Professional Documents
Culture Documents
Universitas Tarumanagara: Fakultas Ekonomi Dan Bisnis - Magister Akuntansi
Uploaded by
Bella Angelina0 ratings0% found this document useful (0 votes)
25 views19 pagesOriginal Title
pert 01_romney_ais14_inppt_05_Untar
Copyright
© © All Rights Reserved
Available Formats
PPSX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PPSX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
25 views19 pagesUniversitas Tarumanagara: Fakultas Ekonomi Dan Bisnis - Magister Akuntansi
Uploaded by
Bella AngelinaCopyright:
© All Rights Reserved
Available Formats
Download as PPSX, PDF, TXT or read online from Scribd
You are on page 1of 19
UNIVERSITAS TARUMANAGARA
Fakultas Ekonomi dan Bisnis – Magister Akuntansi
EA73015 – Sistem Informasi dan Pengendalian Internal
Prepared by: Dr. Julisar., SE., Ak., MM., CA
Chapter 5 - Computer Fraud
SESSION 01
Accounting Information Systems
Fourteenth Edition, Global Edition
Chapter 5
Computer Fraud
Copyright © 2018 Pearson Education, Ltd. All Rights Reserved
Learning Objectives
• Explain the threats faced by modern information systems.
• Define fraud and describe both the different types of fraud
and the auditor’s responsibility to detect fraud.
• Discuss who perpetrates fraud and why it occurs, including
the pressures, opportunities, and rationalizations that are
present in most frauds.
• Define computer fraud and discuss the different computer
fraud classifications.
• Explain how to prevent and detect computer fraud and
abuse.
Copyright © 2018 Pearson Education, Ltd. Chapter 5: Computer Fraud Slide 1 - 5
Threats to AIS
• Natural and Political disasters
• Software errors and equipment malfunctions
• Unintentional acts
• Intentional acts
Copyright © 2018 Pearson Education, Ltd. Chapter 5: Computer Fraud Slide 1 - 6
Fraud
• Any means a person uses to gain an unfair advantage over another person;
includes:
– A false statement, representation, or disclosure
– A material fact, which induces a victim to act
– An intent to deceive
– Victim relied on the misrepresentation
– Injury or loss was suffered by the victim
Fraud is white-collar crime
Copyright © 2018 Pearson Education, Ltd. Chapter 5: Computer Fraud Slide 1 - 7
Two Categories of Fraud
• Misappropriation of assets
– Theft of company assets which can include physical assets (e.g., cash, inventory) and
digital assets (e.g., intellectual property such as protected trade secrets, customer data)
• Fraudulent financial reporting
– “cooking the books” (e.g., booking fictitious revenue, overstating assets, etc.)
Copyright © 2018 Pearson Education, Ltd. Chapter 5: Computer Fraud Slide 1 - 8
Auditor’s Responsibility
SAS No. 99 (AU-C Section 240) requires auditor’s to:
• Understand fraud
• Discuss the risks of material fraudulent misstatements
• Obtain information
• Identify, assess, and respond to risks
• Evaluate the results of their audit tests
• Document and Communicate findings
• Incorporate a technology focus
Copyright © 2018 Pearson Education, Ltd. Chapter 5: Computer Fraud Slide 1 - 9
Conditions for Fraud
These three conditions must be
present for fraud to occur:
• Pressure • Opportunity to:
– Employee – Commit
Financial – Conceal
Lifestyle – Convert to personal gain
Emotional
– Financial Statement • Rationalize
Financial – Justify behavior
Management – Attitude that rules don’t apply
Industry conditions – Lack personal integrity
Copyright © 2018 Pearson Education, Ltd. Chapter 5: Computer Fraud Slide 1 - 10
Fraud Triangle
Copyright © 2018 Pearson Education, Ltd. Chapter 5: Computer Fraud Slide 1 - 11
Computer Fraud
• If a computer is used to commit fraud it is called computer fraud.
• Computer fraud is classified as:
– Input
– Processor
– Computer instruction
– Data
– Output
Copyright © 2018 Pearson Education, Ltd. Chapter 5: Computer Fraud Slide 1 - 12
Preventing and Detecting Fraud
1. Make Fraud Less Likely to Occur
Organizational Systems
• Create a culture of integrity • Develop security policies to guide and design
• Adopt structure that minimizes fraud, create specific control procedures
governance (e.g., Board of Directors) • Implement change management controls and
• Assign authority for business objectives and project development acquisition controls
hold them accountable for achieving those
objectives, effective supervision and
monitoring of employees
• Communicate policies
Copyright © 2018 Pearson Education, Ltd. Chapter 5: Computer Fraud Slide 1 - 13
Preventing and Detecting Fraud
2. Make It Difficulty to Commit
Organizational Systems
• Develop strong internal controls • Restrict access
• Segregate accounting functions • System authentication
• Use properly designed forms • Implement computer controls over input,
• Require independent checks and processing, storage and output of data
reconciliations of data • Use encryption
• Fix software bugs and update systems
regularly
• Destroy hard drives when disposing of
computers
Copyright © 2018 Pearson Education, Ltd. Chapter 5: Computer Fraud Slide 1 - 14
Preventing and Detecting Fraud
3. Improve Detection
Organizational Systems
• Assess fraud risk • Audit trail of transactions through the system
• External and internal audits • Install fraud detection software
• Fraud hotline • Monitor system activities (user and error
logs, intrusion detection)
Copyright © 2018 Pearson Education, Ltd. Chapter 5: Computer Fraud Slide 1 - 15
Preventing and Detecting Fraud
4. Reduce Fraud Losses
Organizational Systems
• Insurance • Store backup copies of program and data
• Business continuity and disaster recovery files in secure, off-site location
plan • Monitor system activity
Copyright © 2018 Pearson Education, Ltd. Chapter 5: Computer Fraud Slide 1 - 16
Key Terms
• Sabotage • Pressure
• Cookie • Opportunity
• Fraud • Rationalization
• White-collar criminals • Lapping
• Corruption • Check kiting
• Investment fraud • Computer fraud
• Misappropriation of assets
• Fraudulent financial reporting
Copyright © 2018 Pearson Education, Ltd. Chapter 5: Computer Fraud Slide 1 - 17
Reference
• Chapter 05. Romney, Marshall B; Paul John Steinbart (2018). Accounting
Information Systems. 14th edition, Global Edition. ISBN: 978-1-292-22008-6
Fakultas Ekonomi dan Bisnis - Magister Akuntansi 18
End of Session 01
You might also like
- Accounting Information Systems: Fourteenth Edition, Global EditionDocument14 pagesAccounting Information Systems: Fourteenth Edition, Global EditionChelsea WulanNo ratings yet
- Chapter 5 - Computer FraudDocument15 pagesChapter 5 - Computer FraudLy Hoàng KhánhNo ratings yet
- Romney Ais13 PPT 05Document20 pagesRomney Ais13 PPT 05stanisNo ratings yet
- Computer FraudDocument15 pagesComputer FraudMāhmõūd ĀhmēdNo ratings yet
- Romney Ais13 PPT 05Document12 pagesRomney Ais13 PPT 05Meta Dwi MarettaNo ratings yet
- Prelim Ch5Document14 pagesPrelim Ch5Cathleen Drew TuazonNo ratings yet
- Accounting Information Systems: Fourteenth Edition, Global EditionDocument24 pagesAccounting Information Systems: Fourteenth Edition, Global EditionChelsea WulanNo ratings yet
- Sia P3Document14 pagesSia P3azis rahmanNo ratings yet
- Accounting Information Systems: Fourteenth EditionDocument25 pagesAccounting Information Systems: Fourteenth EditionNgoc NguyenNo ratings yet
- Chapter 5 Computer FraudDocument5 pagesChapter 5 Computer FraudChenyi GuNo ratings yet
- Accounting Information Systems: Fourteenth Edition, Global EditionDocument22 pagesAccounting Information Systems: Fourteenth Edition, Global EditionFriessy CallistaNo ratings yet
- Computer AIS - Chapter 3Document30 pagesComputer AIS - Chapter 3EmkeiNo ratings yet
- Strategies For Preventing A Breach and Assessing Your Cybersecurity Risk Management ProgramDocument33 pagesStrategies For Preventing A Breach and Assessing Your Cybersecurity Risk Management ProgramnopeNo ratings yet
- Module 3Document44 pagesModule 3Kenneth PimentelNo ratings yet
- Presentation1 Threats and ControlDocument60 pagesPresentation1 Threats and ControlcleophacerevivalNo ratings yet
- 05 Computer FraudDocument15 pages05 Computer Fraudashleykiki.keNo ratings yet
- Accounting Information System (Midterms)Document5 pagesAccounting Information System (Midterms)Luna KimNo ratings yet
- Ethics, Fraud Schemes, and Fraud DetectionDocument41 pagesEthics, Fraud Schemes, and Fraud DetectionIzza Mae Rivera KarimNo ratings yet
- Ethics, Fraud, and Internal Control: Accounting Information Systems, 5Document51 pagesEthics, Fraud, and Internal Control: Accounting Information Systems, 5amirNo ratings yet
- Securing Information SystemsDocument41 pagesSecuring Information SystemsSeemaNo ratings yet
- Ethics and FraudDocument28 pagesEthics and FraudSheena Pearl AlinsanganNo ratings yet
- AIS Chapter 3 Ethics 2Document7 pagesAIS Chapter 3 Ethics 2boa1315100% (1)
- ITE002 - AIS Topic 3 Ethics - Fraud - Internal ControlsDocument24 pagesITE002 - AIS Topic 3 Ethics - Fraud - Internal ControlsHayes HareNo ratings yet
- Ethics, Fraud & Internal ControlDocument46 pagesEthics, Fraud & Internal ControlgoeswidsNo ratings yet
- Fraud, Ethics & Internal Controls: Chapter 3 Cont' Week 4: Lecture # 2Document27 pagesFraud, Ethics & Internal Controls: Chapter 3 Cont' Week 4: Lecture # 2Chand DivneshNo ratings yet
- Romney Ais13 PPT 07Document21 pagesRomney Ais13 PPT 07Yose At The KahyanganNo ratings yet
- Case Study Operational RiskDocument27 pagesCase Study Operational RiskDikankatla SelahleNo ratings yet
- Ethics, Fraud, and Internal ControlDocument49 pagesEthics, Fraud, and Internal ControlJENNIENo ratings yet
- Ais - Ethics, Fraud, and Internal ControlDocument48 pagesAis - Ethics, Fraud, and Internal ControlMiriam LimosoNo ratings yet
- Hapter 5: © 2006 Prentice Hall Business Publishing Accounting Information Systems, 10/e Romney/SteinbartDocument169 pagesHapter 5: © 2006 Prentice Hall Business Publishing Accounting Information Systems, 10/e Romney/SteinbartNia Resky PutraNo ratings yet
- Ethics, Fraud, and Internal ControlDocument49 pagesEthics, Fraud, and Internal ControlAzizah Syarif100% (3)
- Cyber SecurityDocument84 pagesCyber SecurityAnjali MahajanNo ratings yet
- AEAIS Module 3 4 Fraud Computer Fraud and Abuse TechniquesDocument36 pagesAEAIS Module 3 4 Fraud Computer Fraud and Abuse TechniquesFiona MiralpesNo ratings yet
- Share System Security 1Document30 pagesShare System Security 1Md SajidNo ratings yet
- بلا عنوانDocument22 pagesبلا عنوانnermeen alaaeldeinMNo ratings yet
- Ethics, Fraud and Internal Controls ExplainedDocument21 pagesEthics, Fraud and Internal Controls ExplainedAngel YbanezNo ratings yet
- 01-An Introduction To Strategic IT Security and Risk ManagementDocument21 pages01-An Introduction To Strategic IT Security and Risk ManagementMhd Rahul FahrezaNo ratings yet
- Control and Accounting Information SystemsDocument63 pagesControl and Accounting Information SystemsNurulHidayahNo ratings yet
- AIS Chapter 4Document48 pagesAIS Chapter 4Ashenafi ZelekeNo ratings yet
- Ethics, Fraud, and Internal ControlDocument50 pagesEthics, Fraud, and Internal ControlontykerlsNo ratings yet
- Vendor Risk Management 4-20-2018 GuidepointDocument18 pagesVendor Risk Management 4-20-2018 GuidepointGil Quiroz RomanoNo ratings yet
- Lecture 8 - Chapter 8Document39 pagesLecture 8 - Chapter 8Wei NingNo ratings yet
- Computer FraudDocument15 pagesComputer FraudrresaNo ratings yet
- Why Should We Be Concerned About Ethics in The Business World?Document5 pagesWhy Should We Be Concerned About Ethics in The Business World?Orange BunsieNo ratings yet
- Lecture 02 - The Need For Security-2Document48 pagesLecture 02 - The Need For Security-2Umair AmjadNo ratings yet
- Financial Accounting: Internal Control, Cash, and ReceivablesDocument75 pagesFinancial Accounting: Internal Control, Cash, and ReceivablesMaggie ShekNo ratings yet
- Management Information Systems: Managing The Digital Firm: Fifteenth EditionDocument45 pagesManagement Information Systems: Managing The Digital Firm: Fifteenth EditionceliaNo ratings yet
- Principles of Information Security, Fifth Edition: Risk ManagementDocument67 pagesPrinciples of Information Security, Fifth Edition: Risk ManagementCharlito MikolliNo ratings yet
- Hapter 5: © 2008 Prentice Hall Business Publishing Accounting Information Systems, 11/e Romney/SteinbartDocument169 pagesHapter 5: © 2008 Prentice Hall Business Publishing Accounting Information Systems, 11/e Romney/SteinbartUmar Muktar IsduriNo ratings yet
- AIS Chapter 4 Fraud and AbusesDocument73 pagesAIS Chapter 4 Fraud and AbusesKassawmar DesalegnNo ratings yet
- Control and Accounting Information SystemDocument8 pagesControl and Accounting Information SystemAs17 As17No ratings yet
- Ethics, Fraud and Internal ControlDocument59 pagesEthics, Fraud and Internal ControlDarleen Louise PortesNo ratings yet
- Effective Risk Reporting: Sunder Krishnan Chief Risk Officer Reliance Life Insurance CompanyDocument33 pagesEffective Risk Reporting: Sunder Krishnan Chief Risk Officer Reliance Life Insurance CompanyRodrigo PadovanNo ratings yet
- 01-An Introduction To Strategic IT Security and Risk ManagementDocument21 pages01-An Introduction To Strategic IT Security and Risk ManagementAninda MHNo ratings yet
- Part II. Control and Audit of AISDocument29 pagesPart II. Control and Audit of AISnigusNo ratings yet
- Chapter 8 - Part 2Document16 pagesChapter 8 - Part 2Saeed KhawamNo ratings yet
- Module 03 Accounting and Information SystemsDocument8 pagesModule 03 Accounting and Information SystemsYolly DiazNo ratings yet
- Chapter 5 Computer Fraud and AbuseDocument169 pagesChapter 5 Computer Fraud and Abuseislamelshahat100% (1)
- Chapter 23: Modification To The Auditor'S ReportDocument9 pagesChapter 23: Modification To The Auditor'S ReportBella AngelinaNo ratings yet
- Kondisi Ekonomi P1 E (R) 1 2 3 4 5 6 7 R % R % R - E (R) R - E (R)Document10 pagesKondisi Ekonomi P1 E (R) 1 2 3 4 5 6 7 R % R % R - E (R) R - E (R)Bella AngelinaNo ratings yet
- Derivatives and Risk ManagementDocument13 pagesDerivatives and Risk ManagementDedy ArmanNo ratings yet
- Universitas Tarumanagara: Fakultas Ekonomi Dan Bisnis - Magister AkuntansiDocument22 pagesUniversitas Tarumanagara: Fakultas Ekonomi Dan Bisnis - Magister AkuntansiBella AngelinaNo ratings yet
- Chp5 AISDocument35 pagesChp5 AISjujubajujuNo ratings yet
- Banning Cosmetic Animal TestingDocument4 pagesBanning Cosmetic Animal TestingMimi SyahidaNo ratings yet
- Investigation Report On Revaport Theft AttemptDocument3 pagesInvestigation Report On Revaport Theft AttemptElamaran PerumalNo ratings yet
- DR Kaleem Khan Assistant Professor JNMCH, Amu, AligarhDocument44 pagesDR Kaleem Khan Assistant Professor JNMCH, Amu, AligarhNashif RayhanNo ratings yet
- 10.25.21 52B-1 Re Emergency App For Leave To Compel The Gov't To File All 5K DocumentsDocument22 pages10.25.21 52B-1 Re Emergency App For Leave To Compel The Gov't To File All 5K DocumentsThomas WareNo ratings yet
- The Science of Lie Detection: HistoryDocument7 pagesThe Science of Lie Detection: HistoryLawrence Rafael Lardizabal CarmonaNo ratings yet
- Cancio vs. IsipDocument4 pagesCancio vs. IsipWILHELMINA CUYUGANNo ratings yet
- Drug Possession Case in CagayanDocument27 pagesDrug Possession Case in CagayanLance Adrian TumanguilNo ratings yet
- Hawthorne PDFDocument22 pagesHawthorne PDFchasidey_harrisNo ratings yet
- Aug.15 Fort St. James Court ListDocument23 pagesAug.15 Fort St. James Court ListOminecaEditorNo ratings yet
- Introducing To Network SecurityDocument10 pagesIntroducing To Network SecuritycursantcataNo ratings yet
- Crim1 WK1 02lessonproper 1Document7 pagesCrim1 WK1 02lessonproper 1Ella Jordan LoterteNo ratings yet
- Seares vs. Gonzales AlzateDocument2 pagesSeares vs. Gonzales AlzateCherry Bepitel100% (1)
- AFPSAT Reviewer General Aptitude Battery TestDocument58 pagesAFPSAT Reviewer General Aptitude Battery TestLeo Paran Moico Jr.No ratings yet
- Evacuation, Hibernation, and RelocationDocument19 pagesEvacuation, Hibernation, and RelocationavsecNo ratings yet
- Restrictive Rules of Engagement for Military Operations in Urban AreasDocument38 pagesRestrictive Rules of Engagement for Military Operations in Urban AreasЈован АдамовNo ratings yet
- 3rd CaseDocument11 pages3rd CaseAshley Kate PatalinjugNo ratings yet
- Session 6 (Persons Criminally Liable For Felonies)Document14 pagesSession 6 (Persons Criminally Liable For Felonies)Noel Ephraim AntiguaNo ratings yet
- Fundamentals of Criminal Investigation Part 1Document2 pagesFundamentals of Criminal Investigation Part 1johnpaulacostaNo ratings yet
- Online Scams and Frauds During Covid 19Document17 pagesOnline Scams and Frauds During Covid 19RaghavNo ratings yet
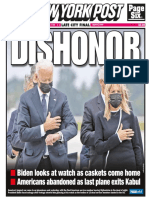
- New York Post 31-8Document116 pagesNew York Post 31-8Deepak MNo ratings yet
- White Collar Crime: - An Insight Into Its Current StateDocument36 pagesWhite Collar Crime: - An Insight Into Its Current StateNicole RichardsonNo ratings yet
- FOCGB2 AK Utest VG 8 PDFDocument3 pagesFOCGB2 AK Utest VG 8 PDFSheila Mignolet0% (1)
- Court grants interim compensation in POCSO caseDocument6 pagesCourt grants interim compensation in POCSO caseDrsika100% (1)
- Supreme CourtDocument7 pagesSupreme CourtJennica Gyrl G. DelfinNo ratings yet
- UN Global Compact Guide For Anti-Corruption Risk AssessmentDocument74 pagesUN Global Compact Guide For Anti-Corruption Risk AssessmentPeterRNWNo ratings yet
- San Mateo Daily Journal 03-13-19 EditionDocument28 pagesSan Mateo Daily Journal 03-13-19 EditionSan Mateo Daily JournalNo ratings yet
- Valmonte vs. de Villa GR No. 83988Document7 pagesValmonte vs. de Villa GR No. 83988Raymond BulosNo ratings yet
- Punitive Articles of The UCMJDocument2 pagesPunitive Articles of The UCMJdevin_a_winklosky_milNo ratings yet
- 473 2009119 10331Document182 pages473 2009119 10331Janeen S HolderNo ratings yet
- Goldenshtein OpinionDocument45 pagesGoldenshtein OpinionBrian WassomNo ratings yet