Professional Documents
Culture Documents
Ijett V39P229
Ijett V39P229
Uploaded by
Nilanka HarshaniOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Ijett V39P229
Ijett V39P229
Uploaded by
Nilanka HarshaniCopyright:
Available Formats
See discussions, stats, and author profiles for this publication at: https://www.researchgate.
net/publication/308661220
The Understanding of GOST Cryptography Technique
Article in International Journal of Engineering Trends and Technology · October 2016
DOI: 10.14445/22315381/IJETT-V39P229
CITATIONS READS
11 4,048
3 authors, including:
Muhammad Iqbal Andysah Putera Utama Siahaan
Universitas Pembangunan Panca Budi Universitas Pembangunan Panca Budi
19 PUBLICATIONS 63 CITATIONS 331 PUBLICATIONS 2,602 CITATIONS
SEE PROFILE SEE PROFILE
Some of the authors of this publication are also working on these related projects:
Decision Support Systems View project
Decision Support System View project
All content following this page was uploaded by Andysah Putera Utama Siahaan on 27 September 2016.
The user has requested enhancement of the downloaded file.
International Journal of Engineering Trends and Technology (IJETT) – Volume 39 Number 3- September 2016
The Understanding of GOST Crytography
Technique
Muhammad Iqbal1, Yudi Sahputra2, Andysah Putera Utama Siahaan3
Faculty of Computer Science
Universitas Pembangunan Panca Budi
Jl. Jend. Gatot Subroto Km. 4,5 Sei Sikambing, 20122, Medan, Sumatera Utara, Indonesia
Abstract - Nowadays, it is often found a wide range of keywords in the order while eight last round uses the
the securing information. The understanding that the key in the reverse order.
author wants to design is about cryptography.
Cryptography is the study of the security of data or This understanding tries to describe the flow of the
information, commonly found in transferring data. GOST algorithm. It describes the basic rule of the key
One of them is the method of GOST, GOST is an generating. It also covers the round of the key. The
abbreviation of "Gosudarstvennyi Standard" or encryption and decryption will prove the GOST
"Government Standard." The algorithm is simple method has been done.
encryption algorithm which has some processes as
many as 32 rounds and uses 64-bit block cipher with II. THEORIES
256-bit key. GOST method also uses the S-Box 8 A. Definition
pieces of permanent and XOR operations and Rotate
Left Shift. The author chose the GOST topic since the GOST stands for "Gosudarstvennyi Standard" or
author wants to describe the understanding of the "Government Standard." Method GOST is a block
GOST method. The learning is presenting calculation cipher algorithm developed by a national of the Soviet
of the encryption and decryption. The learning course Union. This method was developed by the Soviet
is the study of cryptographic methods GOST. Learning Union during the Cold War to hide data or information
software is also designed so that the method can be that is confidential at the time of the communication
more easily understood GOST both algorithms and [3]. This algorithm is a simple encryption algorithm
operations contained in this GOST method. which has some processes as much as 32 round (round)
and uses 64-bit block cipher with 256-bit key. GOST
Keywords – Cryptography, GOST, Encryption, method also uses the S-Box 8 pieces different and
Decryption XOR operations and Circular Shift Left. Weakness
GOST known until now is because its key schedule is
I. INTRODUCTION simply that in certain circumstances be the weak point
of the method of cryptanalysis as Related-key
Encryption is the way to hide information from cryptanalysis. However, this can be resolved by
being stolen [2][7][8]. GOST is a cryptography passing the keys to a strong hash function in
algorithm made in Russia. This algorithm is a rival of cryptography such as SHA-1, and then use the results
the DES algorithm created by the United States to input initialization hash key. The advantage of this
[1][4][6]. Structurally, this algorithm is very similar to method is the speed GOST pretty good, although not
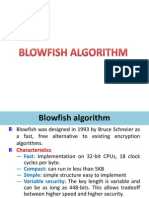
the DES algorithm. As with algorithms DES, GOST as fast as Blowfish, faster than IDEA.
algorithm uses the structure Feistel network
encryption. This algorithm has a block size of the 64- GOST structure such as:
bit message. Unlike the AES, it has a block size of the 1. Key Store Unit (KSU) stores 256-bit string
128-bit message. Every encryption and decryption by 32-bit register (K0, K1, …, K7).
algorithms have a key [5]. This algorithm also has 2. Twoof 32 bit register (R1, R2)
some rounds more than AES-256, which is 32 rounds. 3. 32 bit adder modulo 232 (CM1)
Each round uses eight key pieces scheduled internal 4. Bitwise Adder XOR (CM2)
use. Functions used in each round in the GOST 5. Substitusion block (S), an eight of 64 bit S-
algorithm is very simple. It just adds the subkey that Box.
in-mod with 232. Then the results are put into the S- 6. Left rotation shift register (R),11 bit.
box and rotate these results to the left as much as 11
bits. The results will be used in the next round. And so B. Key Structure
on up to 32 rounds. Key scheduling done by GOST is
very simple. First, the primary key into eight pieces The key structure process is the technique to compose
measuring 32-bit subkey. Each subkey is used four the password to encrypt the plaintext. This process can
times in the algorithm. Twenty-four first round use be seen as follow.
ISSN: 2231-5381 http://www.ijettjournal.org Page 168
International Journal of Engineering Trends and Technology (IJETT) – Volume 39 Number 3- September 2016
1. Input key, 256-bit key (k1, k2, k3, k4, …, 22 S 83 01010011
k256)
2. Generating of eight KSU 23 T 84 01010100
24 , 44 00101100
K0 = (k32, …, k1)
25 32 00100000
K1 = (k64, …, k33)
K2 = (k96, …, k65) 26 A 65 01000001
K3 = (k128, …, k97)
27 n 110 01101110
K4 = (k160, …, k129)
K5 = (k192, …, k161) 28 d 100 01100100
K6 = (k224, …, k193) 29 y 121 01111001
K7 = (k256, …, k225)
30 s 115 01110011
III. Result and Discussion 31 a 97 01100001
A. Key Generator
32 h 104 01101000
The process of formation of this key requires data
input with the key length of 256 bits or 64 In Table 1, there are 32 pieces of characters which
hexadecimal digits or 32 pieces of character. This are converted to the binary digit. It is used as a key to
process can be seen in the following example: process the encryption in GOST algorithm. The
Suppose key: “Kriptografi Metode GOST, Andysah”, conversion to the binary key of the 256-bit is as follow.
then the process of formation of the key above the key
is in the following table. 010010110111001001101001011100000111
010001101111011001110111001001100001
TABLE I 011001100110100100100000010011010110
KEY GENERATOR 010101110100011011110110010001100101
001000000100011101001111010100110101
010000101100001000000100000101101110
No. Coordinate X Y 011001000111100101110011011000010110
1 K 75 01001011 1000
2 r 114 01110010
The key will be categorized to eight parts.
3 i 105 01101001
K[0] :
4 p 112 01110000
0100101101110010011010010111000
5 t 116 01110100 0
K[1] :
6 o 111 01101111
0111010001101111011001110111001
7 g 103 01100111 0
8 r 114 01110010 K[2] :
0110000101100110011010010010000
9 a 97 01100001 0
10 f 102 01100110 K[3] :
0100110101100101011101000110111
11 i 105 01101001 1
12 32 00100000 K[4] :
0110010001100101001000000100011
13 M 77 01001101 1
14 e 101 01100101 K[5] :
0100111101010011010101000010110
15 t 116 01110100 0
16 o 111 01101111 K[6] :
0010000001000001011011100110010
17 d 100 01100100 0
18 e 101 01100101 K[7] :
0111100101110011011000010110100
19 32 00100000 0
20 G 71 01000111
21 O 79 01001111
ISSN: 2231-5381 http://www.ijettjournal.org Page 169
International Journal of Engineering Trends and Technology (IJETT) – Volume 39 Number 3- September 2016
B. Encryption Process R = 5125282998 mod 232
= 830315702
GOST encryption process of the method of = 00110001011111011001110010110110
processing the input plaintext data 64-bit or 16
hexadecimal digits or characters 8 through 32 stages (3) Split to 8 part and put to SBox.
of iterations (rounds). Suppose picking up the key on 0011 = 3 = SBOX(0) = 2 = 0010
the formation and plaintext "ENKRIPSI", then the 0001 = 1 = SBOX(1) = 11 = 1011
encryption process is as follows: 0111 = 7 = SBOX(2) = 2 = 0010
1101 = 13 = SBOX(3) = 2 = 0010
ENCRYPTION, ROUND 0 1001 = 9 = SBOX(4) = 10 = 1010
1100 = 12 = SBOX(5) = 9 = 1001
(1) PLAIN TEXT = ENKRIPSI 1011 = 11 = SBOX(6) = 7 = 0111
Convert to Binary= 0110 = 6 = SBOX(7) = 10 = 1010
0100010101001110010010110101001001001001010
100000101001101001001 (4) Concatenate and Rotate Left Shift 11 times.
L(0) = 10010010110010100000101010010010 RLS(11)=0001010101001011110100010101100
R(0) = 01001010110100100111001010100010 1
(2) R(0) + K(0) mod 232 (5) R(2) = R(1) XOR L(1)
R( 0) = 1255305890 R( 1) = 00010101010010111101000101011001
K( 0) = 244731602 L( 1) = 01001010110100100111001010100010
-------------------------------- + --------------------------------------------------- XOR
R = 1500037492 mod 232 R( 2) = 01011111100110011010001111111011
= 1500037492
= (6) L(2) = R(1) before process.
01011001011010001100000101110100 L(2) = 11100010100101101010011010001000
o
(3) Split to 8 part and put to SBox. o
0101 = 5 = SBOX(0) = 8 = 1000
1001 = 9 = SBOX(1) = 3 = 0011 The process will continue until Round 31.
0110 = 6 = SBOX(2) = 4 = 0100
1000 = 8 = SBOX(3) = 14 = 1110 ENCRYPTION, ROUND 31
1100 = 12 = SBOX(4) = 0 = 0000
0001 = 1 = SBOX(5) = 11 = 1011 (1) L(31) = 10110101101111001100010101011110
0111 = 7 = SBOX(6) = 9 = 1001 R(31) = 10011000110000000111100010010101
0100 = 4 = SBOX(7) = 5 = 0101
(2) R(31) + K(0) mod 232
(4) Concatenate and Rotate Left Shift 11 times. R(31) = 2562750613
RLS(11)=0111000001011100101011000001101 K( 0) = 244731602
0 -------------------------------- +
R = 2807482215 mod 232
(5) R(1) = R(0) XOR L(0) = 2807482215
R( 0) = 01110000010111001010110000011010 = 10100111010101101100011101100111
L( 0) = 10010010110010100000101010010010
-------------------------------------------------- (3) Split to 8 part and put to SBox.
XOR 1010 = 10 = SBOX(0) = 1 = 0001
R( 1) = 11100010100101101010011010001000 0111 = 7 = SBOX(1) = 10 = 1010
0101 = 5 = SBOX(2) = 3 = 0011
(6) L(1) = R(0) before process. 0110 = 6 = SBOX(3) = 9 = 1001
L(1) = 01001010110100100111001010100010 1100 = 12 = SBOX(4) = 0 = 0000
0111 = 7 = SBOX(5) = 13 = 1101
ENCRYPTION, ROUND 1 0110 = 6 = SBOX(6) = 5 = 0101
0111 = 7 = SBOX(7) = 4 = 0100
(1) L(1) = 01001010110100100111001010100010
R(1) = 11100010100101101010011010001000 (4) Concatenate and Rotate Left Shift 11 times.
RLS(11)=1100100001101010101000001101000
(2) R(1) + K(1) mod 232 1
R( 1) = 3801523848
K( 1) = 1323759150 (5) R(32) = R(31) before process.
-------------------------------- + R(32) = 10011000110000000111100010010101
ISSN: 2231-5381 http://www.ijettjournal.org Page 170
International Journal of Engineering Trends and Technology (IJETT) – Volume 39 Number 3- September 2016
R( 1) = 10110101101111001100010101011110
(6) L(32) = R(31) XOR L(31)
R(31) = 11001000011010101010000011010001 (6) L(1) = R(0) before process.
L(31) = 10110101101111001100010101011110 L(1) = 10011000110000000111100010010101
------------------------------------------------------ XOR
L(32) = 01111101110101100110010110001111 DECRYPTION, ROUND 1
(7) L(32) = b(32), b(31), ... b(1) (1) L(1) = 10011000110000000111100010010101
R(32) = a(32), a(31), ... a(1) R(1) = 10110101101111001100010101011110
R = a(1), ... a(32), b(1), ... b(32)
Rin binary = 10101001000111100000 (2) R(1) + K(1) mod 232
0011000110011111000110100110011010111011 R( 1) = 3049047390
1110 = convert to text K( 1) = 1323759150
-------------------------------- +
CIPHER TEXT = © ñ¦k¾ R = 4372806540 mod 232
= 77839244
C. Decryption Process = 00000100101000111011101110001100
The decryption process is the reverse of the (3) Split to 8 part and put to SBox.
encryption process. GOST decryption process of the 0000 = 0 = SBOX(0) = 4 = 0100
method of using the same algorithm with the 0100 = 4 = SBOX(1) = 6 = 0110
encryption process. Suppose picking up the key 1010 = 10 = SBOX(2) = 12 = 1100
establishment and ciphertext above, the decryption 0011 = 3 = SBOX(3) = 1 = 0001
process is as follows: 1011 = 11 = SBOX(4) = 14 = 1110
1011 = 11 = SBOX(5) = 5 = 0101
DECRYPTION, ROUND 0 1000 = 8 = SBOX(6) = 0 = 0000
1100 = 12 = SBOX(7) = 6 = 0110
(1) CIPHER TEXT = © ñ¦k¾
Convert to binary = (4) Concatenate and Rotate Left Shift 11 times.
RLS(11)=0000111100101000001100100011011
1010100100011110000000110001100111110001101 0
001100110101110111110
L(0) = 01111101110101100110010110001111 (5) R(2) = R(1) XOR L(1)
R(0) = 10011000110000000111100010010101 R( 1) = 00001111001010000011001000110110
L( 1) = 10011000110000000111100010010101
(2) R(0) + K(0) mod 232 ---------------------------------------------------- XOR
R( 0) = 2562750613 R( 2) = 10010111111010000100101010100011
K( 0) = 244731602
-------------------------------- + (6) L(2) = R(1) before process.
R = 2807482215 mod 232 L(2) = 10110101101111001100010101011110
= 2807482215 o
= 10100111010101101100011101100111 o
(3) Split to 8 part and put to SBox. The process continues until Round 31.
1010 = 10 = SBOX(0) = 1 = 0001
0111 = 7 = SBOX(1) = 10 = 1010 DECRYPTION, ROUND 31
0101 = 5 = SBOX(2) = 3 = 0011
0110 = 6 = SBOX(3) = 9 = 1001 (1) L(31) = 11100010100101101010011010001000
1100 = 12 = SBOX(4) = 0 = 0000 R(31) = 01001010110100100111001010100010
0111 = 7 = SBOX(5) = 13 = 1101
0110 = 6 = SBOX(6) = 5 = 0101 (2) R(31) + K(0) mod 232
0111 = 7 = SBOX(7) = 4 = 0100 R(31) = 1255305890
K( 0) = 244731602
(4) Concatenate and Rotate Left Shift 11 times. -------------------------------- +
RLS(11)=11001000011010101010000011010001 R = 1500037492 mod 232
= 1500037492
(5) R(1) = R(0) XOR L(0) = 01011001011010001100000101110100
R( 0) = 11001000011010101010000011010001
L( 0) = 01111101110101100110010110001111 (3) Split to 8 part and put to SBox.
---------------------------------------------------- XOR 0101 = 5 = SBOX(0) = 8 = 1000
ISSN: 2231-5381 http://www.ijettjournal.org Page 171
International Journal of Engineering Trends and Technology (IJETT) – Volume 39 Number 3- September 2016
1001 = 9 = SBOX(1) = 3 = 0011 [8] A. P. U. Siahaan, “Factorization Hack of RSA Secret Numbers,”
0110 = 6 = SBOX(2) = 4 = 0100 International Journal of Engineering Trends and Technology,
vol. 37, no. 1, pp. 15-18, 2016.
1000 = 8 = SBOX(3) = 14 = 1110
1100 = 12 = SBOX(4) = 0 = 0000
0001 = 1 = SBOX(5) = 11 = 1011
0111 = 7 = SBOX(6) = 9 = 1001
0100 = 4 = SBOX(7) = 5 = 0101
(4) Concatenate and Rotate Left Shift 11 times.
RLS(11)=01110000010111001010110000011010
(5) R(32) = R(31) before process.
R(32) = 01001010110100100111001010100010
(6) L(32) = R(31) XOR L(31)
R(31) = 01110000010111001010110000011010
L(31) = 11100010100101101010011010001000
------------------------------------------------------- XOR
L(32) = 10010010110010100000101010010010
(7) L(32) = b(32), b(31), ... b(1)
R(32) = a(32), a(31), ... a(1)
R = a(1), ... a(32), b(1), ... b(32)
R in binary = 01000101010011100100
1011010100100100100101010000010100110100
1001 = change to Text
PLAIN TEXT = ENKRIPSI
IV. CONCLUSION
The downside of the GOST algorithm is a simple
key schedule so that in certain circumstances be the
weak point of the method of cryptanalysis as Related-
key cryptanalysis. However, this can be resolved by
passing the keys to a strong hash function in
cryptography such as SHA-1, and then use the results
to input initialization hash key. The advantage of this
method is the speed GOST is pretty good.Although
not as fast as Blowfish, it is faster than IDEA.
REFERENCES
[1] M. Varnamkhasti, “Overview of the Algorithms for Solving the
Multidimensional Knapsack Problems,” Advanced Studies in
Biology, vol. 4, no. 1, pp. 37-47, 2012.
[2] N. Courtois dan G. V. Bard, “Algebraic Cryptanalysis of the
Data Encryption Standard, In Cryptography and Coding,” dalam
11-th IMA Conference, 2007.
[3] L. Babenko dan E. Maro, “Algebraic Cryptanalysis of GOST
Encryption Algorithm,” Journal of Computer and
Communications, vol. 2, no. 1, pp. 10-17, 2014.
[4] C. E. Shannon, “Communication Theory of Secrecy Systems,”
Bell System Technical Journal, vol. 28, no. 1, pp. 656-715,
1949.
[5] N. T. Courtois, “Cryptanalysis of GOST In The Multiple-Key
Scenario,” Tatra Mountains Mathematical Publication, vol. 57,
no. 1, pp. 45-63, 2013.
[6] E. Biham dan A. Shamir, “Differential Cryptanalysis of DES-
like Cryptosystems,” Journal of Cryptology, vol. 4, no. 1, pp. 3-
72, 1991.
[7] A. P. U. Siahaan dan R. Rahim, “Dynamic Key Matrix of Hill
Cipher Using Genetic Algorithm,” International Journal of
Security and Its Applications, vol. 10, no. 8, pp. 173-180, 2016.
ISSN: 2231-5381 http://www.ijettjournal.org Page 172
View publication stats
You might also like
- Gates 'N' Fences: Website Usability ReviewDocument8 pagesGates 'N' Fences: Website Usability ReviewMisty A. Adams-SpackmanNo ratings yet
- Lab 3 Grip Strength LabDocument3 pagesLab 3 Grip Strength LabSofwan JuewekNo ratings yet
- HIGHT: A New Block Cipher Suitable For Low-Resource DeviceDocument14 pagesHIGHT: A New Block Cipher Suitable For Low-Resource DeviceFaisal khanNo ratings yet
- HIGHT: A New Block Cipher Suitable For Low-Resource DeviceDocument14 pagesHIGHT: A New Block Cipher Suitable For Low-Resource DeviceSaurabhNo ratings yet
- Hight PDFDocument14 pagesHight PDFarjun25767No ratings yet
- Improvement in Aes and Ecc: Submitted By: Shabir Ahmad Magray 19MMS010Document14 pagesImprovement in Aes and Ecc: Submitted By: Shabir Ahmad Magray 19MMS010Shabir9237No ratings yet
- BlowFish (Cipher) 20161124Document14 pagesBlowFish (Cipher) 20161124Rami Khalil RouchdiNo ratings yet
- Sensors 14 00975 v2Document20 pagesSensors 14 00975 v2HTEDGNo ratings yet
- AES T-Box SlidesDocument35 pagesAES T-Box SlidesAhmad RushdanNo ratings yet
- A Fast VLSI Design of SMS4 Cipher Based On Twisted BDD S-Box ArchitectureDocument4 pagesA Fast VLSI Design of SMS4 Cipher Based On Twisted BDD S-Box ArchitectureVijay SagarNo ratings yet
- Algebraic AnalysisDocument17 pagesAlgebraic AnalysisibrahimNo ratings yet
- T55 AESEncryptionSecurityDocument28 pagesT55 AESEncryptionSecurityReinardus Surya PradhityaNo ratings yet
- Paper 1: February 2021Document30 pagesPaper 1: February 2021zubair nawazNo ratings yet
- Aes Algorithm For Encryption: Radhika D.BajajDocument6 pagesAes Algorithm For Encryption: Radhika D.BajajamrinNo ratings yet
- Spectral Analysis of ZUC-256: Jing Yang, Thomas Johansson and Alexander MaximovDocument23 pagesSpectral Analysis of ZUC-256: Jing Yang, Thomas Johansson and Alexander MaximovSaurabhNo ratings yet
- Security Evaluation of GOST 28147-89 in View of inDocument16 pagesSecurity Evaluation of GOST 28147-89 in View of inBlack AkatsukiNo ratings yet
- Security Evaluation of GOST 28147-89 in View of International Standardisation Nicolas T. CourtoisDocument15 pagesSecurity Evaluation of GOST 28147-89 in View of International Standardisation Nicolas T. CourtoisRobert BratcherNo ratings yet
- Data Encryption Routines For The PIC18Document34 pagesData Encryption Routines For The PIC18andrel0No ratings yet
- Loki 97Document22 pagesLoki 97Diego Durán100% (1)
- Performance Analysis of Data Encryption Standard DESDocument5 pagesPerformance Analysis of Data Encryption Standard DESEditor IJTSRDNo ratings yet
- A Further Optimized Mix Column Architecture Design For The Advanced Encryption StandardDocument21 pagesA Further Optimized Mix Column Architecture Design For The Advanced Encryption StandardShabbirNo ratings yet
- ProjectDocument8 pagesProjectChaitanya SPNo ratings yet
- Mod2 3Document80 pagesMod2 3geles73631No ratings yet
- SboxDocument7 pagesSboxZeco Neco100% (1)
- 2206 14107Document13 pages2206 14107Ali QasimNo ratings yet
- GUI Implementation of Image Encryption and Decryption Using Open CV-Python Script On Secured TFTP ProtocolDocument9 pagesGUI Implementation of Image Encryption and Decryption Using Open CV-Python Script On Secured TFTP Protocolvijay kumarNo ratings yet
- Security Enhancement of Blowfish Block Cipher: August 2016Document9 pagesSecurity Enhancement of Blowfish Block Cipher: August 2016addis alemuNo ratings yet
- Roadrunner: A Small and Fast Bitslice Block Cipher For Low Cost 8-Bit ProcessorsDocument20 pagesRoadrunner: A Small and Fast Bitslice Block Cipher For Low Cost 8-Bit Processorspanos pNo ratings yet
- IDEA and Blowfish NotesDocument10 pagesIDEA and Blowfish NotesMukesh100% (2)
- Implement Are SErpent PR FPGAJaroslawDocument6 pagesImplement Are SErpent PR FPGAJaroslawghionoiucNo ratings yet
- Lightweight Block Ciphers Revisited CryptanalysisDocument19 pagesLightweight Block Ciphers Revisited CryptanalysisFaisal khanNo ratings yet
- Computer and Network Security: Simplified Data Encryption Standard (DES)Document21 pagesComputer and Network Security: Simplified Data Encryption Standard (DES)Aisha Saman KhanNo ratings yet
- Block Ciphers: 3.1 What Is A Block Cipher?Document19 pagesBlock Ciphers: 3.1 What Is A Block Cipher?hdl_dcvNo ratings yet
- Data Encryption StandardDocument44 pagesData Encryption StandardAnkur AgrawalNo ratings yet
- IDEA by How Shen Chang 2004 FALLDocument11 pagesIDEA by How Shen Chang 2004 FALLSeemant HeeraNo ratings yet
- A Survey of The Elliptic Curve Integrated Encryption Scheme: January 2010Document8 pagesA Survey of The Elliptic Curve Integrated Encryption Scheme: January 2010Dhafin KawakibiNo ratings yet
- CRP2Document29 pagesCRP2sstcbakchodsNo ratings yet
- Class 12th Apogee BITS PilaniDocument22 pagesClass 12th Apogee BITS PilaniVishal MahajanNo ratings yet
- Attacks On The Keeloq Block Cipher and Authentication SystemsDocument13 pagesAttacks On The Keeloq Block Cipher and Authentication SystemsRoberto ZeitounNo ratings yet
- An Efficient Hardware Design and Implementation of Advanced Encryption Standard (AES) AlgorithmDocument5 pagesAn Efficient Hardware Design and Implementation of Advanced Encryption Standard (AES) AlgorithmmianNo ratings yet
- ICCAI 2018 Final PDFDocument6 pagesICCAI 2018 Final PDFGalaxian NoteNo ratings yet
- Cryptanalysis of Magenta: I I T I B IDocument3 pagesCryptanalysis of Magenta: I I T I B IsadsdaNo ratings yet
- Z Cryptogrphic AlgorithmsDocument71 pagesZ Cryptogrphic AlgorithmsSurangma ParasharNo ratings yet
- Cryptography by Karatsuba Multiplier With ASCII Codes: International Journal of Computer Applications February 2010Document10 pagesCryptography by Karatsuba Multiplier With ASCII Codes: International Journal of Computer Applications February 2010Mudit JainNo ratings yet
- A Comparative Study On AES 128 BIT AND AES 256 BITDocument5 pagesA Comparative Study On AES 128 BIT AND AES 256 BITAlexander Hurtado CubillosNo ratings yet
- MIPS-Core Application Specific Instruction-Set Processor For IDEA Cryptography Comparison Between Single-Cycle and Multi-Cycle ArchitecturesDocument13 pagesMIPS-Core Application Specific Instruction-Set Processor For IDEA Cryptography Comparison Between Single-Cycle and Multi-Cycle ArchitecturesEng SaziNo ratings yet
- Improved Authenticated Elliptic Curve Cryptography Scheme For Resource Starve ApplicationsDocument17 pagesImproved Authenticated Elliptic Curve Cryptography Scheme For Resource Starve ApplicationsCSIT iaesprimeNo ratings yet
- CNS Unit 3Document178 pagesCNS Unit 3sonor25972No ratings yet
- Cys505 Lecture03Document90 pagesCys505 Lecture03Abdirizak AbokarNo ratings yet
- 2011 Chapter PiccoloAnUltra-LightweightBloc PDFDocument16 pages2011 Chapter PiccoloAnUltra-LightweightBloc PDFKristian HendersonNo ratings yet
- Stebila Prototyping Post QuantumDocument24 pagesStebila Prototyping Post QuantumRobert Mourey JrNo ratings yet
- BlowfishDocument62 pagesBlowfishDhaval DoshiNo ratings yet
- Sensors 14 00975Document21 pagesSensors 14 00975abdelli aliNo ratings yet
- FPGA Implementation of Rectangle Lightweight Block CipherDocument10 pagesFPGA Implementation of Rectangle Lightweight Block CipherIJRASETPublicationsNo ratings yet
- Unit 2Document92 pagesUnit 2teja mNo ratings yet
- Implementation of Aes Algorithm Using Verilog: Gireesh Kumar P, P. Mahesh KumarDocument4 pagesImplementation of Aes Algorithm Using Verilog: Gireesh Kumar P, P. Mahesh KumarVasanth VasuNo ratings yet
- Encryption: CS 465 January 9, 2006 Tim Van Der HorstDocument32 pagesEncryption: CS 465 January 9, 2006 Tim Van Der HorstAnand Mohan ReddyNo ratings yet
- Advanced Network Security: Chap 2: Encription TechniquesDocument93 pagesAdvanced Network Security: Chap 2: Encription TechniquesSaja KareemNo ratings yet
- Cys535 Lecture03Document70 pagesCys535 Lecture03Waseem LaghariNo ratings yet
- Federal University of Technology AkureDocument9 pagesFederal University of Technology AkuretarvsNo ratings yet
- Assignment #: Shaheed Zulfikar Ali Bhutto Institute of Science &Document9 pagesAssignment #: Shaheed Zulfikar Ali Bhutto Institute of Science &M annonymousNo ratings yet
- Practical Embedded Controllers: Design and Troubleshooting with the Motorola 68HC11From EverandPractical Embedded Controllers: Design and Troubleshooting with the Motorola 68HC11No ratings yet
- The ATLAS Experiment at The CERN Large Hadron ColliderDocument300 pagesThe ATLAS Experiment at The CERN Large Hadron ColliderLeighton KendelyNo ratings yet
- Contents ReDocument8 pagesContents ReLeighton KendelyNo ratings yet
- Seeking Uniting Advancing Training: European Organization For Nuclear ResearchDocument4 pagesSeeking Uniting Advancing Training: European Organization For Nuclear ResearchLeighton KendelyNo ratings yet
- Dust and Its ControlDocument6 pagesDust and Its ControlLeighton KendelyNo ratings yet
- Introduction To The Internet and World Wide Web: Richard C. Van SluytersDocument6 pagesIntroduction To The Internet and World Wide Web: Richard C. Van SluytersLeighton KendelyNo ratings yet
- F21116007 - Skripsi - 1-2Document41 pagesF21116007 - Skripsi - 1-2Leighton KendelyNo ratings yet
- The Inverted Pyramid: Lesson 3Document4 pagesThe Inverted Pyramid: Lesson 3Leighton KendelyNo ratings yet
- 4-Congruence and TrianglesDocument4 pages4-Congruence and TrianglesLeighton KendelyNo ratings yet
- Quality Assurance BrochureDocument2 pagesQuality Assurance BrochureLeighton KendelyNo ratings yet
- Mark Scheme - Designing Interactive MediaDocument2 pagesMark Scheme - Designing Interactive MediaLeighton KendelyNo ratings yet
- Implementation of Cost Management Initiative:: "Paper-Cut Print Management"Document1 pageImplementation of Cost Management Initiative:: "Paper-Cut Print Management"Leighton KendelyNo ratings yet
- Father S Day Father S Day Father S DayDocument5 pagesFather S Day Father S Day Father S DayLeighton KendelyNo ratings yet
- Getting Started With Microsoft TeamsDocument40 pagesGetting Started With Microsoft TeamsLeighton KendelyNo ratings yet
- Drug Addiction PosterDocument1 pageDrug Addiction PosterLeighton Kendely0% (1)
- Evaluación Diagnóstica 4º InglésDocument9 pagesEvaluación Diagnóstica 4º InglésSharon Carola Ruiz GarciaNo ratings yet
- Industrial Power Distribution and Illumination Chapter 7:illuminating Design PrincipleDocument15 pagesIndustrial Power Distribution and Illumination Chapter 7:illuminating Design PrincipleViktor IartavNo ratings yet
- Chemistry Investigatory Project Class 12Document18 pagesChemistry Investigatory Project Class 12Tushar ChopraNo ratings yet
- Bourdieu NotesDocument7 pagesBourdieu NotesfiliafouNo ratings yet
- C 02 S & D (R & 3D S) : MEC 430 - Machine Design - IIDocument80 pagesC 02 S & D (R & 3D S) : MEC 430 - Machine Design - IIAhmd MahmoudNo ratings yet
- PENGARUH EKSTRAK DAUN KELOR (Moringa Oleifera L.) Terhadap Kualitas YoghurtDocument8 pagesPENGARUH EKSTRAK DAUN KELOR (Moringa Oleifera L.) Terhadap Kualitas YoghurtChaaNo ratings yet
- Objectives: The C++ Programming Skills That Should Be Acquired in This LabDocument9 pagesObjectives: The C++ Programming Skills That Should Be Acquired in This Labstudent wwNo ratings yet
- Y4 Unit 1 Our CommunityDocument12 pagesY4 Unit 1 Our Communitymerlyn90No ratings yet
- A Commerce in ButterfliesDocument6 pagesA Commerce in ButterfliesJenika Jean ReanzaresNo ratings yet
- 3 Different Ways To Display Progress in An ASP - Net AJAXDocument7 pages3 Different Ways To Display Progress in An ASP - Net AJAXNehaNo ratings yet
- Egyptian Dance Pe 1Document21 pagesEgyptian Dance Pe 1Jysn JsNo ratings yet
- Intercultural Communication (By O.L. Kocheva)Document21 pagesIntercultural Communication (By O.L. Kocheva)ЕкатеринаNo ratings yet
- James Fowler's Stages of Faith Tantra SongDocument2 pagesJames Fowler's Stages of Faith Tantra SongWangshosanNo ratings yet
- Chapter 1. Electronic Components & SignalsDocument12 pagesChapter 1. Electronic Components & SignalsPavankumar Gosavi100% (2)
- 5 Compeitior 2021Document22 pages5 Compeitior 2021杜昕No ratings yet
- Frespac Ginger (Fiji) Pte Limited Audited Financials 30.6.23 8.9.23Document135 pagesFrespac Ginger (Fiji) Pte Limited Audited Financials 30.6.23 8.9.23Augustine SamiNo ratings yet
- Business Income &expensesDocument6 pagesBusiness Income &expensesNurain Nabilah ZakariyaNo ratings yet
- Revolutionizing Data Warehousing in Telecom With The Vertica Analytic DatabaseDocument11 pagesRevolutionizing Data Warehousing in Telecom With The Vertica Analytic DatabasegrandelindoNo ratings yet
- Tuna BurgersDocument1 pageTuna BurgersmirnafkhouryNo ratings yet
- Safe Back Exercises: The Extensors. Craig LiebensonDocument1 pageSafe Back Exercises: The Extensors. Craig LiebensonrojexeNo ratings yet
- Joan Cruz V Royal Supermart Plaintiff Position PaperDocument6 pagesJoan Cruz V Royal Supermart Plaintiff Position PaperKringNo ratings yet
- Hoffman: Spotmaster Spotting Boards and Cabinets - The Most Complete Range of Spotting Systems!Document2 pagesHoffman: Spotmaster Spotting Boards and Cabinets - The Most Complete Range of Spotting Systems!NugagodaNo ratings yet
- Moodle - Copy - SQLDocument184 pagesMoodle - Copy - SQL'Aan AndriaNo ratings yet
- Professional Ethics: Dr. Ehsan Ul HassanDocument4 pagesProfessional Ethics: Dr. Ehsan Ul HassanHuzaifah TariqNo ratings yet
- Ict ModuleDocument26 pagesIct ModuleSai GuyoNo ratings yet
- Haroon Report FinalDocument13 pagesHaroon Report Finalharoon100% (1)
- Shiftwork Disorder - 0617Document2 pagesShiftwork Disorder - 0617hector ignacio CastellucciNo ratings yet
- Lulik: The Core of Timorese Values (Published Version)Document14 pagesLulik: The Core of Timorese Values (Published Version)Josh TrindadeNo ratings yet