Professional Documents
Culture Documents
Fluck (2017)
Uploaded by
giovanniglembajevicCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Fluck (2017)
Uploaded by
giovanniglembajevicCopyright:
Available Formats
Youth & Society
http://yas.sagepub.com/
Why Do Students Bully? An Analysis of Motives Behind Violence in
Schools
Julia Fluck
Youth Society published online 29 August 2014
DOI: 10.1177/0044118X14547876
The online version of this article can be found at:
http://yas.sagepub.com/content/early/2014/08/28/0044118X14547876
Published by:
http://www.sagepublications.com
Additional services and information for Youth & Society can be found at:
Email Alerts: http://yas.sagepub.com/cgi/alerts
Subscriptions: http://yas.sagepub.com/subscriptions
Reprints: http://www.sagepub.com/journalsReprints.nav
Permissions: http://www.sagepub.com/journalsPermissions.nav
Citations: http://yas.sagepub.com/content/early/2014/08/28/0044118X14547876.refs.html
>> OnlineFirst Version of Record - Aug 29, 2014
What is This?
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
547876
research-article2014
YASXXX10.1177/0044118X14547876Youth & SocietyFluck
Article
Youth & Society
1 –21
Why Do Students Bully? © The Author(s) 2014
Reprints and permissions:
An Analysis of Motives sagepub.com/journalsPermissions.nav
DOI: 10.1177/0044118X14547876
Behind Violence in yas.sagepub.com
Schools
Julia Fluck1
Abstract
Research on school bullying and violence has always been working with
taxonomies of bullying to categorize aggressive acts. Researchers distinguish
between direct and indirect or between physical, verbal, and relational
bullying. Cyberbullying is categorized either by type of action or by type
of medium. In this article, we propose another kind of categorization: the
taxonomy of reasons. A questionnaire was developed that asks for the five
dimensions “instrumental,” “power,” “sadism,” “ideology,” and “revenge.”
It was tested with middle-school children in Germany. While bullies claim
that their reasons were mostly revenge, victims mostly insinuate sadism and
power. Both groups claim that ideology and instrumental violence play a
little role. Confirmatory Factor Analyses (CFA) show that at least four of
the theoretically proposed dimensions make sense (except instrumentality).
A qualitative analysis of open answers shows that for future questionnaires,
the taxonomy should include additional dimensions, such as peer pressure
and lack of self-control.
Keywords
aggressive behavior/bullying, violent behavior, victimization, measurement
development
1University Koblenz-Landau, Germany
Corresponding Author:
Julia Fluck, Center for Educational Research, University Koblenz-Landau, Buergerstraße 23,
Landau 76829, Germany.
Email: fluck@zepf.uni-landau.de
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
2 Youth & Society
Bullying in Schools
Although bullying in schools (defined as “aggressive behavior normally
characterized by repetition and imbalance of power”; Smith & Brain, 2000,
p. 1) has probably existed as long as schools themselves, we can look back on
a rather short period of research of only a bit more than 30 years. During this
time, information was gathered about criteria for definition, personality traits
of bullies and victims, forms of bullying, gender differences, coping strate-
gies, and consequences (Smith & Brain, 2000). Studies have shown early that
there are some cultural differences in understanding bullying (Smith, Cowie,
Olafsson, & Liefooghe, 2002). Compared with Western cultures, the Japanese
phenomenon “ijime,” for example, relies more on relational than on direct
aggression (Akiba, 2004). However, researchers mostly agree on the concep-
tual definitions of bullying. Of course, that does not mean there are no differ-
ences in, for example, prevalence rates among countries (for a detailed
comparison of countries, see Smith et al., 1999).
This article reviews existing taxonomies (categorization systems) for tra-
ditional bullying and cyberbullying and proposes to add a new taxonomy by
type of reason. Taxonomies are an important area of research for two reasons:
First, by defining categories of a phenomenon, they form a rationale for oper-
ationalizing the construct. Questionnaire items are developed based on those
categories, which makes it important to establish exhaustive taxonomies that
cover all aspects of a phenomenon. Second, taxonomies can be used as a
foundation for more elaborate research questions. For example, only the dis-
tinction between physical, verbal, and relational forms of bullying made it
possible to understand gender differences. Especially for new phenomena,
like cyberbullying, good taxonomies are crucial for understanding more
about their true nature.
Taxonomies for Traditional Bullying
School bullying has as many faces as violence itself and can range from phys-
ical attacks such as punching, kicking, or even stabbing with a knife to softer
forms like insults or gossiping. Most common forms of bullying are (in order
of frequency) harassing, ridiculing, beating, threatening, spreading rumors,
and exclusion from common activities (Seals & Young, 2004; Sharp & Smith,
1991).
From the beginning on (Olweus, 1993), researchers have categorized acts
of bullying along the taxonomies of aggressive behavior in general: Direct
versus indirect bullying on the one hand and physical, verbal, and psycho-
logical bullying on the other hand (Smith, 2009) are two dimensions that can
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
Fluck 3
be combined in a matrix of 2 × 3 = 6 possible forms of bullying: Physical
bullying is usually direct (A hits B) but can also take place in an indirect man-
ner (A tells B to punch C). Verbal bullying can also be direct (A insults B) or
happen behind the victims back (A spreads rumors about B). Psychological
(sometimes called relational) bullying is used to undermine the victim’s sta-
tus within a group or to destroy his or her friendships. This can happen with
the knowledge of the victim (direct bullying) or in more covert (indirect)
forms (Coyne, Archer, & Eslea, 2006).
The taxonomy of reasons (TOR, as presented below) describes a third
dimension of bullying incidents: for example, direct verbal bullying out of
revenge or indirect relational bullying for the exertion power.
The Situation in Germany
Bullying in schools has been of interest for German researchers since the
1990s (Petermann, 2003). Research focuses mostly on prevalence rates, char-
acteristics of bullies and victims, and attributes of the school. Most studies
and intervention programs focus on violence in schools in general and not
specifically on bullying (Riebel, 2008). With prevalence rates between 4%
and 12% (Lösel & Bliesener, 1999), bullying is definitely a problem in this
country.
For a few years, the focus of most German researchers has shifted to
cyberbullying, first studies were published since 2008 (Katzer, 2008; Riebel,
2008), focusing on prevalence and overlap with traditional bullying.
Cyberbullying
Since the new millennium, research has started to focus on a new type of
violence among children and adolescents that uses the fast evolving new
media as a method to bully others. Early studies have focused mostly on the
prevalence of cyberbullying and on the differences to traditional bullying.
Only of late, researchers try to cover the basics, which have so far been
neglected: conceptualization, methodology, and theoretical foundation
(Bauman, Cross, & Walker, 2013). A consensus has not been reached on defi-
nition (Tokunaga, 2010), measurement (Menesini & Nocentini, 2009), or cat-
egorization. In this article, we follow the definition by Smith et al. (2008)
“[Cyberbullying is] an aggressive, intentional act carried out by a group or
individual, using electronic forms of contact, repeatedly and over time against
a victim who cannot easily defend him- or herself” (p. 376). For a critical
discussion of the definition, see Smith, Del Barrio, and Tokunaga (2013) and
Bauman, Underwood, and Card (2013).
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
4 Youth & Society
Taxonomies for Cyberbullying
Although there are many ways in which researchers categorize (and therefore
assess) acts of cyberbullying, they mostly use a taxonomy of actions (TOA)
as proposed by Willard (2007) or a taxonomy of media (TOM) as proposed
by Smith et al.(2008). The TOA distinguishes between different behaviors
(harassment—sending offensive messages to the victim; denigration—
spreading rumors about someone; impersonation—identity theft; outing and
trickery—forwarding embarrassing or private pictures, videos, or messages;
exclusion—excluding someone from common activities such as chats or
online games). TOM asks which kind of medium was used to perform the
bullying (by phone, text message, email, picture or video clip, instant mes-
senger, website, chat).
Many current studies use either some kind of TOA (Ang & Goh, 2010;
Erdur-Baker, 2010; Katzer, Fetchenhauer, & Belschak, 2009) or some kind of
TOM (Beran & Li, 2005; Ortega, Calmaestra, & Mora Merchán, 2008; Slonje
& Smith, 2008), although in both cases the authors usually make adaptions.
As a result, there is as little consensus in categorization of cyberbullying as
there is in its definition.
This general lack of a convention for categorizing cyberbullying is a tre-
mendous problem in terms of comparability of results. Usually, the answers on
the several subtypes of bullying are summed up to a score that is used to define
victim status. Menesini & Nocentini (2009) have shown that results can vary
considerably depending on which question one uses to assess victim status.
After reviewing the existing literature on cyberbullying, Dooley, Pyżalski,
and Crosset (2009) come to the following conclusion:
Clearly, the different types of cyberbullying are not equal in terms of the skills
needed to engage in the behavior as well as the impact they have on victims. It
would be interesting to determine if there is an association between a
perpetrator’s motivation (e.g., revenge vs. fun) and the type of media used to
cyberbully. (p. 185)
We therefore propose not to limit scientific outcome by using only one
taxonomy in a study but to use both TOA as well as TOM and to even com-
plement them with a third taxonomy: a categorization of reasons.
Motives Behind Violence in Schools
In his classic work on the roots of “evil” behavior, Baumeister (2001) lists
four different reasons behind violence: predation (or instrumental violence),
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
Fluck 5
revenge, ideology, and sadism. Pinker (2011) takes up this taxonomy of rea-
sons (TOR) but adds a fifth category: power—arguing that the need for power
is a special kind of instrumental violence that is universal in human beings
(McClelland, 1987). In this study, we used the five-factor variant—assuming
that if power were not inherently different from instrumental bullying, this
would be displayed in the data.
A questionnaire that tries to cover all common motives and order them
along theoretically as well as empirically founded dimensions has not yet
been developed for the study of bullying motives. However, the issue of
motives has been addressed in theoretical as well as in empirical works. In
the following overview, the five types of reasons of the TOR are presented
and discussed with regard to school bullying and violence.
Instrumental Violence
We call behavior instrumental violence when the perpetrator attacks the vic-
tim to reach an aim he or she cannot reach with non-violent means. Olweus
(1993) suggests that a common reason for bullying is the fact that the bullies
often blackmail their victims to give them money or valuable items. However,
little is known if this motive plays a significant role and what other kinds of
instrumental violence might be important for bullying.
Power
Violence motivated by a need to exercise power occurs when the perpetrator
hopes to secure or to enhance his or her position within a social entity. This
issue has been addressed on the outskirts of research on gender differences,
which often focuses on the reasons why girls use different kinds of violence
than boys (Coyne et al., 2006; Siann, Callaghan, Glissov, Lockhart, &
Rawson, 1994). The means they use may be different, but the aims they use
them for are the same. Boys as well as girls use violence to maintain or
improve their position in the “pecking order” of the class.
Revenge
Children and adolescents as well as adults can react angry and aggressive
when being threatened and attacked, especially when they feel the attack was
unjustified. Especially in the context of cyberbullying, the question is dis-
cussed if this might be a medium for the physically weak to take revenge on
their real-life bullies.
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
6 Youth & Society
Ideology
In-group/out-group phenomena play an important role in human interactions
and can eventually lead to violence toward individuals who we perceive to
belong to the out-group (Brewer, 1999). When it comes to bullying, the traits
that increase the chance of becoming a schoolyard victim seem to be rather
psychological ones (e.g., low self-esteem, shyness, introversion) than vari-
ables such as ethnicity, social status, outer appearance, sexual orientation,
religious affiliation, and other obvious traits that distinguish the individual
from the majority (Siann et al., 1994). Thus, we can expect that ideologist
reasons play a rather minor role.
Sadism
Sadism sounds like a rather harsh term for interactions between children and
adolescents. But sadism does not necessarily include needles and pins but
merely describes the feeling of joy that is being drawn from watching another
person suffer. In the classroom, this can simply mean that fellow students are
harassed out of boredom, which was indeed one of the main reasons girls
named for bullying others (Owens, Shute, & Slee, 2000).
The TOR was designed to categorize acts of violent and antisocial behav-
ior in human adults, ranging from gossip to robbery and much more serious
forms of violence such as (mass) murder. This study aims to find out if the
five categories are also applicable to the living environment of middle-school
students in an educational context. Three major questions are in focus here:
1. What are the most common motives for bullying in schools (includ-
ing cyberbullying)?
2. Is the empirical factor structure identical with the theoretical concept
as proposed by Baumeister (2001) and Pinker (2011)?
3. Are there any additional reasons relevant in the everyday life of mid-
dle-school students that are not covered by the TOR?
Method
Participants
A questionnaire was presented to 578 middle-school students from five
schools from a rural area in the state of Rhineland-Palatinate, Germany, by
teachers in training. Rhineland-Palatinate is one of 16 German states, wealth
and educational level are consistent with the German average. The schools
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
Fluck 7
were ordinary without any noticeable peculiarities (such as a digital divide or
an accumulation of violent incidents). The sample has to be considered an ad
hoc sample, because the schools were not sampled randomly but chose to
participate on their own account. Fifty-four percent of the participants were
male, 44% female (2% refused to provide information on their gender). The
age ranged from 11 to 18 years with a medium age of 14.71 years (SD =
1.32). As almost all the students were under age, the parents were given an
information form about content and purpose of the study. Their consent was
required for the students to participate in the study.
Assessments and Measures
The questionnaire contained several scales on traditional and cyberbullying
and asked both for bully and victim experiences. The five kinds of reasons
from the TOR were operationalized via three items for each motive (e.g., for
power/victim perspective: “How often did it happen to you in the course of
the last year that you were victimized because the other person wanted to
show you who is stronger?”), and participants were asked to answer them on
a five-point-scale ranging from “never” to “several times a week.” Two scales
were newly developed: one asking students about their own motives when
they bullied others and one asking them what motives the bullies might have
had when they themselves were victimized (for an English translation of the
content of each item, see Table 1). By checking the frequencies of the items
on both scales the most common motives of bullies were identified and com-
pared with what victims assume to be the most common motives.
Confirmatory Factor Analyses (CFA) were used for both the bully and the
victim scale to see if the dimensional structure of the data fit the theoretical
assumptions, this was done using MPLUS Version 6.1. Confirmatory instead
of exploratory factor analysis was used, because there already existed theo-
retically funded assumptions on the underlying factor structure (T. A. Brown,
2006).
In addition to the rating scales, the questionnaire contained an open ques-
tion: “If you ever bullied a fellow student, please name the reason(s) for your
behavior.” This was done to see whether the TOR really does include the
most common motives for bullying or if there are other prominent reasons
that should be included when the taxonomy is adapted for children and ado-
lescents. A qualitative analysis was performed on those open answers: The
text was reviewed and checked for reasons. Not all participants filled in the
forms and some of them gave more than one reason for violent behavior. The
total of N = 186 reasons was analyzed, and a key word was assigned to each
reason.
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
8 Youth & Society
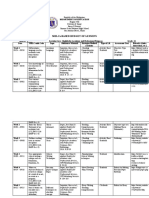
Table 1. Frequency of Reasons in Descending Order (Bullies’ Perspective).
Frequency (in %)
Name Item Never Seldom Often
11_R Victim has angered bully or his friends 61.2 35.7 3.1
2_R Bully takes revenge for something the 65.0 33.2 1.8
victim has done
14_R Victim deserved bullying with his 68.6 29.2 2.2
behavior
3_M Bully wants to show who is stronger 78.3 19.7 2.0
5_S It was fun to bully 78.7 16.5 4.9
4_M Victim stood between bully and his 80.0 19.5 0.5
friends
9_S It was fun to see the victim’s reaction 83.9 13.6 2.5
7_Z Bully could only achieve an aim 85.1 14.0 0.9
through violence
12_S Bully was bored 86.5 11.1 2.3
10_M Bully wanted to demonstrate power 87.5 10.9 1.6
15_I Victim was fan of an unpopular group 88.2 9.5 2.4
13_I Victim was member of an unpopular 90.2 8.8 0.9
clique
6_I Victim was part of a minority 93.8 5.6 0.5
8_Z Bully wanted to force victim to do 96.9 3.1 0.0
something
1_Z Bully wanted money or valuables 98.4 1.3 0.4
Note. The letters in the item name indicate the theoretically assumed affiliation to a
dimension. R = revenge; M = power; S = sadism; Z = instrumental; I = ideology.
Results
Most Common Motives
Table 1 gives an overview on the motives rated most common by the bullies.
The five-point scale is here being transformed into a three-point-scale with
the values “never,” “seldom,” and “often.” The rationale behind this is the
fact that bullying requires—per definition—that victimization occurs repeat-
edly and over a longer period of time. When incidents occur more seldom,
some authors speak of “soft” or “less severe” bullying (Borg, 1999). In any
case, even seldom acts can be described as “violence” because violence does
not demand repetition as a criterion. We can use those incidents to get a clear
picture on the existence and distribution of motives, but we have to keep in
mind that—strictly speaking—this is not bullying.
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
Fluck 9
The rating of the bullies yields a rather clear picture: The items for revenge
are on the very top of the list followed by (less frequently) the items on power
and sadism. Sadistic behavior was however attributed more often to fun than
to boredom. Bullying motivated by ideology seems to play a rather minor
role, and instrumental violence seems to occur on only very few occasions.
The perspective of the victims as presented in Table 2 yields a somewhat
different picture.
The victims attribute the bullies’ behavior mostly to sadism or an urge for
power. Revenge and ideology also play a role. When it comes to ideology, it
is interesting to observe that the victims agree with the bullies on the fact that
belonging to a minority is not a very common reason for being bullied. The
same results were found with regard to instrumental bullying.
Confirmatory Factor Analysis
CFA were used to find out if the division of motives into the five aforemen-
tioned subcategories can be confirmed empirically. For this purpose, the per-
spective of the bullies as well as the one of the victims was taken into account.
Although we can expect to find differences between both perspectives here,
we can look for agreements between both perspectives.
The bullies’ perspective. Probably due to very little variance in the instrumen-
tal items (instrumental bullying was hardly ever reported and by the bullies
even less than by the victims; see above), the model containing all five fac-
tors did not converge. The results of the non-converging solution indicated a
misfit of the factor “instrumental bullying,” so in a second step, the factor
instrumental bullying was removed from the model (as it has little practical
relevance anyway) and a four-factor-version was being calculated. The
results of this model are depicted on the left side of Figure 1. Only a single
adaption had to be made with the four-factor-solution: Item I_15 (victim was
fan of an unpopular group) showed loadings >1 with the ideology factor.
Instead of fixing the variance a more conservative approach was used and the
item was removed from the model (Chen, Bollen, Paxton, Curran, & Kirby,
2001).
As visible on the left side of Figure 1, all items have factor loadings >.50,
except for Item 4_M (victim stood between bully and his friends) with a load-
ing of only λ = .26. This is not surprising as the other two items on the factor
(bully wants to show who is stronger; bully wanted to demonstrate power)
are both about the relationship between bully and victim and 4_M is about the
relationship between the bully and a third party. In spite of the rather low fac-
tor loading, the item is left in the model for theoretical reasons. The fit indices
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
10 Youth & Society
Table 2. Frequency of Reasons in Descending Order (Victims’ Perspective).
Frequency (in %)
Name Item Never Seldom Often
3_M Bully wants to show who’s stronger 66.3 28.8 5.0
9_S It was fun to see the victim’s 67.3 27.4 5.3
reaction
5_S It was fun to bully 70.1 23.3 6.7
12_S Bully was bored 73.9 20.9 5.2
10_M Bully wanted to demonstrate power 75.3 20.7 4.1
4_M Victim stood between bully and his 77.8 20.3 1.9
friends
2_R Bully takes revenge for something 80.4 18.3 1.2
the victim has done
11_R Victim has angered bully or his 82 17.4 0.7
friends
13_I Victim was member of an unpopular 85.2 12.0 2.8
clique
15_I Victim was fan of an unpopular 85.6 12.4 1.9
group
7_Z Bully could only achieve an aim 85.9 11.8 2.3
through violence
14_R Victim deserved bullying with his 87.4 11.6 1.1
behavior
6_I Victim was part of a minority 88.1 9.8 2.1
8_Z Bully wanted to force victim to do 91.6 7.4 0.9
something
1_Z Bully wanted money or valuables 95 4.2 0.7
Note. The letters in the item name indicate the theoretically assumed affiliation to a
dimension. R = revenge; M = power; S = sadism; Z = instrumental; I = ideology.
Comparative Fit Index (CFI), Tucker–Lewis Index (TLI), and root mean
square error of approximation (RMSEA) show that the model fits the data
very well. (The fit indices used in this analysis can be interpreted as follows:
The CFI indicates acceptable model fit when >.90 and good model fit when
>.95; ideally, values should even exceed .97. The TLI has similar criteria and
demand values >.95 for acceptable and >.97 for good model fit. The RMSEA
shows good model fit when 0 < RMSEA < .05 and acceptable model fit when
.05 < RMSEA < .08; T. A. Brown, 2006; Schermelleh-Engel, Moosbrugger,
& Müller, 2003).
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
Fluck 11
Figure 1. Confirmatory factor analysis of reasons from the bullies’ (left side) and
from the victim’s (right side) perspective.
Note. CFI = comparative fit indices; TLI = Tucker–Lewis index; RMSEA = root mean square
error of approximation
The victims’ perspective. The CFA over the victims’ answers is portrayed on
the right side of Figure 1. For the victims’ perspective, the theoretically
assumed factor structure could be verified without any adaptations. All items
show satisfactory factor loadings of λ ≥ .30. The intercorrelations between
the latent factors are all rather high with .57 ≤ r ≤ .94 and higher than the
intercorrelations in the bullies’ perspective. The highest correlation (r = .94)
is between “sadism” and “power”; “instrumental bullying” and “power” (r =
.86) share 74% of their variance. However, the model fit is not entirely satis-
factory: While the RMSEA is in the range of acceptable model fit, CFI and
TLI indicate sub-standard model fit.
Qualitative Analysis of Open Questions
The rating of the open answers yielded 11 key words, to each of which sev-
eral answers (ranging from 6 to 49) were assigned. Five of the key words
responded to the dimensions of the TOR; 6 can be considered additional
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
12 Youth & Society
Table 3. Key Words From Qualitative Analysis of Reasons.
Additional key words (not yet
Answers compatible with the TOR considered in the TOR)
Number of Number of
Key word incidents Key word incidents
Revenge 36 Peer pressure 49
Fun 26 Provocation 20
Social status 13 Self-defense 9
(power)
Deserved attack 7 Coping with 7
(revenge) emotions
Being different 6 Antipathy 7
(ideology)
Thoughtlessness 6
Note. TOR = taxonomy of motives.
kinds of reasons. Table 3 shows how frequent the different key words were
assigned.
First, let us consider the reasons consistent with the TOR taxonomy (see
the left-hand side of Table 3). The order of the frequencies seems to validate
the findings from the quantitative item analysis. Revenge is named most often,
followed by fun (sadistic) and power. Seven participants explicitly mention
that the victim simply deserved being bullied without further explaining how
or why they deserved this kind of treatment. Bullying out of ideological rea-
sons was mentioned only 6 times (3%) where bullies justified their behavior
with the victim being “different” or “weird.” Instrumental bullying in the form
of blackmail for money or valuables was not mentioned at all.
The right-hand side of Table 3 shows the key words that were at first sight
inconsistent with the TOR. Forty-nine students name “peer pressure” as a
reason for bullying someone. With 26% of all mentioned reasons, peer pres-
sure seems to play a huge role as a motivator. Seven of the participants
explicitly use this word, which has to the reader a negative connotation of
being coerced into something. This feeling is evident from wordings such as
“in order not to be bullied as well (boy, 14)” or “[I bullied] maybe a little.
Only for the others to see that I am on their side . . . (girl, 13).” However, the
group can also foster rather positive feelings: “It makes me feel good being
part of a group (boy, 15).”
Provocation is also mentioned very often as a reason for violence, but
other motives also seem to play (although probably a minor) a role:
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
Fluck 13
self-defense, coping with own negative emotions such as anger or frustration,
antipathy toward the victim, or simple thoughtlessness.
Discussion
Most Common Motives
It is no surprise that bullies and victims differ in their assessment of motives.
Human beings process information in ways that allow them to keep a positive
picture of themselves. Both bullies and victims find themselves in situations
where—without justification—their self-worth is threatened. For the bully,
hurting others is in contrast to the self-perception of being a nice person,
whereas being bullied by others might be contradictory to the picture of one-
self as a likable person. For both groups, the result is cognitive dissonance
(Festinger, 1957), which can be overcome by reasonable explanations for
those situations. It is known from research on aggression in general
(Baumeister, 2001) that victims and offenders give very different reasons for
an attack: Offenders can usually justify their behavior with solid reasons that
make it seem like they did not have any other choice but choosing violent
means. Such reasons include being provoked, defense or revenge against ear-
lier attacks by the victim and so on. Victims, however, claim that the perpe-
trators did not actually have any comprehensible reason at all. Instead, they
think the offenders have acted purely out of their evil spirit, without the
slightest reason or provocation. Baumeister (2001) calls this phenomenon
“the myth of pure evil.” The objective “truth” probably lies somewhere in
between both perspectives. Due to the fact that both groups use such self-
justifications for the reduction of their own cognitive dissonance, all parties
involved actually believe in the accuracy of their perspective (i.e., they do not
just lie to others to convince third parties, although the deception of others
might play a role as well as self-deception).
The results of the frequency analyses over the most common motives fit
perfectly within the theoretical framework of the “myth of pure evil.”
Opinions differ quite a lot when it comes to the most common motives. While
bullies give revenge as the most common motive and name sadism and power
only in second place, it is the other way round with the victims, that is, the
victim more often sees the bullying as something that happens either out of
no reason at all (but just for the fun of doing it) or motivated by “lower”
motives (such as the gain or demonstration of power), whereas the bullies
argue with the justification of their behavior by revenge. This finding is con-
sistent with the literature and therefore not very surprising. More interesting
are the facts on which both groups agree: As expected, ideology plays a rather
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
14 Youth & Society
small role as a motive for violence and bullying (Siann et al., 1994) and
instrumentality plays hardly a role at all. Olweus’ (1993) assumption on bul-
lies’ blackmailing for money or valuables seems to be falsified by the data—
occurrences like these are rather the exception than the rule. Still, in schools
from poorer environments, those material reasons might play a bigger role.
Future studies should focus on the question if social class might be factor that
enhances this kind of motivation.
Confirmatory Factor Analysis
The CFA results lead to the conclusion that the theoretically proposed factor
structure seems to be rather valid. The fact that the four dimensions, power,
sadism, ideology, and revenge, could be replicated in both models (bullies’ as
well as victims’ perspective) validates the existence and independency of
these factors. However, the in part sub-standard model fit of the victims’
model suggests that we should refrain from using the instrumental items in
future versions of the questionnaire. This consequence is also consistent with
the findings on most common motives.
On the item level, the questionnaire is being validated by the substantial
factor loadings in both models. All items make sense and to each factor three
items can be clearly assigned. An exception is being made by Item 4_M (vic-
tim stood between bully and his friends). It should be considered if future
versions of the questionnaire should differentiate more between two kinds of
power bullying: the demonstration of power or strength to daunt the victim
and the fight for individual friend or relationships. Both are aspects of power
and status within the class, but the phenomena are rather distinct in their
nature and probably call for two separate dimensions. Further research needs
to find out if the power factor includes two sub-dimensions when the TOR is
used on bullying in schools.
The latent correlations between the five factors are all rather high, which
suggests that students who bully for one reason tend to bully for other reasons
as well.
We can only guess why those correlations are higher from the victims’
perspective than from the bullies’ perspective. We can assume, though, that in
spite of all self-preserving contortions of reality, bullies know why they bully.
One good reason is probably enough for them to justify their behavior. The
victim, however, can only speculate what his bully’s reasons might have
been, which can lead to the fact that victims name several reasons more often
than the bullies do. Victims are probably unable to determine what the exact
reasons behind an incident were. The almost perfect correlation between
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
Fluck 15
sadism and power indicates that victims can hardly differentiate between
those two reasons.
As for the question of power and instrumental bullying, we have only the
victim data to check Pinker’s hypothesis that they are two different dimen-
sions (the factor “instrumental” was not included in the CFA model of the
bullies). Although the association is rather high, there remains 25% of non-
shared variance, which is why we can quite safely assume that, though
related, instrumental and power bullying are two different phenomena.
Qualitative Analysis of Open Questions
The analysis of the qualitative data reveals two major findings. First, the TOR
is validated in the respect that the four factors identified in the CFAs are also
mentioned in the open answers and interestingly even in the same order of
frequency (revenge more often than fun, and power and ideology only in 3%
of the cases).
Second, the analysis also shows that when used for research on bullying,
the TOR does in its current form not cover all kinds of reasons students have
for victimizing others. But not all the key words found justify taking them up
separate full dimensions in a future version of the TOR questionnaire. For
example, “self-defense” does not actually make any sense in the context of
bullying but rather seems to be a kind of (self-)deception of the perpetrator.
Bullying cannot—by definition—happen out of self-defense as it requires the
victim to be the inferior and helpless part (Menesini et al., 2012).
Also, the key words “antipathy,” “coping” and “thoughtlessness” are
counted seldom and could possibly both be attributed to a pattern of disinhib-
ited behavior. In fully socialized grown-ups, antipathy (without provocation)
alone should not result in aggressive behavior and if it does, it is associated
with psychopathology (Aboujaoude & Koran, 2010). Interestingly, some of
the participants mention bullying as result of experiencing negative emotions
such as anger and frustration. Usually, research on bullying considers stress
and negative emotions only on the outcome side—as consequences of bully-
ing. An exception is the recent work of Patchin and Hinduja (2011) who
apply general strain theory (Agnew, 1992) to (cyber)bullying and can show
that indeed strain and anger / frustration are associated to aggressive behavior
in schools. Maladaptive coping, too, can be considered as a form of disinhibi-
tion or more precisely as choosing an alternative out of a catalogue of reac-
tions that is harmful to both bully and victim. Further research needs to find
out if the TOR should be extended by a separate category for lack of impulse
control.
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
16 Youth & Society
The key word “provocation” describes a phenomenon consistent with bul-
lying literature and might hence be a useful addition to the TOR. Olweus
(1993) makes the distinction between ordinary and provocative victims who
challenge their fellow students with strange, dissocial, or inadequate behav-
ior that can result in rejection and even lead to bullying.
“Peer pressure” is the key word mentioned most of all and therefore seems
to play an important role as a motive. This finding shows that in its current
form, the TOR is not perfectly adequate to the experiences of middle-school
students with regard to bullying. The TOR was developed to classify adult’s
motives for violence or antisocial behavior. Although adults, too, are influ-
enced by members of their peer group, the phenomenon is especially evident
in adolescents whose definition of their own identity is highly dependent on
being accepted by one’s peers (B. B. Brown, 2004). Bullying is usually a
group phenomenon (Olweus, 2003) where only a few students in a class actu-
ally initiate the bullying and the others only tend to foster it or stand by. For
the initiators, the TOR in its current form might be exhaustive enough, but for
the majority of the class, it needs to be extended by a category for bystanders
and followers.
Practical Relevance
Studying motives is not only interesting for researchers who want to under-
stand the causes of human behavior. For teachers, social workers, and school
psychologists, it is also important to know and understand the dynamics
behind (cyber-)bullying. For them, it could be useful to investigate the situa-
tion in their school with a simple questionnaire containing TOR items. The
strategies for fighting bullying will depend on the most common motives in
this particular school.
The results of this study are also relevant for the assessment of bullying
and cyberbullying by questionnaires. Using all three of the currently existing
taxonomies takes little space and time, and yields a huge additional benefit in
information. As mentioned above, we suggest using all three taxonomies in
questionnaire studies. Researchers should also consider including open ques-
tions in their studies of new phenomena such as cyberbullying. The reality of
adolescents’ lives at school might (as was the case in this study) yield catego-
ries that were not thought off before.
Limitations
Bullying in schools is still a rather sensitive topic in German schools.
Therefore, the school administrators did not allow questions on parents’
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
Fluck 17
socioeconomic status or ethnicity. To replicate the findings of this study,
future research should use representative random samples—large enough to
consider these and more variables as covariates such as school or class size,
educational achievement, and number of friends. Also, students from other
countries and cultural backgrounds should be questioned, as there might be
cultural differences concerning the motives behind bullying and cyberbully-
ing. Random samples would also solve the problem of self-selection.
The results of this study were drawn from a middle-school setting. Results
cannot simply be transferred to other educational contexts (such as preschool
or higher education) without further validation. However, they can be used as
a point of origin for generating hypotheses.
Conclusion
The aim of this study was to establish a TOR for motives behind bullying in
schools. Based on an existing five-factor theory, most common motives were
identified, and the theoretically assumed factors were tested for factor valid-
ity. Open questions on motives were used to find additional reasons not cov-
ered in the original TOR.
The results show that the taxonomy of reasons can be applied to bullying
in schools, but some fine-tuning is needed for the taxonomy to reflect the
circumstances under which middle-school students live and learn together—
especially when it comes to the influence of the peer group.
Especially for new phenomena such as cyberbullying, good taxonomies
are crucial for understanding its true nature. They help us grasp a more accu-
rate concept of cyberbullying by providing insights on what exactly hap-
pened, how it was carried out, and what the underlying reasons were.
Questionnaires on bullying and on cyberbullying should therefore include
items on reasons. Those items should not replace items in established taxono-
mies but complement them with a further aspect that has been neglected until
now.
Future research needs to be done to develop and validate a revised TOR
scale that includes items on the motives from the qualitative results. Also, it
would be interesting to investigate the relationship between the different cat-
egories in TOA, TOM, and TOR: Do bullies choose different media and
actions, depending on their motives? The existing taxonomies (TOA and
TOM) should also be investigated more thoroughly. So far, they are used
without proof of validity.
In the future, researchers and practitioners should also consider distin-
guishing between the person(s) who initiated a behavior and all those who
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
18 Youth & Society
only bully out of peer pressure. The latter group is distinct from the initiating
bullies as well as from the bystanders and deserves more attention.
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research,
authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publi-
cation of this article.
References
Aboujaoude, E., & Koran, L. M. (2010). Impulse control disorders. New York, NY:
Cambridge University Press.
Agnew, R. (1992). Foundation for a general strain theory of crime and delinquency.
Criminology, 30, 47-88.
Akiba, M. (2004). Nature and correlates of ijime—Bullying in Japanese middle school.
International Journal of Educational Research, 41, 216-236. doi:10.1016/j.
ijer.2005.07.002
Ang, R. P., & Goh, D. H. (2010). Cyberbullying among adolescents: The role of
affective and cognitive empathy, and gender. Child Psychiatry & Human
Development, 41, 387-397. doi:10.1007/s10578-010-0176-3
Bauman, S., Cross, D., & Walker, J. L. (Eds.). (2013). Principles of cyberbullying
research: Definitions, measures, and methodology. New York, NY: Routledge.
Bauman, S., Underwood, M. K., & Card, N. (2013). Definitions: Another perspective
and a proposal for beginning with cyberaggression. In S. Bauman, D. Cross, &
J. L. Walker (Eds.), Principles of cyberbullying research: Definitions, measures,
and methodology (pp. 41-46). New York, NY: Routledge.
Baumeister, R. F. (2001). Evil: Inside human violence and cruelty (1st Holt paperback
ed.). New York, NY: Holt.
Beran, T., & Li, Q. (2005). Cyber-harassment: A new method for an old behavior.
Journal of Educational Computing Research, 32, 265-277.
Borg, M. G. (1999). The extent and nature of bullying among primary and secondary
school children. Educational Research, 41, 137-153.
Brewer, M. B. (1999). The psychology of prejudice: Ingroup love and outgroup hate?
Journal of Social Issues, 55, 429-444. doi:10.1111/0022-4537.00126
Brown, B. B. (2004). Adolescents’ relationships with peers. In R. M. Lerner & L. D.
Steinberg (Eds.), Handbook of adolescent psychology (2nd ed., pp. 363-394).
Hoboken, NJ: John Wiley.
Brown, T. A. (2006). Confirmatory factor analysis for applied research (Methodology
in the social sciences). New York, NY: Guilford Press.
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
Fluck 19
Chen, F., Bollen, K. A., Paxton, P., Curran, P. J., & Kirby, J. B. (2001). Improper solutions
in structural equation models: Causes, consequences, and strategies. Sociological
Methods & Research, 29, 468-508. doi:10.1177/0049124101029004003
Coyne, S. M., Archer, J., & Eslea, M. (2006). “We’re not friends anymore! Unless . . . ”: The
frequency and harmfulness of indirect, relational, and social aggression. Aggressive
Behavior, 32, 294-307.
Dooley, J. J., Pyżalski, J., & Cross, D. (2009). Cyberbullying versus face-to-face
bullying. Zeitschrift für Psychologie/Journal of Psychology, 217(4), 182-188.
doi:10.1027/0044-3409.217.4.182
Erdur-Baker, O. (2010). Cyberbullying and its correlation to traditional bullying, gen-
der and frequent and risky usage of Internet-mediated communication tools. New
Media & Society, 12, 109-125. doi:10.1177/1461444809341260
Festinger, L. (1957). A theory of cognitive dissonance. Stanford, CA: Stanford
University Press.
Katzer, C. (2008). Tatort Internet: Cyberbullying und sexuelle Viktimisierung
von Kindern und Jugendlichen in Chatrooms [The Internet as a crime scene:
Cyberbullying and sexual victimization of childen and adolescents in chat-
rooms]. Forum Kriminalprävention, 3, 26-33.
Katzer, C., Fetchenhauer, D., & Belschak, F. (2009). Cyberbullying: Who are the
victims? Journal of Media Psychology: Theories, Methods, and Applications,
21, 25-36. doi:10.1027/1864-1105.21.1.25
Kowalski, R., & Limber, S. (2008). Electronic bullying among middle school stu-
dents. Journal of Adolescent Health, 41(6), S22-S30.
Lösel, F., & Bliesener, T. (1999). Germany. In P. K. Smith, Y. Morita, J. Junger-Tas,
D. Olweus, R. Catalano, & P. Slee (Eds.), The nature of school bullying: A cross-
national perspective (pp. 225-249). London, England: Routledge.
McClelland, D. C. (1987). Human motivation. Cambridge, UK: Cambridge University
Press.
Menesini, E., & Nocentini, A. (2009). Cyberbullying definition and measure-
ment. Zeitschrift für Psychologie/Journal of Psychology, 217(4), 230-232.
doi:10.1027/0044-3409.217.4.230
Menesini, E., Nocentini, A., Palladino, B. E., Frisén, A., Berne, S., Ortega-Ruiz, R.,
. . .Smith, P. K. (2012). Cyberbullying definition among adolescents: A com-
parison across six European countries. Cyberpsychology, Behavior, and Social
Networking, 15, 455-463. doi:10.1089/cyber.2012.0040
Olweus, D. (1993). Bullying at school: What we know and what we can do. Oxford,
UK, Cambridge, UK: Blackwell.
Olweus, D. (2003). A profile of bullying at school. Educational Leadership, 60(6),
12-17.
Ortega, R., Calmaestra, J., & Mora Merchán, J. (2008). Cyberbullying. International
Journal of Psychology and Psychological Therapy, 8, 183-192.
Owens, L., Shute, R., & Slee, P. (2000). “Guess what I just heard!” Indirect aggres-
sion among teenage girls in Australia. Aggressive Behavior, 26, 67-83.
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
20 Youth & Society
Patchin, J. W., & Hinduja, S. (2011). Traditional and nontraditional bullying among
youth: A test of general strain theory. Youth & Society, 43, 727-751.
Petermann, F. (2003). Klinische Kinderpsychologie Band 8: Bullying unter Schülern.
Erscheinungsformen, Risikobedingungen und Interventionskonzepte [Clinical
child psychology issue 8: Bullying among pupils: appearance, risk factors and
concepts for intervention]. Göttingen, Germany: Hogrefe.
Pinker, S. (2011). The better angels of our nature: Why violence has declined. New
York, NY: Viking.
Riebel, J. (2008). Spotten, Schimpfen, Schlagen . . . Gewalt unter Schülern—Bullying
und Cyberbullying [Taunting, harassing, punching… Violence among pupils:
bullying and cyberbullying]. Landau, Germany: Verlag Empirische Pädagogik.
Schermelleh-Engel, K., Moosbrugger, H., & Müller, H. (2003). Evaluating the fit of
structural equation models: Tests of significance and descriptive goodness-of-fit
measures. Methods of Psychological Research Online, 8(2), 23-74.
Seals, D., & Young, Y. (2004). Bullying and victimization: Prevalence and relation-
ship to gender, grade level, ethnicity, self-esteem and depression. Adolescence,
38, 735-747.
Sharp, S., & Smith, P. K. (1991). Bullying in the UK schools: The DES sheffield bul-
lying project. Early Child Development and Care, 77, 47-55.
Siann, G., Callaghan, M., Glissov, P., Lockhart, R., & Rawson, L. (1994). Who gets
bullied? The effect of school, gender and ethnic group. Educational Research,
36, 123-134.
Slonje, R., & Smith, P. K. (2008). Cyberbullying: Another main type of bully-
ing? Scandinavian Journal of Psychology, 49, 147-154. doi:10.1111/j.1467-
9450.2007.00611.x
Smith, P. K. (2009). Cyberbullying. Zeitschrift für Psychologie/Journal of Psychology,
217(4), 180-181. doi:10.1027/0044-3409.217.4.180
Smith, P. K., & Brain, P. (2000). Bullying in schools: Lessons from two decades of
research. Aggressive Behavior, 26, 1-9.
Smith, P. K., Cowie, H., Olafsson, R. F., & Liefooghe, A. P. (2002). Definitions
of bullying: A comparison of terms used, and age and gender differences, in a
fourteen-country international comparison. Child Development, 73, 1119-1133.
Smith, P. K., Del Barrio, C., & Tokunaga, R. S. (2013). Definitions of bullying
and cyberbullying: How useful are the terms? In S. Bauman, D. Cross, & J. L.
Walker (Eds.), Principles of cyberbullying research: Definitions, measures, and
methodology (pp. 26-40.). New York, NY: Routledge.
Smith, P. K., Mahdavi, J., Carvalho, M., Fisher, S., Russell, S., & Tippett, N. (2008).
Cyberbullying: Its nature and impact in secondary school pupils. Journal of
Child Psychology and Psychiatry, 49, 376-385.
Smith, P. K., Morita, Y., Junger-Tas, J., Olweus, D., Catalano, R. & Slee, P. (Eds.).
(1999). The nature of school bullying: A cross-national perspective. London,
England: Routledge.
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
Fluck 21
Tokunaga, R. S. (2010). Following you home from school: A critical review and
synthesis of research on cyberbullying victimization. Computers in Human
Behavior, 26, 277-287.
Willard, N. E. (2007). Cyberbullying and cyberthreats: Responding to the challenge
of online social aggression, threats, and distress. Champaign, IL: Research
Press.
Ybarra, M. L., & Mitchell, K. J. (2004). Online aggressor/targets, aggressors and
targets: A comparison of associated youth characteristics. The Journal of Child
Psychology and Psychiatry, 35, 1308-1316.
Author Biography
Julia Fluck is a researcher and lecturer at the Center for Educational Research. Her
research interests are psychological diagnostics and school bullying and violence as
well as cyberbullying.
Downloaded from yas.sagepub.com at TEXAS SOUTHERN UNIVERSITY on October 28, 2014
You might also like
- The Psychological Nature of Bullying and Its Determinants: A Study of Teenagers Living in the Country of GeorgiaFrom EverandThe Psychological Nature of Bullying and Its Determinants: A Study of Teenagers Living in the Country of GeorgiaNo ratings yet
- 2017, Fluck Why Do Students Bully An Analysis of Motives Behind Violence in SchoolsDocument21 pages2017, Fluck Why Do Students Bully An Analysis of Motives Behind Violence in SchoolsorangnooolepNo ratings yet
- The Black Male Triumph Story: Successfully Achieving Graduate DegreesFrom EverandThe Black Male Triumph Story: Successfully Achieving Graduate DegreesNo ratings yet
- School BullyingDocument136 pagesSchool Bullyingsupergaucho100% (1)
- Research Paper About Bullying IntroductionDocument5 pagesResearch Paper About Bullying Introductiongvzph2vh100% (1)
- Educational Resilience Among African Survivors of Child Sexual Abuse in South AfricaDocument20 pagesEducational Resilience Among African Survivors of Child Sexual Abuse in South AfricaDNo ratings yet
- PIPS Tarshis2007Document8 pagesPIPS Tarshis2007Raluca GeorgescuNo ratings yet
- Name: Hiba Zahra Class: BS Home Economics Section: B Semester: 2 Subject: Fundamentals of Research Teacher: Miss Faiza ZubairDocument23 pagesName: Hiba Zahra Class: BS Home Economics Section: B Semester: 2 Subject: Fundamentals of Research Teacher: Miss Faiza ZubairHiba ZahraNo ratings yet
- AP Dag-Uman - 1st PR - Phenomenological StudyDocument3 pagesAP Dag-Uman - 1st PR - Phenomenological StudyJOHN PATRICK BERSALOTENo ratings yet
- Research Paper About Bullying SlideshareDocument8 pagesResearch Paper About Bullying Slideshareqhujvirhf100% (1)
- Example of Introduction in Research Paper About BullyingDocument5 pagesExample of Introduction in Research Paper About Bullyinggz7gh8h0No ratings yet
- Psychology Research Papers On Media ViolenceDocument5 pagesPsychology Research Papers On Media Violenceaflbtrnpf100% (1)
- Thesis For Research Paper On BullyingDocument7 pagesThesis For Research Paper On Bullyingzufehil0l0s2100% (3)
- Thesis GuideDocument32 pagesThesis Guidemarianie calibayNo ratings yet
- Thesis of BullyingDocument7 pagesThesis of Bullyingsandygrassolowell100% (2)
- Bullying: The Impact of Bullying in The Growth of The Students in Yllana Bay View College Grade 11 Students of Morning ClassDocument4 pagesBullying: The Impact of Bullying in The Growth of The Students in Yllana Bay View College Grade 11 Students of Morning ClassCristine Joyce Campos ParojinogNo ratings yet
- Fpsyt 10 00868Document10 pagesFpsyt 10 00868shumailaNo ratings yet
- Ideas For A Research Paper On BullyingDocument4 pagesIdeas For A Research Paper On Bullyingfys374dr100% (3)
- Research Paper Bullying LawsDocument7 pagesResearch Paper Bullying Lawsefjk5y50100% (1)
- Group Research PaperDocument9 pagesGroup Research PaperLei Andrew PatunganNo ratings yet
- Introduction For A Research Paper On BullyingDocument4 pagesIntroduction For A Research Paper On Bullyingxvrdskrif100% (1)
- Research Paper About Bullying in SchoolsDocument4 pagesResearch Paper About Bullying in Schoolsefjddr4z100% (1)
- Conclusion For A Research Paper About BullyingDocument7 pagesConclusion For A Research Paper About Bullyingafnkjuvgzjzrgl100% (3)
- Group ResearchDocument11 pagesGroup ResearchHannah May CimafrancaNo ratings yet
- Bullying Research Paper ExamplesDocument6 pagesBullying Research Paper ExampleshfuwwbvkgNo ratings yet
- Research Paper About Bullying AbstractDocument5 pagesResearch Paper About Bullying Abstractscongnvhf100% (1)
- Research Paper On Violence in Public SchoolsDocument9 pagesResearch Paper On Violence in Public Schoolsqyptsxvkg100% (1)
- Thesis About Bullying in Elementary SchoolDocument7 pagesThesis About Bullying in Elementary Schoolpatriciamedinadowney100% (2)
- Review of Related Literature About Bullying in SchoolDocument5 pagesReview of Related Literature About Bullying in Schoolfvf2j8q0No ratings yet
- 14 PDFDocument7 pages14 PDFRosanna ayangwa LumasokNo ratings yet
- Literature Review On Bullying in SchoolsDocument8 pagesLiterature Review On Bullying in Schoolsc5se0nsw100% (1)
- Introduction in Research Paper About BullyingDocument7 pagesIntroduction in Research Paper About Bullyingnidokyjynuv2100% (1)
- Effects of Bullying in School ThesisDocument8 pagesEffects of Bullying in School Thesisafknyfene100% (2)
- Literature Review Example BullyingDocument6 pagesLiterature Review Example Bullyingaflsmawld100% (1)
- Example of Thesis Title About BullyingDocument7 pagesExample of Thesis Title About BullyingWhatIsTheBestPaperWritingServiceSingapore100% (2)
- Luczynski Fahmie 2017 Chapter PLSProsocial SkillsDocument13 pagesLuczynski Fahmie 2017 Chapter PLSProsocial SkillsLam KyuNo ratings yet
- How To Help Me Get Out of A Gang: Youth Recommendations To Family, School, Community, and Law Enforcement..Document38 pagesHow To Help Me Get Out of A Gang: Youth Recommendations To Family, School, Community, and Law Enforcement..Habib RahmanNo ratings yet
- Teachers Who Bully Students (Mcevoy)Document12 pagesTeachers Who Bully Students (Mcevoy)HildorienNo ratings yet
- 01 - Social Learning Theory Research Leap - Docx 16 59 03 219Document6 pages01 - Social Learning Theory Research Leap - Docx 16 59 03 219Jackie Anne Ugay AntigNo ratings yet
- Bullying and School Connectedness Among High School StudentsDocument18 pagesBullying and School Connectedness Among High School StudentsRonaldNo ratings yet
- Research Paper Topics For BullyingDocument5 pagesResearch Paper Topics For Bullyingfzjzn694100% (1)
- Bystanders Are The Key To Stopping BullyingDocument9 pagesBystanders Are The Key To Stopping Bullyingsantiago maciasNo ratings yet
- RESEARCH REPORT 2019-Ag-4504Document34 pagesRESEARCH REPORT 2019-Ag-4504Faseeha ShabbirNo ratings yet
- Chapter 1 Research Group 2Document5 pagesChapter 1 Research Group 2Alliah Monique ReyesNo ratings yet
- Research Final g11Document45 pagesResearch Final g11Adrian CasajeNo ratings yet
- Bullying Research Paper Thesis StatementDocument7 pagesBullying Research Paper Thesis StatementPayPeopleToWritePapersCanada100% (2)
- Literature Review BullyingDocument5 pagesLiterature Review Bullyingafmzvjvjzoeqtg100% (1)
- Empowering Self Defence Trainings Against Sex AssaltDocument21 pagesEmpowering Self Defence Trainings Against Sex AssaltstellaONo ratings yet
- Awareness and Prevention of Bullying Among Students of GGNHSDocument35 pagesAwareness and Prevention of Bullying Among Students of GGNHSGil Bert100% (1)
- Campus Bullying in The Senior High School A Qualitative Case StudyDocument9 pagesCampus Bullying in The Senior High School A Qualitative Case StudyNorman Galabo100% (1)
- Document (1) Practical Research by Garcia ShawnDocument10 pagesDocument (1) Practical Research by Garcia Shawnajcervantes065No ratings yet
- Research Paper On Bullying in The PhilippinesDocument4 pagesResearch Paper On Bullying in The Philippinesgafuz0zewez3100% (3)
- Cyberbullying Among High School Students Cluster ADocument26 pagesCyberbullying Among High School Students Cluster AAdrian Tan100% (1)
- Messy, Butch, and Queer: Journal of Adolescent Research January 2015Document27 pagesMessy, Butch, and Queer: Journal of Adolescent Research January 2015Karen AlvaradoNo ratings yet
- Bullying in Schools Research PaperDocument7 pagesBullying in Schools Research Papercjyjcyakf100% (1)
- Research Paper On Bullying in Schools PDFDocument8 pagesResearch Paper On Bullying in Schools PDFegja0g11100% (1)
- Consequences of Bullying in SchoolsDocument8 pagesConsequences of Bullying in SchoolsThe Three QueensNo ratings yet
- Research Paper On Violence in SchoolsDocument7 pagesResearch Paper On Violence in Schoolsjzneaqwgf100% (1)
- Literature Review Bullying in The WorkplaceDocument8 pagesLiterature Review Bullying in The Workplacerpmvtcrif100% (1)
- Recommendation Thesis Sample BullyingDocument5 pagesRecommendation Thesis Sample Bullyingd0t1f1wujap3100% (2)
- Hegel Zbornik 72 92Document21 pagesHegel Zbornik 72 92giovanniglembajevicNo ratings yet
- 12932-Article Text-46725-1-10-20201123Document6 pages12932-Article Text-46725-1-10-20201123giovanniglembajevicNo ratings yet
- Žunec - Marx's MeontologyDocument20 pagesŽunec - Marx's MeontologygiovanniglembajevicNo ratings yet
- Fuchs IntroductionDocument41 pagesFuchs IntroductiongiovanniglembajevicNo ratings yet
- Fuchs Influencer CapitalismDocument35 pagesFuchs Influencer CapitalismgiovanniglembajevicNo ratings yet
- Public - Private Life - ThompsonDocument23 pagesPublic - Private Life - ThompsongiovanniglembajevicNo ratings yet
- Lazarsfeld 1941 Admin Critical CommunicationDocument16 pagesLazarsfeld 1941 Admin Critical CommunicationgiovanniglembajevicNo ratings yet
- Boyadjieva (2017)Document18 pagesBoyadjieva (2017)giovanniglembajevicNo ratings yet
- Terrorism Experts and Theories of Scientific Production OKDocument20 pagesTerrorism Experts and Theories of Scientific Production OKgiovanniglembajevicNo ratings yet
- Espenshade, Hale Chung (2005)Document25 pagesEspenshade, Hale Chung (2005)giovanniglembajevicNo ratings yet
- Summary Writing History of ArtDocument5 pagesSummary Writing History of ArtgiovanniglembajevicNo ratings yet
- Edu 569Document2 pagesEdu 569Gresell DiazNo ratings yet
- The Impact of National Culture On Organizational Culture - HRMBDDocument4 pagesThe Impact of National Culture On Organizational Culture - HRMBDLorena BarrosNo ratings yet
- UK Professional Standards FrameworkDocument8 pagesUK Professional Standards FrameworkRohan DuttaNo ratings yet
- Dogs Communicating To HumansDocument3 pagesDogs Communicating To HumansMohammed OusmanNo ratings yet
- Unit1.5 Mathematics Helps Control Nature and The Occurrences in The World FDocument2 pagesUnit1.5 Mathematics Helps Control Nature and The Occurrences in The World FMelmel TheKnight88% (66)
- Writing A Comprehensive Report in Special EducationDocument54 pagesWriting A Comprehensive Report in Special EducationBrady Arnold100% (1)
- The Utility of MMPI-2-RF Scale Scores in The Differential Diagnosis of SchizophreniaDocument9 pagesThe Utility of MMPI-2-RF Scale Scores in The Differential Diagnosis of SchizophreniaskafonNo ratings yet
- Write A Play: Curriculum Guide - ExcerptDocument16 pagesWrite A Play: Curriculum Guide - Excerptusagibrian100% (1)
- Using Toys To Support Infant-Toddler Learning and DevelopmentDocument7 pagesUsing Toys To Support Infant-Toddler Learning and DevelopmenttebuluhNo ratings yet
- Week 2 DiscussionDocument3 pagesWeek 2 Discussionapi-528651903No ratings yet
- Effect of Bullying RRLDocument2 pagesEffect of Bullying RRLJenifer Languido CalautitNo ratings yet
- Egyptian EFL University Students' Negative Writing AffectDocument26 pagesEgyptian EFL University Students' Negative Writing AffectkareemhakeemNo ratings yet
- 1-Wall. 2006. An Autoethnography On Learning About AutoethnographyDocument12 pages1-Wall. 2006. An Autoethnography On Learning About AutoethnographydupaduNo ratings yet
- Part BDocument5 pagesPart BjeckNo ratings yet
- Giao Thoa Văn Hóa - Dhnn14a1hn - 010100165704 - Bùi Phương Trang - 20109100228Document15 pagesGiao Thoa Văn Hóa - Dhnn14a1hn - 010100165704 - Bùi Phương Trang - 20109100228Phuong Trang BuiNo ratings yet
- Post Observation Rating Scale For The Tools of The Mind Curriculum (Prs - Tom) Observer ManualDocument27 pagesPost Observation Rating Scale For The Tools of The Mind Curriculum (Prs - Tom) Observer ManualAsmaa AhmedNo ratings yet
- Theory of Object RelationDocument15 pagesTheory of Object RelationHAriom gangwarNo ratings yet
- Traditional and Online Learning: It's Effectiveness Towards Student's Skills DevelopmentDocument15 pagesTraditional and Online Learning: It's Effectiveness Towards Student's Skills DevelopmentKenneth DyNo ratings yet
- Student Teaching JournalDocument8 pagesStudent Teaching Journalapi-474721095No ratings yet
- How Is Language ArbitraryDocument4 pagesHow Is Language ArbitraryAsad MehmoodNo ratings yet
- Chapter 4 IntroductionDocument20 pagesChapter 4 IntroductionJanzell Anne Borja AlbaniaNo ratings yet
- Empirical StudiesDocument82 pagesEmpirical StudiesRapstar VyNo ratings yet
- Brainstorming As A Strategy in Teaching MathematicsDocument2 pagesBrainstorming As A Strategy in Teaching MathematicsRizal Leonardo100% (2)
- English 8 Curriculum MapDocument65 pagesEnglish 8 Curriculum MapMary Kryss DG Sangle80% (5)
- Ramirez, C. Week8 Gokongwei CULSOCPDocument3 pagesRamirez, C. Week8 Gokongwei CULSOCPChristine Ramirez82% (11)
- OJT Narrative ReportDocument25 pagesOJT Narrative ReportReggie Jr C. CuberosNo ratings yet
- Group 7 - Chapter 4 Key Teacher InterventionsDocument18 pagesGroup 7 - Chapter 4 Key Teacher InterventionsAbdul Qadir HamidNo ratings yet
- Bronfenbrenner 1977Document19 pagesBronfenbrenner 1977dtpaguio100% (1)
- PM1 SchizophreniaDocument12 pagesPM1 SchizophreniaShivani SharmaNo ratings yet
- Melcs-Based Budget of Lessons: English For Academic and Professional Purposes, RexDocument3 pagesMelcs-Based Budget of Lessons: English For Academic and Professional Purposes, RexAbi Refugio CabuñagNo ratings yet