Professional Documents
Culture Documents
Eal Ict FWC 5th 2017
Uploaded by
Sandakini ManodyaOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Eal Ict FWC 5th 2017
Uploaded by
Sandakini ManodyaCopyright:
Available Formats
G.C.E.
(A/L) Examination – March 2017
G Conducted by Field Work Center, Thondaimanaru.
In Collaboration with the Zonal Education Office, Jaffna
Information & Communication Technology (ICT)
Grade 13 (A/L) 2017 Part - I Time : 2 hours
Answer all the questions
1. Which of the following statement is correct?
(1) Blaise Pascal designed analytical engine
(2) Adding machine was designed by Von Neumann
(3) Punched card was designed by Blaise Pascal
(4) Difference engine was designed by Blaise Pascal
(5) Alan Turing is considered as the father of computer science
2. Two’s complements of (+910) and (-610) are respectively.
(1) 000010002 > 000100112 (2) 000010012 > 111110102 (3) 111001112 > 000100112
(4) 111101112 > 100100112 (5) 111101112 > 000100112
3. Consider the following statements.
A – allowing the execution of applications even not in main memory fully
B – larger than physical memory
C – its capacity is limited
Which of the above statement(s) is/are correct about virtual memory?
(1) A only (2) B only (3) C only (4) A,C only (5) A,B,C all
4. The simplified result of the Boolean function f ( x, y, z ) 𝑥𝑦̅𝑧 + 𝑥̅ 𝑦̅𝑧 + 𝑥𝑦𝑧 is.
(1) 𝑥𝑦 (2) 𝑦𝑧 (3) 𝑥̅ 𝑦 (4) 𝑦̅𝑧 (5) 𝑧(𝑥 + 𝑦̅)
5. Consider the following statements.
A – allocating and resolving of memory required by processes
B – providing security for computer
C – handling files and folders
Which of the above is/are function(s) of file management in an operating system?
(1) A only (2) B only (3) A,B only (4) A,C only (5) A,B,C all
6. In an automated teller machine (ATM), customers are expected to enter four digits number compulsorily.
Which of the following data validation method(s) is/are most appropriate?
A – format check B – range check C – type check
D – length check E – numeric check
(1) A,B only (2) B,C only (3) C,D,E only (4) A,C only (5) B,C,E only
7. Which of the following is a component of a CPU?
(1) L3 cache memory (2) CU (3) power supply
(4) RAM (5) ROM
1 G.C.E. (A/L) ICT 2017 – Gr.13 March FWC ( Part – I)
8. Which of the following statement is incorrect about UDP (User Datagram Protocol)?
(1) connection-oriented
(2) unreliable service
(3) unordered delivery of data packets
(4) it works on transport layer
(5) connectionless
9. Consider the following logic circuit.
What is the result of R?
A (1) 𝐴. 𝐵
R (2) 𝐴 + 𝐵
(3) ̅̅̅̅̅
𝐴. 𝐵
B (4) 𝐴. 𝐵̅
(5) 𝐴̅. 𝐵̅
10. In a computer architecture, “……………………………. is an event that alters the regular execution flow of
instructions”. The most appropriate word to fill the blank in is.
(1) program counter (2) ALU (3) RAM
(4) interrupt (5) cache memory
11. In an operating system, “……………………..maps virtual memory addresses into physical memory
addresses”.
The most appropriate word to fill the blank in is.
(1) page table (2) virtual memory (3) physical memory
(4) swapping (5) process control block
12. Which of the following uses optical technology to read the contents?
(1) Floppy disk (2) hard disk (3) magnetic tape
(4) DVD (5) Flash memory
13. “……………………….decides which of the ready process is to be executed (allocated a CPU)”.
(1) short-term scheduler (2) long-term scheduler
(3) mid-term scheduler (4) process
(5) swapping
14. In an operating system, process control block (PCB) consists of.
A - process state
B - program counter
C - I/O status information
(1) A only (2) B only (3) A,B only (4) A,C only (5) A,B,C all
15. 768 + AC16 =
(1) A916 (2) B916 (3) E916 (4) C916 (5) 9E16
16. The function of a DNS server.
(1) mapping domain name into IP address
(2) resolving IP addresses dynamically
(3) securing computer from malware
(4) sharing Internet connection among computers
(5) providing various applications to other devices
2 G.C.E. (A/L) ICT 2017 – Gr.13 March FWC ( Part – I)
17. Which of the following python program is syntactically correct?
(1) for X in range(1,5) (2) for X in range(1,5): (3) for X in range(1,5)
print X print X print X
(4) for X in range(1,5): (5) for X in range(1,5):
print X: print X
18. Consider the following about dynamic random access memory (DRAM).
A – DRAM requires refreshing
B – This is used as cache memory
C – Registers are made of DRAM
Which of the above is/are correct?
(1) A only (2) B only (3) A,B only (4) A,C only (5) B,C only
19. Consider the following statements.
A – cache memory saves the frequently used instructions
B – control unit controls information flow and instruct computer how to execute instructions
C – registers keep instructions used by central processing unit
Which of the above is/are correct?
(1) A only (2) B only (3) C only (4) A, B only (5) A,B,C all
20. “Random access memory (RAM) modules are often compared by their capacity, measures in ………… and
by their speed, measured in …………………”.
Most suitable words to fill the blanks of the above statements are respectively.
(1) Kilobytes, Gigabytes (2) Gigabytes, Megabits per second
(3) Gigabytes, Megahertz (4) Megahertz, Kilohertz
(5) Gigabits, Megabits per second
21. The process in which the newly developed system is ensured that the user requirements are satisfied, is
called.
(1) system design (2) system maintenance (3) system analysis
(4) system testing (5) coding
22. Consider the following systems:
A – human blood circulatory system B – human digestive system C – human nervous system
Which of the above could be considered as closed system(s)?
(1) A only (2) B only (3) C only (4) A,B only (5) A,C only
23. Consider the following statements about information system.
A – an information system could be used to achieve goals designed of an organization
B – an information system could be a computerized or manual
C – a banking system may be an example for an information system
Which of the above is/are correct?
(1) A only (2) B only (3) C only (4) A,B only (5) A,B,C all
24. Consider the following memories.
A - Read Only Memory B - Register C - Cache memory
D - Flash memory E - Random Access Memory
Which of the above may be considered as non-volatile memories?
(1) A,B only (2) A,C only (3) A,D only (4) C,E only (5) D,E only
3 G.C.E. (A/L) ICT 2017 – Gr.13 March FWC ( Part – I)
25. Which of the following HTML tag is used to create ordered list?
(1) <CAPTION> (2) <UL> (3) <TABLE> (4) <H1> (5) <OL>
26. In data communication, “…………….. is used to transmit the received signal into higher power”.
(1) router (2) modem (3) multiplexer (4) hub (5) repeater
27. Consider the following statements.
A – L1 cache memory is more speed than L2 cache memory
B – L1 cache memory is less speed than L2 cache memory
C – L1 cache memory is more capacity than L2 cache memory
Which of the above is/are correct?
(1) A only (2) B only (3) C only (4) A,B only (5) A,C only
28. Which of the following is a class C IP address?
(1) 191.1.1.10 (2) 224.5.6.4 (3) 121.8.7.5 (4) 223.4.3.10 (5) 192.5.1.9
29. The IP address of a computer network is 192.168.2.10. If its subnet mask is 255.255.255.192, how many
maximum of hosts can be connected in a network?
(1) 64 (2) 62 (3) 32 (4) 128 (5) 256
30. “……………………. is a computer system that is situated in an environment, and that is capable of
autonomous action in this environment on behalf of its user in order to meet its design objectives.”.
(1) network (2) application software (3) system software
(4) software agent (5) open source software
31. The value of python statement 5 // 2 is.
(1) 2.5 (2) 3 (3) 2 (4) 32 (5) 25
32. Consider the following statements about e-marketing.
A - more speed B - ease and efficiency C - broader selection of customers
Which of the above is/are the benefit(s) of e-marketing?
(1) A only (2) B only (3) A,B only (4) C only (5) A,B,C all
33. Consider the following statements about foreign key in a relational database.
A - In a relationship between two tables, primary key and foreign key may have different field names.
B - In a relationship between two tables, primary key values in a table can have same values with foreign
key in another table.
C - Foreign key is used to create a relationship between two tables
Which of the above is/are correct?
(1) A only (2) B only (3) A,B only (4) A,C only (5) A,B,C all
34. Consider the following ER diagram between Employee and Project.
4 G.C.E. (A/L) ICT 2017 – Gr.13 March FWC ( Part – I)
When this ER diagram is mapped into tables, which of the following table(s) are available?
A - Employee (EmpNo, First, Mid, Last)
B - Project (ProjNo, ProjName)
C - Works_On (EmpNo, ProjNo,Hours)
D - Works_On (Hours)
(1) A,B only (2) A,C only (3) B,C only (4) A,D only (5) A,B,C only
35. What is the output of the following python program?
for a in range(0,5):
a=a+1
print (a, end= ' ')
(1) 1 2 3 4 5 (2) 0 1 2 3 4 (3) 0 1 2 3 4 5 (4) 1 3 5 (5) 0 2 4
36. Which of the following python program best defines a user-defined function?
(1) def function(): (2) def function (3) def function()
print (‘Good’) print (‘Good’) print (‘Good’)
(4) def function(): (5) def function
print (‘Good’) print (‘Good’):
37. Consider the following HTML code segment.
<ol>
<li> Coffee </li>
<li> Tea </li>
<li> <b> Milk </b> </li>
</ol>
Which of the following result is rendered on web browser by this code?
(1) (2) (3) (4) (5)
Coffee Coffee Coffee 1. Coffee i. Coffee
Tea Tea Tea 2. Tea ii. Tea
Milk Milk Milk 3. Milk iii. Milk
38. Consider the following statements.
A – Guido Van Rossum created python interpreter
B – python programs are based on case sensitivity
C – it is a third generation computer programming language
Which of the above is/are correct about python programming language?
(1) A,B only (2) A,C only (3) B,C only (4) A,D only (5) A,B,C only
39. Consider the following statements about HTML tags.
A - <div> defines division or section
B - <p> defines paragraph
C - <br> inserts single line break
Which of the above is/are correct?
(1) A only (2) B only (3) C only (4) A, B only (5) A,B,C all
5 G.C.E. (A/L) ICT 2017 – Gr.13 March FWC ( Part – I)
40. “Operating system retrieves data from secondary storage in same-size blocks”. This is called………………..
Which of the following is correct to fill the blank in?
(1) processing (2) swapping (3) context switching (4) scheduling (5) paging
41. Which of the following CSS definition is correct?
(1) font: "Times New Roman"; (2) family: "Times New Roman";
(3) font-family: "Times New Roman"; (4) font-type: "Times New Roman";
(5) font-category: "Times New Roman";
42. Which of the following will be used to define an external CSS?
(1) < link rel="stylesheet" type="text/css" href="mystyle.css" >
(2) < link src="stylesheet" type="text/css" href="mystyle.css" >
(3) < link link="stylesheet" type="text/css" href="mystyle.css" >
(4) < link a="stylesheet" type="text/css" href="mystyle.css" >
(5) < link img="stylesheet" type="text/css" href="mystyle.css" >
43. “……………………. was created to overcome the problem of collisions that occur when packets are
transmitted simultaneously from different computers”.
(1) IP (2) CSMA/CD (3) TCP (4) FTP (5) UDP
44. Which of the following best describes the non-functional requirement of a cellular phone?
(1) sending a short message
(2) receiving a telephone call
(3) selecting a telephone number from the contact list
(4) making a telephone call
(5) battery has one year warranty period
45. Consider the following flowchart.
Start
What are first three numbers displayed by this flowchart?
N=1 (1) 1, 4, 9
(2) 1, 3, 6
(3) 1, 3, 5
S=1
(4) 2, 4, 6
(5) 2, 3, 5
Display S
N=N+1
S=S+N
No
S > 50 ?
Yes
Stop
6 G.C.E. (A/L) ICT 2017 – Gr.13 March FWC ( Part – I)
46. Consider the following statements about expert systems.
A - it reveals the decision making ability of human experts
B - it provides the solutions for complex problems by reasoning logically
C - it replaces human experts
Which of the above is/are correct?
(1) A only (2) B only (3) A,B only (4) A,C only (5) B,C only
47. In OSI network reference model, FTP is described in.
(1) physical layer (2) application layer (3) network layer
(4) datalink alyer (5) transport layer
48. Which of the following is/are private IP address(es)?
A - 10.1.1.1 B - 172.32.5.2 C - 172.16.4.4
D - 192.168.5.5 E - 224.6.6.6
(1) A only (2) A,B only (3) A,C,D only (4) A,B,E only (5) A,B,C only
49. Which of the following statement about a relation in relational model is correct?
(1) Each relation in a database will consists a primary key
(2) Each relation in a database will consists a foreign key
(3) Order of rows are compulsory
(4) Order of columns are compulsory
(5) Each value in an intersection of row and column should have a single value
50. Consider the following tasks.
A – creating a table
B – removing a row from a table
C – changing data in a column from a table
D – removing database
Which of the following SQL keywords are used to do the tasks given above respectively?
(1) alter, create, delete, update
(2) alter, create, insert, delete
(3) update, create, delete, drop
(4) create, delete, update, drop
(5) update, create, insert, drop
****
7 G.C.E. (A/L) ICT 2017 – Gr.13 March FWC ( Part – I)
G.C.E. (A/L) Examination – March 2017
Conducted by Field Work Center, Thondaimanaru.
In Collaboration with the Zonal Education Office, Jaffna
Information & Communication Technology (ICT)
Grade 13 (A/L) 2017 Part – II A Time : 3 hours
Structured questions Answer all the questions
01.
(a) Write down three media used in secondary storage devices with the help of appropriate example.
(b) Calculate the value of (+810) + (- 610) using 2’s complement 8-bits method.
(c) A computer system contains a byte addressable memory and it uses 32-bits addresses. What is the maximum
usable size of this memory in Giga Bytes? Show your work clearly.
1 G.C.E. (A/L) ICT 2017 – Grade 13 – March FWC – Part - II
02.
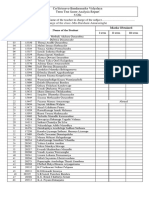
(a) The following table consists of layers in OSI network reference model, their protocols, devices and
functions. Indicate ( ) in suitable places in the table.
Physical Application Transport Network
layer layer layer layer
(1) e-mail service
(2) Routing
(3) TCP
(4) IP
(5) UDP
(6) Communication
media
(b) Differentiate the communication protocols such as TCP and UDP based on connection-oriented.
(c) Consider the following definition list rendered by a web browser.
Singapore
The land of dreams
Thailand
The land of smiles
Complete the following HTML code segment to render the list given above.
<dl>
<……….> Singapore <……….>
<……….> The land of dreams <………>
<…………> Thailand <……….>
<………> The land of smiles <……….>
</dl>
2 G.C.E. (A/L) ICT 2017 – Grade 13 – March FWC – Part - II
03.
(a) Write down the following CSS definitions whether it is syntactically correct or incorrect. If the rule is
incorrect, write down correct rules.
(i) h1 { font-type:arial; }
(ii) p { text-color : red ; }
(b) Consider the following python program.
s=0
n=1
while n<=5:
s=s+n
print (s,end=' ')
n=n+1
What is the output of this program?
(c) How do you modify this program to obtain sum of first 10 odd numbers?
3 G.C.E. (A/L) ICT 2017 – Grade 13 – March FWC – Part - II
04.
Consider the following three tables used in a school database.
Student
stdid name address Subject
S01 Perera Galle subid name
S02 Vimal Galle SU01 Mathematics
S03 Ameen Colombo SU02 Physics
S04 Jamuna Jaffna SU03 ICT
Result
stdid subid marks
S01 SU01 79
S01 SU03 80
S02 SU01 90
S03 SU02 66
(a) Write down appropriate SQL statement to obtain details such as stdid, and address.
(b) Write down appropriate SQL statement to obtain details such Student Name, Subject Name, and Marks.
(c) Write down appropriate SQL statement to insert first record in Student table.
(d) Write down appropriate SQL statement to create Student table (primary key is stdid).
****
4 G.C.E. (A/L) ICT 2017 – Grade 13 – March FWC – Part - II
G.C.E. (A/L) Examination – March 2017
Conducted by Field Work Center, Thondaimanaru.
In Collaboration with the Zonal Education Office, Jaffna
Information & Communication Technology (ICT)
Grade 13 (A/L) 2017 Part – II B
Essay questions Write down answer any four questions only
01.
(a) State the following Boolean Laws.
(i) De Morgan’s Law
(ii) Associative Law
(b) A coin is tossed 3 times. A win is said to occur if the result obtained is Heads for at least 2 tosses.
Taking A, B, C as inputs and W as output, given that A, B, C are 1 if the result is
Heads or 0 if the result is Tails; and W is 1 if a win occurs otherwise it is 0.
(i) Construct a truth table.
(ii) Write a Boolean expression for W in the form of SOP (sum of product).
(iii) Simplify the expression obtained in (ii) above using Karnaugh map.
(iv) Draw a combined gate for the simplified expression obtained in (iii).
02.
(a) Write down any three functions of transport layer of OSI network reference model.
(b) IP address of a network is 192.168.1.2 and its subnet mask is 255.255.255.224. How many hosts may be
connected in this network?
(c) Write down short notes on the followings.
(i) DHCP Server
(ii) Proxy server
(d) Define the term “agent” in the context of agent technology and write down two situations with the help of
example where the agent technology is used.
03.
(a) Write down any two programming approaches.
(b) Draw a flowchart to obtain sum of any ten numbers entered by user.
(c) Write down Python program for the flowchart stated above in (b).
04.
Draw an ER diagram to represent the scenario given below. The attributes and the primary keys of entities
should be clearly indicated. State clearly if any assumptions that you have.
“Jazz Beatle” has decided to store information about musicians who perform on its albums in a database.
Each musician has an MID, a name, an address, and a phone number. Each instrument used in songs recorded
has a unique identification number, a name (e.g., guitar, synthesizer, flute, etc.) and a musical key (e.g., C, B-
flat, etc.).Each album recorded has a unique identification number, a title, a copyright date, a format (e.g.,
DVD), and an album identification number. Each song recorded has a title and an author. Each musician may
play several instruments, and a given instrument may be played by several musicians. Each album has a number
of songs on it, but no song may appear on more than one album. Each song is performed by one or more
5 G.C.E. (A/L) ICT 2017 – Grade 13 – March FWC – Part - II
musicians, and a musician may perform a number of songs. Each album has exactly one musician who acts as its
producer. A musician may produce several albums.
05.
(a) What would be the responses by a browser for a <p> tag and for <img> tag in an HTML?
(b) The following web page is a part of the web site of the “Bird Park - Hambantota, Sri Lanka”.
Write an HTML code to produce the above web page. Assume that the name of the image file is “bird.jpg”.
The link, “Bird Park”, should link to the site “http://www.birdsibr.com”.
06.
“World’s Trend” is a mail order supplier of high-quality, fashionable clothing. Customers place orders by
telephone, by mailing an order form included with each catalog, or via the Web site.
When customer orders come in, the item master and the customer master files are both updated. If an item is out
of stock, the inventory control department is notified. If the order is from a new customer, a new record is
created in the customer master file. Picking slips are produced for the customer order and sent to the warehouse.
A shipping statement is prepared. The process of shipping a customer order involves getting the goods from the
warehouse and matching up the customer shipping statement, getting the correct customer address, and shipping
it all to the customer. The customer statement is generated and a billing statement is sent to a customer. An
accounts receivable report is sent to the accounting department.
Draw a context diagram to show the overview of the order processing system described above. Clearly indicate
external entities and data flows in the diagram.
*****
6 G.C.E. (A/L) ICT 2017 – Grade 13 – March FWC – Part - II
You might also like
- Ict JiyanaDocument6 pagesIct Jiyanashihamh haniffaNo ratings yet
- 2016 July em IctDocument12 pages2016 July em IctMangala SemageNo ratings yet
- ICT 2020 Mar - Part IDocument7 pagesICT 2020 Mar - Part ImaithilyNo ratings yet
- ICT PaperDocument14 pagesICT Papershihamh haniffaNo ratings yet
- ICT Paper FinalDocument13 pagesICT Paper Finalshihamh haniffaNo ratings yet
- InstructionsDocument25 pagesInstructionsKhalifa NiyasNo ratings yet
- OStestDocument6 pagesOStestUmayangaNo ratings yet
- Grade 12 ICT 3rd Term 2021 Paper 1Document9 pagesGrade 12 ICT 3rd Term 2021 Paper 1Thulmin Damsilu JayawardenaNo ratings yet
- ICT PaperDocument14 pagesICT Papershihamh haniffaNo ratings yet
- Information & Communication Technology: Nalanda College - Colombo G.C.E. (Advanced Level)Document6 pagesInformation & Communication Technology: Nalanda College - Colombo G.C.E. (Advanced Level)Keshan BulathsingheNo ratings yet
- General Certificate of Education (Advanced Level) Support Seminar-2013Document24 pagesGeneral Certificate of Education (Advanced Level) Support Seminar-2013hemacrcNo ratings yet
- 2013 AL ICT Model Paper English at Apepanthiya - LKDocument24 pages2013 AL ICT Model Paper English at Apepanthiya - LKprasannaNo ratings yet
- AL ICT 2017 Paper IDocument8 pagesAL ICT 2017 Paper IAvishka ChanukaNo ratings yet
- Part - IDocument11 pagesPart - IAnil UpendraNo ratings yet
- Devi Balika Revision PaperDocument16 pagesDevi Balika Revision PaperDahanyakage WickramathungaNo ratings yet
- HSST Computer ScienceDocument14 pagesHSST Computer SciencetrcvmftNo ratings yet
- Jtyjdtyjr 5Document10 pagesJtyjdtyjr 5Sandunika DevasingheNo ratings yet
- 2012 AL ICT MCQ English at Apepanthiya - LKDocument8 pages2012 AL ICT MCQ English at Apepanthiya - LKSherlin PerithNo ratings yet
- 19 Ict EDocument22 pages19 Ict EArshadNo ratings yet
- Chapter 1 Introduction To Computer Architecture: Multiple-ChoiceDocument17 pagesChapter 1 Introduction To Computer Architecture: Multiple-ChoiceAri BaderNo ratings yet
- Model Papers-Dep of Edu-ICTDocument18 pagesModel Papers-Dep of Edu-ICTchandimaNo ratings yet
- GlobalDocument9 pagesGlobaldildilliNo ratings yet
- 17 Mar 12 ICTEDocument12 pages17 Mar 12 ICTEkanagaratnam ThurshikaNo ratings yet
- Operating System Questions MCQDocument13 pagesOperating System Questions MCQSwetha D75% (4)
- "Sss53S: Eazsiabesÿs I InstructionsDocument8 pages"Sss53S: Eazsiabesÿs I InstructionsAvishka ChanukaNo ratings yet
- Instructions:: U U4 ' I LIUDocument8 pagesInstructions:: U U4 ' I LIUAvishka ChanukaNo ratings yet
- Thapar Institute of Engineering & Technology, Patiala: End Semester Examination (May 2019)Document4 pagesThapar Institute of Engineering & Technology, Patiala: End Semester Examination (May 2019)Forza HorizonNo ratings yet
- Xi-Cs-Reduced - Syllabus Q & A - 21Document20 pagesXi-Cs-Reduced - Syllabus Q & A - 21PriyaNo ratings yet
- CU-2022 B.Sc. (General) Computer Science Semester-4 Paper-CC4-GE4 QPDocument2 pagesCU-2022 B.Sc. (General) Computer Science Semester-4 Paper-CC4-GE4 QPgozombie43No ratings yet
- Mces MCQDocument50 pagesMces MCQshrimanNo ratings yet
- A7 - 90Document3 pagesA7 - 90Sameer MaheNo ratings yet
- Embedded Systems ObjectiveDocument8 pagesEmbedded Systems ObjectiveSuribabu Medisetti100% (1)
- Embeded MCQDocument117 pagesEmbeded MCQSaddam AbdullahNo ratings yet
- Comput Awareness QsDocument22 pagesComput Awareness QsbghcvhjNo ratings yet
- Eol ICT NWDocument15 pagesEol ICT NWRislan MohammedNo ratings yet
- Comp Question 1Document15 pagesComp Question 1SamsonNo ratings yet
- ITPECIP2021 OctoberDocument29 pagesITPECIP2021 OctobergokuNo ratings yet
- Computer SbiDocument136 pagesComputer SbiBasavaraj GadadavarNo ratings yet
- 40 Questions Asked in RRB Po Exam Computer PDFDocument2 pages40 Questions Asked in RRB Po Exam Computer PDFHafiz Muhammad AkhterNo ratings yet
- Advanced Embedded Systems (10EC118)Document2 pagesAdvanced Embedded Systems (10EC118)Shashank HollaNo ratings yet
- Ca 3Document14 pagesCa 3abhiNo ratings yet
- SBI PO: Computer QuizDocument7 pagesSBI PO: Computer QuizSparse ShashankNo ratings yet
- MCQs On Computer Part IIDocument96 pagesMCQs On Computer Part IIYasir MehmoodNo ratings yet
- ÔN TẬP CUỐI MÔN OSDocument16 pagesÔN TẬP CUỐI MÔN OSNguyễn Bảo HưngNo ratings yet
- Mid Sem Ques DCA ITDocument2 pagesMid Sem Ques DCA ITrjoshittaNo ratings yet
- Xi CS New Python Ut 1Document3 pagesXi CS New Python Ut 1Krish AhirwarNo ratings yet
- Operating System FundamentalsDocument6 pagesOperating System FundamentalsGuruKPO100% (2)
- 11 Computer Science: Volume-I (Unit I & Ii)Document8 pages11 Computer Science: Volume-I (Unit I & Ii)Muthu SelvamNo ratings yet
- Computer Knowledge - Competative Exams GuideDocument68 pagesComputer Knowledge - Competative Exams GuideSaubhik DeyNo ratings yet
- 11cs Book Back QuestionsDocument30 pages11cs Book Back QuestionsvujayjananiNo ratings yet
- Instructions:: Appropriate and Mark Your Response On The Answer Sheet With A Cross (Document8 pagesInstructions:: Appropriate and Mark Your Response On The Answer Sheet With A Cross (RafeekIrshadNo ratings yet
- Computer Organization and Assembly Language: Laboratory ManualDocument25 pagesComputer Organization and Assembly Language: Laboratory ManualMohd ShahNo ratings yet
- Os MCQDocument7 pagesOs MCQmakreal100% (1)
- Git Prototype Paper 1Document6 pagesGit Prototype Paper 1Karthicason VigneshwaranNo ratings yet
- G.C.E (O.L) Practice Test - 2020: North Western ProvinceDocument14 pagesG.C.E (O.L) Practice Test - 2020: North Western Provinceinvictus azmunNo ratings yet
- 10TH Nios Data EntryDocument1 page10TH Nios Data EntryArshadkhan A JahagirdarNo ratings yet
- Model Question Paper IT & SystemsDocument24 pagesModel Question Paper IT & SystemsSandipan DasNo ratings yet
- PLC: Programmable Logic Controller – Arktika.: EXPERIMENTAL PRODUCT BASED ON CPLD.From EverandPLC: Programmable Logic Controller – Arktika.: EXPERIMENTAL PRODUCT BASED ON CPLD.No ratings yet
- Computer Knowledge Bit Bank for All Competitive ExamsFrom EverandComputer Knowledge Bit Bank for All Competitive ExamsRating: 4 out of 5 stars4/5 (4)
- Mark SheetDocument3 pagesMark SheetSandakini ManodyaNo ratings yet
- Mark SheetDocument3 pagesMark SheetSandakini ManodyaNo ratings yet
- BandwidthDocument18 pagesBandwidthSandakini ManodyaNo ratings yet
- Transmission MediaDocument32 pagesTransmission MediaSandakini ManodyaNo ratings yet
- Frozen ch02Document42 pagesFrozen ch02Shashank AgarwalNo ratings yet
- Point To Point ProtocolsDocument17 pagesPoint To Point ProtocolsSandakini ManodyaNo ratings yet
- Life Is GoodDocument2 pagesLife Is GoodSandakini ManodyaNo ratings yet
- Ifrka: ?fi Information Communication TechnologyDocument11 pagesIfrka: ?fi Information Communication TechnologyMalan MankhNo ratings yet
- Grade 8 IctDocument36 pagesGrade 8 IctSandakini ManodyaNo ratings yet
- Mark SheetDocument3 pagesMark SheetSandakini ManodyaNo ratings yet
- M Uq JDR Mícikh - 2019: 6 Fya%KshDocument7 pagesM Uq JDR Mícikh - 2019: 6 Fya%KshSandakini ManodyaNo ratings yet
- Manual Ventsim Ingles Ver. 3.2Document270 pagesManual Ventsim Ingles Ver. 3.2Leslie FanyNo ratings yet
- 2022 Newzoo Free Global Games Market ReportDocument61 pages2022 Newzoo Free Global Games Market ReportKRISTIAN HENRY PALOMANo ratings yet
- Fieldserver Quickserver Start-Up Guide Fs-Qs-2X10: Applicability & EffectivityDocument34 pagesFieldserver Quickserver Start-Up Guide Fs-Qs-2X10: Applicability & EffectivityNicol PérezNo ratings yet
- IRIS BPNN - Ipynb - ColaboratoryDocument4 pagesIRIS BPNN - Ipynb - Colaboratoryrwn data100% (1)
- Chinook 11 Tidyverse OlapDocument6 pagesChinook 11 Tidyverse OlapI'm a StarNo ratings yet
- MicroSCADA X SYS600C 5.10 Sales Presentation - 4CAE001299Document20 pagesMicroSCADA X SYS600C 5.10 Sales Presentation - 4CAE001299Jahangir KhanNo ratings yet
- Pans Ops OasDocument25 pagesPans Ops OasYudha Wastu PramukaNo ratings yet
- SLS-T Allgemein VMT - JMDocument65 pagesSLS-T Allgemein VMT - JMjmtexla680% (1)
- OCPP Course - Part 2Document12 pagesOCPP Course - Part 2jeremysalmon.openlabNo ratings yet
- Data Extraction From Hand Filled Forms Using OcrDocument18 pagesData Extraction From Hand Filled Forms Using OcrShinchanNo ratings yet
- The GET Method Is Not Supported For Route Login. Supported Methods - POSTDocument1 pageThe GET Method Is Not Supported For Route Login. Supported Methods - POSTqaz qazyNo ratings yet
- IT Infrastructure Management eI9RGuDM0mDocument276 pagesIT Infrastructure Management eI9RGuDM0mBhawna Singh100% (1)
- Microsoft Azure: Infrastructure As A Service (Iaas)Document16 pagesMicrosoft Azure: Infrastructure As A Service (Iaas)wilberNo ratings yet
- Question Paper Code:: (10×2 20 Marks)Document2 pagesQuestion Paper Code:: (10×2 20 Marks)Ponraj Park100% (4)
- Chapter 1 Introduction To Operating System ConceptsDocument67 pagesChapter 1 Introduction To Operating System ConceptsAbdulrahman khalid100% (1)
- UserManualForNewMembers SMC Swimming Pool SuratDocument17 pagesUserManualForNewMembers SMC Swimming Pool SuratUtsavNo ratings yet
- Design Patterns IntroductionDocument285 pagesDesign Patterns IntroductionMintishu TemesgenzNo ratings yet
- The Arduino Life: Workshop On Arduino Embedded Development BoardDocument41 pagesThe Arduino Life: Workshop On Arduino Embedded Development BoardharishNo ratings yet
- Recognized. Start With at Least The Second Instruction.: Command OperationDocument2 pagesRecognized. Start With at Least The Second Instruction.: Command OperationJingyu XuNo ratings yet
- Platform NotesDocument26 pagesPlatform Notesaniket somNo ratings yet
- FullDating TutorialDocument47 pagesFullDating Tutorialnicholasadjei1090No ratings yet
- Computer Architecture Course IntroDocument13 pagesComputer Architecture Course Intro5NfphK100% (1)
- Goldwind GW165-5.25.6MW-Product BrochureDocument2 pagesGoldwind GW165-5.25.6MW-Product BrochureVictor SNo ratings yet
- Software Installation Instructions For The Carestream Image Suite V4 MR1 SoftwareDocument16 pagesSoftware Installation Instructions For The Carestream Image Suite V4 MR1 SoftwareJuan C GomezNo ratings yet
- Wfretry ReqDocument25 pagesWfretry ReqrodolfoNo ratings yet
- In-System Eye Scan of A PCI Express Link With Vivado IP Integrator and AXI4Document29 pagesIn-System Eye Scan of A PCI Express Link With Vivado IP Integrator and AXI4Amit JainNo ratings yet
- Free Software For Voice Removing From Music?: Frihost Forums Search FAQ TOS Dire Ctory Blogs CompetitionsDocument4 pagesFree Software For Voice Removing From Music?: Frihost Forums Search FAQ TOS Dire Ctory Blogs CompetitionsayubistariNo ratings yet
- Final Advt Project Staff Harsac 06122022Document7 pagesFinal Advt Project Staff Harsac 06122022sid 0596No ratings yet
- Suspects in NYC Shooting That Wounded Boys, 3 and 6, Shown in VideoDocument1 pageSuspects in NYC Shooting That Wounded Boys, 3 and 6, Shown in VideoRamonita GarciaNo ratings yet
- Annex-4-JDVP-Certificate-of-Learners-Mastery Jimley CSS - MasteredDocument17 pagesAnnex-4-JDVP-Certificate-of-Learners-Mastery Jimley CSS - MasteredJimley CanillaNo ratings yet