Professional Documents
Culture Documents
Modified Rsa Encryption Algorithm Using Four Keys IJERTCONV3IS07021
Uploaded by
Jeff HambreOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Modified Rsa Encryption Algorithm Using Four Keys IJERTCONV3IS07021
Uploaded by
Jeff HambreCopyright:
Available Formats
Special Issue - 2015 International Journal of Engineering Research & Technology (IJERT)
ISSN: 2278-0181
NCICN-2015 Conference Proceedings
Modified RSA Encryption Algorithm using Four
Keys
Nivetha A Preethy Mary S Santosh kumar J
Dept of Information Technology Dept of Information Technology Dept of Information Technology
Anand Institute of Higher Anand Institute of Higher Anand Institute of Higher
Technology, Technology, Technology,
Chennai, Tamil nadu Chennai, Tamil nadu Chennai, Tamil nadu
Abstract: The proposed paper enhances the RSA algorithm The encryption function is the only candidate for a
through the use of four prime number in combination of “trap-door one-way permutation” known to the authors.
public and private key. Hence by using this, factoring The large volume of personal and sensitive information
complexity of variable is increased, this makes the analysis currently held in computerized data banks and transmitted
process with the development of equipment and tools become
over telephone lines makes encryption increasingly
much easier. The use of four prime number will give the
ability to the modified encryption technique to provide more important. In recognition of the fact that efficient, high-
security in accessing, and also increased speed. This was quality encryption techniques are very much needed but are
developed from the original RSA algorithm the additional two in short supply, the National Bureau of Standards has
prime numbers are going to provide secrecy. Many recently adopted a “Data Encryption Standard”, developed
experiments have been done under this proving Modified at IBM. The new standard does not have property (c),
RSA encryption Algorithm using four keys to be faster and needed to implement a public-key cryptosystem.
efficient than the original encryption and decryption process.
This thesis presents the implementation of successive Xin Zhou and Xiaofei Tang[2] proposed an
subtraction operation instead of division operation. By implementation of a complete and practical RSA
applying this approach we can achieve the high computational
encrypt/decrypt solution based on the study of RSA public
speed and reduce the complexity of the mathematical steps.
Keyword: Complexity, Prime number, Public key, four keys, key algorithm. In addition, the encrypt procedure and code
algorithm. implementation is provided in details. Encryption is one of
the principal means to guarantee the security of sensitive
1. INTRODUCTION information. It not only provides the mechanisms in
Encryption is one of the principal means to grant information confidentiality, but also functioned with digital
the security of sensitive Information also functioned with signature, authentication, secret sub-keeping, system
digital signature, authentication, secret sub-keeping, system security and etc. The encryption and decryption solution
security and etc. Therefore, the purpose of adopting can ensure the confidentiality of the information, as well as
encryption techniques is to ensure the information's the integrity of information and certainty, to prevent
confidentiality, integrity and certainty, prevent information information from tampering, forgery and counterfeiting.
from tampering, forgery and counterfeiting. Encryption and decryption algorithm's security depends on
At present, the best known and most widely used public the internal structure of the rigor of mathematics, it also
key system is RSA, which was first proposed in paper "A depends on the key confidentiality.
method for obtaining digital signatures and public-key Problem for RSA encryption on the file, it
cryptosystems" by RL Rivest in 1978. It is an asymmetric indicates the RSA mathematical algorithms in the computer
(public key) cryptosystem based on number theory, which industry’s importance and its shortcomings. It discusses the
is a block cipher system. Its security is based on the questions of how to apply to the personal life of RSA
difficulty of the large number prime factorization, which is information security issues. And also contains the use of
a well-known mathematical problem that has no effective RSA and the basic principles of data encryption and
solution. decryption. In the end, it proposed a new program to
2. LITERATURE REVIEW improve RSA algorithm based on RSA cryptography and
the extensive application. In summary, this issue of the
R.L. Rivest, A. Shamir, and L. Adleman[1]
RSA encryption and decryption keys, RSA algorithm, the
proposed a method for implementing a public-key
new use of the RSA and other issues to study and make
cryptosystem whose security rests in part on the difficulty
some new programs, future work should be in the new
of factoring large numbers. If the security of our method
RSA cryptographic algorithms and a wide range of
proves to be adequate, it permits secure communications to
applications continue to research.
be established without the use of couriers to carry keys, and
it also permits one to “sign” digitized documents. The
3. PROBLEM DEFINITION
reader is urged to and a way to “break” the system. Once
the method has withstood all attacks for a sufficient length MREA is secure as compared to RSA as it based
of time it may be used with a reasonable amount of on the factoring problem as well as decisional composite
condense. residuosity assumptions which are the intractability
Volume 3, Issue 07 Published by, www.ijert.org 1
Special Issue - 2015 International Journal of Engineering Research & Technology (IJERT)
ISSN: 2278-0181
NCICN-2015 Conference Proceedings
hypothesis. This scheme also presents comparisons mathematicians who developed it, Rivest, Shamir, and
between RSA and MRSA cryptosystems in terms of Adelman. RSA today is used in hundreds of software
security and performance. This algorithm uses a mod products and can be used for key exchange, digital
operator for computational purposes. The objective of this signatures, or encryption of small blocks of data.RSA uses
thesis presents the implementation of successive a variable size encryption block and a variable size key.
subtraction operation instead of using division operator. 4.2 Attacks against plain RSA
For applying this approach we have to achieve the high There are a number of attacks against plain RSA
computational speed and reduce the complexity of the as described below. When encrypting with low encryption
mathematical steps. exponents (e.g., e = 3) and small values of the m,
(i.e., m < n1/e) the result of me is strictly less than the
3.1 Modulo Operation:
modulus n. In this case, cipher texts can be easily
In computing, modulo operation finds decrypted by taking the eth root of the cipher text over the
the remainder of division of one number by another. . integers. If the same clear text message is sent to e or more
recipients in an encrypted way, and the receivers share the
same exponent e, but different p, q, and therefore n, then it
is easy to decrypt the original clear text message via
the Chinese remainder theorem. Johan Has tad noticed that
this attack is possible even if the clear texts are not equal,
but the attacker knows a linear relation between them. This
attack was later improved by Don Coppersmith. RSA has
the property that the product of two cipher texts is equal to
the encryption of the product of the respective plaintexts.
That is m1em2e ≡ (m1m2)e (mod n). Because of this
multiplicative property a chosen-cipher text attack is
possible
Figure 4: Euclidean algorithm diagram 4.3 Key generation
3.2 Euclidean Algorithm RSA involves a public key and a private key. The
public key can be known by everyone and is used for
Euclid's method for finding the greatest common divisor encrypting messages. Messages encrypted with the public
(GCD) of two starting lengths BA and DC, both defined to key can only be decrypted in a reasonable amount of time
be multiples of a common "unit" length. In mathematics, using the private key. The keys for the RSA algorithm are
the Euclidean algorithm, or Euclid's algorithm, is a generated the following way:
method for computing the greatest common divisor
By reversing the steps in the Euclidean algorithm, 1. Choose two distinct prime numbers p and q. For
the GCD can be expressed as a sum of the two original security purposes, the integer’s p and q should be
numbers each multiplied by a positive or negative integer, chosen at random, and should be of similar bit-
e.g., the GCD of 252 and 105 is 21, and 21 = [5 × 105] + length. Prime integers can be efficiently found
[(−2) × 252]. This important property is known as Bezout's using a primality test.
identity. 2. Compute n = pq.
The simplest form of Euclid's algorithm starts
with a pair of positive integers and forms a new pair that n is used as the modulus for both the public
consists of the smaller number and the difference between and private keys. Its length, usually expressed in
the larger and smaller numbers. The process repeats until bits, is the key length.
the numbers are equal; then that value is the greatest
common divisor of the original pair. The division form of 3. Compute φ(n) = φ(p) φ(q) =
Euclid's algorithm starts with a pair of positive integers and (p − 1)(q − 1), where φ is Euler's totient function.
forms a new pair that consists of the smaller number and
the remainder obtained by dividing the larger number by 4. Choose an integer e such that 1
the smaller number. The process repeats until one number < e <φ(n) and gcd(e,φ(n)) = 1; i.e. e and φ(n)
is zero. The other number then is the greatest common are co-prime is released as the public key
divisor of the original pair. exponent. e having a short bit-length and
4. METHODOLOGY small Hamming weight results in more efficient
encryption – most commonly 216 +1=65537.
4.1 RSA System However, much smaller values of e(such as 3)
have been shown to be less secure in some
RSA is a commonly adopted public key
settings.
cryptography algorithm. The first, and still most commonly
5. Determine d as d−1 ≡ e (mod φ(n)), i.e., d is
used asymmetric algorithm RSA is named for the three
the multiplicative inverse of e (modulo φ(n)).This
Volume 3, Issue 07 Published by, www.ijert.org 2
Special Issue - 2015 International Journal of Engineering Research & Technology (IJERT)
ISSN: 2278-0181
NCICN-2015 Conference Proceedings
is more clearly stated as solve for d given d⋅e ≡ 1 Step 7: exit in for loop go to step 5
(mod φ(n)).This is often computed using
the extended Euclidean algorithm.d is kept as the Step 8: subtract phi value in b and store to phi
private key exponent.
By construction, d⋅e ≡ 1 (mod φ(n)). The public Step 9: if phi value is negative the last value of phi vale is
key consists of the modulus n and the public (or mod value
encryption) exponent e. The private key consists of the
modulus n and the private (or decryption) exponent d, Step 10: Stop the process.
which must be kept secret. p, q, and φ(n) must also be kept
secret because they can be used to calculate d. 5.2 Previous work:
An alternative, used by PKCS#1, is to
choose d matching de ≡ 1 (mod λ) with Let us take example of 125 mod 2. For that we
λ = LCM(p − 1, q − 1), where LCM is the least common take mod operator performing, the following steps,125-
multiple. Using λ instead of φ(n) allows more choices 2=123-2=121-2=119……3-2=1. So that, we want compute
for d. λ can also be defined using the Carmichael function, more (21 steps) steps want to evaluate this expression.
λ(n). Finally got the output as 1.
The ANSI X9.31 standard prescribes, IEEE 5.3 Proposed work:
1363 describes, and PKCS#1 allows, Now introduce the concept, of power subtraction.
that p and q match additional requirements: being strong That is 125-64=61-32=29-16=13-8=5-4=1. In this concept,
primes, and being different enough that Fermat we use only the 4 steps of evaluation. 125 mod 2, the
factorization fails. powers of 2 can be used. That is, nearest value of power is
64=2^6, so use of successful powers of sub tractor is used
to get the answer as 1.So that speed can be increased
6. THE EXISTING RSA ALGORITHM whereas the previous system. And also reduced the
complexity of the computation.
Key generation
1. Select FOUR PRIME NUMBERS P,Q,R,S 6. IMPLEMENTATION
2. Calculate n=p*q*r*s. This paper presents the purpose about
3. Calculate f(n)=(p-1)*(q-1) *(r-1)*(s-1) modification in modified RSA encryption and decryption.
4. Select integers e; gcd(f(n),e)=1;1<e<f(n). Here artificially small parameters are used to clarify the
5. Calculate d; d=e-1 mod f(n) concept. However, the method is applicable in general to
6. Public key KU ={e,n} all suitably selected parameters. Here four prime numbers
7. Private Key KR ={d,N}. will be used to get the public key and private key.
Encryption: Select four prime numbers.
Plain text: M<n 1. Calculate n=p*q*r*s
Cipher text : C= Memod n. P=2, q=3, r=5,s=17
Decryption: n=2*3*5*17
Cipher text to Plain text: M=Cd mod n. 2. Calculate f(n)=(p-1) (q-1) (r-1) (s-1)
Here encryption and decryption using division operation f(510) = (2-1) (3-1) (5-1)(17-1) =128
instead of using that use of successive subtraction which is f (n)=128
reduce the mathematical steps. And also to achieve the 3. Select any number 1<e<128
high computational speed. F (n) must not be divisible by e
Let e=3
5.1 Proposed Algorithm 4. Select d, multiplicative of e(mod f(n))
d= 43
Step1: Start the process The Public Key is (n = 510, e = 3)
Private Key is (n = 510, d = 43)
Given message m= 11.
Step 2: initialize i =0
5. Encryption:
C= 113mod 510 = 311; C = 311
Step 3: Calculate power of ei 6. Decryption:
M = 31143 mod 510 = 11
Step 4: If ei value is less than phi value then go to step5 B got the original message (11) which is sent by A. In
proposed algorithm use of mod function want to perform a
Step 5: if ei value is greater than phi value then goto step 6 division operation, instead of using that use of successive
subtraction which is reduce the mathematical steps. The
Step 6: ei value store in b go to step 7 above encryption and decryption as follows:
Volume 3, Issue 07 Published by, www.ijert.org 3
Special Issue - 2015 International Journal of Engineering Research & Technology (IJERT)
ISSN: 2278-0181
NCICN-2015 Conference Proceedings
Encryption: 113 mod 510 = 1331 mod 510=821-510=311 Calculate Total time for RSA:
Decryption: Same as Encryption TABLE 2:
7. RESULT AND DISCUSSION
The MREA cryptosystem is based on additive
homomorphism properties and RSA cryptosystem, additive
homomorphism scheme required four prime numbers, it
will be more difficult and take long time to factor
modulus, If RSA which is based on single modulus, and
additive homomorphism based on dual modulus, then time
required for MREA algorithm is higher than the proposed
algorithm.
COMPARISON BETWEEN THE ORIGINAL ALGORITHM
AND MODULUS ALGORITHM
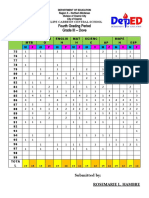
In this thesis calculate the encryption and
decryption time for 4 prime number, In modified RSA
algorithm, the time taken for encryption and decryption is
high using division of arithmetic operation in the following
table1 and table2.
Calculate Total (Encryption and Decryption) Time for
MREA MODULUS OPERATION
Comparison of MREA and RSA algorithm:
TABLE1: 14000
12000
10000 MREA with
Mod
8000
function
6000
RSA
4000
2000
0
16 16 32 128
Figure 5: Analysis of RSA and MREA
The above table and figure shows that the process
of encryption and decryption in the proposed method are
faster than the original method by the apparent results. In
modulus function instead of using that division operation,
use of successive subtraction which is reduce the
mathematical steps and also to achieve the high
computational speed. And also this proposed algorithm is
more secure for mathematical attacks
8. CONCLUSION
Encryption algorithm plays an important role in
communication Security. The proposed cryptography
procedure is the enhanced proposal of our previous
research work where the concept of speed enhancement of
modulus functions. Using this idea to reduce the
mathematical steps to solve that expression. So we
conclude that easily computation can be performed and
complexity was reduced. Complexity time also decreased
Volume 3, Issue 07 Published by, www.ijert.org 4
Special Issue - 2015 International Journal of Engineering Research & Technology (IJERT)
ISSN: 2278-0181
NCICN-2015 Conference Proceedings
by using successive subtraction technique. So that the
speed can be increased.
In this thesis an algorithm is proposed for
Modified RSA modulus factorization. The new algorithm
aims to obtain the prime factors of modulus in Modified
RSA algorithm. This algorithm is relatively simple and
scalable. This method can be used for factorization of
subtraction, very helpful to generate results in high speed.
REFERENCES:
[1] Rivest, R.; A. Shamir; L. Adleman. "A Method for Obtaining Digital
Signatures and Public-Key Cryptosystems", Communications of the
ACM 21 (2): 120–126, doi: 10.1145/359340.359342, 1977
[2] Bell, E. T. "The Prince of Amateurs: Fermat.", New York: Simon and
Schuster, pp. 56-72, 1986.
[3] Gabriel Vasile Iana1, Petre Anghelescu1, Gheorghe Serban “RSA
encryption algorithm implemented on FPGA” 1University of Pitesti,
Department of Electronics and Computers, Romania, Arges, Pitesti,
Str. Targul din Vale, No. 1, Code: 110040.
[4] Na Qi Jing Pan Qun Ding “The implementation of FPGA-based RSA
public-key algorithm and its application in mobile-phone SMS
encryption system” HeiLongjiang University Electronic Engineering
Key Laboratory of Universities in Heilongjiang Province Harbin,
China.
[5] Sonal Sharma, Prashant Sharma and Ravi Shankar Dhakar “RSA
Algorithm Using Modified Subset Sum Cryptosystem” International
Conference on Computer & Communication Technology (ICCCT)-
2011
[3] João Carlos Leandro da Silva, “Factoring Semi primes and Possible
Implications”, IEEE in Israel, 26th Convention, pp. 182-183, Nov.
2010.
[4] Sattar J Aboud, “An efficient method for attack RSA scheme”, IEEE
2009.
[5] L. Scripcariu, M.D. Frunza, "A New Character Encryption
Algorithm", Proceedings of the Intern. Conference on
Microelectronics and Computer Science, Chisinau, (Republica
Moldova), ICMCS 2005, pp. 83 - 86, Sept., 2005.
[6] B. Schneier, Applied cryptography, second edition, NY: John Wiley
&Sons, Inc., 1996.
[7] J. Pollard, "Monte Carlo methods for index computation (mod p)",
Math. Comp., Vol. 32, pp.918-924, 1978.
[8] R. P. Brent, “An improved Monte Carlo factorization algorithm”, BIT
20 (1980), 176-184. MR 82a:10007, Zbl 439.65001. rpb051.
[9] R. Rivest, A. Shamir, and L. Adleman, "A Method for Obtaining
Digital Signatures and Public-Key Cryptosystems," vol. 21 (2),
pp.120-126, 1978.
Volume 3, Issue 07 Published by, www.ijert.org 5
You might also like
- Ijert Ijert: Improvement Over Public Key Encryption Algorithm For Security in Network CommunicationsDocument4 pagesIjert Ijert: Improvement Over Public Key Encryption Algorithm For Security in Network CommunicationsNandha KumarNo ratings yet
- Xin Zhou 2011Document4 pagesXin Zhou 2011Shashi TiwariNo ratings yet
- High Speed Implementation of RSA Algorithm With Modified Keys ExchangeDocument5 pagesHigh Speed Implementation of RSA Algorithm With Modified Keys ExchangeYoniNo ratings yet
- RSA 32-Bit Implementation TechniqueDocument6 pagesRSA 32-Bit Implementation TechniqueMaya BoutebNo ratings yet
- A Comparative Analysis of Cryptographic Algorithms AES & RSA and Hybrid Algorithmfor Encryption and DecryptionDocument8 pagesA Comparative Analysis of Cryptographic Algorithms AES & RSA and Hybrid Algorithmfor Encryption and DecryptionInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- 5-4-26-251Document4 pages5-4-26-251abdulg abdulNo ratings yet
- Research Paper On Rsa AlgorithmDocument8 pagesResearch Paper On Rsa Algorithmafmcpbnrp100% (1)
- Deep KnowledgeDocument6 pagesDeep KnowledgeGitesh GayakwadNo ratings yet
- 2012 - High Speed Implementation of RSA Algorithm With Modified Keys ExchangeDocument4 pages2012 - High Speed Implementation of RSA Algorithm With Modified Keys ExchangePeraKojotNo ratings yet
- A Review On RSA Encryption Algorithm: Shaina Garg, Dr. Mukesh Kumar RanaDocument4 pagesA Review On RSA Encryption Algorithm: Shaina Garg, Dr. Mukesh Kumar RanaPatient ZeroNo ratings yet
- Irjet V5i4919Document5 pagesIrjet V5i4919ghada sayedNo ratings yet
- Irjet Image Encryption Techniques and CoDocument14 pagesIrjet Image Encryption Techniques and Cosnehpatel0308No ratings yet
- Study of RSA Public Key GenerationDocument4 pagesStudy of RSA Public Key GenerationPahchan GargNo ratings yet
- Enhanced Rsa Cryptosystem Based On Three Prime Numbers: Vivek Choudhary and Mr. N. PraveenDocument5 pagesEnhanced Rsa Cryptosystem Based On Three Prime Numbers: Vivek Choudhary and Mr. N. PraveenHarshil ShahNo ratings yet
- A Study of Encryption Algorithms (RSA, DES, 3DES and AES) For Information SecurityDocument6 pagesA Study of Encryption Algorithms (RSA, DES, 3DES and AES) For Information SecurityJeff HambreNo ratings yet
- New Encryption AlgorithmDocument5 pagesNew Encryption AlgorithmcheintNo ratings yet
- Research Papers On Rsa AlgorithmDocument5 pagesResearch Papers On Rsa Algorithmnozyk1m0nut2100% (1)
- Design and Implementation of Pipelined AES Encryption System Using FPGADocument7 pagesDesign and Implementation of Pipelined AES Encryption System Using FPGAC BNo ratings yet
- Bello M ConfDocument11 pagesBello M ConfSýstëmàtíçBéllóNo ratings yet
- A Study and Analysis On Symmetric Cryptography: Sourabh Chandra Siddhartha Bhattacharyya Smita Paira SK Safikul AlamDocument8 pagesA Study and Analysis On Symmetric Cryptography: Sourabh Chandra Siddhartha Bhattacharyya Smita Paira SK Safikul AlamSamuele TesfayeNo ratings yet
- Methods Toward Enhancing Rsa Algorithm: A SurveyDocument18 pagesMethods Toward Enhancing Rsa Algorithm: A SurveyAIRCC - IJNSANo ratings yet
- .Cryptography in Cloud Computing A Basic Approach To Ensure Security in Cloud PDFDocument4 pages.Cryptography in Cloud Computing A Basic Approach To Ensure Security in Cloud PDFHaimy mathaiNo ratings yet
- Global Transitions Proceedings: Fursan Thabit, Sharaf Alhomdy, Associate Prof, Sudhir Jagtap, DR, ProfDocument11 pagesGlobal Transitions Proceedings: Fursan Thabit, Sharaf Alhomdy, Associate Prof, Sudhir Jagtap, DR, ProfYeremia Ivan SabdonoNo ratings yet
- Synopsis of ThesisDocument5 pagesSynopsis of Thesishimanshus13No ratings yet
- Client Server Chat ApplicationDocument6 pagesClient Server Chat ApplicationHabib Ait ElkadiNo ratings yet
- Linear Polarization of Keys (Public and Private) For Increased RSA SecurityDocument4 pagesLinear Polarization of Keys (Public and Private) For Increased RSA SecurityInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Advanced Cryptanalytic Algorithm For Data SecurityDocument4 pagesAdvanced Cryptanalytic Algorithm For Data SecurityInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Secure Cloud Storage Using Different Algorithms in CryptographyDocument10 pagesSecure Cloud Storage Using Different Algorithms in CryptographyIJRASETPublicationsNo ratings yet
- IOP Conference Evaluates Encryption AlgorithmsDocument11 pagesIOP Conference Evaluates Encryption AlgorithmsAbhay JhaNo ratings yet
- Efficiency and Security of Data With Symmetric Encryption AlgorithmsDocument4 pagesEfficiency and Security of Data With Symmetric Encryption Algorithmsexpert 60No ratings yet
- Software Quality Assurance in Network Security Using Cryptographic TechniquesDocument10 pagesSoftware Quality Assurance in Network Security Using Cryptographic TechniquesInternational Journal of Computer and Communication System EngineeringNo ratings yet
- Improved Trial Division Algorithm by Lagrange's Interpolation FunctionDocument5 pagesImproved Trial Division Algorithm by Lagrange's Interpolation FunctionEditor IJRITCCNo ratings yet
- 25j.rsa Public Key Cryptography Algorithm A ReviewDocument6 pages25j.rsa Public Key Cryptography Algorithm A ReviewAnousouya DeviNo ratings yet
- Application of Classical Encryption Techniques For Securing Data - A Threaded ApproachDocument8 pagesApplication of Classical Encryption Techniques For Securing Data - A Threaded ApproachJames MorenoNo ratings yet
- Paper 59-Cryptography A Comparative Analysis For Modern TechniquesDocument7 pagesPaper 59-Cryptography A Comparative Analysis For Modern Techniquesadi putraNo ratings yet
- 9 Dr. Amit Sharma 1459672381 - 254VDocument6 pages9 Dr. Amit Sharma 1459672381 - 254VamittechnosoftNo ratings yet
- IT - IS - Instructor Lab Manual - Even 17-18 SampleDocument4 pagesIT - IS - Instructor Lab Manual - Even 17-18 Samplejasvant282842953No ratings yet
- Sensors: Algorithms For Lightweight Key ExchangeDocument14 pagesSensors: Algorithms For Lightweight Key ExchangeReema AgarwalNo ratings yet
- Introduction to Cryptography ToolsDocument35 pagesIntroduction to Cryptography ToolsManish AeronNo ratings yet
- The Use of Elliptic Curves in Cryptography: Aster S Hesis in AthematicsDocument76 pagesThe Use of Elliptic Curves in Cryptography: Aster S Hesis in AthematicsTeodoraNo ratings yet
- A Review On Implementation of RSA Cryptosystem Using Ancient Indian Vedic MathematicsDocument3 pagesA Review On Implementation of RSA Cryptosystem Using Ancient Indian Vedic MathematicsEditor IJRITCCNo ratings yet
- Study on Cryptanalysis of Tiny Encryption AlgorithmDocument4 pagesStudy on Cryptanalysis of Tiny Encryption Algorithmmiki_dudaulNo ratings yet
- Ijcsn 2013 2 6 153 PDFDocument17 pagesIjcsn 2013 2 6 153 PDFijcsnNo ratings yet
- nis (1)_removedDocument11 pagesnis (1)_removedmadhavronitNo ratings yet
- A Comparative Survey of Symmetric and Asymmetric Key CryptographyDocument12 pagesA Comparative Survey of Symmetric and Asymmetric Key CryptographyLaine VenâncioNo ratings yet
- Digital SIGNATUREDocument4 pagesDigital SIGNATUREMorosan DimitrieNo ratings yet
- IEEE 2017 Enhanced RSA Algorithm With Varying Key Sizes For Data Security in CloudDocument4 pagesIEEE 2017 Enhanced RSA Algorithm With Varying Key Sizes For Data Security in Cloudakash rawatNo ratings yet
- AbstractDocument1 pageAbstractkoti516No ratings yet
- JETIR2308519Document9 pagesJETIR2308519Hitesh TumsareNo ratings yet
- Combination of The "Data Encryption Standard" Algorithm (DES) and The "Public-Key Encryption" Algorithm (RSA) On The Key - Generation StageDocument3 pagesCombination of The "Data Encryption Standard" Algorithm (DES) and The "Public-Key Encryption" Algorithm (RSA) On The Key - Generation StageInternational Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Big Data Security Issues Based On Quantum Cryptography: Prakruti Chaudhari, Prof. Riya GohilDocument5 pagesBig Data Security Issues Based On Quantum Cryptography: Prakruti Chaudhari, Prof. Riya GohilSakshi SinghNo ratings yet
- Rsa Ntos CryptoDocument2 pagesRsa Ntos Cryptotokig61739No ratings yet
- RSA and ECC Thesis PDFDocument21 pagesRSA and ECC Thesis PDFHarpreet SinghNo ratings yet
- Data Security in Cloud Computing Using RSA Algorithm ReviewDocument4 pagesData Security in Cloud Computing Using RSA Algorithm Reviewflora muasyaNo ratings yet
- 09 - Chapter 5Document21 pages09 - Chapter 5Dr D SuneethaNo ratings yet
- 1 s2.0 S235291482100157X MainDocument7 pages1 s2.0 S235291482100157X Maindavid t. KleinNo ratings yet
- A Study of Cryptographic TechniquesDocument10 pagesA Study of Cryptographic TechniquesApi indotechsNo ratings yet
- Efficent Method For Breaking Rsa SchemeDocument5 pagesEfficent Method For Breaking Rsa SchemeUsman TariqNo ratings yet
- Data Encryption StandardDocument37 pagesData Encryption Standardchristian MacNo ratings yet
- New Frontiers in Cryptography: Quantum, Blockchain, Lightweight, Chaotic and DNAFrom EverandNew Frontiers in Cryptography: Quantum, Blockchain, Lightweight, Chaotic and DNANo ratings yet
- Grading SheetDocument2 pagesGrading SheetJeff HambreNo ratings yet
- Go Winds: Volume 4 Number 4 Winter 2001 $3.00Document12 pagesGo Winds: Volume 4 Number 4 Winter 2001 $3.00Jeff HambreNo ratings yet
- Implementation of Forward ChainingDocument7 pagesImplementation of Forward ChainingJeff HambreNo ratings yet
- Automated School Form 2 - DepEdDocument35 pagesAutomated School Form 2 - DepEdJeff HambreNo ratings yet
- Dianna Shien Bentulan: With HonorsDocument4 pagesDianna Shien Bentulan: With HonorsJeff HambreNo ratings yet
- Department of Education School Form 8 Learner's Basic Health and Nutrition Report (SF8)Document12 pagesDepartment of Education School Form 8 Learner's Basic Health and Nutrition Report (SF8)Jeff HambreNo ratings yet
- Bandwidth Allocation Mechanism Based On Users' Web Usage Patterns For Campus NetworksDocument10 pagesBandwidth Allocation Mechanism Based On Users' Web Usage Patterns For Campus NetworksJeff HambreNo ratings yet
- A Computer Package For Measuring The STRDocument11 pagesA Computer Package For Measuring The STRJeff HambreNo ratings yet
- Fourth Grading Period Grade III - Dove: Felipe Carreon Central SchoolDocument2 pagesFourth Grading Period Grade III - Dove: Felipe Carreon Central SchoolJeff HambreNo ratings yet
- A Study of Encryption Algorithms (RSA, DES, 3DES and AES) For Information SecurityDocument6 pagesA Study of Encryption Algorithms (RSA, DES, 3DES and AES) For Information SecurityJeff HambreNo ratings yet
- Novena to Saint CharbelDocument2 pagesNovena to Saint CharbelJeff HambreNo ratings yet
- Huawei B890 SmartHub User GuideDocument44 pagesHuawei B890 SmartHub User GuideMesar AdrianNo ratings yet
- 6.8.1 Packet Tracer - Configure NAT For IPv4Document2 pages6.8.1 Packet Tracer - Configure NAT For IPv4Jeff HambreNo ratings yet
- On Correlation Between The Order of S-Boxes and The Strength of DESDocument10 pagesOn Correlation Between The Order of S-Boxes and The Strength of DESJeff HambreNo ratings yet
- 7.6.1 Packet Tracer - WAN ConceptsDocument3 pages7.6.1 Packet Tracer - WAN ConceptsJeff HambreNo ratings yet
- Cosc 316 Assn 2Document2 pagesCosc 316 Assn 2Jeff HambreNo ratings yet
- Comment: Published July 10, 2020 S2589-7500 (20) 30162-XDocument2 pagesComment: Published July 10, 2020 S2589-7500 (20) 30162-XJeff HambreNo ratings yet
- Developing an E-Learning system using DSDM to support teaching and learningDocument13 pagesDeveloping an E-Learning system using DSDM to support teaching and learningJeff HambreNo ratings yet
- Pi 11 143 PDFDocument9 pagesPi 11 143 PDFJeff HambreNo ratings yet
- Encyclopedia Chapter Draft v10 - FW PDFDocument14 pagesEncyclopedia Chapter Draft v10 - FW PDFRudi GunawanNo ratings yet
- 6.6.7 Packet Tracer - Configure PATDocument4 pages6.6.7 Packet Tracer - Configure PATJeff HambreNo ratings yet
- Applications of Digital Technology in COVID-19 PandemicDocument6 pagesApplications of Digital Technology in COVID-19 PandemicolgranadosNo ratings yet
- Defining The Scourge of COVID-19 Hyperinflammatory Syndrome: Francesco Del GaldoDocument3 pagesDefining The Scourge of COVID-19 Hyperinflammatory Syndrome: Francesco Del GaldoJeff HambreNo ratings yet
- Comment: Lancet Digital Health 2020Document2 pagesComment: Lancet Digital Health 2020kayegi8666No ratings yet
- Activity 12 PDFDocument6 pagesActivity 12 PDFJeff HambreNo ratings yet
- QR Code Based Smart Attendance SystemDocument11 pagesQR Code Based Smart Attendance SystemyochanNo ratings yet
- Correspondence: Genetic Variants Mimicking Therapeutic Inhibition of IL-6 Receptor Signaling and Risk of COVID-19Document2 pagesCorrespondence: Genetic Variants Mimicking Therapeutic Inhibition of IL-6 Receptor Signaling and Risk of COVID-19Jeff HambreNo ratings yet
- DB Activity 2 Creating Server Tables PDFDocument1 pageDB Activity 2 Creating Server Tables PDFJeff HambreNo ratings yet
- QR Code Based Smart Attendance SystemDocument11 pagesQR Code Based Smart Attendance SystemyochanNo ratings yet
- Cold WarDocument42 pagesCold WarTaiba HabibNo ratings yet
- NN47205-500 05.01 Config-SystemDocument328 pagesNN47205-500 05.01 Config-SystemMatias SalatinoNo ratings yet
- AM 2442FX AM 3242FX: User's Manual Manual Del UsuarioDocument32 pagesAM 2442FX AM 3242FX: User's Manual Manual Del UsuarioarsieiraNo ratings yet
- Social Media and Its Impact On Academic Performance of Students in University of MindanaoDocument6 pagesSocial Media and Its Impact On Academic Performance of Students in University of MindanaoPark Shin HyeNo ratings yet
- SAnet CD 9811017409 PDFDocument357 pagesSAnet CD 9811017409 PDFoeamaoesahaNo ratings yet
- Online Reading Test 2 Practice QuestionsDocument16 pagesOnline Reading Test 2 Practice QuestionsThu Cúc VũNo ratings yet
- NajeebRehman 1505 14145 1/AFN ExamplesDocument47 pagesNajeebRehman 1505 14145 1/AFN ExamplesQazi JunaidNo ratings yet
- Recon OpticalDocument3 pagesRecon Opticalthekingfisher1No ratings yet
- JVC Mini DV and S-VHS Deck Instruction Sheet: I. Capturing FootageDocument3 pagesJVC Mini DV and S-VHS Deck Instruction Sheet: I. Capturing Footagecabonedu0340No ratings yet
- Flava Works vs. MyVidster, Leaseweb, Voxel - Net, Et All - 4th Amended ComplaintDocument340 pagesFlava Works vs. MyVidster, Leaseweb, Voxel - Net, Et All - 4th Amended ComplaintPhillip BleicherNo ratings yet
- How To Build A Shed With A Slanted Roof Step-by-Step GuideDocument39 pagesHow To Build A Shed With A Slanted Roof Step-by-Step GuideFederico BarberisNo ratings yet
- CPE655 Solid Waste ManagementDocument108 pagesCPE655 Solid Waste ManagementAmirah SufianNo ratings yet
- English Reviewer Subject-Verb Agreement Exercise 1Document3 pagesEnglish Reviewer Subject-Verb Agreement Exercise 1Honeybel EmbeeNo ratings yet
- ch-1 Phy MEASUREMENT AND MOTIONDocument2 pagesch-1 Phy MEASUREMENT AND MOTIONRakesh GuptaNo ratings yet
- ĐỀ THI GIỮA KÌ 2 - E9 (TẤN)Document4 pagesĐỀ THI GIỮA KÌ 2 - E9 (TẤN)xyencoconutNo ratings yet
- g10 Ntot Physics em SpectrumDocument50 pagesg10 Ntot Physics em Spectrumapi-283862617100% (5)
- 07 Trumpet 2, 3Document3 pages07 Trumpet 2, 3Eneas Augusto100% (1)
- STOW - Vol. 3 - ScheduleDocument12 pagesSTOW - Vol. 3 - ScheduleDavid A. Malin Jr.100% (2)
- Communicating EffectivelyDocument7 pagesCommunicating EffectivelyPaulo LewisNo ratings yet
- Indian Scale For Assessment of AutismDocument15 pagesIndian Scale For Assessment of Autismlakshita2811No ratings yet
- Linear and Nonlinear Dynamic Analysis of Masonry I PDFDocument16 pagesLinear and Nonlinear Dynamic Analysis of Masonry I PDFsaurav rajNo ratings yet
- Quiz ManaSciDocument15 pagesQuiz ManaSciRocio Isabel LuzuriagaNo ratings yet
- Levis Vs VogueDocument12 pagesLevis Vs VoguedayneblazeNo ratings yet
- Business Profile (JAO-REN)Document15 pagesBusiness Profile (JAO-REN)Michael T. SebullenNo ratings yet
- Anuraj JainDocument3 pagesAnuraj Jainanuraj1983No ratings yet
- Cases in OBLIGATIONS AND CONTRACTSDocument17 pagesCases in OBLIGATIONS AND CONTRACTSRommell Esteban ConcepcionNo ratings yet
- 2018 Gauss 7 ContestDocument4 pages2018 Gauss 7 ContestpriyagvNo ratings yet
- 7 Introduction To Life SkillsDocument2 pages7 Introduction To Life SkillsMailat SoranaNo ratings yet
- Abm01 - Module 5-6.1 (Bus. Transaction)Document19 pagesAbm01 - Module 5-6.1 (Bus. Transaction)Love JcwNo ratings yet
- Plusafeeder- 2020SPO样本册-英文Document76 pagesPlusafeeder- 2020SPO样本册-英文sugiantoNo ratings yet