Professional Documents
Culture Documents
Ransomware Readiness Guide
Uploaded by
adminakOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Ransomware Readiness Guide
Uploaded by
adminakCopyright:
Available Formats
Ransomware Readiness:
An In-Depth Evaluation Guide
Strengthen Your Data Security & Cyber Resiliency
Ransomware Readiness:
An In-Depth Evaluation Guide
Contents
The Increasing Blast Radius of Ransomware................................................................................ 3
Critical Actions Countering Ransomware...................................................................................... 3
Protect Your Backup Data and System........................................................................................... 4
Ransomware Isn’t Going Away........................................................................................................ 4
Reduce the Risk of Unauthorized Access....................................................................................... 7
See and Detect Attacks to Stop Encroachment ............................................................................ 8
Strengthen Your Security Posture With Platform Extensibility ............................................... 10
Ensure You Can Rapidly Recover Data at Scale........................................................................... 12
Checklist: Ransomware Readiness Evaluation............................................................................ 13
Be Ready for Ransomware with Cohesity ................................................................................... 15
©2023 Cohesity. All rights reserved. 2
Ransomware Readiness:
An In-Depth Evaluation Guide
The Increasing Blast Radius of Ransomware
Cybercriminals are coming for the data that powers your business. How successful they’ll be at extorting
ransom depends on what you do today to fortify your environment and improve your ability to respond should
an attack occur.
Ransomware threats are evolving. Targets and tactics are expanding. If it hasn’t happened already, soon you’ll
be asked how you’re countering the various ways in which cybercriminals are aiming to disrupt your operations.
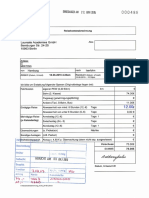
Ransomware 1.0 Ransomware 2.0 Ransomware 3.0
Malware target Production data • Backup data • Backup data
• Backup systems • Backup systems
• Production data • Production data
• Data to illegally
remove
Method of attack Encryption Encryption Encryption and
exfiltration
How companies Backup & recovery Immutable backups and Early detection and
are countering the system cyber vaulting continuous monitoring
attack
Critical Actions Countering Ransomware
If you’re unsure what to do first to strengthen your organization’s cyber resiliency, this guide is for you. It’s
full of practical information and evaluation criteria about what to look for in a data management solution to
bolster your data security strategy. You can also use it to complement the tools your SecOps team uses as
you work together on how best to respond to ever-changing ransomware threats. This guide also features a
checklist to reference as you compare the effectiveness of your existing solutions against our modern data
security and management solutions.
Better protecting your data and your company’s reputation starts by understanding how these five critical
actions empower your organization to counter ransomware:
• Protect Your Backup Data and System
• Reduce the Risk of Unauthorized Access
• See and Detect Attacks to Stop Encroachment
• Strengthen Your Security Posture with Integrations and APIs
• Ensure You Can Rapidly Recover Data at Scale
©2023 Cohesity. All rights reserved. 3
Ransomware Readiness:
An In-Depth Evaluation Guide
Ransomware Isn’t Going Away
1,070% 82% >$1.85 M >$265 B
The percent ransomware The percent average The average cost now to The amount global
grew between July 2020 ransomware payments rectify ransomware attack ransomware damage
and June of 20211 climbed since 2020 to a impacts without paying the costs—lost revenue and
record $570,000 in the ransom3 productivity as well as
first half of 20212 rebuilding—are predicted
to exceed by 20314
Protect Your Backup Data and System
Data safeguards are fundamental to preserving customer trust and keeping your competitive edge. They
counter evolving ransomware threats, including new ones such as “Lockers” that completely shut you out of
your system files and applications while showing you a countdown clock to an expected ransom payment date
and time. Without improving your safeguards, your business has no way of protecting your data from being
encrypted—or worse, stolen—by cybercriminals.
For optimal data resiliency across hybrid and multicloud environments, be sure these six non-negotiable
backup security capabilities are part of any data management solution you’re seriously considering.
Immutable Snapshots
Software-based, native immutable backup snapshots effectively throw up a wall against
ransomware attacks because they can’t be encrypted, modified or deleted—all common tactics
cybercriminals use to force a ransomware payment. This is extremely important for protecting the
authenticity of data, particularly massive amounts of unstructured data such as audio and video
files as well as images required in certain industries such as law enforcement and healthcare.
Unlike hardware-based immutability, the native read-only snapshots housed onsite or in clouds are
never exposed nor mounted externally to any application; they can’t be tampered with, altered or
removed. That makes it hard for malware to target your backup data.
1
FortiGuard Labs. “Global Threat Landscape Report,” August 2021.
2
Palo Alto Networks. “Extortion Payments Hit New Records as Ransomware Crisis Intensifies,” August 9, 2021.
3
Sophos. “The State of Ransomware 2021,” 2021.
4
Cybersecurity Ventures. “Global Ransomware Damage Costs Predicted To Exceed $265 Billion By 2031,” June 3, 2021.
©2023 Cohesity. All rights reserved. 4
Ransomware Readiness:
An In-Depth Evaluation Guide
WORM
Mechanisms such as write once, read many (WORM) technology provide another layer of protection
against a ransomware attack. They allow teams to create and apply a time-bound lock on data
through policies and then assign them to selected jobs to enhance immutability for protected data.
As this is a protection that neither security officers nor security admins can modify or delete, you
don’t have to worry as much about potential insider threats.
Data Encryption
There’s encryption and then there’s software-based FIPS-validated, AES-256 standard
encryption for data in flight and at rest. You want the cryptographic module validated by the
United States National Institute of Standards and Technology (NIST) at the Federal Information
Processing Standards (FIPS) 140-2 Level 1 standard. FIPS 140-2 is a U.S. government standard
for cryptographic modules providing assurances that the module design and implementation of
cryptographic algorithms are secure and correct. FIPS validated encryption is more secure because
products with this distinction pass a rigorous set of tests to be certified to the extent that this has
become valued globally.
Configuration Audit and Scanning
Your IT team is likely now operating many different systems and tools—all with their own set ups,
policies and management interfaces. The manual processes to run them often introduce avoidable
human error. Wouldn’t it be nice if there was a more efficient way? An automated system with
guided scanning that audits various data security and access control settings helps you avoid costly
human mistakes while simplifying your data operations from set up to policies to management
processes.
Fault Tolerance
Because data resilience should always be a guiding security principle, you also need a fault-tolerant
system that helps ensure data integrity and successful backups even in the harshest conditions.
Some of those are when your systems are near full compute, memory or storage capacity; when
you have considerable network congestion; or when you unexpectedly experience a hardware
failure. Look for a solution built with fault tolerance that allows backups to continue in spite of a
failed component/node.
©2023 Cohesity. All rights reserved. 5
Ransomware Readiness:
An In-Depth Evaluation Guide
Modern and Flexible Cyber Vaulting
A companion consideration as you modernize your data management approach is updating your
cyber vaulting strategy. Traditionally, organizations have relied on tapes to maintain air gapped
copies, but that method can no longer keep up with today’s demanding service-level agreements
(SLAs) when it comes to recovery times—particularly those experienced during a widespread
ransomware attack. Despite the term “air gap” protection now being widely misused to describe
techniques that do not maintain an actual gap, don’t be misled. Be sure your data security and
management solution offers both real air gap protection as well as modern options to achieve
cyber vaulting. These balance modern recovery time objective and recovery point objective (RTO/
RPO) requirements with appropriate security controls by storing backup data in the cloud or at
another location with a temporary and highly secure connection. You then get a tamper-resistant
environment, preventing ransomware and insider threat disruption while optimizing for meeting
your organizational SLAs. Best of all, you always retain a copy of your data in an immutable format.
TOP 4 QUESTIONS TO ASK ABOUT BACKUP
DATA AND SYSTEMS
• What does your data management solution do to
protect your backed up data against ransomware
attacks?
• How does your solution continuously back up
workloads even after the failure of a hardware or
software component?
• How does your solution balance needs for stronger
security with ever-faster digital business RTOs/RPOs
that meet SLAs?
• In what ways does your solution provide visibility
into the security gaps in the system configuration
and operational design?
©2023 Cohesity. All rights reserved. 6
Ransomware Readiness:
An In-Depth Evaluation Guide
Reduce the Risk of Unauthorized Access
Bad actors are working for themselves, syndicates and nation states. That’s why it’s an increasingly strategic
move for your business to have a data management solution with strict access controls. These capabilities
can more effectively stop unauthorized access from external hackers or rogue internal professionals taking
advantage of compromised credentials.
To lower your risk of data theft and loss, look for a solution that builds in the principles of least privilege and
segregation of duties with granular security—including the following four must-have capabilities. They keep
your data safe and your customers confident.
Multi-factor Authentication
Regularly compromised, even the most creative passwords can provide only a minimum layer of
security protection for digital businesses. Multi-factor authentication (MFA) is a step forward in
mitigating against phishing schemes and other password hacks. It requires everyone accessing
your backup or data management solution to undergo a multi-step verification requirement
process. They must authenticate—with both something they “know” (e.g., a password) and
something they “have” (e.g., a thumbprint validated by a single sign-on [SSO] provider) to prove
they are who they say they are. Insist any of your short-listed solutions require MFA.
Monitored Modification
Because someone watching can be enough to thwart an attack, you will want a capability that
prevents one compromised credential or individual from modifying critical elements of your data
management solution. Insist on having a platform that helps enforce safeguards, for example,
requiring a root-level or any other critical system change to be authorized by more than one person
so you can protect against malicious intent and stolen credentials.
Granular Role-based Access Control
When it comes to data, effective management of identity and access are increasingly the
cornerstones of good cyber hygiene. Reducing ransomware and insider threats now depends on
IT staff granting each person a minimum level of access to all of the organization’s data needed
to do a particular job and at the same time spreading critical data processes and functions across
IT roles so no single administrator can compromise your whole business. Organizations with data
management solutions that simplify approaches to granular role-based access control (RBAC) do a
better job of thwarting unauthorized access and risking data while efficiently granting their users
appropriate privileges to do their work.
©2023 Cohesity. All rights reserved. 7
Ransomware Readiness:
An In-Depth Evaluation Guide
TOP 3 QUESTIONS TO ASK ABOUT REDUCING
RISK OF UNAUTHORIZED ACCESS
• What does your backup or data management
solution do to prevent unauthorized access to
business data?
• How does your solution protect against both
ransomware and the insider threat?
• How do I set up multi-user approval for critical
operations?
See and Detect Attacks to Stop Encroachment
Digital business moves fast. Business owners increasingly need to know what sensitive data they have,
where it’s located and who has access to it. This is key to complying with industry or government regulations,
maintaining trust and rapidly responding to double-extortion (a.k.a. data exfiltration) attacks.
To minimize the potential blast radius of ransomware, look for a data management solution with intelligence
baked in so you can automatically discover and classify sensitive data while enjoying near real time threat
detection. Find a solution that helps your team work smarter, not harder, and includes four critical capabilities
for proactive response—no matter what threats come your way.
Artificial Intelligence/Machine Learning Powered
Your organization needs data to thrive. But that data is exponentially increasing, making it
impossible for some data management solutions to perform effective pattern matching and
data classification so you know what matters most. In contrast, a modern data security and
management solution powered by artificial intelligence and machine learning (AI/ML) assists your
organization to more accurately detect variations and reduce false positives without adding staff.
You can take advantage of AI/ML techniques to match to “known good” sets of data and do that
more effectively and efficiently as your “known sensitive data” is matched and fed back to the AI/
ML algorithm. Think of it this way, you want to find the needle in the haystack without a lot of heavy
hay-bale lifting.
©2023 Cohesity. All rights reserved. 8
Ransomware Readiness:
An In-Depth Evaluation Guide
Anomaly Detection in Near Real Time
The faster you find an intrusion, the less damage it can do to your business—and the fewer nights
and weekends you burden your IT pros. Powerful automated anomaly detection in near real time
as part of a data management solution continually tracks normal system operations to quickly spot
irregularities and abnormal user behaviors that can signify a ransomware attack. Coupled with
alerting, these capabilities don’t just signal potential danger but can also initiate remediation. With
anomaly detection in near real time, you enjoy fast discovery of both encryption-style and data
exfiltration attacks in progress and that helps you minimize ransomware’s impact.
Understand Attack Impact
When an anomaly is detected, use ML/NLP to determine if sensitive data has been exposed and
determine appropriate remediation and compliance processes. Ensure you can support global
deployments with prepackaged and customizable patterns.
Find Potential Threats in Recovery Data
Reduce your recovery risk by ensuring your backup data is malware free with threat detection
driven by threat intelligence and deep learning. Leverage threat feeds and intelligence to look for
indicators of compromise (IOCs) that can signal an impending attack.
Cyber Vulnerability Discovery
Cybercriminals are known to exploit software and cyber vulnerabilities—often left open due to
unpatched software—to gain access to your production environment. The most effective backup
and data management solutions should help your team gain visibility into those vulnerabilities. It
should also help you proactively address them as well as avoid reinjecting already addressed cyber
vulnerabilities back into your production environment while recovering from an attack.
©2023 Cohesity. All rights reserved. 9
Ransomware Readiness:
An In-Depth Evaluation Guide
TOP 4 QUESTIONS TO ASK TO HELP STOP
ENCROACHMENT
• How does your solution help classify data and identify
sensitive information that may be at risk?
• What does your backup or data management solution do
to provide deep visibility to help identify software and
cyber vulnerabilities, and offer near real time anomaly
detection?
• How does your solution incorporate AI/ML to detect
anomalies that can signify a threat or a ransomware attack?
• How does your solution detect system-level and user
behavior anomalies that indicate different attack vectors?
Strengthen Your Security Posture With Platform
Extensibility
Ransomware isn’t a single threat. It’s evolving and becoming more sophisticated with every iteration. That
means your data management solution cannot be inflexible nor work in isolation; it needs to be future-proof
and extensible. Integrated and interoperable solutions empower your organization to detect, investigate and
confidently respond to threats faster. They’re also the most likely to defeat bad actors.
Look for a modern data management solution that supports third-party collaboration to enhance your data
security; one that ensures flexibility yet provides secure ways to simplify operations and make your data
productive. To build a strong security posture, any solution you consider should include these three must-have
capabilities and play nicely with others.
Pre-built Integrations
Data security concerns keep business leaders up at night. They could sleep better if they had
confidence their trusted security products were working seamlessly together to fight cybercrime.
Find a data management solution that’s already tightly integrated with leading security
orchestration, automation and response (SOAR) as well as security information event management
(SIEM) solutions. It will accelerate time to discovery, investigation and remediation of ransomware
attacks. And be sure it also has pre-built, integrated workflows that are extensible, enabling
SecOps to augment them for automated incident response and unified operations across security,
IT and networking teams.
©2023 Cohesity. All rights reserved. 10
Ransomware Readiness:
An In-Depth Evaluation Guide
Customizable Integrations
Change is constant. But not all data management platforms help you keep up with it. Your
organization needs a cyber resilient solution that works to counter ransomware while also
addressing unique business requirements. Make sure in addition to pre-built integrations that the
solution you select has a secure software development kit (SDK) and customizable management
APIs that give you the flexibility to operate your environment the way you want.
Value-Added Applications Interoperability
In addition to pre-built and customizable integrations within an API-rich architecture that helps
streamline operations, you need a platform that offers ways to future-proof while enhancing
data security. Instead of making copies of data and moving them around, find a solution that
allows you to reuse the data in-place by bringing value-add applications to data for routine and
more challenging tasks—from virus scanning and data masking to analyzing file audit logs and
classifying data. An extensible platform will help reduce your data footprint and attack surface as
well as empower you to derive more value from your investments.
TOP 4 QUESTIONS TO ASK TO ENSURE
EXTENSIBILITY AND INTEROPERABILITY
• What security integrations does your backup or data
management solution support?
• How does your solution work with other leading
security products and platforms?
• How does your solution extract insights while keeping
data safe?
• How does your backup or data management solution
improve team collaboration by eliminating platform,
people and process silos?
©2023 Cohesity. All rights reserved. 11
Ransomware Readiness:
An In-Depth Evaluation Guide
Ensure You Can Rapidly Recover Data at Scale
Should the worst-case scenario happen and ransomware find a way into your production environment, you
need a solution that gives you the power to refuse to pay ransom. Look for a solution with these three non-
negotiable data recovery capabilities to give you that confidence.
Instant Recovery at Scale
If ransomware attackers strike, they aren’t targeting one or two virtual machines (VMs) or
databases anymore. Rather, they want to lock up as much of your data in systems as possible.
That’s why organizations today need a data management solution that can quickly recover
hundreds of systems. An instant recovery at scale capability allows you to rapidly restore hundreds
of VMs, large databases or large volumes of unstructured data instantly, at scale, to any point in
time and location.
Clean Recovery
*In-place Recovery
Provisioning a clean environment after an attack can take time, and restoring to the original
environment could compromise forensics efforts. This can slow down your recovery efforts
(something you definitely don’t want when you’re working hard to get back to business). Find a
data management solution that allows you to recover data directly in-place on the same platform—
without spinning up a new server or database. It will save you time and money.
©2023 Cohesity. All rights reserved. 12
Ransomware Readiness:
An In-Depth Evaluation Guide
TOP 4 QUESTIONS TO ASK TO CONFIRM YOU
CAN RAPIDLY RECOVER AT SCALE
• What does your backup or data management solution
do to help you rapidly, cleanly and predictably recover
data at scale?
• Does your backup system have sufficient resources to
support rapid recovery to any point in time and to any
location?
• What capabilities does your solution support to assess
a snapshot’s health and recover unstructured data
without additional investment?
• How does your data management solution perform
in-place recovery of unstructured data to reduce
downtime?
©2023 Cohesity. All rights reserved. 13
Ransomware Readiness:
An In-Depth Evaluation Guide
Checklist: Ransomware Readiness Evaluation
Cybercriminals are hard at work. You need a data management and data security strategy that can help you
keep up with evolving threats and minimize the impact of ransomware. Rethinking your data management
solution is a good place to start. As you evaluate your options, this checklist of key capabilities can help you
zero in on the best-fit solution for your organization.
Action Key Capability Vendor 1 Vendor 2 Vendor 3 Vendor 4
Protect Your Backup Immutable Snapshots
Data and System
WORM
Data Encryption
Configuration Audit and
Scanning
Fault Tolerance
Modern and Flexible
Cyber Vaulting
Reduce the Risk of Multi-factor Authentication
Unauthorized Access (MFA)
Monitored Modification
Granular Role-based Access
Control (RBAC)
See and Detect Attacks AI/ML Powered
to Stop Encroachment
Anomaly Detection in Near
Real Time
Automated Alerts
Cyber Vulnerability Discovery
Strengthen Your Security Pre-built Integrations
Posture with Platform
Extensibility Customizable Integrations
Value-added Applications
Interoperability
Ensure You Can Rapidly Instant Recovery at Scale
Recover Data at Scale
Clean Recovery
In-place Recovery
©2023 Cohesity. All rights reserved. 14
Ransomware Readiness:
An In-Depth Evaluation Guide
Be Ready for Ransomware with Cohesity
Cohesity makes it simple for your organization to backup, manage, secure, and derive value
from your data—in the data center, edge, and cloud. Use Cohesity software to manage data
infrastructure directly, or have it managed for you through a Cohesity SaaS service, or both.
Cohesity solves mass data fragmentation, makes data compliance a snap, and helps businesses
thwart ransomware attacks.
Cohesity was named a Leader on the Gartner Magic Quadrant for Data Center Backup and
Recovery Solutions and a Leader in “The Forrester Wave™: Data Resiliency Solutions.” The company
is featured in the 2022 Forbes Cloud 100 (for the 4th time), in CRN’s Coolest Cloud Companies of
2022 (for the 3rd time), and is the top-ranked Leader among 16 vendors in the GigaOm Radar for
Unstructured Data Management.
Modernize your data security and management platform today
www.cohesity.com
Learn more at cohesity.com
© 2023 Cohesity, Inc. All rights reserved.
Cohesity, the Cohesity logo, SnapTree, SpanFS, DataPlatform, DataProtect, Helios, the Helios logo, DataGovern, SiteContinuity, and other Cohesity marks are trademarks or registered trademarks of
Cohesity, Inc. in the US and/or internationally. Other company and product names may be trademarks of the respective companies with which they are associated. This material (a) is intended to provide you
information about Cohesity and our business and products; (b) was believed to be true and accurate at the time it was written, but is subject to change without notice; and (c) is provided on an “AS IS” basis.
Cohesity disclaims all express or implied conditions, representations, warranties of any kind.
Cohesity.com | 1-855-926-4374 | 300 Park Ave., Suite 1700, San Jose, CA 95110 4500043-003-EN 7-2023
You might also like
- CyberSense For Dell PowerProtect Cyber Recovery 1656644381Document12 pagesCyberSense For Dell PowerProtect Cyber Recovery 1656644381Marcelo MafraNo ratings yet
- Cyber-Security-Infographic - FCADocument1 pageCyber-Security-Infographic - FCAMousumi Utkarsh RayNo ratings yet
- Solution Brief: Ransomware Targets Endpoints With Devasting Impact Key CapabilitiesDocument4 pagesSolution Brief: Ransomware Targets Endpoints With Devasting Impact Key CapabilitiesPepe890No ratings yet
- Veeam Ransomware Solution BriefDocument2 pagesVeeam Ransomware Solution BriefAwanish DwivediNo ratings yet
- Mitigating Ransomware With Zero TrustDocument18 pagesMitigating Ransomware With Zero TrustMohamed SayedNo ratings yet
- Veeam Ransomware 6 Capabilities Rapid RecoveryDocument13 pagesVeeam Ransomware 6 Capabilities Rapid Recoveryansar89No ratings yet
- 20 CRI Ransomware PlaybookDocument7 pages20 CRI Ransomware PlaybookjagsraoNo ratings yet
- Securing Your Organization From Modern Ransomware: Ransomware Attacks Are Now A Team EffortDocument11 pagesSecuring Your Organization From Modern Ransomware: Ransomware Attacks Are Now A Team EfforttiagouebemoraisNo ratings yet
- 0XugMG7BRKieMmJ0fmcQ - Veeam VMware Cloudian Ransomware ProtectionDocument4 pages0XugMG7BRKieMmJ0fmcQ - Veeam VMware Cloudian Ransomware Protectionsiramc3075No ratings yet
- 勒索软件建立安全备份作为你的最后一道防线Document13 pages勒索软件建立安全备份作为你的最后一道防线青葱冯No ratings yet
- Keatronevans 2023 JulyransomwarepptDocument15 pagesKeatronevans 2023 JulyransomwarepptLuis felizNo ratings yet
- Ransomware Executive One-Pager and Technical Document-FINAL PDFDocument10 pagesRansomware Executive One-Pager and Technical Document-FINAL PDFNeenu SukumaranNo ratings yet
- The Ultimate Guide To Managing Ransomware RiskDocument8 pagesThe Ultimate Guide To Managing Ransomware RiskGhostNo ratings yet
- Securing Your AWS Cloud Environment From RansomwareDocument19 pagesSecuring Your AWS Cloud Environment From RansomwarechloreshockgmailNo ratings yet
- Csol 560 Assignment 7Document12 pagesCsol 560 Assignment 7api-737202431No ratings yet
- DNS AM-Trap-Whitepaperv2.2Document4 pagesDNS AM-Trap-Whitepaperv2.2Pooja GuptaNo ratings yet
- Technical Document Ransomware Prevention and ResponseDocument9 pagesTechnical Document Ransomware Prevention and ResponseZohair Altaf GondalNo ratings yet
- 2016 Trends in Cybersecurity:: A Quick Guide To The Most Important Insights in SecurityDocument24 pages2016 Trends in Cybersecurity:: A Quick Guide To The Most Important Insights in SecurityhelmuthNo ratings yet
- Akamai 5 Step Ransomware Defense EbookDocument9 pagesAkamai 5 Step Ransomware Defense EbookNilesh RoyNo ratings yet
- Combating RansomwareDocument4 pagesCombating RansomwareAzreakhsh RoshangarNo ratings yet
- Risks and Metric in Software SystemsDocument7 pagesRisks and Metric in Software Systemsapi-522484422No ratings yet
- Ransomware OnePager 160822USDocument2 pagesRansomware OnePager 160822UStiagouebemoraisNo ratings yet
- How Ransomware Attacks Exploit Active DirectoryDocument19 pagesHow Ransomware Attacks Exploit Active DirectoryNan Win AungNo ratings yet
- Ransomware Guide Seven Capabilities Rapid Reliable RecoveryDocument13 pagesRansomware Guide Seven Capabilities Rapid Reliable Recoveryjmcr03@gmailNo ratings yet
- Sophos Best Practices For Securing Your Network WPDocument8 pagesSophos Best Practices For Securing Your Network WPankiuNo ratings yet
- Lacework - WP - Ransomware - Rising - 040422 - V4Document8 pagesLacework - WP - Ransomware - Rising - 040422 - V4Vladislav AlekseevNo ratings yet
- RANSOMWARE PPTDocument17 pagesRANSOMWARE PPTVenugopal67% (3)
- Ext 89621Document3 pagesExt 89621Gamer LoverNo ratings yet
- Cyber Riskmgmt AwarenessDocument33 pagesCyber Riskmgmt AwarenessDaniel EsterNo ratings yet
- Protecting Your Enterprise Databases From Ransomware: White PaperDocument6 pagesProtecting Your Enterprise Databases From Ransomware: White PaperSudi ForFrndzNo ratings yet
- Cyber Chief Magazine June 2022Document52 pagesCyber Chief Magazine June 2022AnthonyNo ratings yet
- Endpoint Protection Ransomware Effectiveness ReportDocument10 pagesEndpoint Protection Ransomware Effectiveness ReportCookie CluverNo ratings yet
- Big Data PDFDocument17 pagesBig Data PDFMichel M MbayedNo ratings yet
- ? Protect Your Business From A Cyber Attack ?Document1 page? Protect Your Business From A Cyber Attack ?M. Tanveer BhattíNo ratings yet
- Infographic - 15 Ways To Protect Your Business From A Cyber Attack PDFDocument1 pageInfographic - 15 Ways To Protect Your Business From A Cyber Attack PDFGrzegorz PogodaNo ratings yet
- IVI 2028 Cybersecurity For Extreme ThreatsDocument9 pagesIVI 2028 Cybersecurity For Extreme ThreatsErnesto MorenoNo ratings yet
- Platform For A Safe and Secure Commercial System: Information Security InitiativesDocument2 pagesPlatform For A Safe and Secure Commercial System: Information Security InitiativesAdnan Puji WahyudiNo ratings yet
- Ransomware AttackDocument3 pagesRansomware AttackNUR NABILAH SHAFIQAH BINTI ROSLINo ratings yet
- Ransomware - Ransomware Protection GuideDocument7 pagesRansomware - Ransomware Protection GuideDeep PNo ratings yet
- 2024Q1AgainstRansomware WebinarDocument71 pages2024Q1AgainstRansomware WebinarNilesh NiraleNo ratings yet
- The MSPs Response Guide To A Ransomware AttackDocument4 pagesThe MSPs Response Guide To A Ransomware Attackderic soonNo ratings yet
- CyberSecurity 1 PDFDocument4 pagesCyberSecurity 1 PDFShubhamNo ratings yet
- WP Prepare Recover From RansomwareDocument19 pagesWP Prepare Recover From Ransomwaremaja1301No ratings yet
- SmallBusiness BuyersGuide PDFDocument15 pagesSmallBusiness BuyersGuide PDFNarendra SendhavNo ratings yet
- Machine Learning and Cryptographic Algorithms - Analysis and Design in Ransomware and Vulnerabilities DetectionDocument9 pagesMachine Learning and Cryptographic Algorithms - Analysis and Design in Ransomware and Vulnerabilities DetectionMogabs MogabsNo ratings yet
- Cyber Attack and Data BreachDocument19 pagesCyber Attack and Data BreachArchi BhandariNo ratings yet
- Best Practices For Ransomware ProtectionDocument17 pagesBest Practices For Ransomware Protectionshankar rNo ratings yet
- Ransomware Prevention Checklist:: 5 Steps To PrepareDocument3 pagesRansomware Prevention Checklist:: 5 Steps To PrepareJuan Sebastián Portilla JiménezNo ratings yet
- AstiIndahFadhila 312010260 NetworkScurityebookDocument11 pagesAstiIndahFadhila 312010260 NetworkScurityebookAsti Indah fadhilaNo ratings yet
- Ransomware Attacks Strategies For Prevention and RecoveryDocument20 pagesRansomware Attacks Strategies For Prevention and RecoverysainarendraNo ratings yet
- 12 Steps To Protect Against RansomwareDocument15 pages12 Steps To Protect Against RansomwarediniscamposNo ratings yet
- Endpoints at The Edge: The Stakes Keep Rising: Executive SummaryDocument4 pagesEndpoints at The Edge: The Stakes Keep Rising: Executive SummaryriyasathsafranNo ratings yet
- SSD-Insider: Internal Defense of Solid-State Drive Against Ransomware With Perfect Data RecoveryDocument10 pagesSSD-Insider: Internal Defense of Solid-State Drive Against Ransomware With Perfect Data Recoverymeena meenakshiNo ratings yet
- What Is Malware? - Definition and Examples - CiscoDocument11 pagesWhat Is Malware? - Definition and Examples - CiscoKap MPNo ratings yet
- Preparing For A Cyber Incident - A Guide To Ransomware V 1.1Document3 pagesPreparing For A Cyber Incident - A Guide To Ransomware V 1.1Franco André Calderon YalanNo ratings yet
- IBM Security Ransomware Client Engagement GuideDocument46 pagesIBM Security Ransomware Client Engagement GuideOmarNo ratings yet
- Vmware Best Practices To Protect Ransomware NSX SecurityDocument1 pageVmware Best Practices To Protect Ransomware NSX SecurityMartin MorávekNo ratings yet
- ITC263 S Lesson5Document29 pagesITC263 S Lesson5lawerenceNo ratings yet
- 805-Article Text-3656-1-10-20220310Document16 pages805-Article Text-3656-1-10-20220310abolfazlshamsNo ratings yet
- APAC Endpoint Security PracticesDocument1 pageAPAC Endpoint Security PracticesadminakNo ratings yet
- Veeam Definitive Guide 2023Document36 pagesVeeam Definitive Guide 2023adminakNo ratings yet
- Addressing The Office 365 Monitoring Gap (7.2)Document15 pagesAddressing The Office 365 Monitoring Gap (7.2)adminakNo ratings yet
- Backup and Recovery For ServiceNow 0516Document12 pagesBackup and Recovery For ServiceNow 0516adminakNo ratings yet
- Curtin University Case StudyDocument2 pagesCurtin University Case StudyadminakNo ratings yet
- IT Infrastructure Monitoring For DummiesDocument49 pagesIT Infrastructure Monitoring For DummiesadminakNo ratings yet
- Ebook EndpointDocument8 pagesEbook EndpointadminakNo ratings yet
- Windows and Physical Servers Backup Best PracticesDocument43 pagesWindows and Physical Servers Backup Best PracticesadminakNo ratings yet
- 10 Outstanding Linux Backup Utilities: FwbackupsDocument3 pages10 Outstanding Linux Backup Utilities: FwbackupsadminakNo ratings yet
- General iOS RestrictionsDocument9 pagesGeneral iOS RestrictionsadminakNo ratings yet
- An A-Z Index of Commands: Windows PowershellDocument8 pagesAn A-Z Index of Commands: Windows PowershelladminakNo ratings yet
- Step-By-Step App Deployment Via Microsoft IntuneDocument8 pagesStep-By-Step App Deployment Via Microsoft IntuneadminakNo ratings yet
- AgendaDocument2 pagesAgendaadminakNo ratings yet
- General iOS RestrictionsDocument9 pagesGeneral iOS RestrictionsadminakNo ratings yet
- Visio-DEP Setup Drawing1Document1 pageVisio-DEP Setup Drawing1adminakNo ratings yet
- In 2012Document5 pagesIn 2012adminakNo ratings yet
- How To Use Phishing Alert in MS-Intune OutlookDocument7 pagesHow To Use Phishing Alert in MS-Intune OutlookadminakNo ratings yet
- Add Users To Office 365 With Windows PowerShellDocument3 pagesAdd Users To Office 365 With Windows PowerShelladminakNo ratings yet
- MAXON EportfolioDocument1 pageMAXON EportfolioadminakNo ratings yet
- Managing Devices & Corporate Data On iOSDocument14 pagesManaging Devices & Corporate Data On iOSadminakNo ratings yet
- Configure and Deploy Intune MDMDocument92 pagesConfigure and Deploy Intune MDMadminak100% (1)
- Ms IntuneTutorialDocument23 pagesMs IntuneTutorialadminakNo ratings yet
- Add Users To Office 365 With Windows PowerShellDocument3 pagesAdd Users To Office 365 With Windows PowerShelladminakNo ratings yet
- Business Analyst On IT Infrastructure Client Print PDFDocument2 pagesBusiness Analyst On IT Infrastructure Client Print PDFadminakNo ratings yet
- 05996520150709130739Document1 page05996520150709130739adminakNo ratings yet
- Symantec Endpoint Protection 50 CloudDocument6 pagesSymantec Endpoint Protection 50 CloudadminakNo ratings yet
- Setting Up A Shared Mailbox On Your iOS DeviceDocument2 pagesSetting Up A Shared Mailbox On Your iOS DeviceadminakNo ratings yet
- Add Users To Office 365 With Windows PowerShellDocument3 pagesAdd Users To Office 365 With Windows PowerShelladminakNo ratings yet
- Gsmme Admin Guide: G Suite Migration For Microsoft ExchangeDocument54 pagesGsmme Admin Guide: G Suite Migration For Microsoft ExchangeadminakNo ratings yet
- Guidelines of PBL - MBA (22-24) Sem IIDocument8 pagesGuidelines of PBL - MBA (22-24) Sem IIShivnath KarmakarNo ratings yet
- Ps2 3 KHDocument14 pagesPs2 3 KHBranden933No ratings yet
- Emerging TechnologiesDocument8 pagesEmerging TechnologiesYasmin MohammedNo ratings yet
- Three Phase Full and Semi Converter - R and RL LoadDocument18 pagesThree Phase Full and Semi Converter - R and RL LoadDHINESH J100% (1)
- Service Manual: Split Type Room Air ConditionerDocument14 pagesService Manual: Split Type Room Air ConditionerMuhamad PriyatnaNo ratings yet
- WSN Classroom KitDocument2 pagesWSN Classroom KitAditya MaratheNo ratings yet
- VRZ Usa Iphone 11 128GBDocument1 pageVRZ Usa Iphone 11 128GBDamien Tucson100% (2)
- An Overview of LTE PositioningDocument12 pagesAn Overview of LTE PositioningJose Carlos Mendez PenaNo ratings yet
- Q.Peak Duo L-G7: Enduring High PerformanceDocument2 pagesQ.Peak Duo L-G7: Enduring High Performancehechano2No ratings yet
- Adams Herb Chassis EngineeringDocument142 pagesAdams Herb Chassis EngineeringTapare Ankush90% (39)
- MYSWEETY GRBL Offline ControllerDocument7 pagesMYSWEETY GRBL Offline ControllerJuan José Bagur ColominasNo ratings yet
- Internal Audit Checklist StoresDocument2 pagesInternal Audit Checklist Storesdhir.ankurNo ratings yet
- SRN Raptakos PLANTDocument41 pagesSRN Raptakos PLANTscribd viewerNo ratings yet
- SMF&W 851-01-07 Manual Arc Welding 220319Document9 pagesSMF&W 851-01-07 Manual Arc Welding 220319Shahid RazaNo ratings yet
- Technical Support Engineer - JDDocument2 pagesTechnical Support Engineer - JDKshitiz SagarNo ratings yet
- Internalisation StrategyDocument12 pagesInternalisation StrategyANEESH KULSHRESTHANo ratings yet
- Operating System (17CS64)Document3 pagesOperating System (17CS64)Pranove ABNo ratings yet
- Profile - National Car RentalDocument1 pageProfile - National Car RentalPedro Filipe CunhaNo ratings yet
- Chapter 1 - Introduction To System AdministrationDocument27 pagesChapter 1 - Introduction To System AdministrationAbdul KilaaNo ratings yet
- Business Letter ExampleDocument5 pagesBusiness Letter ExampleAhl BkdNo ratings yet
- NM-238 GBDocument27 pagesNM-238 GBShania GintingNo ratings yet
- Bharat Petroleum: Star PEB India Private LimitedDocument10 pagesBharat Petroleum: Star PEB India Private LimitedParvinder Kaur100% (1)
- Aluminium Extrusion Process PlanningDocument10 pagesAluminium Extrusion Process PlanningHarshith Rao VadnalaNo ratings yet
- Tia Eia 568 B.1 PDFDocument94 pagesTia Eia 568 B.1 PDFMartin MoyanoNo ratings yet
- Crowdsourcing and Social Engagement:: Potential, Power and Freedom For Libraries and UsersDocument73 pagesCrowdsourcing and Social Engagement:: Potential, Power and Freedom For Libraries and Usersjaypee pengNo ratings yet
- Verilog HDL: Special ClassesDocument11 pagesVerilog HDL: Special ClassesUnique ProNo ratings yet
- CS103 Syllabus: Date Topics Readings Assignments M January 8Document3 pagesCS103 Syllabus: Date Topics Readings Assignments M January 8Dupla PaltaNo ratings yet
- Evolving Business Models of Online Food Delivery Industry in Indian ContextDocument8 pagesEvolving Business Models of Online Food Delivery Industry in Indian ContextDeepak TyagiNo ratings yet
- 1001 Solved Electrical Engineering ProblemsDocument798 pages1001 Solved Electrical Engineering ProblemsHero Cordova de Guzman95% (20)
- Compal Confidential: Dali & Astro BKA40/BKA50/BKD40/BKD50 MB Schematic Document LA-D822PDocument46 pagesCompal Confidential: Dali & Astro BKA40/BKA50/BKD40/BKD50 MB Schematic Document LA-D822PPhạm CườngNo ratings yet