Professional Documents
Culture Documents
Cyberdin-Example Report
Uploaded by
Miloš UrbišOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Cyberdin-Example Report
Uploaded by
Miloš UrbišCopyright:
Available Formats
Find the vulnerabilities before hackers do. Always be a few steps ahead.
Cyberdin
Web Application Penetration Test Report
CYBERDIN © 2010-2012 All Rights Reserved contact@cyberdin.com | www.cyberdin.com
Find the vulnerabilities before hackers do. Always be a few steps ahead.
Introduction
This report holds the results of a web application security scan performed on the
Test-Website.com application.
CYBERDIN provides customized security solutions to support the integrity of
your environment. These assessments aim to unconver any security issues in the
scanned web application, explain the impact and risks associated with the found
issues, and provide guidance in the prioritization and remediation steps.
Using CYBERDIN services, you can identify security holes in Web Applications
and Network based systems.
CYBERDIN was not provided with access credentials for the application and an
overview of the application.
This report relates to the testing against the Test-Website.com application from
the perspective of an unauthorized attacker.
CYBERDIN © 2010-2012 All Rights Reserved contact@cyberdin.com | www.cyberdin.com
Find the vulnerabilities before hackers do. Always be a few steps ahead.
Executive Summery
URL / IP: Test-Website.com
Check Type: Web Application
Check schedule: Single Check
CYBERDIN Threat Level: 5
The systems exposed to critical vulnerabilities.
Malicious user can exploit existing vulnerabilities and
perform hostile operations.
CYBERDIN © 2010-2012 All Rights Reserved contact@cyberdin.com | www.cyberdin.com
Find the vulnerabilities before hackers do. Always be a few steps ahead.
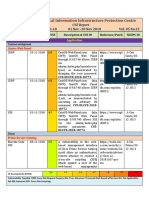
Vulnerability Severity Security Risk Recommendation More Info
SQL Injection Critical It is possible to execute SQL Parameterized statements must be used. http://en.wikipedia.org/
commands on the SQL Server thru User input must be carefully escaped or wiki/SQL_injection
the application. filtered.
eShoplifting High It is possible to steal goods or Do not relay on the client side parameters http://en.wikipedia.org/
services. for price calculations. Do not use Base- wiki/Shoplifting
64 for encoding price information.
Blind SQL High It is possible to execute SQL User input must not directly be embedded http://en.wikipedia.org/
Injection commands on the SQL Server thru in SQL statements. Instead, wiki/SQL_injection
the application. parameterized statements must be used.
User input must be carefully escaped or
filtered.
Cross Side High It is possible to steal or manipulate There are several issues whose http://en.wikipedia.org/
Scripting (XSS) customer session and cookies, which remediation lies in sanitizing user input. wiki/Cross-
may be used to impersonate a site_scripting
legitimate user.
LDAP Injection High This could result in the execution of There are several issues whose http://www.blackhat.co
arbitrary commands such as granting remediation lies in sanitizing user input. m/presentations/LDAP.
permissions to unauthorized users, pdf
and content modifications.
CAPTCHA Medium Could allow a remote attacker to Upgrade to newer version (if exists). http://www.cs.sfu.ca/~m
Bypass bypass the CAPTCHA Captcha image should be distorted, and ori/research/gimpy/
implementation, thus undermining cluttered and with textured background.
http://www.owasp.org/i
the security benefit of the The distortion and clutter is sufficient to
ndex.php/Testing_for_C
CAPTCHA technology. confuse OCR (optical character aptcha_(OWASP-AT-
recognition) software. 008)
Cross Site Medium Http Track & Trace enabled on the Disable the HTTP TRACE method in http://www.kb.cert.org/
Tracing web server. It is possible to steal or your web server. vuls/id/867593
manipulate customer session and
cookies, which may be used to
impersonate a legitimate user.
Application Low It is possible to gather sensitive Use generic error displaying. Use try and http://www.owasp.org/i
Errors debugging information. The attacker catch blocks. ndex.php/Missing_Error
can gain useful information from the _Handling
application's responses.
Hidden Informational It is possible to retrieve information If the forbidden resource is not required,
Directory about the site's file system structure, remove it from the site.
which may help the attacker to map
the web site.
CYBERDIN © 2010-2012 All Rights Reserved contact@cyberdin.com | www.cyberdin.com
Find the vulnerabilities before hackers do. Always be a few steps ahead.
Performed Attacks List
A L
Account lockout attack LDAP injection
Asymmetric resource consumption
M
B
Man-in-the-middle attack
Blind SQL Injection
Blind XPath Injection O
Brute force attack
Buffer overflow attack Overflow Binary Resource File
C P
CSRF Parameter Delimiter
Cache Poisoning Path Traversal
Command Injection
Cross Site Tracing
Cross-Site Request Forgery (CSRF)
R
Cross-site Scripting (XSS)
Resource Injection
Cryptanalysis
D S
SQL Injection
Denial of Service
Server-Side Includes (SSI) Injection
Direct Dynamic Code Evaluation
Session Prediction
('Eval Injection')
Session fixation
Double Encoding
Session hijacking attack
F
U
Forced browsing
Unicode Encoding
Format string attack
Full Path Disclosure
W
H
Web Parameter Tampering
HTTP Request Smuggling
HTTP Response Splitting X
XPATH Injection
CYBERDIN © 2010-2012 All Rights Reserved contact@cyberdin.com | www.cyberdin.com
Find the vulnerabilities before hackers do. Always be a few steps ahead.
Performed Tests List
Information Gathering Authentication Testing
Spiders, Robots and Crawlers Credentials transport over an encrypted
Search Engine channel
Discovery/Reconnaissance User enumeration
Identify application entry points Guessable (Dictionary) User Account
Testing for Web Application Brute Force Testing
Fingerprint Bypassing authentication schema
Application Discovery Vulnerable remember password and
Analysis of Error Codes password reset
Logout and Browser Cache
Configuration Management Testing Management
Weak Captcha implementation
SSL/TLS Testing (SSL Version, Multiple Factors Authentication
Algorithms, Key length, Digital Cert.
Validity) Session Management
DB Listener Testing
Infrastructure Configuration Bypassing Session Management
Management Testing Schema (Weaknesses in Session
Application Configuration Token)
Management Testing Testing for Cookies attributes (‘HTTP
File Extensions Handling Only’, ‘Secure’, and time validity)
Old, backup and unreferenced files Session Fixation
Infrastructure and Application Exposed Session Variables
Admin Interfaces CSRF – Cross Site Request Forgery
HTTP Methods and XST (Cross Site
Tracing) Authorization Testing
Path Traversal
Bypassing authorization schema
Privilege Escalation
CYBERDIN © 2010-2012 All Rights Reserved contact@cyberdin.com | www.cyberdin.com
Find the vulnerabilities before hackers do. Always be a few steps ahead.
Business logic testing Denial of Service Testing
Bypassing Business Logic SQL Wildcard Attacks
Locking Customer Accounts
Data Validation Testing DoS using Buffer Overflow
User Specified Object Allocation
Reflected Cross Site Scripting User Input as a Loop Counter
Stored Cross Site Scripting Writing User Provided Data to Disk
DOM based Cross Site Scripting Failure to Release Resources
Cross Site Flashing Storing too Much Data in Session
SQL Injection
LDAP Injection Web Services Testing
ORM Injection
XML Injection WS Information Gathering
SSI Injection Testing WSDL Weakness
XPath Injection XML Structural Testing
IMAP/SMTP Injection XML content-level Testing
Code Injection HTTP GET parameters/REST Testing
OS Commanding Naughty SOAP attachments
Buffer overflow Replay Testing
Incubated vulnerability
HTTP Splitting/Smuggling Ajax Testing
AJAX Vulnerabilities
AJAX Testing
CYBERDIN © 2010-2012 All Rights Reserved contact@cyberdin.com | www.cyberdin.com
Find the vulnerabilities before hackers do. Always be a few steps ahead.
Detailed Report
SQL Injection Vulnerability
Severity: Critical
Security Risk: It is possible to execute SQL commands on the SQL
Server thru the application.
Recommendation: User input must not directly be embedded in SQL
statements. Instead, parameterized statements must be
used. User input must be carefully escaped or filtered.
More Info: http://en.wikipedia.org/wiki/SQL_injection
Get Requests:
http://www.Test-Website.com/Products.aspx?item=1'%20having%201=1--
http://www.Test-Website.com/Products.aspx?cat=1%a5'%20having%201=1--
http://www.Test-Website.com/List-Products.aspx?prod=%00'
http://www.Test-Website.com/List-Products.aspx?cat=1'
http://www.Test-Website.com/Members.aspx?userid= \'
Server Response:
Microsoft OLE DB Provider for ODBC Drivers error '80040e14'
[Microsoft][ODBC SQL Server Driver][SQL Server]ORDER BY items must appear in the
select list if the statement contains a UNION operator.
/Products.aspx, line 5
CYBERDIN © 2010-2012 All Rights Reserved contact@cyberdin.com | www.cyberdin.com
Find the vulnerabilities before hackers do. Always be a few steps ahead.
eShoplifting Vulnerability
Severity: High
Security Risk: It is possible to steal goods or services.
Recommendation: Do not relay on the client side parameters for price
calculations. Do not use Base-64 for encoding price
information.
More Info: http://en.wikipedia.org/wiki/Shoplifting
Post Requests & Server Response:
CYBERDIN © 2010-2012 All Rights Reserved contact@cyberdin.com | www.cyberdin.com
Find the vulnerabilities before hackers do. Always be a few steps ahead.
Blind SQL Injection Vulnerability
Severity: High
Security Risk: It is possible to execute SQL commands on the SQL
Server thru the application.
Recommendation: User input must not directly be embedded in SQL
statements. Instead, parameterized statements must be
used. User input must be carefully escaped or filtered.
More Info: http://en.wikipedia.org/wiki/SQL_injection
Post Requests:
POST /Members/account.aspx HTTP/1.0
listAccounts=1001160141+and+1=1
POST /Members/account.aspx HTTP/1.0
listAccounts=1001160141+and+1=2
Server Response:
The resulting test responses show that requests containing conditions with the same logical
values were identical to the original valid response, and the responses with different values
were not. This indicates that an SQL query is being executed at the back-end database, and that
the injected values affect the original query.
CYBERDIN © 2010-2012 All Rights Reserved contact@cyberdin.com | www.cyberdin.com
Find the vulnerabilities before hackers do. Always be a few steps ahead.
Cross Side Scripting (XSS) Vulnerability
Severity: High
Security Risk: It is possible to steal or manipulate customer session
and cookies, which may be used to impersonate a
legitimate user.
Recommendation: There are several issues whose remediation lies in
sanitizing user input.
By verifying that user input does not contain hazardous
characters, it is possible to prevent malicious users
from causing your application to execute unintended
JavaScript code.
More Info: http://en.wikipedia.org/wiki/Cross-site_scripting
Get & Post Requests:
http://www. www.Test-
Website.com/Search.aspx?test=%3E%22%27%3E%3Cscript%3Ealert%281491%29%3C%2Fscript%3E
http:// www.Test-Website.com/Resource/controller.swf?onend=javascript:alert(XSS)//
POST /members.aspx HTTP/1.0
name=anonymous+user&text=>"'><img%20src%3D%26%23x6a;%26%23x61;%26%23x76;%26%23x6
1;%26%23x73;%26%23x63;%26%23x72;%26%23x69;%26%23x70;%26%23x74;%26%23x3a;alert(50
108)>&submit=add+message
POST /search.aspx?test=query HTTP/1.0
searchFor=>"'><img%20src%3D%26%23x6a;%26%23x61;%26%23x76;%26%23x61;%26%23x73;%2
6%23x63;%26%23x72;%26%23x69;%26%23x70;%26%23x74;%26%23x3a;alert(100783)>&goButton=
go
CYBERDIN © 2010-2012 All Rights Reserved contact@cyberdin.com | www.cyberdin.com
Find the vulnerabilities before hackers do. Always be a few steps ahead.
POST /secured/newuser.apsx HTTP/1.0
uuname=</TextArea><script>alert(50108)</script>&upass=&upass2=&urname=&ucc=1234&uemail=ab
c123%40acme-hackme.com&uphone=555-555-5555&uaddress=753+Main+Street&signup=signup
POST /List-Products.aspx?cat=1 HTTP/1.0
searchFor=</title><ScRiPt%20%0a%0d>alert(400163922725)%3B</ScRiPt>&goButton=go
CYBERDIN © 2010-2012 All Rights Reserved contact@cyberdin.com | www.cyberdin.com
Find the vulnerabilities before hackers do. Always be a few steps ahead.
LDAP Injection Vulnerability
Severity: High
Security Risk: This could result in the execution of arbitrary
commands such as granting permissions to
unauthorized users, and content modification inside the
LDAP tree.
Recommendation: Use input validation. The underlying code needs to
verify the correct input using a white list and regular
expression. Verify that the input is validated and that
there is not the ability to inject additional LDAP
information, especially the () | * characters.
More Info: http://www.blackhat.com/presentations/LDAP.pdf
Post Requests:
POST /Members.aspx
uid=admin)(&))&password=pwd
Server Response:
Authentication bypasses using LDAP injection on the “uid” parameter.
CYBERDIN © 2010-2012 All Rights Reserved contact@cyberdin.com | www.cyberdin.com
Find the vulnerabilities before hackers do. Always be a few steps ahead.
CAPTCHA Bypass Vulnerability
Severity: Medium
Security Risk: Could allow a remote attacker to bypass the
CAPTCHA implementation, thus undermining the
security benefit of the CAPTCHA technology.
Recommendation: Upgrade to newer version (if exists). Captcha image
should be distorted, and cluttered and with textured
background. The distortion and clutter is sufficient to
confuse OCR (optical character recognition) software.
More Info: http://www.cs.sfu.ca/~mori/research/gimpy/
http://www.owasp.org/index.php/Testing_for_Captcha
_(OWASP-AT-008)
Post Requests:
POST /Members.aspx
uid=CYBERDIN&password=InfoSeCheck.com&captchaImage=agos 12F
CYBERDIN © 2010-2012 All Rights Reserved contact@cyberdin.com | www.cyberdin.com
Find the vulnerabilities before hackers do. Always be a few steps ahead.
Cross Site Tracing Vulnerability
Severity: Medium
Security Risk: Http Track & Trace enabled on the web server. It is
possible to steal or manipulate customer session and
cookies, which may be used to impersonate a
legitimate user.
Recommendation: Disable the HTTP TRACE method in your web server.
More Info: http://www.kb.cert.org/vuls/id/867593
Test Requests:
TRACE /CYBERDIN-HTTP_Track_Vuln HTTP/1.0
Server Response:
HTTP/1.1 200 OK
Connection: close
Content-Type: message/http
TRACE / CYBERDIN-HTTP_Track_Vuln HTTP/1.0
CYBERDIN © 2010-2012 All Rights Reserved contact@cyberdin.com | www.cyberdin.com
Find the vulnerabilities before hackers do. Always be a few steps ahead.
Application Errors
Severity: Low
Security Risk: It is possible to gather sensitive debugging
information. The attacker can gain useful information
from the application's responses.
Recommendation: Use generic error displaying. Use try and catch blocks.
More Info: http://www.owasp.org/index.php/Missing_Error_Handling
Post Requests:
POST /Members.aspx
uid='0x%0a&password=CYBERDIN_Technologies
Server Response:
CYBERDIN © 2010-2012 All Rights Reserved contact@cyberdin.com | www.cyberdin.com
Find the vulnerabilities before hackers do. Always be a few steps ahead.
Hidden Directory Detected
Severity: Informational
Security Risk: It is possible to retrieve information about the site's file
system structure, which may help the attacker to map
the web site.
Recommendation: If the forbidden resource is not required, remove it
from the site. Website's Back-Office should be
restricted to specific IP's.
Get Requests:
GET /admin/ HTTP/1.0
Server Response:
HTTP/1.1 403 Forbidden
CYBERDIN © 2010-2012 All Rights Reserved contact@cyberdin.com | www.cyberdin.com
Find the vulnerabilities before hackers do. Always be a few steps ahead.
Password Input with Auto-Complete Enabled
Severity: Informational
Security Risk: Stored passwords can be extracted from local browser
and exposed to hostile use.
Recommendation: Password Auto-Complete property should be disabled.
You may use a code similar to:
<INPUT TYPE="password" AUTOCOMPLETE="off">
More Info: http://msdn.microsoft.com/en-us/library/ms533032(VS.85).aspx
Get Requests:
Get /Members.aspx
Server Response:
HTTP/1.1 200 OK
CYBERDIN © 2010-2012 All Rights Reserved contact@cyberdin.com | www.cyberdin.com
Find the vulnerabilities before hackers do. Always be a few steps ahead.
Appendix 1
Special (dangerous) Characters List:
It is advised to filter out all the following characters:
[1] |
[2] & [15] 0x0d
[3] ; [16] ,
[4] $ [17] \
[5] % [18] ~
[6] @ [19] #
[7] ' [20] ^
[8] " [21] *
[9] \ [22] _
[10] > and < [23] } and {
[11] ) and ( [24] ] and [
[12] + [25] =
[13] 0x00 [26] -
[14] 0x0a [27] `
CYBERDIN © 2010-2012 All Rights Reserved contact@cyberdin.com | www.cyberdin.com
You might also like
- Web Penetration Testing with Kali Linux - Second EditionFrom EverandWeb Penetration Testing with Kali Linux - Second EditionNo ratings yet
- Nilesh ChouibisaDocument15 pagesNilesh ChouibisaDhruv KanthaliyaNo ratings yet
- NMCSP 2008 Batch-I: Web Application VulnerabilitiesDocument56 pagesNMCSP 2008 Batch-I: Web Application VulnerabilitiesJitendra Kumar DashNo ratings yet
- CEH Module 17: Web Application VulnerabilitiesDocument28 pagesCEH Module 17: Web Application VulnerabilitiesAhmad MahmoudNo ratings yet
- Security Testing Lab: 360 Logica Software Testing ServicesDocument20 pagesSecurity Testing Lab: 360 Logica Software Testing ServicesGirish RajendraNo ratings yet
- Report For Foophones: by Utkarsh MunraDocument37 pagesReport For Foophones: by Utkarsh Munrasuraj fbNo ratings yet
- ZAP Scanning Report: Site: Https://webapps - Bps.go - IdDocument4 pagesZAP Scanning Report: Site: Https://webapps - Bps.go - Idyoga_wpNo ratings yet
- Ijsrdv5i120193-For ReferanceDocument3 pagesIjsrdv5i120193-For ReferanceAditya GalandeNo ratings yet
- Web Application Penetration Testing Report of Juice ShopDocument15 pagesWeb Application Penetration Testing Report of Juice ShopPavan Reddy50% (2)
- Hacking Web ApplicationsDocument5 pagesHacking Web ApplicationsDeandryn RussellNo ratings yet
- 02lec - 10 OWASP Vulnerabilities (1) (6 Files Merged)Document153 pages02lec - 10 OWASP Vulnerabilities (1) (6 Files Merged)manju kakkarNo ratings yet
- Proactive Network Defence 7CS017Document15 pagesProactive Network Defence 7CS017Anchal SinghNo ratings yet
- 4.1 Web Application Vulnerabilities - OWASP - ZSSDocument20 pages4.1 Web Application Vulnerabilities - OWASP - ZSSDhairya ThakkarNo ratings yet
- 10a - Web SecurityDocument14 pages10a - Web SecurityAlif FaisalNo ratings yet
- Threat Model For BwappDocument38 pagesThreat Model For Bwappshinde_jayesh2005No ratings yet
- GamaSec Example ReportDocument42 pagesGamaSec Example ReportMefistogrNo ratings yet
- Vuln ScanDocument12 pagesVuln ScanBrijendra Pratap SinghNo ratings yet
- Hardening Enterprise Apache Installations: Sander TemmeDocument39 pagesHardening Enterprise Apache Installations: Sander Temmewcai88No ratings yet
- Practical Risk Analysis and Threat Modeling v.1.0Document85 pagesPractical Risk Analysis and Threat Modeling v.1.0Nayana SavalaNo ratings yet
- Web Application SecurityDocument8 pagesWeb Application SecurityfunpriyanNo ratings yet
- Ridho Abdul MajidDocument24 pagesRidho Abdul MajidRidho Abdul MajidNo ratings yet
- CSRF DangerDetectionDefensesDocument20 pagesCSRF DangerDetectionDefensesCristian OrtízNo ratings yet
- Grice PresentationDocument6 pagesGrice Presentationanil100% (1)
- A Novel Technique To Prevent SQL Injection and Cross-Site Scripting Attacks Using Knuth-Morris-Pratt String Match AlgorithmDocument14 pagesA Novel Technique To Prevent SQL Injection and Cross-Site Scripting Attacks Using Knuth-Morris-Pratt String Match AlgorithmChandan NareshNo ratings yet
- Interview Preparation Part-4Document17 pagesInterview Preparation Part-4Abdul Mateen UkkundNo ratings yet
- Web Application SecurityDocument25 pagesWeb Application SecurityNipun VermaNo ratings yet
- Sample Report WebDocument19 pagesSample Report WebMuhammad AwaisNo ratings yet
- Static Detection of Cross-Site Scripting VulnerabilitiesDocument10 pagesStatic Detection of Cross-Site Scripting VulnerabilitiesLeo LopezNo ratings yet
- Hack2Secure Web Application Security Testing Workshop Reference GuideDocument9 pagesHack2Secure Web Application Security Testing Workshop Reference GuideJavvedNo ratings yet
- 19 Expt10Document17 pages19 Expt10bhalaninaman7No ratings yet
- Hacking TestDocument42 pagesHacking TestNehmaizNo ratings yet
- PMBDocument39 pagesPMBkartit0% (1)
- 15067CEM ResitDocument20 pages15067CEM Resithoney arguellesNo ratings yet
- Snyk Top 10: Code Vulnerabilities in 2022Document6 pagesSnyk Top 10: Code Vulnerabilities in 2022gavam63877No ratings yet
- 02lec - 10 OWASP VulnerabilitiesDocument40 pages02lec - 10 OWASP Vulnerabilitiesmanju kakkarNo ratings yet
- Application Level DDoSDocument1 pageApplication Level DDoSthemansuNo ratings yet
- Sessionals 1 - Vapt Pratical Lab AssignmentDocument12 pagesSessionals 1 - Vapt Pratical Lab AssignmentCFIS 2k19No ratings yet
- Diploma in Applied Network and Cloud Technology DNCT703 Network and Cloud SecurityDocument17 pagesDiploma in Applied Network and Cloud Technology DNCT703 Network and Cloud SecurityAnchal SinghNo ratings yet
- Sow - VAPT LeadsquredDocument5 pagesSow - VAPT LeadsquredChandanNo ratings yet
- Durkee OWASP Top 10 2016 11 v11Document42 pagesDurkee OWASP Top 10 2016 11 v11Pavan ReddyNo ratings yet
- Web Application Hacking & Security Program GuideDocument10 pagesWeb Application Hacking & Security Program GuideZubair ChNo ratings yet
- Report For Review1 A) Title, Abstract and KeywordsDocument9 pagesReport For Review1 A) Title, Abstract and KeywordsPrasoonNo ratings yet
- Web Application Security by (Abdallah Elsokary)Document38 pagesWeb Application Security by (Abdallah Elsokary)moradNo ratings yet
- ReportDocument17 pagesReportJay SoniNo ratings yet
- National Critical Information Infrastructure Protection CentreDocument4 pagesNational Critical Information Infrastructure Protection CentreRavi SankarNo ratings yet
- INF 123 Lecture 15Document45 pagesINF 123 Lecture 15ramzi akkariNo ratings yet
- Practical Web Penetration TestingDocument300 pagesPractical Web Penetration TestingKamarNo ratings yet
- Bao-Mat-Web-Va-Ung-Dung - Week02 - (Cuuduongthancong - Com)Document17 pagesBao-Mat-Web-Va-Ung-Dung - Week02 - (Cuuduongthancong - Com)Hân LươngNo ratings yet
- Lab 3Document4 pagesLab 3Shiv PatelNo ratings yet
- 15067CEM ResitDocument17 pages15067CEM Resithoney arguellesNo ratings yet
- Vulnerabilities in Web ApplicationsDocument6 pagesVulnerabilities in Web ApplicationswamalupiloNo ratings yet
- Cargill Web Application Scanning ReportDocument27 pagesCargill Web Application Scanning ReportHari KingNo ratings yet
- Hack2Secure Web Application Security Testing Workshop LiveOnlineDocument5 pagesHack2Secure Web Application Security Testing Workshop LiveOnlineAnonymous Rp4du2No ratings yet
- Cracking The Lens: Targeting HTTP's Hidden Attack Surface: OutlineDocument17 pagesCracking The Lens: Targeting HTTP's Hidden Attack Surface: OutlineoooNo ratings yet
- Web PentestDocument9 pagesWeb PentestsatheeshbabunNo ratings yet
- A Closer Look On C&C Panels: Seminar On Practical Security Tandhy SimanjuntakDocument39 pagesA Closer Look On C&C Panels: Seminar On Practical Security Tandhy Simanjuntaksadsada12e12312No ratings yet
- Brute Force Attack: Barracuda Web Application FirewallDocument5 pagesBrute Force Attack: Barracuda Web Application FirewallAbdinah GonfaNo ratings yet
- Attacks On ApacheDocument26 pagesAttacks On Apachehatim44026No ratings yet
- Wapiti Vulnerability Report: Target: Http://123.231.148.147:8081/webserviceDocument7 pagesWapiti Vulnerability Report: Target: Http://123.231.148.147:8081/webservicePlokodot PlokodotNo ratings yet
- Penetration Testing Report TemplateDocument9 pagesPenetration Testing Report TemplatemedtrachiNo ratings yet
- Advanced Web Application Penetration TestDocument6 pagesAdvanced Web Application Penetration TestMiloš UrbišNo ratings yet
- AttackingIPv4overIPv6 Micha Borrmann EaDocument93 pagesAttackingIPv4overIPv6 Micha Borrmann EaMiloš UrbišNo ratings yet
- ReportDocument12 pagesReportMiloš UrbišNo ratings yet
- 6net Secure Ipv6 Operation d351v3Document44 pages6net Secure Ipv6 Operation d351v3Miloš UrbišNo ratings yet
- Ipv6 World Report v4Document46 pagesIpv6 World Report v4cossuttiNo ratings yet
- x64 CheatsheetDocument9 pagesx64 CheatsheetahervalejoNo ratings yet
- Mmpa PDFDocument8 pagesMmpa PDFluis guillermo reyesNo ratings yet
- Configuration Management Plan TemplateDocument32 pagesConfiguration Management Plan Templatesanjay Sharma100% (2)
- Lesson 1 2 3 PrimaveraDocument85 pagesLesson 1 2 3 PrimaveraM Aamir AsgharNo ratings yet
- Architectural Frameworks, Models, and Views - The MITRE CorporationDocument7 pagesArchitectural Frameworks, Models, and Views - The MITRE CorporationAshutosh GuptaNo ratings yet
- Practical No 1Document4 pagesPractical No 1Gurjot Singh 651No ratings yet
- The Definitive Guide To Manufacturing AcronymsDocument8 pagesThe Definitive Guide To Manufacturing AcronymsAlfredo PanceronNo ratings yet
- Instructor: Ms. Sonia RafaqatDocument52 pagesInstructor: Ms. Sonia RafaqatAmna AhmedNo ratings yet
- CS510 Software Requirements and SpecificationDocument4 pagesCS510 Software Requirements and Specificationnoneuseemail1No ratings yet
- Sacosbgr PDF 1663417129Document36 pagesSacosbgr PDF 1663417129M7do gamerNo ratings yet
- QM Cycle - ProcessDocument3 pagesQM Cycle - ProcessPatil MGNo ratings yet
- Java Assignment PDFDocument8 pagesJava Assignment PDFGajendra gangwarNo ratings yet
- Edoc - Pub E53173000eDocument64 pagesEdoc - Pub E53173000eBayanaka TehnikNo ratings yet
- Batch No 14Document62 pagesBatch No 14Santhosh ReddyNo ratings yet
- HITACHI Training Text Engine Isuzu 6WG1X PDFDocument101 pagesHITACHI Training Text Engine Isuzu 6WG1X PDFMarwellOkay100% (11)
- E2.4 - CPSC 210 - PrairieLearnDocument5 pagesE2.4 - CPSC 210 - PrairieLearnErainne Yuting DaiNo ratings yet
- Advanced Process Control Instructions With LogixDocument13 pagesAdvanced Process Control Instructions With LogixAzito JumNo ratings yet
- Requirements Specification and Analysis IIDocument35 pagesRequirements Specification and Analysis IIayushNo ratings yet
- Engines MaterialsDocument20 pagesEngines MaterialsMarkos100% (1)
- 1.1 Algorithms and IPO DiagramsDocument15 pages1.1 Algorithms and IPO DiagramsJuan PerezNo ratings yet
- Crankshaft - RemoveDocument7 pagesCrankshaft - RemoveJose Fernando Huaman RosalesNo ratings yet
- PythonDocument25 pagesPythonSREEJITH S NAIRNo ratings yet
- Case Study - VoicePicking: Henry Schein Distribution Centers Increase Efficiency Using Voice Picking TechnologyDocument2 pagesCase Study - VoicePicking: Henry Schein Distribution Centers Increase Efficiency Using Voice Picking TechnologyHenry ScheinNo ratings yet
- Batch Management Technology To Improve - Honeywell (WP-Batch-May2010)Document12 pagesBatch Management Technology To Improve - Honeywell (WP-Batch-May2010)Yang Gul Lee100% (1)
- TIE-21204 2015 en PDFDocument504 pagesTIE-21204 2015 en PDFSuruBabuThalupuruNo ratings yet
- Software Engineering Notes Unit-4Document26 pagesSoftware Engineering Notes Unit-4Tanya PanwarNo ratings yet
- JSPM's Rajarshi Shahu College of Engineering, Pune: Instructions For Writing BE Project Work Stage - II ReportDocument12 pagesJSPM's Rajarshi Shahu College of Engineering, Pune: Instructions For Writing BE Project Work Stage - II ReportBEIT-B-4426No ratings yet
- Pino ASP - Net WorkbookDocument133 pagesPino ASP - Net WorkbookJunwil TorreonNo ratings yet
- SAD - Ch10 - Case StudyDocument44 pagesSAD - Ch10 - Case StudyPhi Nguyễn ĐứcNo ratings yet
- Egi-Ins Part 2Document18 pagesEgi-Ins Part 2versineNo ratings yet
- Csen3102Document15 pagesCsen3102shashank kumarNo ratings yet