Professional Documents
Culture Documents
Information Systems Audit Program: Aprina Nugrahesthy Sulistya Hapsari Aprina@uksw - Edu
Uploaded by
maulana afiansyah0 ratings0% found this document useful (0 votes)
10 views8 pagesOriginal Title
Program Audit
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
10 views8 pagesInformation Systems Audit Program: Aprina Nugrahesthy Sulistya Hapsari Aprina@uksw - Edu
Uploaded by
maulana afiansyahCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 8
INFORMATION
SYSTEMS AUDIT
PROGRAM
Aprina Nugrahesthy Sulistya Hapsari
aprina@uksw.edu
Audit Program
Audit programs are:
• Essentially checklists of the various tests
that auditors must perform within the scope
of their audits
• To determine whether key controls intended
to mitigate significant risks are functioning
as designed,
• Based on the test results of the test
performed:
→ determine the adequacy of the controls
over a particular process
Audit Programs are necessary to perform an effective and
efficient audit
BENEFITS OF AUDIT
PROGRAM
• Assist audit management in resource
planning
• Promote consistency in tests performed on
audits of the same process from one cycle
to the next
→ the previous audit programs can be
employed during the current audit
• Promote consistency in tests performed on
controls that are common to all process
→ standard audit program
INFORMATION SYSTEMS AUDIT
PROGRAM
→ Designed to address the
primary risks of virtually all
computing systems
IS controls in the audit program:
➢ Environmental Controls
➢ Physical Security Controls
➢ Logical Security Controls
➢ IS Operating Controls
Environmental Controls
→ are more general than physical and logical
security controls
• Dictate the extent to which physical and logical
security controls are deployed
• Include:
– IS security policies, standards, and guidelines;
– the reporting structure within the IS processing
environment (including computer operations and
programming);
– the financial condition of service organizations and
vendors, vendor software license, maintenance, and
support agreements and warranties;
– the status of computing systems policies and procedures
placed in operation at service organizations (if
applicable)
Physical Security Controls
• Pertain to the protection over:
– Computer Hardware;
– Components;
– Facilities within which they reside
(…Although somewhat of an environmental
control, insurance coverage over computing
system hardware and the costs to re-create or
replace lost or damaged software programs and
data…)
Logical Security Controls
→ are those that have been deployed
within the operating system and
applications to help prevent unauthorized
access and accidental or intentional
destruction of programs and data
• Include:
– System access capabilities of users:
– System access profiles and parameters;
– Logging mechanisms
IS Operating Controls
→ designed to help ensure that the
information system is operating efficiently
and effectively
• Include:
– The timely and accurate completion of
production jobs;
– Distribution of output media;
– Performance of backup and recovery
procedures;
– Performance of maintenance procedures;
– Documentation and resolution of system
problems;
– Monitoring of CPU and data storage capacity
utilization
You might also like
- The Beginner's Guide To Microsoft Excel PDFDocument23 pagesThe Beginner's Guide To Microsoft Excel PDFNabeel Gonzales Akhtar100% (1)
- Internal Control in A CIS EnvironmentDocument25 pagesInternal Control in A CIS Environmentjunalyn150% (1)
- Data Security in Cloud ComputingDocument324 pagesData Security in Cloud Computingprince2venkatNo ratings yet
- 07 - Cisa It AuditDocument54 pages07 - Cisa It AuditHamza NaeemNo ratings yet
- Smartdrive Premier System: T E C H N I C A L C A T A L O GDocument52 pagesSmartdrive Premier System: T E C H N I C A L C A T A L O GKrzysztof Bręk100% (1)
- 10.2 Using CaattsDocument38 pages10.2 Using CaattsPauline MercadoNo ratings yet
- IT Security Audit: Prepared by Mbabazi SylviaDocument36 pagesIT Security Audit: Prepared by Mbabazi SylviaMicheal BixNo ratings yet
- ISO 9001 General AwarenessDocument24 pagesISO 9001 General AwarenesspvendaraNo ratings yet
- CyberArk - PrivilegeCloud - Implementation DocumentDocument45 pagesCyberArk - PrivilegeCloud - Implementation DocumentramuNo ratings yet
- 01) MTU Hybrid Solution - Marine For Distributor - 01062017Document32 pages01) MTU Hybrid Solution - Marine For Distributor - 01062017priyoNo ratings yet
- NS - 12 Incident ResponseDocument24 pagesNS - 12 Incident ResponseYogaRizwanNo ratings yet
- IT Controls: Northern Arizona University Compliance, Controls & Business Services December 2011Document35 pagesIT Controls: Northern Arizona University Compliance, Controls & Business Services December 2011Sefi RifkianaNo ratings yet
- Information Systems Auditing: The IS Audit Testing ProcessFrom EverandInformation Systems Auditing: The IS Audit Testing ProcessRating: 1 out of 5 stars1/5 (1)
- Auditing Operating Systems Networks: Security Part 1: andDocument24 pagesAuditing Operating Systems Networks: Security Part 1: andAmy RillorazaNo ratings yet
- Ch03-Security Part 1. Auditing Operating Systems and NetworksDocument42 pagesCh03-Security Part 1. Auditing Operating Systems and NetworksAlfin Abdullah100% (1)
- Free PLC Tutorial PDFDocument2 pagesFree PLC Tutorial PDFLance0% (1)
- Vulnerability Management Policy and ProceduresDocument18 pagesVulnerability Management Policy and Procedureshari bhandari50% (4)
- Software Testing Interview Questions You'll Most Likely Be AskedFrom EverandSoftware Testing Interview Questions You'll Most Likely Be AskedNo ratings yet
- 3.software Quality AssuranceDocument22 pages3.software Quality AssurancearunlaldsNo ratings yet
- Auditing Application ControlDocument18 pagesAuditing Application ControlSrie ZanraNo ratings yet
- Kelompok 5 - Presentation Chapter 9 & 10Document31 pagesKelompok 5 - Presentation Chapter 9 & 10derrick leeNo ratings yet
- Structured System Analysis and Design (BIT321) System Security and AuditDocument18 pagesStructured System Analysis and Design (BIT321) System Security and AuditGlobal AccessNo ratings yet
- Information System AuditDocument45 pagesInformation System AuditabcdNo ratings yet
- Managing Digital Firms: Information Security: Unit 4Document37 pagesManaging Digital Firms: Information Security: Unit 4Janavi KalekarNo ratings yet
- Oracle Health Check Comprehensive: Oracle ApplicationsDocument7 pagesOracle Health Check Comprehensive: Oracle ApplicationsvijayakumarjNo ratings yet
- Systems Architecture, Documentation and TestingDocument24 pagesSystems Architecture, Documentation and Testingaddokenneth58No ratings yet
- Cisa - 4th Chapter - IT Service Delivery and SupportDocument4 pagesCisa - 4th Chapter - IT Service Delivery and SupportfaizthemeNo ratings yet
- System Analysis Design Chapter 8Document41 pagesSystem Analysis Design Chapter 8Siva BalanNo ratings yet
- Cyber Security U3Document90 pagesCyber Security U3Mr. RAVI KUMAR INo ratings yet
- Establishing A Management Framework For Security and ControlDocument12 pagesEstablishing A Management Framework For Security and Controlgerald paduaNo ratings yet
- Auditing in Computer Environment in WordDocument2 pagesAuditing in Computer Environment in WordLotte CabreraNo ratings yet
- Topic 10 - The Impact of IT On Audit ProcessDocument34 pagesTopic 10 - The Impact of IT On Audit Process2022930579No ratings yet
- Accounting Information Systems: Moscove, Simkin & BagranoffDocument37 pagesAccounting Information Systems: Moscove, Simkin & BagranoffDaiannaNo ratings yet
- Internal Control2Document31 pagesInternal Control2hangbg2k3No ratings yet
- Lecture 12 - Auditing Procedures To Analyze IS For Improving Business ResilienceDocument47 pagesLecture 12 - Auditing Procedures To Analyze IS For Improving Business Resilienceshujaa mbawalaNo ratings yet
- Auditing in An IT EnvironmentDocument13 pagesAuditing in An IT Environmentbangtan ' liciousNo ratings yet
- Unit 5Document16 pagesUnit 5Bharti PatelNo ratings yet
- Cis 2Document10 pagesCis 2Jyle Mareinette ManiagoNo ratings yet
- CisDocument4 pagesCisJyle Mareinette ManiagoNo ratings yet
- Lec-5 - System Analysis (DZI) System Testing and Quality AssuranceDocument14 pagesLec-5 - System Analysis (DZI) System Testing and Quality AssuranceCreatics HubNo ratings yet
- Lo3 Riskmanagement MCQDocument31 pagesLo3 Riskmanagement MCQisraaNo ratings yet
- Nour Alkharraz Scope of WorkDocument5 pagesNour Alkharraz Scope of WorkNourNo ratings yet
- Nour Eddin Al-Kharraz IT Presales / Cloud & On-Premises Systems AdministratorDocument5 pagesNour Eddin Al-Kharraz IT Presales / Cloud & On-Premises Systems AdministratorNourNo ratings yet
- Module 6Document30 pagesModule 6AshwinSivasankar VenkatesanNo ratings yet
- Auditing in CIS Environment - Auditing Operating Systems and Networks (Final)Document44 pagesAuditing in CIS Environment - Auditing Operating Systems and Networks (Final)Luisito100% (2)
- SESlides 2Document26 pagesSESlides 2tayyabson06No ratings yet
- 21 - WK 9 Slides IMPACT OF IT ON INTERNAL AUDITING AND RISK WEEK 9Document20 pages21 - WK 9 Slides IMPACT OF IT ON INTERNAL AUDITING AND RISK WEEK 9Camilo ToroNo ratings yet
- Information System Audit Process: by Dr. Selasi OcanseyDocument17 pagesInformation System Audit Process: by Dr. Selasi OcanseyHannett WoodNo ratings yet
- Processing Controls (1) 4Document14 pagesProcessing Controls (1) 4Shame BopeNo ratings yet
- Phishing-Is The Attempt To Acquire Sensitive Information Such As Usernames, Passwords, BankDocument9 pagesPhishing-Is The Attempt To Acquire Sensitive Information Such As Usernames, Passwords, BankTrixie CasipleNo ratings yet
- Soft Eng AnswerkeyDocument4 pagesSoft Eng AnswerkeyJoseph EscovidalNo ratings yet
- Is Audit Report - Chapter 8Document14 pagesIs Audit Report - Chapter 8Mary Grace Caguioa AgasNo ratings yet
- Cleanroom Software Engineering: CIS 376 Bruce R. Maxim UM-DearbornDocument35 pagesCleanroom Software Engineering: CIS 376 Bruce R. Maxim UM-DearbornMuskan KarjgiNo ratings yet
- SWE-600 SW Dependable SystemDocument48 pagesSWE-600 SW Dependable SystemMark WilliamsNo ratings yet
- CISDocument21 pagesCISDaud Farook IINo ratings yet
- Notes in A25Document5 pagesNotes in A25ejrileyriegoNo ratings yet
- Chapter 3Document4 pagesChapter 3sicelosmavusoNo ratings yet
- Processing ControlsDocument14 pagesProcessing ControlsMusariri TalentNo ratings yet
- Information Security IVDocument39 pagesInformation Security IVPratik BajajNo ratings yet
- Module 11 Maintaining InfoSec 211Document57 pagesModule 11 Maintaining InfoSec 211Umair AmjadNo ratings yet
- Chapter Four Information Technology and AuditingDocument78 pagesChapter Four Information Technology and Auditingabel habtamuNo ratings yet
- Monitoring and AuditingDocument31 pagesMonitoring and AuditingFlorence Heart ViñasNo ratings yet
- Computer Operational System PracDocument31 pagesComputer Operational System PracAnushkaNo ratings yet
- Chapter 7 Characteristics of CIS EnvironmentDocument40 pagesChapter 7 Characteristics of CIS EnvironmentEISEN BELWIGANNo ratings yet
- Software Quality ManagementDocument25 pagesSoftware Quality ManagementjatinderNo ratings yet
- It AuditDocument15 pagesIt AuditaleeshatenetNo ratings yet
- Untitled DocumentDocument5 pagesUntitled DocumentShiela MarieNo ratings yet
- HBT DS IDEMIA US EN 08mar2021 PDFDocument2 pagesHBT DS IDEMIA US EN 08mar2021 PDFErnesto GuerreroNo ratings yet
- Outdoor Streetlight Controller OLC Datasheet-SkyLiteDocument2 pagesOutdoor Streetlight Controller OLC Datasheet-SkyLiteYouTube YouTube vancedNo ratings yet
- ASSURx-G7 Raman Analyzer US - 500xxxx RevA - WEB PDFDocument4 pagesASSURx-G7 Raman Analyzer US - 500xxxx RevA - WEB PDFRossie' Kumoro AldianNo ratings yet
- CSE AI - 4 1 SEM CS Syllabus - UG - R20Document50 pagesCSE AI - 4 1 SEM CS Syllabus - UG - R20saitirumula541No ratings yet
- ProductsDocument7 pagesProductsAnonymous G1iPoNOKNo ratings yet
- Smart Manual ThomsonDocument32 pagesSmart Manual ThomsonJeevaNo ratings yet
- Tips and Tricks For Building ERP Interfaces in MIIDocument19 pagesTips and Tricks For Building ERP Interfaces in MIInetra14520100% (1)
- T2 - Precision PDFDocument4 pagesT2 - Precision PDFStephen BridgesNo ratings yet
- SHD Series Field Butt Fusion Welding Machine Technical Parameters PDFDocument19 pagesSHD Series Field Butt Fusion Welding Machine Technical Parameters PDFJavier Moya PiñonesNo ratings yet
- Eye Tracking Literature AnalysisDocument11 pagesEye Tracking Literature AnalysisSudhanshu DNo ratings yet
- FreemanWhite Hybrid Operating Room Design Guide PDFDocument11 pagesFreemanWhite Hybrid Operating Room Design Guide PDFNana AkwaboahNo ratings yet
- LUPIN TELEPOWER Corporate Profile New 06-10-10Document19 pagesLUPIN TELEPOWER Corporate Profile New 06-10-10Kikkeri S PrasadNo ratings yet
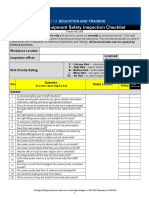
- Electrical Equipment Check ListDocument3 pagesElectrical Equipment Check ListPuran Singh LabanaNo ratings yet
- Mekelle University Mekelle Institute of TechnologyDocument17 pagesMekelle University Mekelle Institute of Technologysltanbrhane50No ratings yet
- GX2 HSG PDFDocument2 pagesGX2 HSG PDFMauro Barragan SanchezNo ratings yet
- 20687B ENU TrainerHandbook PDFDocument540 pages20687B ENU TrainerHandbook PDFRodolfo Jose Moncada AriasNo ratings yet
- Cad Drafting ServicesDocument11 pagesCad Drafting ServicesTanya PatelNo ratings yet
- Rdso Summer Training ProgramDocument4 pagesRdso Summer Training ProgramvlucknowNo ratings yet
- Window SosDocument18 pagesWindow SosJanela Natal MurilloNo ratings yet
- Tutoriel 2 - Shape and Combine Data in Power BI DesktopDocument19 pagesTutoriel 2 - Shape and Combine Data in Power BI DesktopLahmar AkramNo ratings yet
- 00040900Document30 pages00040900asperfudNo ratings yet
- EUDAMED GuidanceDocument20 pagesEUDAMED GuidancebiomedvibhutiNo ratings yet
- 2016 EIBN Sector Report Gaming IndustryDocument23 pages2016 EIBN Sector Report Gaming IndustryUlen IndonesiaNo ratings yet