN types.
Table 5-2 Support for PKI digital certificate authentication
VPN Type/OS Windows Mac OS Linux
SSL VPN (certificate- Y Y Y
anonymous
authentication)
SSL VPN (certificate- Y Y Y
challenge
authentication)
L2TP VPN N N N
L2TP over IPSec VPN Y Y N
Procedure
Step 1 Import the PKI digital certificate to your mobile device.
● In the Windows certificate authentication scenario, import the certificate to
the Internet Explorer.
● In the MAC certificate authentication scenario, import the certificate to
Credential.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 36
HUAWEI SecoClient
User Access Guide 5 Establishing a VPN Connection
● In the Linux certificate authentication scenario, save the certificate in the
Certificate folder in the main directory.
Step 2 Double-click the certificate to install it as prompted.
Step 3 Initiate a VPN connection request. The certificate authentication page is displayed.
Step 4 In the Certificate list, select the imported PKI digital certificate. If the SSL VPN
certificate-challenge authentication mode is used, enter the login password
corresponding to the user name extracted from the certificate. For an L2TP over
IPSec VPN connection, you need to enter the user name and password. Then, click
Login.
Step 5 If the authentication succeeds, the device successfully connects to the intranet.
The message "The Connection is successful" or "negotiation succeeded" is
displayed.
----End
Follow-Up Procedure
● If you need to perform two-factor authentication, see Two-Factor
Authentication.
● If the authentication or VPN connection fails, rectify the fault by referring to
Connection Faults.
● After your device successfully connects to the intranet, you can try to access
resources in the intranet. If the resources cannot be accessed, rectify the fault
by referring to Service Faults.
● Alternatively, you can return to Getting Started to view other content on the
task map.
5.2.3 USB Key Authentication
You can insert the USB key device provided by your enterprise network
administrator into the USB port of your mobile device and use the certificate in
the USB key for identity authentication. USB key certificate-anonymous
authentication and USB key certificate-challenge authentication are supported in
SSL VPN scenarios. In the L2TP over IPSec VPN scenario, if IPSec Identity
Authentication Mode is set to USB Key Digital Signature Authentication, USB
key certificate authentication is used.
Before You Start
Obtain the following information required for USB key certificate authentication
from your enterprise network administrator:
1. USB key device, driver, and PIN
2. Login password corresponding to the user name extracted from the certificate
(This password is required only in USB key certificate-challenge authentication
mode.)
3. Login user name and password (required only in the L2TP over IPSec VPN
scenario)
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 37
HUAWEI SecoClient
User Access Guide 5 Establishing a VPN Connection
You can also use the configuration and connection templates in Appendix to check
whether the obtained authentication information is complete.
The following table lists the support for USB key certificate authentication in
different OSs and VPN types.
Table 5-3 Support for USB key certificate authentication
VPN Type/OS Windows Mac OS Linux
SSL VPN (certificate- Y N N
anonymous
authentication)
SSL VPN (certificate- Y N N
challenge
authentication)
L2TP VPN N N N
L2TP over IPSec VPN Y N N
Procedure
Step 1 Insert the USB key into the USB port of your mobile device and install the USB key
driver.
Step 2 Initiate a VPN connection request. The certificate authentication page is displayed.
Step 3 In the Certificate list, select the identified USB key certificate. If the SSL VPN
certificate-challenge authentication mode is used, enter the login password
corresponding to the user name extracted from the certificate. For an L2TP over
IPSec VPN connection, you need to enter the user name and password. Then, click
Login.
Step 4 In the displayed dialog box, enter the PIN of the USB key device and click OK.
Step 5 If the authentication succeeds, the device successfully connects to the intranet.
The message "The Connection is successful" or "negotiation succeeded" is
displayed.
----End
Follow-Up Procedure
● If you need to perform two-factor authentication, see Two-Factor
Authentication.
● If the authentication or VPN connection fails, rectify the fault by referring to
Connection Faults.
● After your device successfully connects to the intranet, if you can access the
resources in the intranet but cannot access the Internet, rectify the fault by
referring to Service Faults.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 38
HUAWEI SecoClient
User Access Guide 5 Establishing a VPN Connection
● Alternatively, you can return to Getting Started to view other content on the
task map.
5.2.4 Two-Factor Authentication
In SSL VPN scenarios, the client supports two-factor authentication. That is, the
client uses a dynamic token or SMS verification code to perform secondary
authentication based on user name/password authentication or certificate
authentication.
Before You Start
Contact your enterprise network administrator to prepare the device for receiving
the dynamic token or SMS verification code. The device is used to obtain the
verification information required for two-factor authentication.
Before performing two-factor authentication, you need to perform initial
authentication. Confirm with your enterprise network administrator about the
authentication mode and complete the authentication by referring to one of the
following sections:
● User Name/Password Authentication
● Authentication by Importing the PKI Digital Certificate
● USB Key Authentication
You can also use the configuration and connection templates in Appendix to check
whether the obtained authentication information is complete.
Procedure
Step 1 After the initial authentication succeeds, a dialog box is displayed, asking you to
enter the dynamic token or SMS verification code for two-factor authentication.
Step 2 Obtain the dynamic token or SMS verification code on the receiving device, enter
it in the text box, and click OK.
Step 3 After two-factor authentication succeeds, your device successfully connects to the
intranet. The message "The Connection is successful" or "negotiation
succeeded" is displayed.
----End
Follow-Up Procedure
● If the authentication or VPN connection fails, rectify the fault by referring to
Connection Faults.
● After your device successfully connects to the intranet, you can try to access
resources in the intranet. If the resources cannot be accessed, rectify the fault
by referring to Service Faults.
● Alternatively, you can return to Getting Started to view other content on the
task map.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 39
HUAWEI SecoClient
User Access Guide 6 Optional Configurations
6 Optional Configurations
This section describes the following optional configurations of the SecoClient:
● Uninstalling the SecoClient
● Version Detection and Upgrade
● Changing the Login Password
● Blocking Connections to Untrusted Servers
● Setting Automatic Startup upon Power-On
● Canceling Automatic Login
● Changing the UI Language
6.1 Uninstalling the SecoClient
Currently, the SecoClent supports two types of OSs: Windows and Mac OS. To
uninstall the SecoClient software in either of the OSs, you need to run the
uninstallation program.
6.2 Version Detection and Upgrade
The SecoClient supports version detection and upgrade.
6.3 Changing the Login Password
The SecoClient allows users to change their login passwords.
6.4 Other Configurations
This section describes other optional configurations of the SecoClient.
6.1 Uninstalling the SecoClient
Currently, the SecoClent supports two types of OSs: Windows and Mac OS. To
uninstall the SecoClient software in either of the OSs, you need to run the
uninstallation program.
Uninstalling the SecoClient in the Windows System
Step 1 Choose Start > All Programs > SecoClient.
Step 2 Click Uninstall. In the displayed dialog box, click Yes.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 40
HUAWEI SecoClient
User Access Guide 6 Optional Configurations
Step 3 During the uninstallation, the system asks you whether to delete the user
configuration and log file. If you select Yes, the user configuration and log file are
deleted.
Step 4 Click OK. The SecoClient is uninstalled.
----End
Uninstalling the SecoClient in the Mac OS
Use the uninstallation program to uninstall the SecoClient by referring to the following
procedure. You are not advised to drag SecoClient.app to the Trash to uninstall the
software. Otherwise, residual files remain in the system, which may cause anomalies upon
next installation.
Step 1 Double-click the uninstallation program SecoClientUninstaller.app in the
SecoClient folder.
Step 2 Click Uninstall. The program starts to authenticate user identity. Only the user
with the root permission can uninstall the SecoClient.
Step 3 After the user authentication succeeds, the software is uninstalled.
----End
Uninstalling the Software in the Linux System
Step 1 Log in to the Linux system using an account that has the root permission.
Step 2 Start the Terminal and access the usr/local/SecoClient directory.
root@sec-virtual-machine:~# cd ..
root@sec-virtual-machine:/# cd usr/local/SecoClient/
root@sec-virtual-machine:/usr/local/SecoClient#
Step 3 Run the ./ uninstall.sh command as the root user to uninstall the SecoClient.
root@sec-virtual-machine:/usr/local/SecoClient# ./uninstall.sh
Stopping SecoClientPromoteService daemon: SecoClientPromoteService.
Removing any system startup links for /etc/init.d/SecoClientPromoteService.sh ...
----End
6.2 Version Detection and Upgrade
The SecoClient supports version detection and upgrade.
Before You Start
● The SecoClient can detect software versions and perform upgrades only after
establishing a VPN connection with the peer gateway.
● The basic upgrade procedure is as follows:
a. The enterprise network administrator uploads the latest SecoClient
software package to the enterprise gateway.
b. When you establish a VPN tunnel with the gateway through the
SecoClient, the SecoClient automatically detects and compares the
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 41
HUAWEI SecoClient
User Access Guide 6 Optional Configurations
current version with the version of the software installation package on
the gateway.
c. If the software installation package on the gateway is determined as a
new version, the system prompts you to perform the upgrade.
Procedure
Step 1 Right-click the tray icon of the SecoClient and choose Option from the shortcut
menu. The Options dialog box is displayed. Select Detect a new version. If this
option is selected, the SecoClient periodically checks whether there is a new
version on the gateway.
Step 2 If a new version is detected, a prompt is displayed, asking you to upgrade the
software. Click Yes to download and install the new version.
----End
6.3 Changing the Login Password
The SecoClient allows users to change their login passwords.
Before You Start
The password can be changed only when a VPN connection is set up between the
SecoClient and the peer gateway.
The password change function is supported only in SSL VPN scenarios.
Procedure
Step 1 Right-click the tray icon of the SecoClient and choose Change Password from the
shortcut menu. The Change Password dialog box is displayed.
Step 2 Enter the new password.
----End
Follow-Up Procedure
After the password is changed, the current VPN connection is interrupted. You
must enter the new password to re-log in.
6.4 Other Configurations
This section describes other optional configurations of the SecoClient.
Blocking Connections to Untrusted Servers
When the SecoClient establishes an SSL VPN tunnel with the peer gateway, it
checks the device certificate sent by the gateway.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 42
HUAWEI SecoClient
User Access Guide 6 Optional Configurations
Right-click the tray icon of the SecoClient and choose Option from the shortcut
menu. The Options dialog box is displayed. Select Block connections to
untrusted servers.
● If this option is selected:
When the SecoClient fails to verify the gateway device certificate, the system
displays the alarm "Safety warning: untrusted VPN server certificate!" If
you have confirmed that the peer gateway is secure, click Continue to
continue establishing the SSL VPN tunnel. If you cannot confirm the security
of the peer gateway, click Cancel to stop the tunnel establishment.
● If this option is deselected:
When the SecoClient fails to verify the gateway device certificate, the system
does not generate any alarm and directly establishes the tunnel.
Setting Automatic Startup upon Power-On
The SecoClient supports automatic startup upon power-on.
Right-click the tray icon of the SecoClient and choose Option from the shortcut
menu. The Options dialog box is displayed. Select Automatic startup upon
power-on. If this option is selected, the SecoClient automatically starts after the
device starts.
Canceling Automatic Login
Right-click the tray icon of the SecoClient and choose Cancel Automatic Login
from the shortcut menu. Then, the SecoClient will not automatically start after the
device starts.
Changing the UI Language
The SecoClient supports 12 types of UI languages.
Right-click the tray icon of the SecoClient and choose Option from the shortcut
menu. The Options dialog box is displayed. You can select a language from the UI
Language drop-down list.
Proxy Shielding
● In the Windows system:
The Windows system uses the proxy information of the Internet Explorer.
Therefore, you need to modify the proxy information of the Internet Explorer.
a. Open the Internet Explorer and click Tools. The Internet Options dialog
box is displayed.
b. Click the Connections tab and click Local Area Network (LAN)
Settings.
c. Set the proxy shielding information on the Proxy server setting page.
d. Click OK to save the settings.
● In the Linux system:
By default, the Linux system uses the proxy information setting module of the
Firefox browser.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 43
HUAWEI SecoClient
User Access Guide 6 Optional Configurations
a. Open the Firefox browser, enter about:preferences in the address box,
and press Enter.
b. Choose Advanced > Network and click Settings under Connection.
c. Set the proxy shielding information.
d. Click OK to save the settings.
After you configure the proxy server on the Local Area Network (LAN) Settings
page and log in to the client, a PAC file is automatically generated. After you
select Use automatic configuration script on the Local Area Network (LAN)
Settings page, the PAC file address is automatically specified and the PAC file is
used for proxy shielding during client login. After you log out of the client, the
browser automatically restores the proxy settings used before login.
The settings in the PAC file instruct the traffic to correctly access the gateway and
intranet resources, preventing intranet resource access failures caused by the proxy
server configured in the browser. The PAC file keeps the original proxy information
unchanged and therefore does not affect the original proxy function.
If you delete the PAC file while you are logged in to the client, you may fail to
access the gateway or intranet resources using Internet Explorer when the proxy is
used.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 44
HUAWEI SecoClient
User Access Guide 7 Troubleshooting
7 Troubleshooting
This section describes common faults that may occur during the installation or use
of the SecoClient and the troubleshooting methods. For details about how to
locate and rectify common faults on the client, log in to HUAWEI Technical
Support website and obtain the maintenance guide of the firewall product.
According to the task scenarios of mobile device users, faults can be classified into
three types:
1. Installation and Upgrade Faults
2. Connection Faults
3. Service Faults
If the fault persists, contact your enterprise network administrator for technical
support. To quickly locate faults, you need to collect information for
troubleshooting before obtaining the help information. For details, see Collecting
InformationRequired for Troubleshooting.
7.1 Collecting InformationRequired for Troubleshooting
If you encounter a fault that cannot be rectified by yourself during the installation
or use of the SecoClient, contact your enterprise network administrator to rectify
the fault. Before this, you need to collect information for fault locating on your
mobile device.
7.2 Installation and Upgrade Faults
7.3 Connection Faults
7.4 Service Faults
7.1 Collecting InformationRequired for Troubleshooting
If you encounter a fault that cannot be rectified by yourself during the installation
or use of the SecoClient, contact your enterprise network administrator to rectify
the fault. Before this, you need to collect information for fault locating on your
mobile device.
1. The SecoClient supports Collecting an Error Report. It can collect
information in one-click mode and generate an error report file in .zip format.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 45
HUAWEI SecoClient
User Access Guide 7 Troubleshooting
2. You need to export the configuration file by referring to Exporting the
Configuration File and submit the configuration file and error report file to
your enterprise network administrator.
7.1.1 Collecting an Error Report
You can use this function to collect fault locating information in one-click mode
and generate an error report file in .zip format.
Before You Start
When generating the error report file, the SecoClient collects the software usage
information and some system information (see the following part). Ensure that
the following information is strictly protected:
● error_detail.txt: records the manually entered description of the operation
procedure that causes an error as well as the SecoClient version information.
● netcard_info.txt: records the network adapter information.
● operate_system_info.txt: records the OS information.
● proxy_info.txt: records the proxy server information.
● route_info.txt: records the route information.
● SecoClient_SecoClientCS_0.log: records the log information generated during
the service configuration of the SecoClient, such as the login success or failure
and whether the VPN tunnel is properly established.
● SecoClient_SecoClientUI_0.log: records the log information generated on the
configuration UI of the SecoClient, such as the VPN connection configuration
and switchover between UI languages.
● SecoClient_SecoClientPromoteService_0.log: Records the service process
information of the SecoClient. The service process is used to ensure the
normal running of the SecoClient.
● Crash file: generated when the SecoClient is shut down unexpectedly. The
name of a crash file varies with the cause of the crash. In the Windows
system, the file name extension of a crash file is .dmp, while in the Mac OS,
the file name extension of a crash file is .core.
Procedure
Step 1 Right-click the tray icon of the SecoClient.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 46
HUAWEI SecoClient
User Access Guide 7 Troubleshooting
Step 2 Click Error Report. In the displayed dialog box, describe the configuration or
operation procedure that caused this error and then click OK.
Step 3 Click Browse to select a directory to which the error report file will be saved.
When the compressed package of a fault report is saved in the Linux system, the selected
path cannot contain ~ < > | ; ? ' , & #.
Step 4 Click OK to download the error report file to the specified directory.
----End
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 47
HUAWEI SecoClient
User Access Guide 7 Troubleshooting
Follow-Up Procedure
After an error report is generated, you need to export the configuration file by
referring to Exporting the Configuration File and send the error report and
configuration file to your enterprise network administrator through email, USB
flash drive, or another method. Then, your enterprise network administrator will
help you rectify the fault.
7.1.2 Exporting the Configuration File
The configuration file is an .ini file generated by your enterprise network
administrator using the configuration file export function of the SecoClient. The
file contains all parameters required for creating a specific VPN connection.
Therefore, the configuration file is the important reference information for
troubleshooting.
Procedure
Step 1 Select the configured VPN connection from the Connect drop-down list on the
main interface of the SecoClient and click on the right.
Step 2 On the Connection Details window, click Export on the navigation tree and select
the directory to which the configuration file will be saved. The default format of
the configuration file is .ini.
Step 3 Click Save to save the configuration file to the specified directory.
----End
Follow-Up Procedure
After the configuration file is exported, you can send the configuration file and
error report generated in Collecting an Error Report to your enterprise network
administrator by email, USB flash drive, or another method. Then, the enterprise
network administrator will help you handle the fault.
7.2 Installation and Upgrade Faults
Software Installation Failure
Read the precautions in Installation Precautions to check whether your login
account has the administrator permission. Only the users who have the
administrator permission can install the SecoClient.
Before installing the software, ensure that the OS environment and version of your
mobile device comply with the system configuration requirements described in
Installation Precautions.
Software Upgrade Failure
The possible cause is that the software installation package on the gateway is
incorrect. Contact your enterprise network administrator for confirmation.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 48
HUAWEI SecoClient
User Access Guide 7 Troubleshooting
7.3 Connection Faults
Fail to Establish a VPN Connection for the First Time
The possible cause is that the firewall of the OS blocks the VPN connection of the
SecoClient. In Start > Control Panel > System and Security > Windows Firewall,
set the access rule of the built-in firewall of the OS to Permit (the Windows 7
system is used as an example).
The Mobile Device Cannot Identify the Certificate in the USB Key
The possible cause is that the USB key is in poor contact with the USB port of the
mobile device or the USB key driver is faulty. Remove the USB key from the USB
port and insert it again. If the system still cannot identify the USB key, you need to
re-install the USB key driver.
The Message "Tunnel keepalive timed out or negotiation timed out" Is
Displayed When a VPN Tunnel Is Established in L2TP Mode
The possible cause is that the encryption and decryption negotiation parameters
on the SecoClient and gateway are inconsistent or the SecoClient and gateway are
unreachable. In this case, contact your enterprise network administrator to
confirm the configuration.
The Message "Failure to Obtain the System Proxy" Is Displayed When
System Proxy Is Selected
If you set Proxy Type to System proxy, the SecoClient uses the proxy
configuration in the browser. The message "Failure to Obtain the System Proxy"
indicates that no proxy is set for the browser.
In this case, set the proxy server by referring to the following procedure:
Step 1 Open the Internet Explorer and choose Tools > Internet options on the upper
right corner. In the displayed dialog box, click the Connections tab.
Step 2 Click LAN settings and set the proxy server. Obtain the proxy server information
from your enterprise network administrator. After the configuration is complete,
click OK.
Step 3 Open the SecoClient, set Proxy Type to System proxy. Then, you can find that the
proxy server information set in the browser is automatically added to the Proxy
Settings of the SecoClient.
----End
7.4 Service Faults
The User Cannot Access the Internet After a VPN Tunnel Is Established
Symptom
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 49
HUAWEI SecoClient
User Access Guide 7 Troubleshooting
After a VPN tunnel is established, the message "The Connection is successful" or
"negotiation succeeded" is displayed. In this case, the user can access resources
on the enterprise network, but cannot access the Internet.
Analysis and handling
The possible cause is that tunnel separation is not configured. As a result, all
traffic enters the VPN tunnel.
SSL VPN, L2TP VPN, and L2TP over IPSec VPN support tunnel separation.
● SSL VPN tunnel separation involves configuration on the gateway. Therefore,
if you cannot access the Internet in an SSL VPN connection, contact your
enterprise network administrator to modify the configuration on the gateway.
● L2TP VPN tunnel separation involves configuration on the SecoClient. Check
whether Allow Internet Access is selected and whether the network segment
for VPN access is set. If the configuration on the SecoClient is correct, contact
your enterprise network administrator.
● L2TP over IPSec VPN tunnel separation can be configured in two modes.
Which mode is used depends on the route configuration for the VPN
connection:
– If Mode Config is selected in the route configuration on the SecoClient,
tunnel separation must be configured on the gateway, and the
corresponding route must be delivered. In this case, contact your
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 50
HUAWEI SecoClient
User Access Guide 7 Troubleshooting
enterprise network administrator to modify the configuration on the
gateway.
– If Allow Internet Access is selected in the route configuration on the
SecoClient, check whether the network segment for VPN access is
configured. If the configuration on the SecoClient is correct, contact your
enterprise network administrator.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 51
HUAWEI SecoClient
User Access Guide 8 Appendix
8 Appendix
This chapter provides the method for using commands to configure the client in
the Linux system as well as configuration and connection templates for SSL VPN,
L2TP VPN, and L2TP over IPSec VPN. The templates contain all connection
parameters and authentication information required for configuring and
establishing the corresponding VPN connections. You can refer to these templates
to check whether the obtained information is sufficient. Enterprise network
administrators can use these templates to provide necessary connection
parameters and authentication information for mobile device users.
8.1 Mobile Client
In addition to the SecoClient PC client, Huawei has launched the mobile client for
the iOS and Android operating systems.
8.2 Using Commands to Configure the Client in the Linux System
8.3 VPN Configuration and Connection Templates
8.1 Mobile Client
In addition to the SecoClient PC client, Huawei has launched the mobile client for
the iOS and Android operating systems.
How to Obtain
● Mobile client for the iOS operating system
Way 1: Open APP Store, search for SecoClient, and download the latest
version of the SecoClient iOS client.
Way 2: Download the correct software installation package in HUAWEI
technical support website.
– For enterprise network users: log in to http://support.huawei.com/
enterprise, choose Enterprise Networking > Security > Firewall & VPN
Gateway > Secospace USG6600 > Downloads, and select the correct
software installation package.
– For carrier users: log in to http://support.huawei.com/carrier, choose
Software > Network > Switch & Gateway > Switch & Gateway >
Eudemon1000E-N Series > Eudemon1000E-N, and select the correct
software installation package.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 52
HUAWEI SecoClient
User Access Guide 8 Appendix
● Mobile client for the Android operating system
Way 1: Download and open Huawei AppGallery, search for SecoClient, and
download the latest version of the SecoClient Android client.
Way 2: Download the correct software installation package in HUAWEI
technical support website.
– For enterprise network users: log in to http://support.huawei.com/
enterprise, choose Enterprise Networking > Security > Firewall & VPN
Gateway > Secospace USG6600 > Downloads, and select the correct
software installation package.
– For carrier users: log in to http://support.huawei.com/carrier, choose
Software > Network > Switch & Gateway > Switch & Gateway >
Eudemon1000E-N Series > Eudemon1000E-N, and select the correct
software installation package.
Specifications
Currently, the SecoClient mobile client supports only SSL VPN connections. The
following table lists the supported models and operating system versions.
Table 8-1 Models and operating system versions supported by a mobile SecoClient
Operating iOS Android
System
Supported iOS 10.0 and later versions Android 5.0 and later
Operating are supported. versions are supported.
System Versions
Supported ● iPhone X -
Device Models ● iPhone 8/8 Plus
● iPhone 7/7 Plus
● iPhone 6s/6s Plus
● iPhone 6/6 Plus
● iPhone 5s
● iPad Pro
● iPad Air 1/2
● iPad 4
● iPad mini 2/3/4
Supported - ● 720*1280
Device Screen ● 1080*1920
Resolution
● 1440*2560
● 2160*4096
The following table lists the function specifications of a mobile SecoClient.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 53
HUAWEI SecoClient
User Access Guide 8 Appendix
Table 8-2 Function specifications of a mobile SecoClient
Function iOS Android
SSL Network extension Supported Supported
VPN
Endpoint security Not supported Not supported
NOTE
When the terminal
security function is
enabled on the
gateway, the mobile
SecoClient can dial
up successfully.
Preferential Not supported Not supported
gateway selection
Reconnection Not supported Not supported
Link backup Supported Supported
NOTE
When the link
backup function is
enabled on the
gateway, the mobile
SecoClient can dial
up successfully.
Certificate Not supported Not supported
authentication
MAC Address Not supported Not supported
Authentication
Certificate filtering Not supported Not supported
Two-factor Not supported Not supported
authentication
L2TP VPN Not supported Not supported
L2TP over IPSec VPN Not supported Not supported
NAT traversal Supported Supported
Proxy traversal Not supported Not supported
Tunnel splitting Supported Supported
Basic Automatic startup Not supported Not supported
functi upon power-on
ons
Language Supported Supported
NOTE
Only Chinese and
English are
supported.
Automatic login Supported Supported
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 54
HUAWEI SecoClient
User Access Guide 8 Appendix
Function iOS Android
Profile Import Not supported Not supported
Export Not supported Not supported
Fault location Supported Supported
Configuration using Not supported Not supported
commands
Non-administrator user Supported Supported
configuration
The following table lists the performance specifications of a mobile SecoClient.
Table 8-3 Performance specifications of a mobile SecoClient
Function Specifications
Number of new VPN connections per 16
second
Operation
For details about how to use the SecoClient mobile client, see the online help of
Settings > Help in the app.
8.2 Using Commands to Configure the Client in the
Linux System
8.2.1 Starting the Client
Step 1 Access the /usr/local/SecoClient/serviceclient directory.
Step 2 Run the ./SecoClientCS command to start the client. This command can be
executed by both common and root users.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 55
HUAWEI SecoClient
User Access Guide 8 Appendix
Before starting the client using the command, ensure that the client started through the UI
desktop has been shut down.
----End
8.2.2 Configuring an SSL VPN Connection
Configuring SSL VPN
Step 1 Enter 1 to create a connection.
Step 2 Enter 1 to set the VPN type to SSL VPN.
Step 3 Enter the corresponding sequence number to complete the configuration of
parameters 1 to 5.
● 1. Connection Name(Required)
● 2. Description
● 3. Gateway Address
● 4. Port(Required)
● 5. Tunnel Mode(Required): The options are Reliable Transmission, Quick
Transmission, and Auto-sensing.
For details about the parameters, see Establishing an SSL VPN Tunnel.
Step 4 Enter 6 to save the configuration.
----End
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 56
HUAWEI SecoClient
User Access Guide 8 Appendix
Establishing an SSL VPN Connection
Step 1 Enter the corresponding number to establish an SSL VPN connection.
Step 2 Enter 1 to set up an SSL VPN connection.
Step 3 A message is displayed, indicating that the connection is set up successfully. Enter
the user name and password to log in.
----End
● In the Linux system, the SSL VPN connection configured and established using
commands supports only user name/password authentication.
● After the connection is successful, do not close the terminal window. Otherwise, the
connection will be disconnected.
SSL VPN Disconnection
Enter q to cut off the connection.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 57
HUAWEI SecoClient
User Access Guide 8 Appendix
8.2.3 Configuring an L2TP VPN Connection
Configuring L2TP VPN
Step 1 Enter 1 to create a connection.
Step 2 Enter 2 and set the VPN type to L2TP/IPSec.
Step 3 Enter the corresponding sequence number to complete the configuration of
parameters 1 to 8.
● 1. Connection Name(Required)
● 2. Description
● 3. LNS Server Address(Required)
● 4. Tunnel Name(Required)
● 5. Authentication Mode
● 6. Tunnel Authentication: Enable the tunnel authentication function. After the
tunnel authentication function is enabled, you need to enter the tunnel
authentication password.
● 7. IPSec Protocol: Enable the IPSec protocol. Do not enable this function.
● 8. Allow Internet access after connection: Set routes. After this option is
enabled, you can set the traffic to be encrypted in the VPN tunnel by adding
an IP address segment.
For details about the parameters, see Establishing an L2TP VPN Tunnel.
Step 4 Enter 9 to save the configuration.
----End
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 58
HUAWEI SecoClient
User Access Guide 8 Appendix
Establishing an L2TP VPN Connection
Step 1 Enter the corresponding number to establish an L2TP VPN connection.
Step 2 Enter 1 to set up an L2TP VPN connection.
Step 3 Enter the user name and password to log in.
----End
After the connection is successful, do not close the terminal window. Otherwise, the
connection will be disconnected.
L2TP VPN Disconnection
Enter q to cut off the connection.
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 59
HUAWEI SecoClient
User Access Guide 8 Appendix
8.2.4 Configuring an L2TP over IPSec VPN Connection
Setting L2TP Parameters
Step 1 Enter 1 to create a connection.
Step 2 Enter 2 and set the VPN type to L2TP/IPSec.
Step 3 Enter the corresponding sequence number to complete the configuration of
parameters 1 to 6.
● 1. Connection Name(Required)
● 2. Description
● 3. LNS Server Address(Required)
● 4. Tunnel Name(Required)
● 5. Authentication Mode
● 6. Tunnel Authentication: Enable the tunnel authentication function. After the
tunnel authentication function is enabled, you need to enter the tunnel
authentication password.
For details about the parameters, see Establishing an L2TP over IPSec VPN Tunnel.
----End
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 60
HUAWEI SecoClient
User Access Guide 8 Appendix
Setting IPSec Parameters
Step 1 Enter 7 to enable the IPSec protocol.
Step 2 Enter the corresponding sequence number to complete the configuration of
parameters 8 to 20.
● 8. IPSec Authentication Mode: In the Linux system, IPSec supports only pre-
shared key authentication. In pre-shared key authentication mode, the pre-
shared key is required.
● 9. IPSec Server address: IP address of the IPSec server. By default, the IP
address of the LNS server is used (Use LNS server address).
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 61
HUAWEI SecoClient
User Access Guide 8 Appendix
● 10. Encapsulation Mode: IPSec encapsulation mode, which can be
Transmission mode or Tunnel mode.
● 11. ESP Authentication Algorithm
● 12. ESP Encryption Algorithm
● 13. Negotiation Mode: IKE negotiation mode, which can be Main Mode or
Aggressive Mode.
● 14. Authentication Algorithm: authentication algorithm used for IKE
negotiation
● 15. Encryption Algorithm: encryption algorithm used for IKE negotiation
● 16. DH Group ID: DH group ID used for IKE negotiation
● 17. PFS: After the PFS function is enabled, the corresponding security
parameter (Security Parameter) must be configured.
● 18. SA Lifetime(IKE Advanced Configuration): IKE SA lifetime
● 19. SA Lifetime(IPSec Advanced Configuration): IPSec SA lifetime
● 20. Route Settings: The mode can be Mode Config or Allow Internet access
after connection. After this parameter is set to Allow Internet access after
connection, you can set the traffic to be encrypted in the VPN tunnel by
adding an IP address segment.
For details about the parameters, see Establishing an L2TP over IPSec VPN Tunnel.
Step 3 Enter 21 to save the configuration.
----End
Establishing an L2TP over IPSec VPN Connection
Step 1 Enter the corresponding number to establish an L2TP over IPSec VPN connection.
Step 2 Enter 1 to set up the L2TP over IPSec VPN connection.
Step 3 Enter the user name and password to log in.
----End
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 62
HUAWEI SecoClient
User Access Guide 8 Appendix
● In the Linux system, the L2TP over IPSec VPN connection configured and established
using commands supports only user name/password authentication.
● After the connection is successful, do not close the terminal window. Otherwise, the
connection will be disconnected.
L2TP over IPSec VPN Disconnection
Enter q to cut off the connection.
8.3 VPN Configuration and Connection Templates
8.3.1 SSL VPN Configuration and Connection Template
Table 8-4 SSL VPN Configuration and Connection Template
SSL VPN Configuration Template
No. Item Parameter
1 Are Proxy No -
Settings
needed? Yes Whic System Address,
h proxy port
proxy number,
mode HTTP/ account,
is HTTPS and
used? proxy password
Socks5
proxy
2 Connection name
3 Description
4 Remote gateway address
5 Port
6 Which Reliable Transmission -
tunnel
mode is Quick Transmission -
used? Auto-sensing -
7 Are you sure you want to enable the route overwrite -
function?
8 Are you sure you want to enable the chinese -
cryptographic algorithm function?
SSL VPN Connection Template
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 63
HUAWEI SecoClient
User Access Guide 8 Appendix
No. User Required Information
Identity
Authentica
tion
1 User name/ User name
password
authenticati Password
on
2 PKI digital Certificat Valid PKI digital certificate
certificate e-
authenticati anonymo
on us
authentic
ation
Certificat Valid PKI digital certificate
e-
challenge Login password corresponding to the user
authentic name extracted from the certificate
ation
3 USB key Certificat USB key device, driver, and PIN
certificate e-
authenticati anonymo
on us
authentic
ation
Certificat USB key device, driver, and PIN
e-
challenge Login password corresponding to the user
authentic name extracted from the certificate
ation
4 Two-factor Initial User name/password authentication (referring
authenticati authentic to the above)
on ation
PKI digital certificate authentication (referring
to the above)
USB key certificate authentication (referring to
the above)
Two- Dynamic token Obtain the value from the
factor code dynamic token code
authentic authentication receiving device.
ation
SMS Obtain the value from the
verification SMS verification code
code receiving device.
authentication
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 64
HUAWEI SecoClient
User Access Guide 8 Appendix
8.3.2 L2TP VPN Configuration and Connection Template
Table 8-5 L2TP VPN Configuration and Connection Template
L2TP VPN Configuration Template
No. Item Parameter
Proxy Settings
1 Are Proxy No -
Settings
needed? Yes (Socks5 Address
proxy is
used.) Port
Account
Password
L2TP Configuration
2 Connection name
3 Description
4 LNS server address
Tunnel Configuration
5 Tunnel name
6 Which CHAP -
authentication
mode is used? PAP -
7 Is tunnel No -
authentication
enabled? Yes Tunnel
authentication
password
Route Settings
8 Deselect Allow Internet access after -
connection.
Select Allow Internet access after connection. -
No IP address is added to the IP address list.
Select Allow Internet IP addresses to be
access after connection. added
Add IP addresses to the IP
address list.
L2TP VPN Connection Template
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 65
HUAWEI SecoClient
User Access Guide 8 Appendix
No. User Identity Required Information
Authenticatio
n
1 User name/ User name
password
authentication Password
8.3.3 L2TP over IPSec VPN Configuration and Connection
Template
Table 8-6 L2TP over IPSec VPN Configuration and Connection Template
L2TP over IPSec VPN Configuration Template
No. Item Parameter
Proxy Settings
1 Are Proxy Settings No -
needed?
Yes (Socks5 Address
proxy is
used.) Port
Account
Password
L2TP Configuration
2 Connection name
3 Description
4 LNS server address
Tunnel Configuration
5 Tunnel name
6 Which CHAP -
authentication
mode is used? PAP -
7 Is tunnel No -
authentication
enabled? Yes Tunnel
authentication
password
Enable IPSec Protocol
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 66
HUAWEI SecoClient
User Access Guide 8 Appendix
8 Which IPSec Pre-shared Pre-shared key
identity key
authentication authenticatio
mode is used? n
USB key USB PIN
digital
signature
authenticatio
n
IPSec Settings
9 IPsec server Are L2TP No -
address VPN and
IPSec VPN Yes Select Use the
gateways are LNS server
the same? address.
10 Which Tunnel Mode -
encapsulation
mode is used? Transmission Mode -
11 Which ESP MD5 -
authentication
algorithm is used? SHA1 -
SHA2-256 -
12 Which ESP DES -
encryption
algorithm is used? 3DES -
AES -
IKE Settings
13 Which negotiation Main Mode -
mode is used?
Aggressive Mode -
14 Which type of ID is IP address -
used?
Name -
15 Local name (this parameter is required if the ID type
is set to Name.)
16 Security gateway name (this parameter is required if
the ID type is set to Name.)
17 Authentication MD5 -
algorithm
SHA1 -
SHA2-256 -
18 Encryption DES-CBC -
algorithm
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 67
HUAWEI SecoClient
User Access Guide 8 Appendix
3DES-CBC -
AES-128
AES-192 -
AES-256 -
19 DH Group ID Group1 -
Group2 -
Group5 -
IKE Advanced Settings
20 Is PFS enabled? No -
Yes Secur Group1 -
ity
Para Group2 -
mete Group5 -
r
21 SA lifecycle
IPsec Advanced Settings
22 SA lifecycle
Route Settings
23 Select Mode Config. -
Select Allow Internet access after connection. -
No IP address is added to the IP address list.
Select Allow Internet access after IP addresses to
connection. be added
Add IP addresses to the IP address
list.
L2TP over IPSec VPN Connection Template
No. User Identity Required Information
Authentication
1 User name/ User name
password
authentication Password
2 PKI digital Valid PKI digital certificate
certificate
authentication User name
Password
3 USB key certificate USB key device, driver, and PIN
authentication
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 68
HUAWEI SecoClient
User Access Guide 8 Appendix
User name
Password
Issue 05 (2019-09-23) Copyright © Huawei Technologies Co., Ltd. 69
You might also like
- HCIA-Cloud Computing V4.0 Learning GuideDocument142 pagesHCIA-Cloud Computing V4.0 Learning GuideNour IjerNo ratings yet
- Wi-Fi EasyMesh Specification v3Document163 pagesWi-Fi EasyMesh Specification v3givangustavo100% (1)
- VoLTE Features - HuaweiDocument255 pagesVoLTE Features - HuaweiDJRashDownloadNo ratings yet
- CISM Acronyms PDFDocument4 pagesCISM Acronyms PDFComas OlivosNo ratings yet
- Huawei SDC Technical White Paper - 290819Document65 pagesHuawei SDC Technical White Paper - 290819James DonaldNo ratings yet
- Technical Proposal For The WAN Interconnection Solution (V100R001C00 - 01)Document59 pagesTechnical Proposal For The WAN Interconnection Solution (V100R001C00 - 01)Duncan NgachaNo ratings yet
- VoLTE (eRAN12.1 08)Document462 pagesVoLTE (eRAN12.1 08)waelq2003No ratings yet
- Modernizing Your Soc StrategyDocument16 pagesModernizing Your Soc Strategyep230842No ratings yet
- Laurent Ouakil, Guy Pujolle - Telephonie Sur IP - H.323, SIP, MGCP, QoS Et Securite, Filtrage, ToIP Sur Wi-Fi, PBX Asterisk, Skype Et Autres Softphones, VoIP, Offre Multi-Play Des FAI, ...Document17 pagesLaurent Ouakil, Guy Pujolle - Telephonie Sur IP - H.323, SIP, MGCP, QoS Et Securite, Filtrage, ToIP Sur Wi-Fi, PBX Asterisk, Skype Et Autres Softphones, VoIP, Offre Multi-Play Des FAI, ...Karima DjmNo ratings yet
- Developer Guide: Huawei HilensDocument53 pagesDeveloper Guide: Huawei HilensRiyanto riyantoNo ratings yet
- User Guide: IDU R2561 V100R001C00SPC012Document64 pagesUser Guide: IDU R2561 V100R001C00SPC012Maro WelchNo ratings yet
- Huawei IP Phone ESpace 6850 User Manual (V100R001C02SPC100 - 01)Document30 pagesHuawei IP Phone ESpace 6850 User Manual (V100R001C02SPC100 - 01)Jignesh BhalsodNo ratings yet
- HUAWEI IdeaHub S2 2.1 Product OverviewDocument42 pagesHUAWEI IdeaHub S2 2.1 Product Overviewottmar mendoza juarezNo ratings yet
- Multicast Feature Guide (MA5800 and Other OLT Products)Document158 pagesMulticast Feature Guide (MA5800 and Other OLT Products)xebigo7728No ratings yet
- FusionSolar App User ManualDocument158 pagesFusionSolar App User ManualDhyan KavindaNo ratings yet
- Wireless Access Controller (AC and Fit AP) V200R019C00 Web-Based Configuration Guide PDFDocument846 pagesWireless Access Controller (AC and Fit AP) V200R019C00 Web-Based Configuration Guide PDFVillatoro ChrisNo ratings yet
- IMaster NCE-Campus V300R020C00 RESTful API Development GuideDocument3,370 pagesIMaster NCE-Campus V300R020C00 RESTful API Development GuidedelplayNo ratings yet
- Huawei FusionSphere 6.5.0 Technical White Paper (Server Virtualization)Document26 pagesHuawei FusionSphere 6.5.0 Technical White Paper (Server Virtualization)Myo Lwin SoeNo ratings yet
- Huawei Hg556a Manual Servicio enDocument59 pagesHuawei Hg556a Manual Servicio enAndrei LucianNo ratings yet
- Cloud Backup and RecoveryDocument66 pagesCloud Backup and RecoveryCRISTIANNo ratings yet
- Huawei HG556 A Service ManualDocument59 pagesHuawei HG556 A Service ManualJeremy YangNo ratings yet
- Huawei B315s - User GuideDocument55 pagesHuawei B315s - User GuideGilang PratomoNo ratings yet
- FusionSolar App User ManualDocument134 pagesFusionSolar App User ManualPanji Joyonegoro RamadhanNo ratings yet
- Help PDFDocument61 pagesHelp PDFDela Cruz RepsacNo ratings yet
- Huawei OceanStor Dorado All-Flash Storage 6.1.0 Technical White PaperDocument186 pagesHuawei OceanStor Dorado All-Flash Storage 6.1.0 Technical White PaperFernandoNo ratings yet
- Se2900 Product Description PDFDocument220 pagesSe2900 Product Description PDFZia100% (3)
- Huawei Videoconferencing Management System SMC2.0 Product OverviewDocument80 pagesHuawei Videoconferencing Management System SMC2.0 Product OverviewBtakeshi1No ratings yet
- HUAWEI WATCH GT 2 Pro OnlineHelp - (VID-B19,01, En)Document49 pagesHUAWEI WATCH GT 2 Pro OnlineHelp - (VID-B19,01, En)Giorgos GiannakakisNo ratings yet
- Huawei EulerOS V2.0 Administrators Guide 05Document164 pagesHuawei EulerOS V2.0 Administrators Guide 05rsrsuporteNo ratings yet
- FusionSolar App User ManualDocument182 pagesFusionSolar App User ManualRadu BarbuNo ratings yet
- IMaster NCE-Fabric V100R021C10 RESTful API Development GuideDocument4,558 pagesIMaster NCE-Fabric V100R021C10 RESTful API Development Guidelita litaNo ratings yet
- BBU Interconnection (SRAN10.1 - 01)Document55 pagesBBU Interconnection (SRAN10.1 - 01)Henri DiemeNo ratings yet
- Feature Description - (V200R008C02 01, NGN)Document432 pagesFeature Description - (V200R008C02 01, NGN)Catherine HiginoNo ratings yet
- Fat AP and Cloud AP V200R019C00 Command Reference PDFDocument4,890 pagesFat AP and Cloud AP V200R019C00 Command Reference PDFsean orderNo ratings yet
- Lte TDD b2328-42 User GuideDocument88 pagesLte TDD b2328-42 User GuidedchardwareNo ratings yet
- Wlan AP User Manual (v100r006c00 - 07) (PDF) - enDocument141 pagesWlan AP User Manual (v100r006c00 - 07) (PDF) - enDuval Fortes55% (11)
- 05 VLAN Principles and ConfigurationDocument33 pages05 VLAN Principles and ConfigurationChema GuerraNo ratings yet
- HG630b Home Gateway: User GuideDocument57 pagesHG630b Home Gateway: User GuidemaheshkzmNo ratings yet
- Quidway Eudemon 200E-B Firewall Feature Description (V100R002 - 01)Document229 pagesQuidway Eudemon 200E-B Firewall Feature Description (V100R002 - 01)Jk GancitaNo ratings yet
- Pki (Sran10.1 02)Document183 pagesPki (Sran10.1 02)riamaNo ratings yet
- G630-U10 Advanced Maintenance ManualDocument71 pagesG630-U10 Advanced Maintenance ManualwebpcnetlinkNo ratings yet
- FusionSolar App, SUN2000 App Device Commissioning GuideDocument329 pagesFusionSolar App, SUN2000 App Device Commissioning GuidegeorgedrobotNo ratings yet
- Commissioning Guide - (V200R008C02 01, NGN)Document148 pagesCommissioning Guide - (V200R008C02 01, NGN)Catherine HiginoNo ratings yet
- Huawei Ipc6224 VRZ Configuration GuideDocument150 pagesHuawei Ipc6224 VRZ Configuration GuideMuhammad RanggaNo ratings yet
- CloudEngine S Series Switches Security Hardening Guide (V600)Document124 pagesCloudEngine S Series Switches Security Hardening Guide (V600)KeithNo ratings yet
- HUAWEI Ascend P2-6070 Maintenance ManualDocument101 pagesHUAWEI Ascend P2-6070 Maintenance ManualDayronToroNo ratings yet
- SEP Technology White PaperDocument115 pagesSEP Technology White PaperNguyễn Đức ToànNo ratings yet
- #00400221-IGateway Bill User Manual (V300R001 - 02)Document309 pages#00400221-IGateway Bill User Manual (V300R001 - 02)Shahab RezakhaniNo ratings yet
- NE40E-F V800R011C10 Configuration Guide - Interface and Data Link 02Document54 pagesNE40E-F V800R011C10 Configuration Guide - Interface and Data Link 02Tinashe Dinero MurapaNo ratings yet
- IPC6325-WD-VF Configuration GuideDocument192 pagesIPC6325-WD-VF Configuration GuideRissel Moretti100% (1)
- BBU Interconnection (SRAN11.1 - 02)Document64 pagesBBU Interconnection (SRAN11.1 - 02)goutam4321No ratings yet
- Welcome To The LTE CPE!: Online HelpDocument52 pagesWelcome To The LTE CPE!: Online HelpgopihcNo ratings yet
- Huawei OceanStor 6800 V5 Mission-Critical Hybrid Flash Storage System Technical White PaperDocument94 pagesHuawei OceanStor 6800 V5 Mission-Critical Hybrid Flash Storage System Technical White PaperMohammed AliNo ratings yet
- Huawei Guide m2000 PDFDocument127 pagesHuawei Guide m2000 PDFMilen PetkovNo ratings yet
- EchoLife HG850a GPON Terminal Service Manual (V100R001 - 06) PDFDocument98 pagesEchoLife HG850a GPON Terminal Service Manual (V100R001 - 06) PDFagustin_rg_22No ratings yet
- Code Leader: Using People, Tools, and Processes to Build Successful SoftwareFrom EverandCode Leader: Using People, Tools, and Processes to Build Successful SoftwareRating: 4.5 out of 5 stars4.5/5 (2)
- Microsoft Virtualization: Master Microsoft Server, Desktop, Application, and Presentation VirtualizationFrom EverandMicrosoft Virtualization: Master Microsoft Server, Desktop, Application, and Presentation VirtualizationRating: 4 out of 5 stars4/5 (2)
- Microsoft Windows Server 2008 R2 Administrator's Reference: The Administrator's Essential ReferenceFrom EverandMicrosoft Windows Server 2008 R2 Administrator's Reference: The Administrator's Essential ReferenceRating: 4.5 out of 5 stars4.5/5 (3)
- Developing Virtual Reality Applications: Foundations of Effective DesignFrom EverandDeveloping Virtual Reality Applications: Foundations of Effective DesignNo ratings yet
- OT Cybersecurity Solution Buyers GuideDocument12 pagesOT Cybersecurity Solution Buyers Guideep230842No ratings yet
- Industrial Defender Utilities WP 5 2020Document6 pagesIndustrial Defender Utilities WP 5 2020ep230842No ratings yet
- Security Risk Management - Approaches and MethodologyDocument13 pagesSecurity Risk Management - Approaches and Methodologyep230842No ratings yet
- ID20-108 WP OperationalTechnologyCybersecurity 052721Document15 pagesID20-108 WP OperationalTechnologyCybersecurity 052721ep230842No ratings yet
- NIST SP 800-82 MappingGuideDocument14 pagesNIST SP 800-82 MappingGuideep230842No ratings yet
- Ieeehst 16 CainsDocument5 pagesIeeehst 16 Cainsep230842No ratings yet
- NERC CIP Comparison Guide - ID vs. PassiveDocument3 pagesNERC CIP Comparison Guide - ID vs. Passiveep230842No ratings yet
- Uws Using Mitre Attack in Threat Hunting and DetectionDocument26 pagesUws Using Mitre Attack in Threat Hunting and Detectionep230842No ratings yet
- Ethics and Accountability PDFDocument32 pagesEthics and Accountability PDFep230842No ratings yet
- Best Practices For Security Monitoring During A CrisisDocument8 pagesBest Practices For Security Monitoring During A Crisisep230842No ratings yet
- Cortex XDR: Architecture OverviewDocument26 pagesCortex XDR: Architecture Overviewep230842No ratings yet
- Ethics Moral AccountabilityDocument8 pagesEthics Moral Accountabilityep230842No ratings yet
- Applied Sciences: An Integrated Cyber Security Risk Management Approach For A Cyber-Physical SystemDocument29 pagesApplied Sciences: An Integrated Cyber Security Risk Management Approach For A Cyber-Physical SystemihabNo ratings yet
- White Paper Defense in Depth PDFDocument17 pagesWhite Paper Defense in Depth PDFep230842No ratings yet
- Cortex XDR: Architecture OverviewDocument26 pagesCortex XDR: Architecture Overviewep230842No ratings yet
- Gain Board Level SupDocument17 pagesGain Board Level Supep230842No ratings yet
- Comprehensive Guide To Operational Technology CybersecurityDocument68 pagesComprehensive Guide To Operational Technology CybersecurityDea Josh FarroNo ratings yet
- XDR: Extended Detection and ResponseDocument46 pagesXDR: Extended Detection and ResponseAnderson WanselowskiNo ratings yet
- A Solution Guide To Operational Technology Cybersecurity: White PaperDocument24 pagesA Solution Guide To Operational Technology Cybersecurity: White PaperManuelNo ratings yet
- Security in SAP HANA 2016Document17 pagesSecurity in SAP HANA 2016ep230842No ratings yet
- Lesson 1 Host Insights Add On TEMPLATE Cortex PDFDocument12 pagesLesson 1 Host Insights Add On TEMPLATE Cortex PDFep230842No ratings yet
- Security Best Practises WorksheetDocument78 pagesSecurity Best Practises WorksheetShiva KumarNo ratings yet
- URL Categories Allowed Per User GroupDocument9 pagesURL Categories Allowed Per User Groupep230842No ratings yet
- 8-Digital ForensicsDocument30 pages8-Digital Forensicsep230842No ratings yet
- Sysadmin Magazine October 2021Document32 pagesSysadmin Magazine October 2021TonyTonySNo ratings yet
- Threat Hunting With Cortex XDR: Jani Haapio Channel SEDocument32 pagesThreat Hunting With Cortex XDR: Jani Haapio Channel SEep230842No ratings yet
- CH 16Document25 pagesCH 16iamthe11No ratings yet
- White Paper Defense in Depth PDFDocument17 pagesWhite Paper Defense in Depth PDFep230842No ratings yet
- SAP Cybersecurity Comparison Chart v8Document4 pagesSAP Cybersecurity Comparison Chart v8ep2308420% (1)
- Servicedesk Plus Installation Best Practices GuideDocument5 pagesServicedesk Plus Installation Best Practices GuideaforabadNo ratings yet
- FortiADC 2000F PDFDocument8 pagesFortiADC 2000F PDFĐình Khánh BùiNo ratings yet
- How To Connect To EPRS - (Updated)Document33 pagesHow To Connect To EPRS - (Updated)Mondeh Albero100% (1)
- Manual Iws ToolDocument61 pagesManual Iws ToolSebastianCarlosNo ratings yet
- Compliance Dashboard v0.6Document449 pagesCompliance Dashboard v0.6Debanjan DeyNo ratings yet
- Syllabus Bca FinalDocument6 pagesSyllabus Bca FinalRaj VermaNo ratings yet
- 118337-Wlanpat 2-12Document21 pages118337-Wlanpat 2-12obaidu419No ratings yet
- Most Common ESM Public Folder Expansion ErrorsDocument15 pagesMost Common ESM Public Folder Expansion Errorskhushpreet1022No ratings yet
- Handle Technical ManualDocument95 pagesHandle Technical ManualgreatkithainNo ratings yet
- MTMDocument14 pagesMTMShruti DhariyaNo ratings yet
- AnalysisDocument8 pagesAnalysisGoCpg.Com ReviewNo ratings yet
- Security+ Cram Sheet - ProprofsDocument3 pagesSecurity+ Cram Sheet - Proprofstom100% (1)
- Manually Upgrading p6 Eppm For Microsoft SQL Server DatabaseDocument51 pagesManually Upgrading p6 Eppm For Microsoft SQL Server Databasejama99No ratings yet
- Fortios™ Handbook: Managing Devices For Fortios 5.0Document27 pagesFortios™ Handbook: Managing Devices For Fortios 5.0paulo_an7381No ratings yet
- Faculty: Realtime Experience: Weblogic Application Server TrainingDocument9 pagesFaculty: Realtime Experience: Weblogic Application Server TrainingSyed NoumanNo ratings yet
- Manual Referenciav5.3 ENDocument354 pagesManual Referenciav5.3 ENMahmoud AhmedNo ratings yet
- EMC Secure Remote Services (ESRS) Release 3.12 Pre Site ChecklistDocument24 pagesEMC Secure Remote Services (ESRS) Release 3.12 Pre Site Checklistmontecito1No ratings yet
- Forticlient Admin 50Document154 pagesForticlient Admin 50Aukkaranan RonachitNo ratings yet
- (Nov-2020) New PassLeader AZ-304 Exam DumpsDocument12 pages(Nov-2020) New PassLeader AZ-304 Exam Dumpsyb0% (1)
- Microsoft Security Response Center (MSRC) Progress Report 2013Document27 pagesMicrosoft Security Response Center (MSRC) Progress Report 2013MSFTSIRNo ratings yet
- XR IosDocument312 pagesXR Ioshector_oliveros_9898No ratings yet
- Technological Advancement in Banking Sectors of Pakistan by NiftDocument71 pagesTechnological Advancement in Banking Sectors of Pakistan by NiftMaria Shaffaq100% (2)
- Manonmani am Sundaranar University B.Sc. Computer Science Course DetailsDocument23 pagesManonmani am Sundaranar University B.Sc. Computer Science Course DetailslousieNo ratings yet
- Fortify Sys Reqs 22.1.0Document66 pagesFortify Sys Reqs 22.1.0quyetpv144100% (1)
- Openmediavault Readthedocs Io en LatestDocument73 pagesOpenmediavault Readthedocs Io en LatestFauzan HaritsNo ratings yet
- MicroSCADA X SYS600C 5.10 Sales Presentation - 4CAE001299Document20 pagesMicroSCADA X SYS600C 5.10 Sales Presentation - 4CAE001299Jahangir KhanNo ratings yet
- Complete Ethicacl Hacking CourseDocument2 pagesComplete Ethicacl Hacking CourseAnimorphsNo ratings yet
- Encrypting Voice Calls in Elastix and Fail2banDocument8 pagesEncrypting Voice Calls in Elastix and Fail2banGodspower InibuNo ratings yet