Professional Documents
Culture Documents
Logical Malleability, Invisibility Factor, Moral Responsibilities
Uploaded by
Jordan BasiloniaCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Logical Malleability, Invisibility Factor, Moral Responsibilities
Uploaded by
Jordan BasiloniaCopyright:
Available Formats
Social and Professional Issues (IT)
Lesson no. 3
Logical Malleability
Computers can be shaped and molded to perform any activity that can be
characterized in terms of inputs, outputs, and connecting logical operations. This
is in contrast to the majority of manufactured products. For example, a car,
television or refrigerator has well-defined and quite specific functions.
The logic of computers, however, can be shaped in infinite ways through
changes in hardware and software and in terms of their usage. This enables
computer-based technologies to exhibit tremendous flexibility. Moor writes:
Just as the power of steam engine was the raw resource of the Industrial
Revolution so the logic of a computer is a raw of the Information Revolution.
Because the logic applies everywhere, the potential applications of computer
technology appear limitless. The computer is the nearest thing we have to a
universal tool. Indeed, the limits of computers are largely the limits of our own
creativity.
Invisibility Factor
An important fact about computers is that most of the time, and under
most conditions, computer operations are invisible. Moor identifies three kinds of
invisibility that can have ethical significance:
1. INVISIBLE ABUSE. Moor describes this as : “the international use of the
invisible operations of a computer to engage in unethical conduct.” He cites some
examples:
The programmer who realized he could steal excess interest from a bank.
When interest on a bank account is calculated, there is often a fraction of a cent
left over after rounding off. This programmer instructed a computer to deposit
these fractions of a cent to his own account.
The invasion of the property and privacy of others, computers can be
programmed to surreptitiously remove or alter confidential information.
2. INVISIBLE PROGRAMMING VALUES. These values are embedded into a
computer program:
A programmer makes some value judgments about what is important and
what is not. These values become embedded in the final product and may be
invisible to someone who runs the program.
3. INVISIBLE COMPLEX CALCULATION. In this context, Moor writes;
Computers today are capable of enormous calculations beyond human
comprehension. Even if a program is understood, it does not follow that the
respective calculations are understood. Computers today perform…calculations
which are too complex for human inspection and understanding.
He argues that the issue is how much we should trust computer’s invisible
calculation. This becomes a significant issue as the consequences grow in
importance.
For Example:
Computers are used by the military in making decisions about launching
nuclear weapons. On the other hand, computers are fallible and there may not be
time to confirm their assessment of the situation. On the other hand, making
decisions about launching nuclear weapons without using computers may be
even more fallible and more dangerous.
Moral Responsibilities of Computer Professionals
Some ethicists believe that all professionals, regardless of their practice,
have special moral obligations as professionals. For example, Michael Bayles
(2003) argues that professionals have a special obligation to their clients to be
worthy of a client’s trust, and this , further suggests, leads to obligations of
honesty, candor, competence, diligence, loyalty and discretion. In Bayle’s scheme,
all professionals who work in the computing field would be bound to similar
standards of obligations to their clients, regardless of their specific professional
type.
Computer professionals are responsible for developing safety-critical
systems, therefore, they have the significant opportunities to:
a. do good or cause harm.
b. enable others to do good or cause harm.
c. influence others to do good or cause harm.
Thus, Gotterbarn suggests that the roles and responsibilities involved in the
development of safety-critical systems are a differentiating factor.
Kevin Bowyer (2001) points out that the phrase “safety critical system” is
often used to refer to computer systems that can have a “direct life-threatening
impact.” Examples of safety-critical software applications typically include:
a. aircraft and air traffic control systems
b. mass transportation system
c. nuclear reactors
d. missile systems
e. medical treatment systems
Reference: Social, Ethical, Legal and Professional Issues in Computing
by : Charlemagne G. Lavina
You might also like
- Aclu List Research Export 20160810050210Document2 pagesAclu List Research Export 20160810050210api-285701682100% (1)
- Clarisonic Business ReportDocument13 pagesClarisonic Business Reportapi-484594814No ratings yet
- Entrepreneur'S Attributes, Qualities and CharacteristicsDocument17 pagesEntrepreneur'S Attributes, Qualities and CharacteristicsAira PartiNo ratings yet
- ICTWS - (18.3.2) Web Scripting Learning Plans - SJEDocument64 pagesICTWS - (18.3.2) Web Scripting Learning Plans - SJEIkee AlianganNo ratings yet
- DREAMTEAM102619Document20 pagesDREAMTEAM102619Jade Flores NipasNo ratings yet
- Shangri La Hotels and Resorts SWOTDocument2 pagesShangri La Hotels and Resorts SWOTHadi Agustana100% (1)
- Introduction To Software LicensingDocument4 pagesIntroduction To Software LicensingRay-Ray OdagenerNo ratings yet
- Christian Renewal of Filipino Values V GorospeDocument38 pagesChristian Renewal of Filipino Values V GorospeDebbie Angel LorenzanaNo ratings yet
- Chapter 9-: Capacity Planning & Facility LocationDocument29 pagesChapter 9-: Capacity Planning & Facility LocationYash SharmaNo ratings yet
- Education DepartmentDocument67 pagesEducation DepartmentJanillaNo ratings yet
- ENG221-CIA1: Advantages and Disadvantages of CoVID-19Document6 pagesENG221-CIA1: Advantages and Disadvantages of CoVID-19Aman KumarNo ratings yet
- Tony Tan Caktiong – Jollibee founderDocument6 pagesTony Tan Caktiong – Jollibee founderRose Ann0% (1)
- Bangayan, Melody D. Discussion 4 Hypothesis.Document2 pagesBangayan, Melody D. Discussion 4 Hypothesis.Melody Domingo BangayanNo ratings yet
- Chapter 1 - Santol Siopao - 1Document6 pagesChapter 1 - Santol Siopao - 1GilbertGacisNo ratings yet
- Exercise # 5Document1 pageExercise # 5Mara Shaira SiegaNo ratings yet
- Chapter 1Document9 pagesChapter 1Jhoy Vien BenavidezNo ratings yet
- Reaction Paper ExhibitDocument2 pagesReaction Paper ExhibitAnna Lorraine Galura100% (4)
- Lesson 4 For EntrepDocument14 pagesLesson 4 For EntrepRhea May Peduca67% (3)
- Chapter 1Document8 pagesChapter 1Mehari TemesgenNo ratings yet
- GEC Purposive Communication Course PackDocument81 pagesGEC Purposive Communication Course PackJulianna Jade Dela Cruz100% (1)
- MGT 406 - Chapter 1Document18 pagesMGT 406 - Chapter 1Bilal AfzalNo ratings yet
- Path Fit 1Document25 pagesPath Fit 1Jeru Elbanbuena100% (1)
- Generalization Week2Document4 pagesGeneralization Week21104 Canales Ma GraciellaNo ratings yet
- Purposive CommunicationDocument15 pagesPurposive CommunicationJella LaurenNo ratings yet
- AdetDocument6 pagesAdetAnjemar AcostaNo ratings yet
- The Business ProponentsDocument2 pagesThe Business ProponentsChubby BunnyNo ratings yet
- Group 6 Grade 12 ABM B Research ProblemDocument8 pagesGroup 6 Grade 12 ABM B Research ProblemEleonor Rose Lopez100% (1)
- Answer 1Document3 pagesAnswer 1Charlote Jennifer FetalinoNo ratings yet
- Purposive CommunicationDocument61 pagesPurposive CommunicationBaby PinkNo ratings yet
- Act 8 Sts PDFDocument3 pagesAct 8 Sts PDFCherry Ann OlasimanNo ratings yet
- Practical Research 1aDocument8 pagesPractical Research 1aKapitan Bilang0% (1)
- Marketing PlanDocument18 pagesMarketing PlanPatricia Mae ObiasNo ratings yet
- Module 3 Learning Activities - GE6 (STS) Learning Activity 1Document1 pageModule 3 Learning Activities - GE6 (STS) Learning Activity 1Alejandro RabanaljrNo ratings yet
- Principles of Marketing: Senior High SchoolDocument21 pagesPrinciples of Marketing: Senior High SchoolGeraldine EctanaNo ratings yet
- PR 1 Lesson 3Document9 pagesPR 1 Lesson 3Steven Paul BacantoNo ratings yet
- Impact of Fringe Benefits On Employee Performance in San Pedro AcademyDocument13 pagesImpact of Fringe Benefits On Employee Performance in San Pedro AcademyDanica ImboNo ratings yet
- Group 5 ABMDocument94 pagesGroup 5 ABMArra BaluyutNo ratings yet
- CK College Narra Campus Ollopa Company WIL ReportDocument3 pagesCK College Narra Campus Ollopa Company WIL ReportBryent GawNo ratings yet
- Characteristics of A Well-Written ObjectivesDocument15 pagesCharacteristics of A Well-Written ObjectivesRamil GofredoNo ratings yet
- Resume ShelwinDocument2 pagesResume ShelwinShelby AntonioNo ratings yet
- Perdev Q3 Module 2 Ans - Stem 11Document6 pagesPerdev Q3 Module 2 Ans - Stem 11Nadine JongNo ratings yet
- PE3 Input and Output 1Document29 pagesPE3 Input and Output 1Marq John TabiliranNo ratings yet
- Baybayin Thesis Chapter 1Document2 pagesBaybayin Thesis Chapter 1Steph BentülanNo ratings yet
- 5x2 - 2 Term 10x2 - 3 Term 20x2 - 4 Term 40x2 - 5 Term 80x2 - Last TermDocument2 pages5x2 - 2 Term 10x2 - 3 Term 20x2 - 4 Term 40x2 - 5 Term 80x2 - Last TermJhiemalyn RonquilloNo ratings yet
- Instructional Module: Republic of The Philippines Nueva Vizcaya State University Bayombong, Nueva VizcayaDocument14 pagesInstructional Module: Republic of The Philippines Nueva Vizcaya State University Bayombong, Nueva VizcayaMary Jane BugarinNo ratings yet
- Frayer Model Graphic OrganizerDocument7 pagesFrayer Model Graphic OrganizerBenjamin TaduranNo ratings yet
- Use Business Tools Efficiently and Effectively and in Accordance With Enterprise Policy and ProceduresDocument8 pagesUse Business Tools Efficiently and Effectively and in Accordance With Enterprise Policy and ProceduresJessalyn Sarmiento TancioNo ratings yet
- 2B1 - Expression of Intent For Incoming Freshman Admission - 034018 PDFDocument4 pages2B1 - Expression of Intent For Incoming Freshman Admission - 034018 PDFSassy BulanNo ratings yet
- Source of Ideas For Entrepreneurial VenturesDocument13 pagesSource of Ideas For Entrepreneurial VenturesKelvin Jay Sebastian SaplaNo ratings yet
- Purposive Communication Module 2 PDFDocument24 pagesPurposive Communication Module 2 PDFEdgar Belono-ac Jr.No ratings yet
- Advance Business Communication - Chapter 1,2Document24 pagesAdvance Business Communication - Chapter 1,2Fatima MazharNo ratings yet
- Accounting Concepts and Principles Are A Set of Broad Conventions That Have Been Devised To Provide A Basic Framework For Financial ReportingDocument8 pagesAccounting Concepts and Principles Are A Set of Broad Conventions That Have Been Devised To Provide A Basic Framework For Financial ReportingGesa StephenNo ratings yet
- Consumer Memory and Product Knowledge: By: Garcia, Katrine Dianne M. 2-BSBA-MMDocument24 pagesConsumer Memory and Product Knowledge: By: Garcia, Katrine Dianne M. 2-BSBA-MMPaulNo ratings yet
- Ethics ReportDocument1 pageEthics ReportValero AngelicaNo ratings yet
- The Lost, The Least and The LastDocument2 pagesThe Lost, The Least and The LastGil Ramos100% (1)
- Final Research PaperDocument11 pagesFinal Research Paperapi-546795600No ratings yet
- Toteally Trendy Bag: AnswersDocument2 pagesToteally Trendy Bag: AnswersRose BaynaNo ratings yet
- Strategic Management Model ExplainedDocument10 pagesStrategic Management Model ExplainedJanrhey EnriquezNo ratings yet
- Frames - Tools for telling storiesDocument16 pagesFrames - Tools for telling storiesMike BalubarNo ratings yet
- Ge 101 - UtsDocument3 pagesGe 101 - UtsRenz Phillip LacsamanaNo ratings yet
- Taking Carmen's Best Ice Cream GlobalDocument8 pagesTaking Carmen's Best Ice Cream GlobalN.a. M. TandayagNo ratings yet
- My Life Journey Through . . . with God: Reality and Facts of Life!From EverandMy Life Journey Through . . . with God: Reality and Facts of Life!No ratings yet
- Math 350 Paper 5Document4 pagesMath 350 Paper 5Jordan BasiloniaNo ratings yet
- Math 350-Info-4Document4 pagesMath 350-Info-4Jordan BasiloniaNo ratings yet
- Math 350-HW-6Document4 pagesMath 350-HW-6Jordan BasiloniaNo ratings yet
- Math 350 Lecture 7Document4 pagesMath 350 Lecture 7Jordan BasiloniaNo ratings yet
- Math 350 Report 3Document4 pagesMath 350 Report 3Jordan BasiloniaNo ratings yet
- SOC267 Doc 7Document4 pagesSOC267 Doc 7kcr zones243No ratings yet
- Math 350 Notes 7Document4 pagesMath 350 Notes 7Jordan BasiloniaNo ratings yet
- Math 350-HW-1Document4 pagesMath 350-HW-1Jordan BasiloniaNo ratings yet
- Math 350 Handout 1Document4 pagesMath 350 Handout 1Jordan BasiloniaNo ratings yet
- Math 350 Notes 1Document4 pagesMath 350 Notes 1Jordan BasiloniaNo ratings yet
- Math 350 Answers 3Document4 pagesMath 350 Answers 3Jordan BasiloniaNo ratings yet
- Math 350 Test Prep 6Document4 pagesMath 350 Test Prep 6Jordan BasiloniaNo ratings yet
- Math 350 Chapter Summary 10Document4 pagesMath 350 Chapter Summary 10Jordan BasiloniaNo ratings yet
- Math 350 Practice Problems 7Document4 pagesMath 350 Practice Problems 7Jordan BasiloniaNo ratings yet
- Math 350 Lec Notes 4Document4 pagesMath 350 Lec Notes 4Jordan BasiloniaNo ratings yet
- Math 350 Final 2Document4 pagesMath 350 Final 2Jordan BasiloniaNo ratings yet
- Bio 101 - Lecture - Notes - 8Document4 pagesBio 101 - Lecture - Notes - 8Jordan BasiloniaNo ratings yet
- Math 350-Exam-2Document4 pagesMath 350-Exam-2Jordan BasiloniaNo ratings yet
- Math 350 Homework Help 7Document4 pagesMath 350 Homework Help 7Jordan BasiloniaNo ratings yet
- Math 350 - Doc - 8Document4 pagesMath 350 - Doc - 8Jordan BasiloniaNo ratings yet
- Math 350 Answer Key 2Document4 pagesMath 350 Answer Key 2Jordan BasiloniaNo ratings yet
- Bio 101 - HW - 4Document4 pagesBio 101 - HW - 4Jordan BasiloniaNo ratings yet
- Bio 101-Worksheet-10Document4 pagesBio 101-Worksheet-10Jordan BasiloniaNo ratings yet
- Bio 101 - Extra - Credit - 4Document4 pagesBio 101 - Extra - Credit - 4Jordan BasiloniaNo ratings yet
- Bio 101 - Problems - 8Document4 pagesBio 101 - Problems - 8Jordan BasiloniaNo ratings yet
- Bio 101-Week-4Document4 pagesBio 101-Week-4Jordan BasiloniaNo ratings yet
- Greek and Roman Mythology QuizDocument4 pagesGreek and Roman Mythology QuizJordan BasiloniaNo ratings yet
- PHAR238 Info 4Document4 pagesPHAR238 Info 4Ovelia KayuzakiNo ratings yet
- Bio 101-Lab-9Document4 pagesBio 101-Lab-9Jordan BasiloniaNo ratings yet
- Bio 101-Midterm-1Document4 pagesBio 101-Midterm-1Jordan BasiloniaNo ratings yet
- EJN-00625 Installation of Manual Pull Valves in Deluge Systems For SOLPEDocument4 pagesEJN-00625 Installation of Manual Pull Valves in Deluge Systems For SOLPESARAVANAN ARUMUGAMNo ratings yet
- MSCL PipeDocument9 pagesMSCL PipeAhmad Zakwan Asmad100% (1)
- Governor's Pleasure and Dismissal of Council of MinistersDocument10 pagesGovernor's Pleasure and Dismissal of Council of MinistersUditanshu MisraNo ratings yet
- Atlantic Revolutions: Ogé Insurrection Inspired Haitian IndependenceDocument18 pagesAtlantic Revolutions: Ogé Insurrection Inspired Haitian IndependenceNiara ChaneyNo ratings yet
- Lewin's 3 Leadership StylesDocument2 pagesLewin's 3 Leadership Stylesmar_hisham8900No ratings yet
- Space Management Guidelines: Brief SummaryDocument17 pagesSpace Management Guidelines: Brief SummaryMOHD JIDINo ratings yet
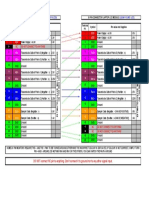
- Total Standards: - Total Sub-Standards: - Total ESR StandardsDocument8 pagesTotal Standards: - Total Sub-Standards: - Total ESR StandardsHCX dghhqNo ratings yet
- Procedures For Drill String Design Engineering EssayDocument16 pagesProcedures For Drill String Design Engineering EssayGerardy Cantuta AruniNo ratings yet
- Nimt Institute of Method & Law, Greater Noida: "Legal Bases and Issues in Scrapping Article 370"Document12 pagesNimt Institute of Method & Law, Greater Noida: "Legal Bases and Issues in Scrapping Article 370"Preetish Sahu100% (1)
- Director Infrastructure Technology Data Center in Atlanta GA Resume Thiron BarrDocument4 pagesDirector Infrastructure Technology Data Center in Atlanta GA Resume Thiron BarrThironBarrNo ratings yet
- An Improved TS Algorithm For Loss-Minimum Reconfiguration in Large-Scale Distribution SystemsDocument10 pagesAn Improved TS Algorithm For Loss-Minimum Reconfiguration in Large-Scale Distribution Systemsapi-3697505No ratings yet
- Systemverilog Interview QuestionsDocument31 pagesSystemverilog Interview QuestionsDivya Dm100% (1)
- Control unit checks gas burner valve tightness according to EN 1643Document12 pagesControl unit checks gas burner valve tightness according to EN 1643alfredomamutNo ratings yet
- Rotating EquipmentDocument3 pagesRotating EquipmentSathish DesignNo ratings yet
- Quiz ME 1Document4 pagesQuiz ME 1Radytia BimantaraNo ratings yet
- W3. The Relational ModelDocument21 pagesW3. The Relational ModelSABOOR UR RAHMANNo ratings yet
- Jurnal Tentang Akuntansi Dengan Metode Kualitatif IDocument8 pagesJurnal Tentang Akuntansi Dengan Metode Kualitatif IAfni FebrianaNo ratings yet
- Discharging A ClientDocument6 pagesDischarging A ClientNorman Batalla Juruena, DHCM, PhD, RNNo ratings yet
- Chandler V MillerDocument2 pagesChandler V MillerJay Cezar100% (1)
- Lecture 08Document27 pagesLecture 08simraNo ratings yet
- Understanding The American Education SystemDocument6 pagesUnderstanding The American Education SystemCastor JavierNo ratings yet
- The Stolen EaglesDocument12 pagesThe Stolen EaglesJavier Horacio FernandezNo ratings yet
- Instruction Manual For Spider S3 and Spider S4Document6 pagesInstruction Manual For Spider S3 and Spider S4Syah KamalNo ratings yet
- LCD PinoutsDocument1 pageLCD PinoutsPablo Daniel MagallanNo ratings yet
- PRACTICA (1) (1) - Páginas-2-4Document3 pagesPRACTICA (1) (1) - Páginas-2-4EDDY POLICARPIO BRAVO HUAMANINo ratings yet
- App Cache 133069888033757953Document46 pagesApp Cache 133069888033757953akunkelasdNo ratings yet
- Design Thinking ReflectionDocument3 pagesDesign Thinking ReflectionNeil PerlasNo ratings yet
- Thesis Supervisor Recommendation With Representative Content and Information RetrievalDocument8 pagesThesis Supervisor Recommendation With Representative Content and Information RetrievalIlmiMardatillahNo ratings yet