Professional Documents
Culture Documents
Subtitle
Uploaded by
Mohammed Zakaria0 ratings0% found this document useful (0 votes)
3 views1 pageOriginal Title
subtitle (27)
Copyright
© © All Rights Reserved
Available Formats
TXT, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as TXT, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
3 views1 pageSubtitle
Uploaded by
Mohammed ZakariaCopyright:
© All Rights Reserved
Available Formats
Download as TXT, PDF, TXT or read online from Scribd
You are on page 1of 1
In this video, you will learn to; describe application
gateways and how this differ from standard
packet filtering firewalls, describe the limitations
of application gateways. Application gateways, so these
also are filter packets. But they are on
the application data. Which is the payload right at the top level
of the OSI stack, as well as these IP transport the fields that are in there. So
this allows for example, select users to employee the Telnet application
right outside. So effectively to
do this mandate. We require all telnet connections to go through a gateway. There's
an access
control mechanism that says, yes this is a telnet
connection and then is this user authorized
or not authorized. So it is once again an access control type mechanism that is
applied to
an application. So there's some
limitations right here. One of the things that as I said is that these are based
on transport protocol, so we can masquerade or
spook the IP address. This is done significantly
with Internet attacks that the source destination
is not in fact the true source destination
but its masqueraded, it appears to becoming
from either a customer or a trusted source when
in fact it is anything. But these firewalls that
we have been discussing. Do not have a mechanism
to really validate this, but significant threat
area right there. For application gateways
application firewalls. This is a one-to-one
relationship so that if you've got a single application
like a telnet, or in broadcast UDP
each one of these is going to require
its own application gateways. So there's one to
one relationship. This gets into
a very expensive process. In addition, the client software, the applications,
the web browsers, the email tools, Ftp tools, instant messaging all of
them have to be smart. So they need to have the protocol predetermined to know how
to communicate with the gateways whether that's an application
or a packet filter. These packet filters
will frequently are all or nothing application
relative to UDP. There's a security
thought that UDP should be largely disengaged. Because that's broadcasts,
there's a number of security vulnerabilities that
are associated with that. So what is the trade-off? The trade-off is
open communication with the outside world. No security policies in play. As opposed
to an increasing
level of security. With the increasing
level of security, there's more control
on protocols and applications and user access. So that is the trade space that the
security engineer
needs to outbreak. Despite that, many
highly protected sites US government sites still
suffer from cyber attack.
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5796)
- Salesforce MFA Mandate Global Campaign in A Box v1Document22 pagesSalesforce MFA Mandate Global Campaign in A Box v1Mohammed ZakariaNo ratings yet
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- E Nomination Process FlowDocument6 pagesE Nomination Process FlowMohammed ZakariaNo ratings yet
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- Welcome To People, Process and Operating System Fundamentals For CybersecurityDocument21 pagesWelcome To People, Process and Operating System Fundamentals For CybersecurityMohammed ZakariaNo ratings yet
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Iceland: by Mohammed Zakaria 215115066Document5 pagesIceland: by Mohammed Zakaria 215115066Mohammed ZakariaNo ratings yet
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- Sta Brings Security To Authentication and Access Product ReviewDocument8 pagesSta Brings Security To Authentication and Access Product ReviewMohammed ZakariaNo ratings yet
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- CMMDocument3 pagesCMMMohammed ZakariaNo ratings yet
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (400)
- IBPSDocument1 pageIBPSMohammed ZakariaNo ratings yet
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
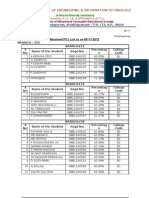
- Received PC List As On 12-12-12 SNO Name of The Student Branch Hall Ticket NumberDocument2 pagesReceived PC List As On 12-12-12 SNO Name of The Student Branch Hall Ticket NumberMohammed ZakariaNo ratings yet
- Application For Combined Defence Services Examination (I) - 2013Document1 pageApplication For Combined Defence Services Examination (I) - 2013Mohammed ZakariaNo ratings yet
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (589)
- Frank Burnash Resume - 2014Document2 pagesFrank Burnash Resume - 2014api-273214651No ratings yet
- Principles of Data Integrity - Pharmaceutical GuidelinesDocument1 pagePrinciples of Data Integrity - Pharmaceutical Guidelinessandro Cardoso100% (1)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- CBC Barbering NC IIDocument94 pagesCBC Barbering NC IINovalyn PaguilaNo ratings yet
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Dow Vinerobot (610953) 2013-09-10Document110 pagesDow Vinerobot (610953) 2013-09-10Jean-Marc DeHaeneNo ratings yet
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- Computer Networking: Lecture7: The Network LayerDocument22 pagesComputer Networking: Lecture7: The Network LayerTony JamesNo ratings yet
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- Add To Cart 15,00 EUR: Other Author's PublicationsDocument1 pageAdd To Cart 15,00 EUR: Other Author's PublicationsReo28No ratings yet
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (345)
- SecASC - M02 - Azure Security Center Setup and ConfigurationDocument53 pagesSecASC - M02 - Azure Security Center Setup and ConfigurationGustavo WehdekingNo ratings yet
- Postgraduate Orthopaedics Viva Guide For The Frcs TR Orth ExaminationDocument29 pagesPostgraduate Orthopaedics Viva Guide For The Frcs TR Orth ExaminationAshish Batra0% (1)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- Risk Register 7D6129 - Risk Log Template2Document4 pagesRisk Register 7D6129 - Risk Log Template2prabha_501131890No ratings yet
- MC Electronic InstrumentationDocument8 pagesMC Electronic InstrumentationMelvin Garcia QuirosNo ratings yet
- 3.6.mean and Variance of Sample MeansDocument41 pages3.6.mean and Variance of Sample Meansmuffinfluffy78No ratings yet
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- 73 Amateur Radio MagazineDocument66 pages73 Amateur Radio Magazinecaldan52No ratings yet
- SEO Action PlanDocument16 pagesSEO Action PlantanmayiNo ratings yet
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1091)
- 260918supervisor Form FinalDocument4 pages260918supervisor Form FinalNaveen RajNo ratings yet
- Updated Catalogue - Hue - Nov 2021 - LowRes VersionDocument48 pagesUpdated Catalogue - Hue - Nov 2021 - LowRes VersionHarshitBabooNo ratings yet
- BIOS-Code Meaning Part DevicesDocument21 pagesBIOS-Code Meaning Part DevicesFida HussainNo ratings yet
- Communication Systems QuestionDocument23 pagesCommunication Systems QuestionAman RaiNo ratings yet
- Drager Oxylog Family Accessory BrochureDocument28 pagesDrager Oxylog Family Accessory BrochuredeeNo ratings yet
- Error For FilesDocument23 pagesError For FilesGaurav BhardwajNo ratings yet
- Price 14.10.2020Document120 pagesPrice 14.10.2020MurcaNo ratings yet
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- Chapter I1Document53 pagesChapter I1مہنور مہتابNo ratings yet
- Ultracapacitor Technology Powers Electronic Circuits: Director of Product DevelopmentDocument6 pagesUltracapacitor Technology Powers Electronic Circuits: Director of Product Developmentkarthikeyantce502241No ratings yet
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Ramyashree H M: Curriculam VitaeDocument3 pagesRamyashree H M: Curriculam VitaeVishal FernandesNo ratings yet
- Vibrotip Web PAM1Document8 pagesVibrotip Web PAM1Bahtiar YudhistiraNo ratings yet
- E Banking EpwDocument5 pagesE Banking EpwArup BoseNo ratings yet
- Cisco IOS Security Command Reference - Commands S To ZDocument1,314 pagesCisco IOS Security Command Reference - Commands S To ZsilverclericNo ratings yet
- FranzJ Config Sept. 2021Document3 pagesFranzJ Config Sept. 2021ZippyシNo ratings yet
- TCG 01 G User Manual v2.1Document52 pagesTCG 01 G User Manual v2.1ParthNo ratings yet
- All Model LCDDocument240 pagesAll Model LCDlaxmansonawane75% (12)
- Evermotion Vol 55 PDFDocument2 pagesEvermotion Vol 55 PDFSimbad0% (1)