Professional Documents
Culture Documents
DNS It 2018
Uploaded by
rumi noor0 ratings0% found this document useful (0 votes)
7 views1 pageDesign and network security
Original Title
DNS IT 2018
Copyright
© © All Rights Reserved
Available Formats
PDF or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentDesign and network security
Copyright:
© All Rights Reserved
Available Formats
Download as PDF or read online from Scribd
0 ratings0% found this document useful (0 votes)
7 views1 pageDNS It 2018
Uploaded by
rumi noorDesign and network security
Copyright:
© All Rights Reserved
Available Formats
Download as PDF or read online from Scribd
You are on page 1of 1
WO UN
Universes“ oarpodha .
7° By i
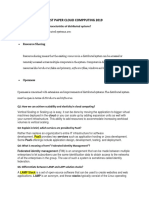
Subject; Information Technology Paper: Data & Nei
ork Si y (IT: 4549,
Time Allowed; 2:30 Hours
Maximum Marks: 80
Note: Objective Part is compulsory. AttemP! #"Y four questions from subjective Part.
- ce Pa
Objective Part (Computsory)
4. Write short answers of the following in 2-3 Tines ea
8 1 What is the importance of security Policy? ch on thé answer sheeb (2"16)
What is chosen-plaintext attack?
@ iii, Define Security Association.
“iv. What is the role of Kerberos in network Seuiy?
fy. Write the function of Handshake protocol? '
vi, Define'trust?
Tyii, ‘The strength ofvigencre cipher lies on which factor?
_.viii, Define transposition technique?
_~ ix. Define router security? 5
nx. Wh Avalanche effect is desirable property in any e1 ‘ an
a Whauis the drawback of tiple DES? Seven ean
— xii, Which factors affect the size of initialization vector?
_— xiii. Define timing attacks.
xiv. When Symmetric-key cryptography is more efficient than asymmemc-key
cryptography?
_—xv. _ Whatis bash function?
_-xvi. How AAA ensures security?
Subjective Part (4912)
How AES ensures security? }
Explain encryption and decryption with Playfair in detail?
Explain Diffie-Hellman key exchange technique with example?
How certificate authority solves the problem of management of public keys?
What is a WLAN? How Wireless Works swith and without open ports?
What is message authentication? Explait authentication functions.
tShahab.blogspot.com
You might also like
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (121)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (400)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2259)
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (345)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (74)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- Short Questions: Past Papers Network Design & ManagementDocument5 pagesShort Questions: Past Papers Network Design & Managementrumi noorNo ratings yet
- Past Paper Erp ShortDocument6 pagesPast Paper Erp Shortrumi noorNo ratings yet
- PAST PAPER CLOUD COMPPUTING Short 2019Document3 pagesPAST PAPER CLOUD COMPPUTING Short 2019rumi noorNo ratings yet
- Past Paper Game Development 2019Document3 pagesPast Paper Game Development 2019rumi noorNo ratings yet
- DNS It 2017Document1 pageDNS It 2017rumi noorNo ratings yet
- Virtual Furniture Using Augmented Reality: Snehal Mangale, Nabil Phansopkar, Safwaan Mujawar, Neeraj SinghDocument5 pagesVirtual Furniture Using Augmented Reality: Snehal Mangale, Nabil Phansopkar, Safwaan Mujawar, Neeraj Singhrumi noorNo ratings yet
- NDM Mit 2020Document1 pageNDM Mit 2020rumi noorNo ratings yet