Professional Documents
Culture Documents
T REC G.803 200506 I!Amd1!PDF E
Uploaded by
utkarsh aroraOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
T REC G.803 200506 I!Amd1!PDF E
Uploaded by
utkarsh aroraCopyright:
Available Formats
I n t e r n a t i o n a l T e l e c o m m u n i c a t i o n U n i o n
ITU-T G.803
TELECOMMUNICATION Amendment 1
STANDARDIZATION SECTOR
OF ITU (06/2005)
SERIES G: TRANSMISSION SYSTEMS AND MEDIA,
DIGITAL SYSTEMS AND NETWORKS
Digital networks – General aspects
Architecture of transport networks based on the
synchronous digital hierarchy (SDH)
Amendment 1
ITU-T Recommendation G.803 (2000) – Amendment 1
ITU-T G-SERIES RECOMMENDATIONS
TRANSMISSION SYSTEMS AND MEDIA, DIGITAL SYSTEMS AND NETWORKS
INTERNATIONAL TELEPHONE CONNECTIONS AND CIRCUITS G.100–G.199
GENERAL CHARACTERISTICS COMMON TO ALL ANALOGUE CARRIER- G.200–G.299
TRANSMISSION SYSTEMS
INDIVIDUAL CHARACTERISTICS OF INTERNATIONAL CARRIER TELEPHONE G.300–G.399
SYSTEMS ON METALLIC LINES
GENERAL CHARACTERISTICS OF INTERNATIONAL CARRIER TELEPHONE SYSTEMS G.400–G.449
ON RADIO-RELAY OR SATELLITE LINKS AND INTERCONNECTION WITH METALLIC
LINES
COORDINATION OF RADIOTELEPHONY AND LINE TELEPHONY G.450–G.499
TRANSMISSION MEDIA CHARACTERISTICS G.600–G.699
DIGITAL TERMINAL EQUIPMENTS G.700–G.799
DIGITAL NETWORKS G.800–G.899
General aspects G.800–G.809
Design objectives for digital networks G.810–G.819
Quality and availability targets G.820–G.829
Network capabilities and functions G.830–G.839
SDH network characteristics G.840–G.849
Management of transport network G.850–G.859
SDH radio and satellite systems integration G.860–G.869
Optical transport networks G.870–G.879
DIGITAL SECTIONS AND DIGITAL LINE SYSTEM G.900–G.999
QUALITY OF SERVICE AND PERFORMANCE – GENERIC AND USER-RELATED G.1000–G.1999
ASPECTS
TRANSMISSION MEDIA CHARACTERISTICS G.6000–G.6999
DATA OVER TRANSPORT – GENERIC ASPECTS G.7000–G.7999
ETHERNET OVER TRANSPORT ASPECTS G.8000–G.8999
ACCESS NETWORKS G.9000–G.9999
For further details, please refer to the list of ITU-T Recommendations.
ITU-T Recommendation G.803
Architecture of transport networks based on the synchronous
digital hierarchy (SDH)
Amendment 1
Summary
This amendment replaces some definitions with a reference to ITU-T Rec. G.780/Y.1351 and the
modifications contained in Study Group 15 Report COM 15-R 5 Annex C.
Source
Amendment 1 to ITU-T Recommendation G.803 (2000) was approved on 29 June 2005 by ITU-T
Study Group 15 (2005-2008) under the ITU-T Recommendation A.8 procedure.
ITU-T Rec. G.803 (2000)/Amd.1 (06/2005) i
FOREWORD
The International Telecommunication Union (ITU) is the United Nations specialized agency in the field of
telecommunications. The ITU Telecommunication Standardization Sector (ITU-T) is a permanent organ of
ITU. ITU-T is responsible for studying technical, operating and tariff questions and issuing
Recommendations on them with a view to standardizing telecommunications on a worldwide basis.
The World Telecommunication Standardization Assembly (WTSA), which meets every four years,
establishes the topics for study by the ITU-T study groups which, in turn, produce Recommendations on
these topics.
The approval of ITU-T Recommendations is covered by the procedure laid down in WTSA Resolution 1.
In some areas of information technology which fall within ITU-T's purview, the necessary standards are
prepared on a collaborative basis with ISO and IEC.
NOTE
In this Recommendation, the expression "Administration" is used for conciseness to indicate both a
telecommunication administration and a recognized operating agency.
Compliance with this Recommendation is voluntary. However, the Recommendation may contain certain
mandatory provisions (to ensure e.g. interoperability or applicability) and compliance with the
Recommendation is achieved when all of these mandatory provisions are met. The words "shall" or some
other obligatory language such as "must" and the negative equivalents are used to express requirements. The
use of such words does not suggest that compliance with the Recommendation is required of any party.
INTELLECTUAL PROPERTY RIGHTS
ITU draws attention to the possibility that the practice or implementation of this Recommendation may
involve the use of a claimed Intellectual Property Right. ITU takes no position concerning the evidence,
validity or applicability of claimed Intellectual Property Rights, whether asserted by ITU members or others
outside of the Recommendation development process.
As of the date of approval of this Recommendation, ITU had not received notice of intellectual property,
protected by patents, which may be required to implement this Recommendation. However, implementors
are cautioned that this may not represent the latest information and are therefore strongly urged to consult the
TSB patent database.
ITU 2005
All rights reserved. No part of this publication may be reproduced, by any means whatsoever, without the
prior written permission of ITU.
ii ITU-T Rec. G.803 (2000)/Amd.1 (06/2005)
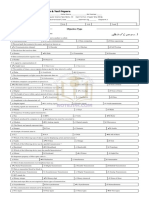
CONTENTS
Page
1) Clause 2 References...................................................................................................... 1
2) Clause 3 Terms and definitions .................................................................................... 1
3) Clause 6.3 Sublayer monitoring ................................................................................... 2
ITU-T Rec. G.803 (2000)/Amd.1 (06/2005) iii
ITU-T Recommendation G.803
Architecture of transport networks based on the synchronous
digital hierarchy (SDH)
Amendment 1
1) Clause 2 References
Add the following new reference alphanumerically:
– ITU-T Recommendation G.808.1 (2003), Generic protection switching – Linear trail and
subnetwork protection.
2) Clause 3 Terms and definitions
Replace the original terms and definitions with the new text as follows and remove footnotes:
Original term Replacement text
3.1 SDH higher-order path layer 3.1 SDH higher-order path layer
networks: Those layer networks with networks: See ITU-T Rec. G.780/Y.1351.
characteristic information of VC-31, VC-3-Xv
(X = 2 … 48)2, VC-4, VC-4-Xc (X = 4, 16)3 or
VC-4-Xv (X = 2 … 16)3.
3.2 SDH lower-order path layer 3.2 SDH lower-order path layer
networks: Those layer networks with networks: See ITU-T Rec. G.780/Y.1351.
characteristic information of VC-11, VC-11-Xv
(X = 2 … 84), VC-12, VC-12-Xv (X = 2 … 63),
VC-2, VC-2-Xc (X = 2 … 7)4, VC-2-Xv
(X = 2 … 21)5 or VC-31 or VC-3-Xv
(X = 2 … 3)5.
3.3 SDH path layer: A transport assembly 3.3 SDH path layer: See ITU-T
composed of the SDH higher-order path layer Rec. G.780/Y.1351.
network and lower-order path layer network
together with the associated adaptation
functions.
3.4 SDH section layer: A transport 3.4 SDH section layer: See ITU-T
assembly composed of the SDH multiplex Rec. G.780/Y.1351.
section layer network and regenerator section
layer network together with the associated
adaptation functions.
3.5 SDH multiplex section layer: A layer 3.5 SDH multiplex section layer:
network with characteristic information of See ITU-T Rec. G.780/Y.1351.
STM-N, i.e., with a bit rate of STM-N and the
multiplex section overhead as defined in ITU-T
Rec. G.707.
ITU-T Rec. G.803 (2000)/Amd.1 (06/2005) 1
Original term Replacement text
3.6 SDH regenerator section layer: A 3.6 SDH regenerator section layer: See
layer network with characteristic information of ITU-T Rec. G.780/Y.1351.
STM-N, i.e., with a bit rate of STM-N and the
regenerator section overhead as defined in
ITU-T Rec. G.707.
Footnotes:
1 The VC-3 is considered to be a higher-order path if it
is supported directly by an AU-3 in a multiplex
section layer network; it is considered a lower-order
path if it is supported by a TU-3 in a VC-4 layer
network.
2 Values of X larger than 48 may be required.
3 Values of X larger than 16 may be required.
4 Transported in one higher order VC-3
5 Transported in one higher order VC-4.
3) Clause 6.3 Sublayer monitoring
After Figure 6-1 insert the following text and figures:
Note that SDH supports only one level of TCM per VC-n path level. Nesting and overlapping of
TCM as shown in Figure 6-1a is, therefore, not supported.
Figure 6-1a/G.803 – Not supported SDH tandem connection monitoring (nesting, overlapping)
Together with VC-n subnetwork protection SNC (see 11.2/G.808.1) TCM can be used to provide
the protection switching criteria by monitoring the working and protection subnetwork connection
between the protection switching points (SNC/S as defined in 11.2/G.808.1) or for monitoring of
the protected signal as shown in Figure 6-1b.
2 ITU-T Rec. G.803 (2000)/Amd.1 (06/2005)
monitoring of monitoring of
working and protection connection (SNC/S) protected connection
VC-n TC working
working connection working connection
NE NE NE NE
NE NE NE NE
protection NE protection protection NE protection
switching switching switching switching
node protection connection node node protection connection node
VC-n TC protection SNC/I or SNC/N
SNC/S VC-n TC protected
overlapping of TCM and protection
not allowed
working connection
NE NE
NE NE
NE
protection protection
switching NE switching
node protection connection node
SNC/I or SNC/N
VC-n TC
G.803AMD.1_F6-1b
Figure 6-1b/G.803 – SDH tandem connection monitoring SNC protection
Note that TCM for the working and protection connection and the protected connection at the same
time is not possible as nesting of TCM is not supported.
Overlapping of TCM and subnetwork connection protection is not allowed as the relation between
TCM source and sink functions will change with every protection switch.
ITU-T Rec. G.803 (2000)/Amd.1 (06/2005) 3
SERIES OF ITU-T RECOMMENDATIONS
Series A Organization of the work of ITU-T
Series D General tariff principles
Series E Overall network operation, telephone service, service operation and human factors
Series F Non-telephone telecommunication services
Series G Transmission systems and media, digital systems and networks
Series H Audiovisual and multimedia systems
Series I Integrated services digital network
Series J Cable networks and transmission of television, sound programme and other multimedia signals
Series K Protection against interference
Series L Construction, installation and protection of cables and other elements of outside plant
Series M Telecommunication management, including TMN and network maintenance
Series N Maintenance: international sound programme and television transmission circuits
Series O Specifications of measuring equipment
Series P Telephone transmission quality, telephone installations, local line networks
Series Q Switching and signalling
Series R Telegraph transmission
Series S Telegraph services terminal equipment
Series T Terminals for telematic services
Series U Telegraph switching
Series V Data communication over the telephone network
Series X Data networks, open system communications and security
Series Y Global information infrastructure, Internet protocol aspects and next-generation networks
Series Z Languages and general software aspects for telecommunication systems
Printed in Switzerland
Geneva, 2005
You might also like
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (122)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (589)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (401)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (842)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (897)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5806)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (345)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1091)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Technical Seminar Topic Name 6G Mobile Technology: Seminar By: Karthik Rajaram (1BH17CS028) Sem: VIII Department of CSEDocument9 pagesTechnical Seminar Topic Name 6G Mobile Technology: Seminar By: Karthik Rajaram (1BH17CS028) Sem: VIII Department of CSEYATHISH M GNo ratings yet
- Atta CV Updated (01-07-22)Document2 pagesAtta CV Updated (01-07-22)Saddam A. AbbasiNo ratings yet
- 1ST Term SS1 Data Processing Note SumDocument26 pages1ST Term SS1 Data Processing Note SumimoleayooluwaseunNo ratings yet
- Axis Se 01Document57 pagesAxis Se 01SergejNo ratings yet
- CS101 Final Term by AR Lucky TermDocument256 pagesCS101 Final Term by AR Lucky Termnoor ainNo ratings yet
- NSF 330Document10 pagesNSF 330amzad khanNo ratings yet
- TelecommunicationsDocument23 pagesTelecommunicationsnigel989No ratings yet
- Chapter 3 Wireless Network Principles 1Document54 pagesChapter 3 Wireless Network Principles 1Tsion KebedeNo ratings yet
- Introduction To CNDocument52 pagesIntroduction To CNNithilan ANo ratings yet
- Module 4Document49 pagesModule 4asaintjerkNo ratings yet
- Saed Jamil Shahwan: The Impact of Social Media On LiteratureDocument20 pagesSaed Jamil Shahwan: The Impact of Social Media On Literaturesohaib ShahwanNo ratings yet
- 8310PD9604Document8 pages8310PD9604diego quinteroNo ratings yet
- 2nd Year CitDocument49 pages2nd Year CitmalikhuzaifaawaanNo ratings yet
- Gujarat Technological University: 1. Learning ObjectivesDocument8 pagesGujarat Technological University: 1. Learning ObjectivesuditNo ratings yet
- MSc-IT-Semester-System Outlines PUNJAB UNIVERSITY PakistanDocument33 pagesMSc-IT-Semester-System Outlines PUNJAB UNIVERSITY PakistanDANCE MUJRA FUNNo ratings yet
- AMR Notes - Anil Manal PatilDocument25 pagesAMR Notes - Anil Manal PatilDuRvEsH RaYsInGNo ratings yet
- Chap3solved MCQsDocument2 pagesChap3solved MCQshassan janNo ratings yet
- Digital CommunicationchapterprepressDocument14 pagesDigital CommunicationchapterprepresslorennavNo ratings yet
- M.tech Thesis Topics in Wireless CommunicationDocument6 pagesM.tech Thesis Topics in Wireless Communicationjanaclarkbillings100% (2)
- Physics New NotesDocument8 pagesPhysics New NotesDaniel CannywoodNo ratings yet
- ch3 DatatransmissionDocument103 pagesch3 DatatransmissionNaveed AhmedNo ratings yet
- Q4 W1 - DiassDocument4 pagesQ4 W1 - DiassClaire CaraigNo ratings yet
- 9066Document5 pages9066Aryan JaiswalNo ratings yet
- GSM Based DC Motor ControlDocument8 pagesGSM Based DC Motor ControlK IsmailNo ratings yet
- HSST Computer Science 1Document4 pagesHSST Computer Science 1Anjalaa ZhNo ratings yet
- Introduction To Digital Electronics: Analog DataDocument6 pagesIntroduction To Digital Electronics: Analog DataAbishek NeupaneNo ratings yet
- Study On Delhi Metro: Summer Internship Project Report - 2010Document63 pagesStudy On Delhi Metro: Summer Internship Project Report - 2010nitik chakmaNo ratings yet
- Ref Bts Alarms and Fault Sran21b Sran21aDocument832 pagesRef Bts Alarms and Fault Sran21b Sran21awini komlanNo ratings yet
- Dwnload Full Business Data Communications and Networking 13th Edition Fitzgerald Test Bank PDFDocument22 pagesDwnload Full Business Data Communications and Networking 13th Edition Fitzgerald Test Bank PDFkilergstudiousdrgyo100% (12)
- Data Communication SlideDocument309 pagesData Communication SlideEnoch AidooNo ratings yet