Professional Documents
Culture Documents
Shadow IT Audit Program
Uploaded by
kenny15220Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Shadow IT Audit Program
Uploaded by
kenny15220Copyright:
Available Formats
IS Audit/Assurance Program for Shadow IT
Table of Contents
IS Audit/Assurance Program for Shadow IT...................................................................................3
Audit Subject: Shadow IT...........................................................................................................3
Audit Objectives...........................................................................................................................3
Audit Scope..................................................................................................................................3
Business Impact and Risk.............................................................................................................3
Minimum Audit Skills..................................................................................................................4
Testing Steps................................................................................................................................4
Acknowledgments........................................................................................................................5
Note: The Shadow IT audit program worksheet is provided as a separate file.
© ISACA 2017 All Rights Reserved Page 2
IS Audit/Assurance Program for Shadow IT
IS Audit/Assurance Program for Shadow IT
Audit Subject: Shadow IT
Shadow IT is growing at a staggering pace as enterprises strive to be more agile, flexible and
competitive. Ease of adoption, rapid deployment and cost savings often make shadow IT
solutions appear beneficial from a business standpoint. However, the risk is often overlooked.
Therefore, ISACA has developed an audit/assurance program to provide enterprises with a
framework for managing shadow IT.
Over the years, many IT organisations invested in control frameworks to increase the security
and reliability of their services. Wherever applications are deployed outside of these frameworks,
they have potential to undermine the enterprise’s overall security posture.
Audit Objectives
The objective of a shadow IT audit is to inform management regarding the effectiveness of
shadow IT governance, monitoring and management. The review will focus on shadow IT
governance and response mechanisms as well as supporting IT processes that can help manage
the risk associated with shadow IT. The review will rely upon other IT audits, including those
governing identity and access management, change management and backup and recovery
management processes. The shadow IT audit/assurance program seeks to:
Provide management with an assessment of shadow IT policies, procedures and operating
effectiveness
Identify control weaknesses that could result in proliferation of shadow IT solutions and
greater likelihood that shadow IT is not detected
Evaluate the effectiveness of the enterprise’s response to and ongoing management of
shadow IT
Audit Scope
The audit/assurance program is built on the following three categories:
Prevent
Discover
Manage
The auditor will identify the scope of organizational functions, systems and assets to be
reviewed.
Business Impact and Risk
Critical business applications existing outside of IT control frameworks may not be visible to IT
control, information security or vendor-management functions and may therefore creating risk
that has not been measured.
© ISACA 2017 All Rights Reserved Page 3
IS Audit/Assurance Program for Shadow IT
Shadow IT can have the following business impacts:
Security of data stored by third-party vendors may be compromised.
Fines, lawsuits and legal fees may result from noncompliance and/or loss of confidential or
consumer information.
Lack of knowledge of shadow IT solutions could cause loss of time and productivity.
Complicated IT architecture may increase the risk of business disruption.
Costs may increase and other complications may arise in relation to services by third-party
development vendors.
Minimum Audit Skills
The IT audit and assurance professional must understand security, controls and IT processes. The
auditor should have sufficient functional and business knowledge to assess alignment with
business strategy. Professionals should complete the necessary research to understand the nature
of shadow IT and the risk it may represent to the enterprise.
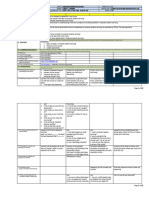
Testing Steps
Audit steps have been developed for each category and subprocess to evaluate the effectiveness
of the enterprise’s controls. Refer to the accompanying spreadsheet file for the full program.
In combination with the audit/assurance program, auditors may conduct interviews with key
stakeholders to help identify shadow IT and assess the operational effectiveness of supporting
processes. The auditor should approach interviews openly and ask indirect questions to
discourage interviewees from withholding information.
Consider the following questions:
1. What IT solutions do you or your team use to increase productivity?
2. Are there any employees responsible for system support, operation or development within
your function?
3. Are there any IT solutions where you must seek IT support from third-party vendors?
4. What process would you follow in the acquisition of a new IT solution?
5. Can you claim IT-related expenses through your budget (e.g., licensing costs)?
6. Have you ever received any education or training on the risk of shadow IT?
7. Are all the IT solutions you use documented within your business continuity management
documentation?
© ISACA 2017 All Rights Reserved Page 4
IS Audit/Assurance Program for Shadow IT
Acknowledgments
Lead Developer
Ewan Johnston, CISA, United Kingdom
Expert Reviewers
Rosemary Amato, CISA
Mohammed J. Khan, CISA, CRISC, CIPM
Chris Wilken, CISA, CGEIT
Sanjiv Agarwala, CISA, CISM, CGEIT
Board of Directors
Theresa Grafenstine, CISA, CRISC, CGEIT, CGAP, CGMA, CIA, CISSP, CPA, Deloitte-Arlington, VA, USA,
Chair
Robert Clyde, CISM, Clyde Consulting LLC, USA, Vice-Chair
Brennan Baybeck, CISA, CRISC, CISM, CISSP, Oracle Corporation, USA, Director
Zubin Hagar, CISA, CISM, PMP, Amazon Web Services, UK, Director
Peter Christiaans, CISA, CRISC, CISM, PMP, Deloitte Consulting LLP, USA, Director
Hironori Goth, CISA, CRISC, CISM, CGEIT, ABCP, Five-I, LLC, Japan, Director
Mike Hughes, CISA, CRISC, CGEIT, Haines Watts, UK, Director
Leonard Ong, CISA, CRISC, CISM, CGEIT, CPP, CFE, PMP, CIPM, CIPT, CISSP ISSMP-ISSAP, CSSLP,
CITBCM, GCIA, GCIH, GSNA, GCFA, Merck & Co., Inc., Singapore, Director
R.V. Raghu, CISA, CRISC, Versatilist Consulting India Pvt. Ltd., India, Director
Jo Stewart-Rattray, CISA, CRISC, CISM, CGEIT, FACS CP, BRM Huldah, Australia, Director
Ted Wolff, CISA, Vanguard, Inc., USA, Director
Tichaona Zororo, CISA, CRISC, CISM, CGEIT, COBIT 5 Certified Assessor, CIA, CRMA, EGIT |
Enterprise Governance of IT (Pty) Ltd, South Africa, Director
Christos K. Dimitriadis, Ph.D., CISA, CRISC, CISM, Intralot, S.A., Greece, Past Chair
Robert E Stroud, CRISC, CGEIT, Forrester Research, Inc., USA, Past Chair
Tony Hayes, CGEIT, AFCHSE, CHE, FACS, FCPA, FIIA, Queensland Government, Australia, Past Chair
Matt Loeb, CGEIT, FASAE, CAE, ISACA, USA, Director
© ISACA 2017 All Rights Reserved Page 5
IS Audit/Assurance Program for Shadow IT
About ISACA
Nearing its 50th year, ISACA® (isaca.org) is a global association helping individuals and
enterprises achieve the positive potential of technology. Technology powers today’s world and
ISACA equips professionals with the knowledge, credentials, education and community to
advance their careers and transform their organizations. ISACA leverages the expertise of its
half-million engaged professionals in information and cyber security, governance, assurance, risk
and innovation, as well as its enterprise performance subsidiary, CMMI® Institute, to help
advance innovation through technology. ISACA has a presence in more than 188 countries,
including more than 215 chapters and offices in both the United States and China.
Disclaimer
ISACA has designed and created IS Audit/Assurance Program for Shadow IT (the “Work”)
primarily as an educational resource for audit professionals. ISACA makes no claim that use of
any of the Work will assure a successful outcome. The Work should not be considered inclusive
of all proper information, procedures and tests or exclusive of other information, procedures and
tests that are reasonably directed to obtaining the same results. In determining the propriety of
any specific information, procedure or test, audit professionals should apply their own
professional judgment to the specific circumstances presented by the particular systems or
information technology environment.
Reservation of Rights
© 2017 ISACA. All rights reserved. No part of this publication may be used, copied, reproduced,
modified, distributed, displayed, stored in a retrieval system or transmitted in any form by any
means (electronic, mechanical, photocopying, recording or otherwise) without the prior written
authorization of ISACA.
ISACA
3701 Algonquin Road, Suite 1010
Rolling Meadows, IL 60008 USA
Phone: +1.847.660.5505
Fax: +1.847.253.1755
Email: mailto:info@isaca.org
Website: www.isaca.org
Provide feedback: www.isaca.org/auditprograms
Participate in the ISACA Knowledge Center: www.isaca.org/knowledge-center
Twitter: www.twitter.com/ISACANews
LinkedIn: www.linkd.in/ISACAOfficial
Facebook: www.facebook.com/ISACAHQ
Instagram: www.instagram.com/isacanews/
ISBN 978-1-60420-722-4
IS Audit/Assurance Program for Shadow IT
© ISACA 2017 All Rights Reserved Page 6
You might also like
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (590)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (401)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (842)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (897)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5807)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (345)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1091)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Cyber ReportDocument121 pagesCyber ReportÄl ÖÏvínNo ratings yet
- FujiGSA 070107Document23 pagesFujiGSA 070107Nguyen Trong SachNo ratings yet
- What Is ?: SoftwareDocument12 pagesWhat Is ?: Softwarekishore5783No ratings yet
- Exercise: Xercise BjectiveDocument23 pagesExercise: Xercise BjectiveKrishna PriyaNo ratings yet
- A Guide To Mpeg Fundamentals and Protocol Analysis: Updated With Qos/Qoe Diagnostics and TroubleshootingDocument108 pagesA Guide To Mpeg Fundamentals and Protocol Analysis: Updated With Qos/Qoe Diagnostics and Troubleshootinginfo gear4No ratings yet
- Oracle® Database Patch 22243551 - Database Patch For Engineered Systems and DB In-Memory 12.1.0.2Document10 pagesOracle® Database Patch 22243551 - Database Patch For Engineered Systems and DB In-Memory 12.1.0.2Thiago MedeirosNo ratings yet
- DSP Question and DPSDDocument3 pagesDSP Question and DPSDaasminarNo ratings yet
- Annalise Kraus ResumeDocument1 pageAnnalise Kraus ResumeannalisekrausNo ratings yet
- EAIDocument15 pagesEAIrahulsseNo ratings yet
- Oxygen Toxicity CalculationsDocument12 pagesOxygen Toxicity CalculationsAdmNo ratings yet
- TT4875Document1 pageTT4875Benjazz31No ratings yet
- Firstnet / LMR: System InterconnectionDocument6 pagesFirstnet / LMR: System InterconnectionShy GuyNo ratings yet
- Updated ML LAB Manual-2020-21Document57 pagesUpdated ML LAB Manual-2020-21SnehaNo ratings yet
- Scan CodeDocument35 pagesScan Codec282707No ratings yet
- Resume and Cover LetterDocument3 pagesResume and Cover Letterapi-285170225No ratings yet
- 3G Template V4 7Document59 pages3G Template V4 7callreturnsNo ratings yet
- Multichannel Attendance Management System Using QR Code and LocationDocument7 pagesMultichannel Attendance Management System Using QR Code and LocationDervpolo VansNo ratings yet
- Unifique Meta AAU Test Report-0122Document11 pagesUnifique Meta AAU Test Report-0122Kiko AndradeNo ratings yet
- 6a8467c5 1675934506819Document2 pages6a8467c5 1675934506819amtul mouizNo ratings yet
- Export File Not WorkingDocument14 pagesExport File Not WorkingRahul Gupta100% (3)
- Anithakumarisingamaneni X 2 Pax Kulblr 19janDocument4 pagesAnithakumarisingamaneni X 2 Pax Kulblr 19janjames cookNo ratings yet
- Discrete Math Chapter 5Document14 pagesDiscrete Math Chapter 5kumar_anup11No ratings yet
- Daily Lesson Log For Css g12 SY 2019 2020Document82 pagesDaily Lesson Log For Css g12 SY 2019 2020Emily S. AwaNo ratings yet
- Chem 3 DDocument334 pagesChem 3 DBastosZayasJoseNo ratings yet
- User's Manual: Tower and Rack-Mount Convertible UPSDocument14 pagesUser's Manual: Tower and Rack-Mount Convertible UPSAbdelwhab ElsaftyNo ratings yet
- Vtu SyllabusDocument140 pagesVtu Syllabuss.kotireddy44586No ratings yet
- IBM Cognos TM1: Reference GuideDocument282 pagesIBM Cognos TM1: Reference GuiderodublinNo ratings yet
- Lab Exercise - 802.11: ObjectiveDocument15 pagesLab Exercise - 802.11: Objectiveravi_nakarmi20019650No ratings yet
- Math F212 1122Document3 pagesMath F212 1122shivam12365No ratings yet
- U CESP4 MicroGridsPy Tutorial PDFDocument24 pagesU CESP4 MicroGridsPy Tutorial PDFRenzo Diaz DelgadoNo ratings yet