Professional Documents
Culture Documents
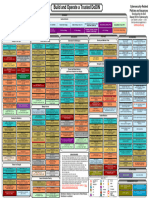
CYBERSECURITY
Uploaded by
MNEMOSYNNE BUENO0 ratings0% found this document useful (0 votes)
6 views19 pagesCybersecurity involves defending computers and networks from malicious attacks like cybercrime, cyber-attacks, and cyberterrorism. There are many types of malware threats such as viruses, trojans, ransomware, adware, and botnets. Other common cyber threats are SQL injection attacks, phishing scams, man-in-the-middle attacks, and denial-of-service attacks. To stay safe, it is important to keep software updated, use antivirus software, employ strong unique passwords, avoid opening attachments from unknown senders, and be wary of links from unfamiliar emails or websites.
Original Description:
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCybersecurity involves defending computers and networks from malicious attacks like cybercrime, cyber-attacks, and cyberterrorism. There are many types of malware threats such as viruses, trojans, ransomware, adware, and botnets. Other common cyber threats are SQL injection attacks, phishing scams, man-in-the-middle attacks, and denial-of-service attacks. To stay safe, it is important to keep software updated, use antivirus software, employ strong unique passwords, avoid opening attachments from unknown senders, and be wary of links from unfamiliar emails or websites.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
6 views19 pagesCYBERSECURITY
Uploaded by
MNEMOSYNNE BUENOCybersecurity involves defending computers and networks from malicious attacks like cybercrime, cyber-attacks, and cyberterrorism. There are many types of malware threats such as viruses, trojans, ransomware, adware, and botnets. Other common cyber threats are SQL injection attacks, phishing scams, man-in-the-middle attacks, and denial-of-service attacks. To stay safe, it is important to keep software updated, use antivirus software, employ strong unique passwords, avoid opening attachments from unknown senders, and be wary of links from unfamiliar emails or websites.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 19
CYBERSECURITY
INSTR. Kenneth Martinez
Cyber security is the practice of
defending computers, servers,
mobile devices, electronic systems,
networks, and data from malicious
attacks
Types of cyber threats
1. Cybercrime includes single actors or groups targeting
systems for financial gain or to cause disruption.
2. Cyber-attack often involves politically motivated
information gathering.
3. Cyberterrorism is intended to undermine electronic
systems to cause panic or fear.
There are a number of different types
of malware
Virus: A self-replicating program that attaches itself to
clean file and spreads throughout a computer system,
infecting files with malicious code.
Trojans: A type of malware that is disguised as
legitimate software. Cybercriminals trick users into
uploading Trojans onto their computer where they cause
damage or collect data.
Ransomware: Malware which locks down a user’s files
and data, with the threat of erasing it unless a ransom
is paid.
There are a number of different types
of malware
Adware: Advertising software which can be used to
spread malware.
Botnets: Networks of malware infected computers
which cybercriminals use to perform tasks online
without the user’s permission.
SQL injection
An SQL (structured language query)
injection is a type of cyber-attack used
to take control of and steal data from a
database. Cybercriminals exploit
vulnerabilities in data-driven
applications to insert malicious code
into a databased via a malicious SQL
statement. This gives them access to
the sensitive information contained in
the database.
SQL injection
Phishing
Phishing is when cybercriminals
target victims with emails that
appear to be from a legitimate
company asking for sensitive
information. Phishing attacks are
often used to dupe people into
handing over credit card data and
other personal information.
Phishing
Man-in-the-middle attack
A man-in-the-middle attack is a
type of cyber threat where a
cybercriminal intercepts
communication between two
individuals in order to steal data. For
example, on an unsecure WiFi
network, an attacker could intercept
data being passed from the victim’s
device and the network.
Man-in-the-middle attack
Denial-of-service attack
A denial-of-service attack is where
cybercriminals prevent a computer
system from fulfilling legitimate
requests by overwhelming the
networks and servers with traffic.
This renders the system unusable,
preventing an organization from
carrying out vital functions.
Denial-of-service attack
Cyber safety tips
protect yourself
against
cyberattacks
1. Update your software and operating
system: This means you benefit from
the latest security patches.
2. Use anti-virus software: Security
solutions like Kaspersky Total Security
will detect and removes threats. Keep
your software updated for the best level
of protection.
3. Use strong passwords: Ensure your
passwords are not easily guessable.
4. Do not open email attachments from
unknown senders: These could be
infected with malware.
5. Do not click on links in emails from
unknown senders or unfamiliar
websites:This is a common way that
malware is spread.
6. Avoid using unsecure WiFi networks in
public places: Unsecure networks leave
you vulnerable to man-in-the-middle
attacks.
ANY
QUESTIONS?
You might also like
- Cyber Security Seminar ReportDocument19 pagesCyber Security Seminar ReportManik Sharma76% (25)
- Cyber SecurityDocument14 pagesCyber SecurityPavan Shinde81% (16)
- Codes FinalDocument16 pagesCodes FinalJamil AbdullahNo ratings yet
- Cybersecurity For BeginnersDocument317 pagesCybersecurity For Beginnerskanantaram7197100% (4)
- Cyber SecurityDocument22 pagesCyber Securitytaguba luckyNo ratings yet
- Cyber Security MaterialDocument20 pagesCyber Security Materialagentvikram74No ratings yet
- Cyber SecurityDocument2 pagesCyber SecurityPushpendra gourNo ratings yet
- Cyber SecurityDocument17 pagesCyber SecurityMd AMsh MahmoodNo ratings yet
- Cyber SecurityDocument5 pagesCyber Securityjoel pabadoraNo ratings yet
- Modlue 4: Cybersecurity Awareness: ObjectivesDocument9 pagesModlue 4: Cybersecurity Awareness: ObjectivesJulie RamosNo ratings yet
- Latest Cyber Threats: SQL InjectionDocument3 pagesLatest Cyber Threats: SQL InjectionwindowsNo ratings yet
- Cse - 1Document25 pagesCse - 1santhosh n prabhuNo ratings yet
- Cyber Security IntroductionDocument20 pagesCyber Security IntroductionjilikajithendarNo ratings yet
- Cyber Security Introduction Latest Cyber Security Threats 5594e707Document10 pagesCyber Security Introduction Latest Cyber Security Threats 5594e707Lý Nghĩa PhanNo ratings yet
- COM 426 COMPUT4R SECURITY COURSE NOTEpdfDocument18 pagesCOM 426 COMPUT4R SECURITY COURSE NOTEpdfAhmed SaliuNo ratings yet
- Beginner Guide To Cyber SecurityDocument7 pagesBeginner Guide To Cyber SecurityGangadharNo ratings yet
- Module 1Document7 pagesModule 1AYUSH 822No ratings yet
- Cybersecurity Group 3 Bsa2bDocument45 pagesCybersecurity Group 3 Bsa2bCj AntonioNo ratings yet
- CSF Unit 1Document15 pagesCSF Unit 1Yaswanth Kumar Karaka (Yash)No ratings yet
- Cyber Security Unit-3Document22 pagesCyber Security Unit-3Vineet AnejaNo ratings yet
- Day 3: Introduction To Cyber SecurityDocument18 pagesDay 3: Introduction To Cyber SecurityAdedinewNo ratings yet
- Report File of Cyber SecurityDocument19 pagesReport File of Cyber SecurityNikita TomarNo ratings yet
- Reviewer Module 1 InfosecDocument23 pagesReviewer Module 1 InfosecMeilin Denise MEDRANANo ratings yet
- Unit Internet SecurityDocument29 pagesUnit Internet Securitykapinga0609No ratings yet
- What Is Cybersecurity and Why It Is ImportantDocument22 pagesWhat Is Cybersecurity and Why It Is ImportantOgieva ElvisNo ratings yet
- Q1 Common Types of Cybersecurity Attacks: 1. MalwareDocument32 pagesQ1 Common Types of Cybersecurity Attacks: 1. MalwareKhateeb AhmadNo ratings yet
- Cyber Security Notes 4-1Document81 pagesCyber Security Notes 4-1Sripriya BellaryNo ratings yet
- It Practical Cyber Security: Nishita Nagar X-ADocument11 pagesIt Practical Cyber Security: Nishita Nagar X-ANISHITA NAGARNo ratings yet
- Cyber SecurityDocument5 pagesCyber SecurityKrrishNo ratings yet
- Malware and Its TypesDocument5 pagesMalware and Its TypestinashejohnnesonganoNo ratings yet
- Cyber Security CEHDocument5 pagesCyber Security CEHSridhar PNo ratings yet
- CYBERSECURITYPPTDocument23 pagesCYBERSECURITYPPTAkula SreenivasuluNo ratings yet
- Cyber Security NotesDocument51 pagesCyber Security NotesBhure VedikaNo ratings yet
- Cyber Security Introduction - Cyber Security BasicsDocument30 pagesCyber Security Introduction - Cyber Security BasicsNilesh SharmaNo ratings yet
- Unit IDocument101 pagesUnit IYogita TiwariNo ratings yet
- Cyber Security Seminar ReportDocument19 pagesCyber Security Seminar ReportNoobToProytNo ratings yet
- BS (Hons.) Information Technology: University of OkaraDocument9 pagesBS (Hons.) Information Technology: University of OkaraAbdul Manan SajidNo ratings yet
- IT NS 1 - Chapter 1b Types of Attacks and DetectionDocument6 pagesIT NS 1 - Chapter 1b Types of Attacks and DetectionGALAPON FRANCISNo ratings yet
- Exam Paper Solution: Section - IDocument18 pagesExam Paper Solution: Section - IthefactzsupplierNo ratings yet
- DocumentDocument16 pagesDocumentVaibhav BhardwajNo ratings yet
- Ethical Hacking Scrip (M2)Document2 pagesEthical Hacking Scrip (M2)uhafduhkjhasNo ratings yet
- Cyber Security !Document3 pagesCyber Security !kavya keerthiNo ratings yet
- Data 1Document6 pagesData 1Gaurav RaneNo ratings yet
- Introduction To Cyber Security Handbook PDFDocument104 pagesIntroduction To Cyber Security Handbook PDFVjay MadhamNo ratings yet
- Let The Picture SpeakDocument6 pagesLet The Picture SpeakASHA KAINDALNo ratings yet
- Is Unit IDocument37 pagesIs Unit IShailendra PardeshiNo ratings yet
- Topic 5 Malware and Cyber AttackDocument6 pagesTopic 5 Malware and Cyber AttackJohn Mark DaludadoNo ratings yet
- Ism 8isDocument33 pagesIsm 8isMidhun KvNo ratings yet
- For Final YearDocument13 pagesFor Final YearnishpriyasudhagarNo ratings yet
- Cybersecurity: Categories of CybercrimeDocument6 pagesCybersecurity: Categories of Cybercrimeamna100% (1)
- d2 PrintedDocument27 pagesd2 PrintededrisNo ratings yet
- Cys 102Document33 pagesCys 102othman09714164No ratings yet
- INDIVIDUAL BY StanleyDocument4 pagesINDIVIDUAL BY Stanleyphenomenal 4spNo ratings yet
- Cyber Security Seminar Report PDF FreeDocument19 pagesCyber Security Seminar Report PDF Freediyis61035100% (1)
- Cyber Security Seminar ReportDocument19 pagesCyber Security Seminar ReportManik SharmaNo ratings yet
- Cybersecurity PrologueDocument44 pagesCybersecurity PrologueRaj Prabhu RajendranNo ratings yet
- Cyber SecurityDocument3 pagesCyber Securitykschauhan8007No ratings yet
- Type of Cyber AttacksDocument2 pagesType of Cyber Attacksvorleak chenNo ratings yet
- Othonial College Department of Management Introduction To Emerging Technology Report On Cyber SecurityDocument18 pagesOthonial College Department of Management Introduction To Emerging Technology Report On Cyber SecurityEdlamu AlemieNo ratings yet
- Introduction ImDocument13 pagesIntroduction ImRam NeymarjrNo ratings yet
- Unit 3 Cyber SecurityDocument39 pagesUnit 3 Cyber Securityakshatvishwakarma06No ratings yet
- 9.1.2.5 Lab - Hashing Things OutDocument3 pages9.1.2.5 Lab - Hashing Things Outc583706No ratings yet
- Cyber Handbook-Enterprise v1.6Document33 pagesCyber Handbook-Enterprise v1.6PrashanthPrashanthNo ratings yet
- IT06 Certificatein Cyber SecurityDocument39 pagesIT06 Certificatein Cyber SecurityAbdul MannanNo ratings yet
- AV Botnet Detection PDFDocument23 pagesAV Botnet Detection PDFIvan PopovNo ratings yet
- Ethical Hacking: An Impact On Society: April 2014Document11 pagesEthical Hacking: An Impact On Society: April 2014Sarah TambunanNo ratings yet
- Configuring Ohs and Essbase With SSL For ObieeDocument15 pagesConfiguring Ohs and Essbase With SSL For ObieeKrishna Kant NemaNo ratings yet
- HUAWEI USG6600 Series Next-Generation Firewall DatasheetDocument13 pagesHUAWEI USG6600 Series Next-Generation Firewall DatasheetTony KhouryNo ratings yet
- Fingerprints For SFTP Destinations in SAP BusinessObjects BI Platform 4.1Document17 pagesFingerprints For SFTP Destinations in SAP BusinessObjects BI Platform 4.1KalyanNo ratings yet
- CCNA Security Lab Manual by Yasir ImranDocument178 pagesCCNA Security Lab Manual by Yasir ImranIkki de Fênix100% (4)
- OMV Perimeter FW Replacement Project - Implementation SOWDocument7 pagesOMV Perimeter FW Replacement Project - Implementation SOWTenishan FernandoNo ratings yet
- Part I: The Essentials of Network Perimeter Security Chapter 1. Perimeter Security FundamentalsDocument4 pagesPart I: The Essentials of Network Perimeter Security Chapter 1. Perimeter Security Fundamentalsnhanlt187No ratings yet
- VPN Access Using Tunnel Mode User Manual PDFDocument6 pagesVPN Access Using Tunnel Mode User Manual PDFSreejith G SNo ratings yet
- Cryptography - Cryptography and Data SecurityDocument224 pagesCryptography - Cryptography and Data Securityg4t0l0c0100% (1)
- ID2S Password-Authenticated Key Exchange ProtocolsDocument5 pagesID2S Password-Authenticated Key Exchange ProtocolsThe Futura LabsNo ratings yet
- Facts RobotDocument2 pagesFacts RobotJain PradeepNo ratings yet
- How Can Human Behavior Be Considered One of The Biggest Potential Threats To Operating System Integrity - Google SearchDocument3 pagesHow Can Human Behavior Be Considered One of The Biggest Potential Threats To Operating System Integrity - Google SearchJust SomeoneNo ratings yet
- Case Study #2: Data Security & Data Loss Prevention: UMUC CSIA 300 7380 Cybersecurity For Leaders and ManagersDocument6 pagesCase Study #2: Data Security & Data Loss Prevention: UMUC CSIA 300 7380 Cybersecurity For Leaders and Managersjasmine prudenceNo ratings yet
- Mat263 Case StudyDocument13 pagesMat263 Case Studyhafi zainNo ratings yet
- Cisco CCNA Security-SummaryDocument56 pagesCisco CCNA Security-Summaryhttp://utsit.blogspot.com.au/100% (2)
- Pen TestDocument5 pagesPen TestHiepHenryNo ratings yet
- Checkpoint Certification Exam Questions 156-80 Enero 2020Document200 pagesCheckpoint Certification Exam Questions 156-80 Enero 2020rulohb83No ratings yet
- Build and Operate A Trusted DoDINDocument1 pageBuild and Operate A Trusted DoDINpradhyaNo ratings yet
- Computer Security: Principles and Practice: Fourth Edition By: William Stallings and Lawrie BrownDocument30 pagesComputer Security: Principles and Practice: Fourth Edition By: William Stallings and Lawrie BrownJeremy David AlexanderNo ratings yet
- CyberSense For Dell PowerProtect Cyber Recovery 1656644381Document12 pagesCyberSense For Dell PowerProtect Cyber Recovery 1656644381Marcelo MafraNo ratings yet
- ContentType InjectionDocument12 pagesContentType Injectionpavan pkNo ratings yet
- Security of Hash Functions and MacsDocument9 pagesSecurity of Hash Functions and MacsKirti singh sikarwarNo ratings yet
- Assignment 1 IISDocument4 pagesAssignment 1 IISZulqarnain KambohNo ratings yet
- Computer Security Risks: 2.1. Computer and Cyber CrimesDocument12 pagesComputer Security Risks: 2.1. Computer and Cyber CrimesZeke MJNo ratings yet