Professional Documents
Culture Documents
Rizalie Evangelista-Bsit3f-It-Ias01
Uploaded by
Nhiel Patrick EvangelistaOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Rizalie Evangelista-Bsit3f-It-Ias01
Uploaded by
Nhiel Patrick EvangelistaCopyright:
Available Formats
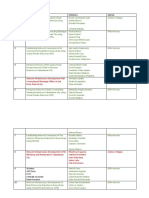
Directions: Write the letter of the correct answer on the space provided before each
item.
____A_____ 1. What do you call the unsolicited messenger you found on your
Facebook messenger?
a.Spam b. Spim
c.Junk d.Archive
____C_____ 2. The following are the ways to prevent malware EXCEPT for
what?
a.Conduct educating sessions
b.Utilize pwerful username and passwords
c.Sell them your downloaded anti-malware programs
d.Scan your drives regularly and put malicious files on quarantine
_____C____ 3. It is a type of malware that masquerades as an essential
application,
a.Trojan Horse b.Worm
c.Virus d.Rootkit
_____A____ 4. It refers to a suggested activity that may help to assure the
safety of your assets.
a.Countermeasure b.Scanning
c.Quarantine d.Anti-malware
_____A____ 5. We can say that a file is malicious if it _________,
a.Causes damage b.Escalates security privileges
c.Divulges private data d.Back-ups important files
_____C____ 6. It refers to the data that one needs to enable to maximize web-
browsing capability.
a.Hoax b.Worm c.Cookies d.Incognito
_____C____ 7. This refers to a threat when someone exploits the confidential
information into organization or people for intention of attacking the asset’s owner.
a.Death Threat b.Disclosure Threat
c.Unauthorized Threat d.Hijacking
____D_____ 8. The following are “Security Breaches”EXCEPTfor what?
a.Denial of Service Attack(DoS) b.Distributed denial-of-service (DDoS)
c.Wiretapping d.Computer Formatting
____A_____ 9. The following are the stuff that Information Security is trying
to protect EXCEPTfor what?
a. Attitudes b.Bank Accounts
c. Registration Details d. LAN and WAN Networks
_____B____ 10. Assets, such as Crown Jewels
should be kept in________.
a.Treasure Box b.Vault
c.Secured database d. Fault-free bodega
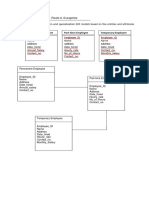
POST-TEST. Quiz 2.2
Directions: Tell whether the following is an asset, threat, risk, vulnerability, or
countermeasure.
______Countermessure______ 1. The manager told a client the account balance
of his/her rival.
_____ Countermessure _____ 2. The student wrote his home address on the
registration form.
_______Risk_________3. The Network Engineer left the server room open while
he/she went for a snack.
____ Countermessure _____ 4. The anti-malware software runs scan every
three hours.
_______Threat_________5. The hacker of your rival company found out that your
login credential is your birthday.
________Threat________6. You found out that your computer is infected and you
run the back-up quickly.
________Asset________7. You answered 150,00.00 on the survey of your family’s
annual income. ________________8. The IT Team advises their online bankers not
to share their One-Time Passwords (OTP)
________Vulnerability________9. Your anti-malware application expired and you
did not purchase a good one to secure your files.
________Risk________10. The manager forgot to lock his/her computer because of
the tension happened in the office.
You might also like
- Chapter 1-4 Cybersecurity Review QuestionsDocument28 pagesChapter 1-4 Cybersecurity Review QuestionsDerrick S Gabbard60% (10)
- CEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021From EverandCEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021No ratings yet
- Is Awareness Quiz Answers FinalDocument36 pagesIs Awareness Quiz Answers FinalAman RanaNo ratings yet
- Management of Information Security 5th Edition Whitman Test BankDocument9 pagesManagement of Information Security 5th Edition Whitman Test BankJonathanWoodfkwpx100% (18)
- 10 Types of Computer Viruses ExplainedDocument3 pages10 Types of Computer Viruses ExplainedTAI LONG100% (1)
- Manual For Dr. X CourseDocument4 pagesManual For Dr. X CourseSaad WakeelNo ratings yet
- Build A Small NetworkDocument58 pagesBuild A Small Networkthanh vienNo ratings yet
- Introductio in Chaldaicam Linguam, Syriacam, Atque Armenicam and Decem Alias LinguaDocument462 pagesIntroductio in Chaldaicam Linguam, Syriacam, Atque Armenicam and Decem Alias LinguaIstoriskiBlog100% (5)
- CAE Writing Exam TasksDocument3 pagesCAE Writing Exam TasksCharlie ChapNo ratings yet
- Sic Final (E-Next - In) (E-Next - In)Document56 pagesSic Final (E-Next - In) (E-Next - In)Prathamesh BhosaleNo ratings yet
- 1st Quarter Exam in Empowerment Technologies Sy 2022 2023Document4 pages1st Quarter Exam in Empowerment Technologies Sy 2022 2023JEROME CACHONo ratings yet
- Unit of Competence: Module Title: TTLM Code: Name: - DateDocument3 pagesUnit of Competence: Module Title: TTLM Code: Name: - DateKefelegn GulintNo ratings yet
- Question and AnswerDocument6 pagesQuestion and Answereliza marie luisNo ratings yet
- Computer Security Principles and Practice Global 3rd Edition Stallings Test BankDocument6 pagesComputer Security Principles and Practice Global 3rd Edition Stallings Test Bankrowanbridgetuls3100% (23)
- Full download Test Bank For Computer Security Principles And Practice 3E By Stallings 9780133773927 pdfDocument30 pagesFull download Test Bank For Computer Security Principles And Practice 3E By Stallings 9780133773927 pdfkimberly.levy818100% (9)
- Finals Exam in Information Assurance and SecurityDocument3 pagesFinals Exam in Information Assurance and SecurityJovanna Lagradilla OcampoNo ratings yet
- Siber Güvenlik SorularDocument14 pagesSiber Güvenlik SorularAnonymous eUJXtKNo ratings yet
- Cyber Security Training ContentDocument4 pagesCyber Security Training ContentPrashant ZambreNo ratings yet
- First Quarter E - Tech 2019-2020Document5 pagesFirst Quarter E - Tech 2019-2020Angel CabreraNo ratings yet
- Security MidtermDocument11 pagesSecurity Midtermjunkmailsux88No ratings yet
- Malware Types and Vulnerabilities ExplainedDocument3 pagesMalware Types and Vulnerabilities ExplainedlloysarahNo ratings yet
- Empowerment of Technology Test Questioner Grade 12 1st SemDocument9 pagesEmpowerment of Technology Test Questioner Grade 12 1st SemMary Jean Farillon100% (1)
- New Perspectives Computer Concepts Enhanced Comprehensive 2016 19th Edition Parsons Test BankDocument17 pagesNew Perspectives Computer Concepts Enhanced Comprehensive 2016 19th Edition Parsons Test Bankdelwynluongkam74z100% (21)
- DATA SECURITY WorksheetDocument3 pagesDATA SECURITY WorksheetAnahi BeltranNo ratings yet
- Annunciation College of Bacon Sorsogon Unit, Inc: I. IdentificationDocument8 pagesAnnunciation College of Bacon Sorsogon Unit, Inc: I. IdentificationRina DinNo ratings yet
- IT Security Chapter 1 SummaryDocument2 pagesIT Security Chapter 1 SummaryNaib BilloNo ratings yet
- Lino P. Bernardo National High SchoolDocument2 pagesLino P. Bernardo National High Schoolma'am Edlyn Faith PadillaNo ratings yet
- Empowerment Technologies Summative AssessmentDocument2 pagesEmpowerment Technologies Summative Assessmentjacqueline fernandezNo ratings yet
- Midterm Test in Empowerment TechnologiesDocument5 pagesMidterm Test in Empowerment TechnologiesTristan PereyNo ratings yet
- AbiotiDocument3 pagesAbiotiEndale GirumeNo ratings yet
- QUIZ 2 Empowerment TechnologyDocument1 pageQUIZ 2 Empowerment TechnologyKlarryze Jenel B. ManioNo ratings yet
- Cybercrime and Environmental Laws and Protection1-10Document2 pagesCybercrime and Environmental Laws and Protection1-10Kobi FækNo ratings yet
- I MID Objective QuestionsDocument6 pagesI MID Objective QuestionsNagur BashaNo ratings yet
- 4.1 Introductory Activity: Prepared By: Noted: Jose C. Lita JR Celma N. Miraran SHS-Teacher 1 School Principal IIDocument1 page4.1 Introductory Activity: Prepared By: Noted: Jose C. Lita JR Celma N. Miraran SHS-Teacher 1 School Principal IIJose C. Lita JrNo ratings yet
- Ebook Computer Security Principles and Practice 4Th Edition Stallings Test Bank Full Chapter PDFDocument28 pagesEbook Computer Security Principles and Practice 4Th Edition Stallings Test Bank Full Chapter PDFjoanneesparzagwjxmyqont100% (10)
- PRE-TEST On EmptechDocument2 pagesPRE-TEST On EmptechAngela D. De LeonNo ratings yet
- Protecting Information Resources Chapter 5 Multiple Choice QuestionsDocument4 pagesProtecting Information Resources Chapter 5 Multiple Choice QuestionsruvenNo ratings yet
- 5th Summative TestDocument2 pages5th Summative TestEbb Tenebroso JudillaNo ratings yet
- Hide Answer Workspace: A. Phishing B. Bulling C. Stalking D. Identity TheftDocument23 pagesHide Answer Workspace: A. Phishing B. Bulling C. Stalking D. Identity TheftDr ManiNo ratings yet
- Grade 11 ICT - Class TaskDocument5 pagesGrade 11 ICT - Class TaskCraigNo ratings yet
- mcq-7Document8 pagesmcq-7Wendi ZinabuNo ratings yet
- CSS10 Q3. Week 1Document6 pagesCSS10 Q3. Week 1CESARIO BOADONo ratings yet
- ICT Grade 10 Test PaperDocument6 pagesICT Grade 10 Test PaperVinceM.Gabejan67% (6)
- Tle Css10 Week8Document8 pagesTle Css10 Week8Enelra Nat VilNo ratings yet
- Access and Use Internet Final ExamDocument2 pagesAccess and Use Internet Final ExamIsrael Kifle100% (1)
- MCQ Cyber SecurityDocument29 pagesMCQ Cyber SecurityNamrataNo ratings yet
- POST - Test in E-TechDocument2 pagesPOST - Test in E-TechCarolyn FaburadaNo ratings yet
- IctDocument12 pagesIctkj meNo ratings yet
- تجميعات الاسئلة السايبرDocument80 pagesتجميعات الاسئلة السايبرOMAR ALKHUDAYDINo ratings yet
- CSS-10-Q3-W4 - Anti Virus Software-Edited Final For Printing No Answer Key FinalDocument6 pagesCSS-10-Q3-W4 - Anti Virus Software-Edited Final For Printing No Answer Key FinalGrace Lazala AlvarezNo ratings yet
- Quiz Empowe TechDocument2 pagesQuiz Empowe Techmanilyn100% (1)
- DCS Unit 6 MCQs PDFDocument146 pagesDCS Unit 6 MCQs PDFSwapnil ShindeNo ratings yet
- Test IDocument2 pagesTest IAnn Matinong Dela CruzNo ratings yet
- Chapter 01 Introduction To The Management of Information SecurityDocument12 pagesChapter 01 Introduction To The Management of Information Securityغسان الشليف100% (1)
- Security in ComputingDocument3 pagesSecurity in ComputingRtr.Priyanka Adak RC Sathaye College, MumbaiNo ratings yet
- Computer 6 I - Read Each Statement Carefully and Identify What Is Being AskedDocument2 pagesComputer 6 I - Read Each Statement Carefully and Identify What Is Being AskedDiana Nara Gail GaytosNo ratings yet
- Css 4th Quarter Week 1Document6 pagesCss 4th Quarter Week 1Hera AsuncionNo ratings yet
- Css 4th Quarter Week 1Document6 pagesCss 4th Quarter Week 1Hera AsuncionNo ratings yet
- TestYourKnowledgeNow Chapter 08Document6 pagesTestYourKnowledgeNow Chapter 08Thien KimNo ratings yet
- App Dev and Emerging TecDocument4 pagesApp Dev and Emerging TecGUMARANG CHARYANNNo ratings yet
- TD2 Lesson 1Document4 pagesTD2 Lesson 1MODA ZINANo ratings yet
- Blind Spot: Smartphone and Computer Personal Security GuideFrom EverandBlind Spot: Smartphone and Computer Personal Security GuideRating: 3 out of 5 stars3/5 (1)
- Your System's Sweetspots: CEO's Advice on Basic Cyber Security: CEO's Advice on Computer ScienceFrom EverandYour System's Sweetspots: CEO's Advice on Basic Cyber Security: CEO's Advice on Computer ScienceNo ratings yet
- Lingap Sa Barangay ProgramDocument10 pagesLingap Sa Barangay ProgramNhiel Patrick EvangelistaNo ratings yet
- Asian Development Bank: Impact of Rural Roads ON Poverty Reduction: A Case Study-Based AnalysisDocument141 pagesAsian Development Bank: Impact of Rural Roads ON Poverty Reduction: A Case Study-Based AnalysisNhiel Patrick EvangelistaNo ratings yet
- Case Study Maron BSIT 3KDocument22 pagesCase Study Maron BSIT 3KNhiel Patrick EvangelistaNo ratings yet
- Literature Review and Analysis Related To Municipal Government ConsolidationDocument52 pagesLiterature Review and Analysis Related To Municipal Government ConsolidationNhiel Patrick EvangelistaNo ratings yet
- AshtonDocument1 pageAshtonNhiel Patrick EvangelistaNo ratings yet
- Group No. Concept/Title Members Adviser 1Document2 pagesGroup No. Concept/Title Members Adviser 1Nhiel Patrick EvangelistaNo ratings yet
- Case Study Maron BSIT 3KDocument22 pagesCase Study Maron BSIT 3KNhiel Patrick EvangelistaNo ratings yet
- NEUST CICT students request network project adviserDocument1 pageNEUST CICT students request network project adviserNhiel Patrick EvangelistaNo ratings yet
- Network Infrastructure Development Plan Connecting All Barangay Offices in Santa Rosa Nueva EcijaDocument6 pagesNetwork Infrastructure Development Plan Connecting All Barangay Offices in Santa Rosa Nueva EcijaNhiel Patrick EvangelistaNo ratings yet
- Abstract of QuotationDocument1 pageAbstract of QuotationNhiel Patrick EvangelistaNo ratings yet
- Assignment No.3 - RIZALIE A. EVANGELISTADocument3 pagesAssignment No.3 - RIZALIE A. EVANGELISTANhiel Patrick EvangelistaNo ratings yet
- Area Triangle Computation FormDocument6 pagesArea Triangle Computation FormNhiel Patrick EvangelistaNo ratings yet
- Purchase Requisition (Local) : Luzon I MarketingDocument1 pagePurchase Requisition (Local) : Luzon I MarketingNhiel Patrick EvangelistaNo ratings yet
- Introduction To TRICONDocument11 pagesIntroduction To TRICONneoamnNo ratings yet
- Advanced Voting Management System Using PHPMySQLDocument2 pagesAdvanced Voting Management System Using PHPMySQLsaidu musaNo ratings yet
- Call It Spring - Call It Spring USDocument2 pagesCall It Spring - Call It Spring USCarlos De LeonNo ratings yet
- Access Tools and Services To Open AccessDocument17 pagesAccess Tools and Services To Open AccessAdrianaRodriguesNo ratings yet
- Monthly Marketing Reporting TemplateDocument20 pagesMonthly Marketing Reporting TemplateMukul AroraNo ratings yet
- Manual Telnet Client - Coletor de DadosDocument258 pagesManual Telnet Client - Coletor de DadosmiguelhfsNo ratings yet
- Intro to PeopleSoft QueryDocument127 pagesIntro to PeopleSoft QuerynagasankarNo ratings yet
- Syllabus Science PDFDocument207 pagesSyllabus Science PDFPriyanshu VermaNo ratings yet
- 25 Salient Features From New Foreign Trade Policy To Push Up India's Exports - The Economic TimesDocument4 pages25 Salient Features From New Foreign Trade Policy To Push Up India's Exports - The Economic TimesvatsadbgNo ratings yet
- Ocean Digital wr-23dDocument38 pagesOcean Digital wr-23djewsNo ratings yet
- Marketing-Customer Driven Marketing Strategy-TMDocument7 pagesMarketing-Customer Driven Marketing Strategy-TMSaha Norrazief Abdul HakimNo ratings yet
- Stratosphere WriteupDocument7 pagesStratosphere WriteupshivNo ratings yet
- Farewell Speech on RetirementDocument7 pagesFarewell Speech on Retirementdeepti_singh_ntlNo ratings yet
- 363121343Document1 page363121343MericatNo ratings yet
- BVD 2407 GBDocument5 pagesBVD 2407 GBSaeed Ahmad ChandioNo ratings yet
- 2 1 2 10+Lab+-+Building+a+Switched+Network+with+Redundant+LinksDocument9 pages2 1 2 10+Lab+-+Building+a+Switched+Network+with+Redundant+LinkspeiyiNo ratings yet
- Tamil Nadu Public Service CommissionDocument34 pagesTamil Nadu Public Service Commissionv.lakshmiNo ratings yet
- Report 1Document28 pagesReport 1zeeshan sohailNo ratings yet
- Charan - Cyber SecurityDocument7 pagesCharan - Cyber SecuritySatish Kumar SinhaNo ratings yet
- Chapter 3Document22 pagesChapter 3dennis tanNo ratings yet
- WDM Security GuidelinesDocument27 pagesWDM Security GuidelineshgergesNo ratings yet
- Citibank's EPay MinDocument2 pagesCitibank's EPay MinDevesh KumarNo ratings yet
- SQL Trace Data (Paper)Document15 pagesSQL Trace Data (Paper)Krishna Kishore ReddyNo ratings yet
- HTML - DevdocsDocument4 pagesHTML - DevdocsRenato MouraNo ratings yet
- Industrial Training ReportDocument28 pagesIndustrial Training ReportIdowu OjoNo ratings yet
- Web Designer Portfolio by SlidesgoDocument26 pagesWeb Designer Portfolio by SlidesgoBetül SevindiNo ratings yet