Professional Documents
Culture Documents
MCQ Test
Uploaded by
4AL19CS059 BHAGYASREEOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
MCQ Test
Uploaded by
4AL19CS059 BHAGYASREECopyright:
Available Formats
1. To print a float value which format specifier can be used?
A - %f *
B - %lf
C - %Lf
D - None of the above
2. Which operator is used to continue the definition of macro in the next line?
A - #
B - ##
C - $
D-/ *
3.Which of the following transmission directions listed is not a legitimate channel?
Simplex
Half Duplex
Full Duplex
Double Duplex *
4.The term HTTP stands for?
a. Hyper terminal tracing program
b. Hypertext tracing protocol
c. Hypertext transfer protocol *
d. Hypertext transfer program
5. Which software prevents the external access to a system?
a. Firewall *
b. Gateway
c. Router
d. Virus checker
6. Which one of the following is the most common internet protocol?
a. HTML
b. NetBEUI
c. TCP/IP *
d. IPX/SPX
7.Which one of the following is not a network topology?
a. Star
b. Ring
c. Bus
d. Peer to Peer *
8 The length of an IPv6 address is?
a. 32 bits
b. 64 bits
c. 128 bits *
d. 256 bits
9.ThefirstNetworkwascalled________
a)CNNET
b)NSFNET
c)ASAPNET
d) ARPANET *
10.The attacker using a network of compromised devices is known as _____________
a)Internet
b)Botnet*
c)Telnet
d) D-net
11. IPSec is designed to provide security at the _________
a) Transport layer
b) Network layer *
c) Application layer
d) Session layer
12.An attempt to make a computer resource unavailable to its intended users is
called ______
a) Denial-of-service attack *
b) Virus attack
c) Worms attack
d) Botnet process
13. A DNS client is called _________
a) DNS updater
b) DNS resolver *
c) DNS handler
d) none of the mentioned
14. Scanning is performed in which phase of a pen test?
A. Pre-attack *
B. Attack
C. Post-attack
D. Reconnaissance
15.What is the attack called "evil twin"?
A. MAC Spoofing
B. ARP poisoning
C. Rogue access point *
D. Session hijacking
16. Which of the following is a passive wireless discovery tool?
A. NetStumbler
B. Airerack
C. Kismet *
D. Netsniff
17.What is another term for turning off the SSID broadcast?
A. SSID stealth
B. SSID unicast
C. SSID cloaking *
D. SSID Sec
18 Which is the correct syntax to include comment in an HTML document?
A. //
B. /* Comment */
C. // Comment //
D. <!-- Comment --> *
19 Which element/tag defines a paragraph?
A. <p> *
B. <pre>
C. <panel>
D. None of the above
20.PGP encrypts data by using a block cipher called ______
a) international data encryption algorithm *
b) private data encryption algorithm
c) internet data encryption algorithm
d) local data encryption algorithm
21.What is Wired Equivalent Privacy (WEP)?
a) security algorithm for ethernet
b) security algorithm for wireless networks *
c) security algorithm for usb communication
d) security algorithm for emails
22.UTXO stands for ___.
A. Unspent Transaction Office
B.United Transaction Office
C.United Transaction Output
D.Unspent Transaction Output *
23.Blockchain and Bitcoin are both same.
a. True
b. False *
c. Neither False nor True
d. Cannot Determine
24.Which of the following is not a blockchain component?
a. Ledger
b. Wallet
c. Certificate authority *
d. Hash
25. Identify one of the types of the blockchain network.
a. Open blockchain network
b. Constraint blockchain network
c. Private blockchain network *
d. Restricted blockchain network
26.A proxy firewall filters at _________
a) Physical layer
b) Data link layer
c) Network layer
d) Application layer
27.A stateful firewall maintains a ___________ which is a list of active connections.
a) Routing table *
b) Bridging table
c) State table
d) Connection table
28.ICMP is used in _________
a) Ping
b) Traceroute
c) Ifconfig
d) Both Ping & Traceroute *
29.Which of the following is an advantage of anomaly detection?
a) Rules are easy to define
b) Custom protocols can be easily analyzed
c) The engine can scale as the rule set grows *
d) Malicious activity that falls within normal usage patterns is detected
30.What is the purpose of a shadow honeypot?
a) To flag attacks against known vulnerabilities
b) To help reduce false positives in a signature-based IDS
c) To randomly check suspicious traffic identified by an anomaly detection system *
d) To enhance the accuracy of a traditional honeypot
31.RTP is used to ________
a) carry the media stream *
b) monitor transmission statistics of streams
c) monitor quality of service of streams
d) secure the stream
You might also like
- Iot MCQDocument18 pagesIot MCQShweta kumbharNo ratings yet
- Iot MCQDocument10 pagesIot MCQRui ManjrekarNo ratings yet
- Unit 1 & 2 – Objective Type Questions and Answers on Computer NetworksDocument18 pagesUnit 1 & 2 – Objective Type Questions and Answers on Computer NetworksNAGARAJ GNo ratings yet
- Hcia Security Mock PDFDocument5 pagesHcia Security Mock PDFIct lab0% (1)
- Penetration Testing Multiple Choice Questions - Yeah HubDocument24 pagesPenetration Testing Multiple Choice Questions - Yeah HubKiran MudaliyarNo ratings yet
- SNA Bullet 10 MCQS-50: Which Types of Network Hardware Does Linux Support ?Document11 pagesSNA Bullet 10 MCQS-50: Which Types of Network Hardware Does Linux Support ?Mursaleen UmerNo ratings yet
- Soal UAS IT SecurityDocument5 pagesSoal UAS IT SecurityDiki RasaptaNo ratings yet
- Fraud Chapter 14Document3 pagesFraud Chapter 14Jeffrey O'LearyNo ratings yet
- NS QB Unit-1Document4 pagesNS QB Unit-1Syed ZubairNo ratings yet
- Introduction to Cyber SecurityDocument8 pagesIntroduction to Cyber Securityrahulbias.dbgNo ratings yet
- Draft InternHiringQuestionnaireDocument8 pagesDraft InternHiringQuestionnaireShekhar SumanNo ratings yet
- Accenture Mcq's Cloud NW MsofficeDocument32 pagesAccenture Mcq's Cloud NW MsofficeSai KethavarapuNo ratings yet
- Q.no 1. Which of The Following Is Billing and Account Management Service ?Document362 pagesQ.no 1. Which of The Following Is Billing and Account Management Service ?Harshal ChaudharyNo ratings yet
- Assessment test paper - A internet basics authentication questionsDocument5 pagesAssessment test paper - A internet basics authentication questionsamrita singNo ratings yet
- What Are The Advantages of Address Translation Techniques Included? (Multiple Choice)Document46 pagesWhat Are The Advantages of Address Translation Techniques Included? (Multiple Choice)Rachid AbdelNo ratings yet
- CEH Sample Questions For PractiseDocument8 pagesCEH Sample Questions For PractisevijayNo ratings yet
- information-security [set 1]Document11 pagesinformation-security [set 1]raval.sunil955No ratings yet
- 320 - Computer Security - R - 2021Document12 pages320 - Computer Security - R - 2021avfg gfavd100% (1)
- Introduction to Computer Security and TrendsDocument11 pagesIntroduction to Computer Security and TrendsBen TenNo ratings yet
- MCQ 1Document32 pagesMCQ 1AshishNo ratings yet
- Cyber Security MCQDocument9 pagesCyber Security MCQPriti Patil50% (2)
- Answer 2Document5 pagesAnswer 2Yohannes bekeleNo ratings yet
- Ict DiagnosticDocument3 pagesIct DiagnosticJoshua GuiriñaNo ratings yet
- Solution Network Essential Guide ch1 09Document4 pagesSolution Network Essential Guide ch1 09Hussain MirNo ratings yet
- MCQ CN (6 Test)Document4 pagesMCQ CN (6 Test)Anil BegarNo ratings yet
- NSQ 1Document4 pagesNSQ 1Mithun MangaloreNo ratings yet
- ESIOT 5 Set With AnswersDocument63 pagesESIOT 5 Set With AnswersSpiderspider2021No ratings yet
- Q.no 1. Information Model Adds More Details To The Virtual Entities by Defining Their - and RelationsDocument163 pagesQ.no 1. Information Model Adds More Details To The Virtual Entities by Defining Their - and RelationsAdeshNo ratings yet
- Sheet 2Document6 pagesSheet 2Amir TarekNo ratings yet
- Computer Networks Mcq-1Document21 pagesComputer Networks Mcq-1Sreyas KNo ratings yet
- Domain 4 QuestionsDocument10 pagesDomain 4 QuestionsRajaram K.VNo ratings yet
- Computer Communication & NetworkDocument14 pagesComputer Communication & NetworkDisha SharmaNo ratings yet
- Tyit Iot Mcqs (E-Next - In)Document26 pagesTyit Iot Mcqs (E-Next - In)glen mnx100% (1)
- Net1130 Final Study Part 1Document62 pagesNet1130 Final Study Part 1robpierce78No ratings yet
- Module1 - ExamDocument6 pagesModule1 - ExamAdnan MuçiqiNo ratings yet
- Artificial Intelligence and Digital Evidence TopicsDocument13 pagesArtificial Intelligence and Digital Evidence TopicsSpiderspider2021No ratings yet
- Assessment TestDocument7 pagesAssessment TestMohammed Sabeur GHARBINo ratings yet
- Question BankDocument12 pagesQuestion Banks.istr.u.nk.e.r.icbNo ratings yet
- CompTIA SY0-301 100-Question Practice ExamDocument28 pagesCompTIA SY0-301 100-Question Practice ExamMichael RoseNo ratings yet
- B. Coaxial CableDocument6 pagesB. Coaxial Cablemeymuna100% (1)
- MCQs For SComputerDocument15 pagesMCQs For SComputerzawiyartariqNo ratings yet
- Internet QuestionsDocument10 pagesInternet QuestionsAkhil AggarwalNo ratings yet
- 320 - Computer Security - R - 2018Document10 pages320 - Computer Security - R - 2018avfg gfavdNo ratings yet
- MCQ On Computer Network - CS601Document7 pagesMCQ On Computer Network - CS601SAFIKURESHI MONDAL100% (1)
- 9tut Q&aDocument40 pages9tut Q&alucaluca2No ratings yet
- MCQsDocument16 pagesMCQsmanobillimano613No ratings yet
- Networking Multiple Choice Questions: A) Error and Diagnostic FunctionsDocument36 pagesNetworking Multiple Choice Questions: A) Error and Diagnostic FunctionsAhmed HashimNo ratings yet
- Network MCQDocument36 pagesNetwork MCQAhmed HashimNo ratings yet
- Information Cyber Security [Set 1]Document21 pagesInformation Cyber Security [Set 1]Atul GaikwadNo ratings yet
- Ethical MCQDocument12 pagesEthical MCQRik AntonovoNo ratings yet
- Hands On Ethical Hacking and Network DefenseDocument5 pagesHands On Ethical Hacking and Network DefenseAjmal Qala100% (1)
- Internet MCQsDocument8 pagesInternet MCQstamoorqureshiNo ratings yet
- Cyber Security Module - IDocument7 pagesCyber Security Module - IAbhishek ChavanNo ratings yet
- Zonal Telecom Training Centre, KalyaniDocument10 pagesZonal Telecom Training Centre, KalyaniArun Kumar PatelNo ratings yet
- C. Port Scanning, Banner Grabbing, Service Identification: D. IDS LogDocument30 pagesC. Port Scanning, Banner Grabbing, Service Identification: D. IDS LogEkaNo ratings yet
- Practice - Exam 1Document7 pagesPractice - Exam 1Sakhawat AliNo ratings yet
- Iron ManDocument1 pageIron Man4AL19CS059 BHAGYASREENo ratings yet
- Import Numpy As NPDocument4 pagesImport Numpy As NP4AL19CS059 BHAGYASREENo ratings yet
- Tushit - s12652 020 01911 5Document11 pagesTushit - s12652 020 01911 54AL19CS059 BHAGYASREENo ratings yet
- Blockchain Security Attacks, Challenges, and Solutions For The Future Distributed Iot NetworkDocument22 pagesBlockchain Security Attacks, Challenges, and Solutions For The Future Distributed Iot NetworkNon PhetsomphouNo ratings yet
- Chap 7Document35 pagesChap 7Nizar TayemNo ratings yet
- Awfpc 2022Document7 pagesAwfpc 2022Jay-p BayonaNo ratings yet
- Syllabus For ETABSDocument2 pagesSyllabus For ETABSSandgrouse RajNo ratings yet
- Input Interfaces - Locate LPN LockDocument22 pagesInput Interfaces - Locate LPN LockSatyanarayana NekkantiNo ratings yet
- Body in Movement - WorkshopDocument8 pagesBody in Movement - WorkshopAndrew CareyNo ratings yet
- Mercedes 220 AirmaticDocument7 pagesMercedes 220 AirmaticadinxNo ratings yet
- DQFAQsDocument8 pagesDQFAQsBhagyashree kawaleNo ratings yet
- Male Hijab: Cover in RighteousnessDocument11 pagesMale Hijab: Cover in RighteousnessIbn SadiqNo ratings yet
- CCPDocument2 pagesCCPsanojmk2004No ratings yet
- Ruminations by Other PeopleDocument31 pagesRuminations by Other PeopledhultstromNo ratings yet
- BMEn 3301 Spring 2013 SyllabusDocument13 pagesBMEn 3301 Spring 2013 SyllabussfairhuNo ratings yet
- Tafila Technical University Course Syllabus for Manufacturing Processes (1) / Metal CuttingDocument4 pagesTafila Technical University Course Syllabus for Manufacturing Processes (1) / Metal CuttingG. Dancer GhNo ratings yet
- MCM SQL PDFDocument8 pagesMCM SQL PDFJeyakumar NarasingamNo ratings yet
- ZEOLITEDocument13 pagesZEOLITEShubham Yele100% (1)
- CH2 Related Disciplines - Gass & Selinker, 2008Document11 pagesCH2 Related Disciplines - Gass & Selinker, 2008Víctor ManzanaresNo ratings yet
- BEETLE /M-II Plus: POS System For The Highest Standards of PerformanceDocument2 pagesBEETLE /M-II Plus: POS System For The Highest Standards of PerformanceHeather JensenNo ratings yet
- Data CollectionDocument4 pagesData CollectionjochukoNo ratings yet
- Gas Turbine Flow MeterDocument33 pagesGas Turbine Flow MeterKhabbab Hussain K-hNo ratings yet
- Rossetto Et AlDocument21 pagesRossetto Et AlEunice FiecasNo ratings yet
- Fire and Ice by Robert FrostDocument2 pagesFire and Ice by Robert Frostapi-561976496No ratings yet
- S/4HANA Margin Analysis, Predictive Accounting, and Continuous CloseDocument27 pagesS/4HANA Margin Analysis, Predictive Accounting, and Continuous Closessbhagat001No ratings yet
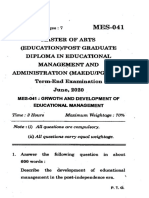
- Master of Arts (Education) /post Graduate Diploma in Educational Management and Administration (Maedu/Pgdema) Term-End Examination June, 2020Document7 pagesMaster of Arts (Education) /post Graduate Diploma in Educational Management and Administration (Maedu/Pgdema) Term-End Examination June, 2020Shreyashi Santra MitraNo ratings yet
- Detector Balance Induccion.Document11 pagesDetector Balance Induccion.Jesus OrtizNo ratings yet
- Periodic Table: Oakland Schools Chemistry Resource UnitDocument42 pagesPeriodic Table: Oakland Schools Chemistry Resource UnitAnum TauqirNo ratings yet
- How To Avoid PlagiarismDocument2 pagesHow To Avoid PlagiarismShiny Deva PriyaNo ratings yet
- (Historical Materialism Book Series 32) Lapavitsas, Costas - Financialisation in Crisis (2012, Brill Academic Pub)Document276 pages(Historical Materialism Book Series 32) Lapavitsas, Costas - Financialisation in Crisis (2012, Brill Academic Pub)monikaNo ratings yet
- E44 - Wet Cooling Tower: InstructionsDocument3 pagesE44 - Wet Cooling Tower: InstructionsMarc AnmellaNo ratings yet
- Fundamentals WindDocument67 pagesFundamentals WindwlyskrdiNo ratings yet
- Lab Manual Ds&BdalDocument100 pagesLab Manual Ds&BdalSEA110 Kshitij BhosaleNo ratings yet
- Tracing Chronic Fatigue Syndrome Tsfunction Is Key To ME - CFS - B Day PDFDocument91 pagesTracing Chronic Fatigue Syndrome Tsfunction Is Key To ME - CFS - B Day PDFsanthigiNo ratings yet


















![information-security [set 1]](https://imgv2-2-f.scribdassets.com/img/document/724520849/149x198/4c1536e8a3/1713499604?v=1)































![Information Cyber Security [Set 1]](https://imgv2-1-f.scribdassets.com/img/document/719581554/149x198/da0db1deb2/1712131401?v=1)