Professional Documents
Culture Documents
Steganography
Uploaded by
Nidaa Flaih0 ratings0% found this document useful (0 votes)
29 views28 pagesOriginal Title
steganography
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
29 views28 pagesSteganography
Uploaded by
Nidaa FlaihCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 28
Watermarking & Steganography
ITM 604
Communications, Networking and Security
Sanjay Goel
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Cryptograpy & Steganography vs. Watermarking
Comparison
• Cryptography is about protecting the content of
messages (their meaning).
• Steganography is about concealing the existence of
messages
• Watermarking is about establishing identity of
information to prevent unauthorized use
– They are imperceptible
– They are inseparable from the works they are embedded in
– They remain embedded in the work even during
transformation
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
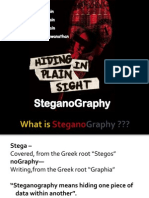
Steganography
Basics
• The word steganography comes from the Greek steganos ,
meaning covered or secret, and graphy , meaning writing or
drawing. Therefore, steganography literally means covered
writing.
• Steganography simply takes one piece of information and
hides it within another
– Computer files (images, sounds recordings, even disks) contain
unused or insignificant areas of data
– Steganography takes advantage of these areas, replacing them with
information (encrypted mail, for instance).
– The files can then be exchanged without anyone knowing what really
lies inside of them
– An image of the space shuttle landing might contain a private letter to
a friend.
– Rumor has it that terrorists used steganography to transmit messages
to one another. (http://www.wired.com/news/politics/0,1283,41658,00.html)
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Reference: http://members.tripod.com/steganography/stego.html
Steganography
Early Examples
In his history of the Persian
Wars, Herodotus tells of a
messenger who shaved his head
and allowed a secret message to
be tattooed on his scalp. He
waited until his hair grew back.
Then he journeyed to where the
recipient awaited him and shaved
his head again. The message was
revealed. It was history’s first use
of steganography.
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Steganography
Invisible Ink
Ancient Romans used to write
between lines using invisible ink
based on various natural
substances such as fruit juices,
urine, and milk. Their experience
was not forgotten: even
nowadays children play spies and
write secret messages that appear
only when heated.
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Steganography
Invisible Ink
During the World War II the
Germans developed the microdot.
A secret message was
photographically reduced to the
size of a period, and affixed as the
dot for the letter 'i' or other
punctuation on a paper containing
a written message. Microdots
permitted the transmission of
large amounts of printed data,
including technical drawings, and
the fact of the transmission was
effectively hidden.
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Steganography
Principles
• Computer Steganography is based on two principles.
– The first one is that the files containing digitized images or
sound can be altered to a certain extend without loosing
their functionality.
– The other principle deals with the human inability to
distinguish minor changes in image color or sound quality,
which is especially easy to make use of in objects that
contain redundant information, be it 16-bit sound, 8-bit or
even better 24-bit image. The value of the least significant
bit of the pixel color won’t result in any perceivable
change of that color.
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Steganography
Process
• The data to be concealed is compressed and hidden within
another file.
• The first step is to find a file which will be used to hide the
message (also called a carrier or a container.)
• The next step is to embed the message one wants to hide
within the carrier using a steganographic technique.
• Two different techniques commonly used for embedding are:
– Replace the least significant bit of each byte in the [carrier] with a
single bit for the hidden message.
– Select certain bytes in which to embed the message using a random
number generator; resampling the bytes to pixel mapping to preserve
color scheme, in the case of an image...; hiding information in the
coefficients of the discrete cosine, fractal or wavelet transform of an
image; and applying mimic functions that adapt bit pattern to a given
statistical distribution."
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Steganography
Software
• EZStego (Stego Online, Stego Shareware, Romana Machado)
– Java based software program which supports only GIF and PICT
formats;
• Gif-It-Up v1.0 (Lee Nelson)
– A stego program for Windows 95 that hides data in GIF files
• Hide and Seek (Colin Maroney)
– can hide any data into GIF images;
• JPEG-JSTEG (Derek Upham)
– can hide data inside a JPEG file
• MP3Stego (Fabien A.P. Petitcolas, Computer Laboratory, University
of Cambridge)
– can hide data inside MP3 sound files;
• Steganos (Demcom, Frankfurt, Germany)
– encrypts files and then hides them within BMP, DIB, VOC, WAV,
ASCII and HTML files.
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Reference:http://www.antichildporn.org/steganog.html
Steganography Software
S-Tools
• S-Tools is one of the most popular steganography tools.
– This program is Windows 95/98 compatible
– It has the ability to conceal files within BMP, GIF and WAV files.
– Allows you to simply point and click your way to hiding files.
– It also has the ability to hide multiple files in one container.
– It has been updated each year and can be easily downloaded by
anyone. (http://members.tripod.com/steganography/stego/software.html)
Dear Susan:
I can wait no
longer I want to see you
now please say that you
will come.
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
San...
Steganalysis
Basics
• Steganalysis is the art of discovering and rendering
useless such covert messages.
• Steganalysis involves analysis of the carrier file
– Simpler steganographic techniques produce some
discernible change in the file size, statistics or both.
– These changes can manifest themselves in color variations,
loss of resolution and other distortions that are visible to
the human eye.
– This form of detection requires that you know what the
original carrier image or file should look like.
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Watermarking
Basics
• Watermarking is the practice of hiding a
message about an image, audio clip, or other
work of media within the work itself.
– Watermark is hidden from the user in normal use
– Watermark becomes visible as a result of a special
viewing process
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Watermarking
Examples
• Sending a message to a spy by marking certain letters
in a newspaper using invisible ink
• Adding sub-perceptible echo at certain places in an
audio recording.
• Embedding a picture of President Andrew Jackson
into the paper during paper making process.
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Watermarking
Examples
“In 1981, photographic reprints of confidential British
Cabinet Documents were being printed in newspapers.
Rumor has it that to determine the source of the leak,
Margaret Thatcher arranged to distribute uniquely identifiable
copies of the documents to each of the ministers. Each copy had
a different word spacing that was used to encode the identity of
the recipient.”
- Digital Watermarking, Cox
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Digital Watermarking
Basics
• A digital watermark is a digital signal or pattern
inserted into a digital image.
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Watermarking
Applications
• In a broadcast monitoring system identifying data is
added to the video/audio signal prior to transmission
• Two kinds of monitoring systems exist
– Passive Monitoring:
• Recognize the content being broadcast
• Compares received signals against a database of known content
• Very expensive as large frames need to be compared
• Useful for monitoring of competition
– Active Monitoring:
• Rely on information that is broadcast along with the content
• Relatively easier to implement
• Identification information is easily to interpret
• Requires cooperation of broadcasting mechanism
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Watermarking
Owner Identification
• Under US law the creator of a story, painting, song, or any
other original work holds copyright the instant it is recorded
in some physical form
– Up to 1998 a copyright notice was required to be attached to each
distributed copy if the owner wanted to protect his/her rights
– Even after the change in 1998 when this is no longer required the
awards are reduced significantly if the copyright information is not
present with the work
• Textual Copyright notices have several limitations
– They are easy to remove deliberately or inadvertently
– They can be aesthetically ugly if they cover a part of the image
– For music the copyright is only on the media not on the work
• Electronic watermarks are imperceptible and inseparable from
the work they are contained and are hence superior
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Watermarking
Proof of Ownership
• Textual notices can be erased and replaced by a forger
– Image editors can be used to edit copyright notices
– One solution is to register the image with copyright
depository (expensive)
• Watermarking can prove image identity
– Watermarks may also be altered
– It is possible to prove that one image is derived from
another indirectly proving the ownership
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Watermarking
Other Applications
• Transaction Tracking
• Content Authentication
• Copy Control
• Device Control
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Image Watermarking
Properties
• Should be perceptually invisible to prevent obstruction of the
original image.
• Statistically invisible so it cannot be detected or erased.
• Simple to extract watermark from image
– Otherwise, the detection process requires too much computation
time.
• Detection should be accurate.
– Few false positives & false negatives
• Should be able to produce numerous watermarks.
– Otherwise, only a limited number of images may be marked.
• Should be robust to filtering, additive noise, compression, and
other forms of image manipulation.
• Should be able to determine the true owner of the image.
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Watermarking
Process
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Reference: http://www.ece.utexas.edu/~bevans/courses/ee381k/projects/fall98/fu/literatureSurvey.pdf
Image Watermarking
Techniques
• M-Sequence Generator
– Embedded or added to the last significant digit of the original image
– Watermark was extracted by taking the least significant bits at specific
locations
– Detection was done by cross correlation of the original and extracted
watermarks
• Discrete Cosine Transform (DCT)
– Watermark was placed in perpetually significant areas of the image
– Watermark based on 1000 random samples of a N(0,1) distribution
– Sample was added to the 1000 largest DCT coefficients of the image
– Inverse DCT was taken to retrieve the watermarked image
– For detection watermark was extracted from the DCT of suspected
image
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Image Watermarking
Techniques
• Discrete Wavelet Transform(DWT)
– Watermark modeled as Gaussian noise was added to
middle and high frequency bands of the image
– Decoding process involved taking DWT of potentially
marked image
• Fractal Codes
– A collage map was composed from 8x8 blocks of original
image and from image’s DCT
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Watermarking
Image
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Watermarking
Image
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Watermarking
Audio Properties
• Perceptually inaudible,
– such that no perceptual quality degradation occurs
• Statistically undetectable
– To ensure security
• Cannot be removed or modified by any signal
processing operation (e.g. filtering, compression,
MP3-encoding,...) without degrading perceptual
quality
• Readily extractable to detect copyright information
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Watermarking
Audio Techniques
• Echo Coding
• Phase Coding
• Direct-Sequence Spread Spectrum
• Frequency-Hopped Spread Spectrum
• Frequency Masking
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
Watermarking
Audio
Original Sound Original Sound
Watermarked Sound Watermarked Sound
Echo Coding Frequency Hopped Spread Spectrum
• Wideband Audio Signal is a raw WAV file
- Ten seconds in length
- Sampled at 44.1 kHz
- Quantized to 16 bits per sample
Sanjay Goel, ITM Department, School of Business, SUNY, Albany
You might also like
- 8-Steganography Kshitij 2Document21 pages8-Steganography Kshitij 2Sourabh SoniNo ratings yet
- WatermarkingDocument30 pagesWatermarkingfantasticlala06No ratings yet
- 100314Document8 pages100314vol2no3No ratings yet
- Seminar On Steganography: K.VISHNU MURTHY (18N81A05C5)Document21 pagesSeminar On Steganography: K.VISHNU MURTHY (18N81A05C5)mahera KhatoonNo ratings yet
- An Introduction To Image Steganography TechniquesDocument15 pagesAn Introduction To Image Steganography TechniquesDeeNo ratings yet
- Ijcii 3-3-118Document6 pagesIjcii 3-3-118v3rajasekarNo ratings yet
- Steganography: Submitted By: Nawlendu BhushanDocument23 pagesSteganography: Submitted By: Nawlendu BhushanNawlendu BhushanNo ratings yet
- A Comparative Study of Audio Steganography Techniques PDFDocument6 pagesA Comparative Study of Audio Steganography Techniques PDFUtsav GuptaNo ratings yet
- Steganography PPT!!!Document30 pagesSteganography PPT!!!skumar_293596No ratings yet
- Steganography 1Document7 pagesSteganography 1joby georgeNo ratings yet
- Analysis of Various Image Steganography Techniques: Dr. Amit Chaturvedi Malik AijazDocument7 pagesAnalysis of Various Image Steganography Techniques: Dr. Amit Chaturvedi Malik AijazAftab AalamNo ratings yet
- Image SteganographyDocument43 pagesImage SteganographyGeetha Sokkian Rammanohar50% (4)
- Fdocuments - in About SteganographyDocument27 pagesFdocuments - in About SteganographyABHISHEK TOPIWALANo ratings yet
- Project PythonDocument22 pagesProject Pythonmahe140% (1)
- Advanced Image HidingDocument15 pagesAdvanced Image HidingDahlia DevapriyaNo ratings yet
- SteganographyDocument63 pagesSteganographySri KrishnaNo ratings yet
- Comparative Study of Image Steganography TechniquesDocument5 pagesComparative Study of Image Steganography TechniquesseventhsensegroupNo ratings yet
- SynopsisDocument2 pagesSynopsisSiddhant1741991No ratings yet
- A Survey On Image Steganography Types and Hiding TechniquesDocument6 pagesA Survey On Image Steganography Types and Hiding TechniquesInternational Journal of Trendy Research in Engineering and TechnologyNo ratings yet
- Major ProjectDocument19 pagesMajor ProjectNikhil BudhirajaNo ratings yet
- Steganography: by G.Krishna 17A81A0569Document18 pagesSteganography: by G.Krishna 17A81A0569Bhargav NanIENo ratings yet
- Steganography PresentationDocument15 pagesSteganography PresentationhiraL_patel936No ratings yet
- Steganography 2Document18 pagesSteganography 2ShahrukhNo ratings yet
- ZX WPS OfficeDocument8 pagesZX WPS OfficeAkhil P StanlyNo ratings yet
- IJSRP Paper Submission Format Double ColumnDocument5 pagesIJSRP Paper Submission Format Double Column20EC144 TejasviNo ratings yet
- SteganographyDocument22 pagesSteganographyEkta Bende0% (1)
- Ijser: Case Study of Hiding A Text Using Video SteganographyDocument5 pagesIjser: Case Study of Hiding A Text Using Video SteganographyAniket WableNo ratings yet
- Steganography PaperDocument6 pagesSteganography PaperHarit SoniNo ratings yet
- Steganography: - A Word Document Might Be Hidden Inside of AnDocument17 pagesSteganography: - A Word Document Might Be Hidden Inside of AnSnehal SolankeNo ratings yet
- Steganography: Presented By: Surbhi GosainDocument30 pagesSteganography: Presented By: Surbhi GosainSurbhi GosainNo ratings yet
- Progress Report CSE-1-50Document14 pagesProgress Report CSE-1-50Dhruv GoelNo ratings yet
- Audio Files and 4612Document18 pagesAudio Files and 4612Jeyapirashath SakthithasanNo ratings yet
- Video Steganography ProjectDocument3 pagesVideo Steganography ProjectDeepak KumarNo ratings yet
- Overview of Secure Data Transmission Using SteganographyDocument4 pagesOverview of Secure Data Transmission Using SteganographyNawfal BahriaNo ratings yet
- Seminar ReportDocument29 pagesSeminar ReportHarshada ChapreNo ratings yet
- ASurveyofImageSteganographyTechniques IJAST 2013Document13 pagesASurveyofImageSteganographyTechniques IJAST 2013Everyone DiesNo ratings yet
- Audio Steganography in Wavelet Domain - A Survey: Jisna Antony Sobin C. C Sherly A. PDocument5 pagesAudio Steganography in Wavelet Domain - A Survey: Jisna Antony Sobin C. C Sherly A. PcheintNo ratings yet
- TECNICA ITALIANA-Italian Journal of Engineering Science: Received: 6 November 2020 Accepted: 27 January 2021Document7 pagesTECNICA ITALIANA-Italian Journal of Engineering Science: Received: 6 November 2020 Accepted: 27 January 2021PHANTOME FFNo ratings yet
- Steganalysis Using Colour Model ConversionDocument11 pagesSteganalysis Using Colour Model ConversionsipijNo ratings yet
- SynopsisDocument11 pagesSynopsisArushi SaklaniNo ratings yet
- Adaptive Steganography Based On TexturesDocument8 pagesAdaptive Steganography Based On Texturesmiracle AtianashieNo ratings yet
- 187 - Steganography For Secure CommunicationDocument4 pages187 - Steganography For Secure CommunicationPriya LohakareNo ratings yet
- INTRODUCTIONDocument11 pagesINTRODUCTIONAnkit TripathiNo ratings yet
- SSRN Id3171494Document17 pagesSSRN Id3171494rube nobeNo ratings yet
- DWT ReportDocument37 pagesDWT ReportsankarideviNo ratings yet
- Steganography NotesDocument13 pagesSteganography NotesakshayNo ratings yet
- Evaluation of Best Steganography Tool Using Image Features: Jensi Lakdawala, Jiya RankawatDocument9 pagesEvaluation of Best Steganography Tool Using Image Features: Jensi Lakdawala, Jiya RankawatazmiNo ratings yet
- Wavelet Transform Color Image SteganographyDocument29 pagesWavelet Transform Color Image SteganographyAlly KhanNo ratings yet
- Media SteganographyDocument8 pagesMedia Steganographyalisdrizwan959No ratings yet
- Video Steganography: A Comprehensive ReviewDocument32 pagesVideo Steganography: A Comprehensive ReviewSparsh RathourNo ratings yet
- Digital Image Steganography: Available Online at WWW - Interscience.inDocument4 pagesDigital Image Steganography: Available Online at WWW - Interscience.inClaudiu StanciuNo ratings yet
- Steganography Using Interpolation and LSB With Cryptography On Video Images-A ReviewDocument3 pagesSteganography Using Interpolation and LSB With Cryptography On Video Images-A ReviewATSNo ratings yet
- Steganography: Khan, Mohammed MinhajuddinDocument13 pagesSteganography: Khan, Mohammed MinhajuddinShivaEshwariNo ratings yet
- Basic Steganography ReportDocument11 pagesBasic Steganography ReportAkash KumarNo ratings yet
- Ethical Hacking Project of Final YearDocument13 pagesEthical Hacking Project of Final Year6743 SINGH VAISHALINo ratings yet
- Analysis of Different Steganographic Algorithms For Secured Data HidingDocument7 pagesAnalysis of Different Steganographic Algorithms For Secured Data HidingKamau GabrielNo ratings yet
- SteganographyDocument23 pagesSteganographyEr Uttam JainNo ratings yet
- High Capacity and Lossless Steganography Using Discrete Cosine TransformDocument6 pagesHigh Capacity and Lossless Steganography Using Discrete Cosine TransformerpublicationNo ratings yet
- Human Visual System Model: Understanding Perception and ProcessingFrom EverandHuman Visual System Model: Understanding Perception and ProcessingNo ratings yet
- Cave of ShadowsDocument3 pagesCave of ShadowsMichael KnappNo ratings yet
- Vocabulary 7 Reading ComprehensionDocument1 pageVocabulary 7 Reading ComprehensionFreddy Benjamin Sepulveda TapiaNo ratings yet
- The Sims 2Document4 pagesThe Sims 2Noel MacapulayNo ratings yet
- MLQHS - Certification - List of EstablishmentsDocument2 pagesMLQHS - Certification - List of EstablishmentsBplo CaloocanNo ratings yet
- 9 - Creative Writing Short Stories VocabularyDocument11 pages9 - Creative Writing Short Stories VocabularyMariaNo ratings yet
- Thí sinh lưu ý: a. Làm bài trên Phiếu Trả Lời (Answer sheet) b. Nộp bài làmDocument4 pagesThí sinh lưu ý: a. Làm bài trên Phiếu Trả Lời (Answer sheet) b. Nộp bài làmViệt AnNo ratings yet
- Dwarf Fortress 101: Lesson 1 - Getting Set UpDocument16 pagesDwarf Fortress 101: Lesson 1 - Getting Set UpOneDeadPixelNo ratings yet
- No Gym No Problem - (Spreads) PDFDocument101 pagesNo Gym No Problem - (Spreads) PDFexpatrickdale2427No ratings yet
- Half A Century of ChessDocument286 pagesHalf A Century of Chessandrewpiano100% (3)
- Parts Manual - SoNALIKA WorldTrac 60 75 90 PDFDocument578 pagesParts Manual - SoNALIKA WorldTrac 60 75 90 PDFkvsj2001No ratings yet
- Philips SPD2400L1 Update To Y5H4 InformationDocument6 pagesPhilips SPD2400L1 Update To Y5H4 Informationtonyj327No ratings yet
- Archdiocese of Caceres Parish of St. Dominic of Guzman: Ecclesiastical Award For ServiceDocument14 pagesArchdiocese of Caceres Parish of St. Dominic of Guzman: Ecclesiastical Award For ServiceMherl PaañoNo ratings yet
- Unit 5 Test: Listening, Vocabulary and GrammarDocument2 pagesUnit 5 Test: Listening, Vocabulary and GrammarAbidur rahmanNo ratings yet
- Dragon Antipaladin PDFDocument78 pagesDragon Antipaladin PDFJim JimjimNo ratings yet
- Solutions Manuals For Operations Management First Canadian Edition Jay Heizer Barry Render Paul GriffinDocument10 pagesSolutions Manuals For Operations Management First Canadian Edition Jay Heizer Barry Render Paul GriffinJaneRobinsonwmny100% (40)
- ArcadeFire EverythingNowDocument4 pagesArcadeFire EverythingNowLuigi PambianchiNo ratings yet
- Campfire Program PlannerDocument2 pagesCampfire Program PlannerkirktgravesNo ratings yet
- Pioneer VSX 418Document93 pagesPioneer VSX 418janussiNo ratings yet
- Defiant Awakening: Angel: CourtiersDocument2 pagesDefiant Awakening: Angel: CourtiersJean-Patrick Cacereco BerthiaumeNo ratings yet
- Reported Speech Exercises 2Document5 pagesReported Speech Exercises 2martagomezsanisidro100% (1)
- Handout Past SimpleDocument1 pageHandout Past SimpleMariana GereliukNo ratings yet
- Template Proposal P2MWDocument11 pagesTemplate Proposal P2MWRanti nemNo ratings yet
- Atkins Made EasyDocument16 pagesAtkins Made EasyIxchel SélavyNo ratings yet
- Worksheet From British CouncilDocument6 pagesWorksheet From British CouncilCelestina TanNo ratings yet
- Bobcat T2556 Hydraulic Schematic PDFDocument3 pagesBobcat T2556 Hydraulic Schematic PDFAnonymous HxADrI1bNo ratings yet
- Partes de Una Oficina de Contabilidad en InglesDocument11 pagesPartes de Una Oficina de Contabilidad en InglesAvigail de GramajoNo ratings yet
- The Construction of Spiritual Identity in CyberspaceDocument23 pagesThe Construction of Spiritual Identity in CyberspaceTheo ZijderveldNo ratings yet
- NOTA Hosts ScriptDocument15 pagesNOTA Hosts ScriptGabriella VenturinaNo ratings yet
- Business Lunch Japazonico MergedDocument2 pagesBusiness Lunch Japazonico MergedBsnNo ratings yet
- Dave Brubeck Take Five Saxo AltoDocument5 pagesDave Brubeck Take Five Saxo AltoChepenhauer KalashnikovNo ratings yet