Professional Documents
Culture Documents
Information System Security
Uploaded by
makangara220 ratings0% found this document useful (0 votes)
7 views2 pagesOriginal Title
INFORMATION SYSTEM SECURITY (1)
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
7 views2 pagesInformation System Security
Uploaded by
makangara22Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 2
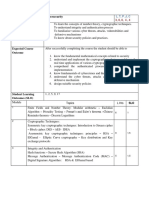
Course title: IS251: Information Systems Security
Course Aims:
The aims of this course are to:
i. Develop an understanding of the role of procedures, policies, standards and
guideline in information systems security.
ii. Develop an understanding of the fundamentals of cryptography, cryptographic
techniques and network security.
iii. Enable students to categorize threats and classify security strategies based on
system security principles.
Course status: Core
Credit rating: 8 credits
Total hours spent: 80 hours
Course Expected Learning Outcomes
By the end of the course, students should be able to:
i. Describe basic information security concepts and defense methods.
ii. Explain Symmetric and Asymmetric Encryption crypto systems.
iii. Design Authentication Applications.
iv. Apply network and information security concepts and cryptographic algorithms.
Course Contents
Introduction to Security Concepts; goals, security threats, attacks,
vulnerabilities, risks and countermeasure, Information security management
taxonomy, policy formation & ethical and legal issues;
Malicious software and network security; Viruses, Trojans, Spyware,
Backdoors, Trapdoors and Rootkits; Intrusion detection and prevention
mechanisms, firewall taxonomy, wireless network security
Cryptography; History and Overview of Cryptography, Encryption basics,
symmetric encryption algorithms: block ciphers and stream ciphers, asymmetric
encryption and Public Key Infrastructure. Secure One-Way Hash Function and
Message Authentication Codes (MD4, MD5, SHA-1, SHA-2, MAC and keyed-
MAC.
Access Control; Key Certificates and Digital Signatures. E-mail, Web and E-
Commerce security (PGP, PKI and SSL). Access Control mechanisms, Access
Control Lists, Capability Lists, Operating Systems Access Control, Security of
Linux and Windows File Systems and personnel and physical security.
Authentication: Authentication mechanisms and technologies for
authentication, Challenge-response systems, Smartcards, Security Tokens,
Biometry and Kerberos.
Emerging Trend in IT Security: Cyber-security, Trusted Computing,
Quantum Cryptography, cloud computing security, proivacy and data theft
issues, Designing secure systems.
Teaching and learning activities: Lectures 30 hours, seminars 15 hours, assignments 15
hours and independent study 20 hours.
Assessment methods: Continuous assessment will comprise 30 marks and Final Examination
70 marks.
Reading List:
1. William Stallings (2010). Cryptography and Network Security: Principles and
Practice, 5th Edition. USA: Prentice Hall.
2. Ross J. Anderson (2008). Security Engineering: A Guide to Building
Dependable Distributed Systems. Wiley.
3. Larry Ullman (2013). Effortless E-Commerce with PHP and MySQL, 2nd
Edition (Voices That Matter). USA: Pearson Education.
4. Gurpreet Dillon (2007). Principles of Information Systems Security: Text and
Cases, 1st Edition. Wiley.
5. Mark Stamp (2005). Information Security: Principles and Practice. Wiley.
You might also like
- CISSP Fast Track Master: CISSP Essentials for Exam Success - Exam Cram Notes: 1st Edition - 2024From EverandCISSP Fast Track Master: CISSP Essentials for Exam Success - Exam Cram Notes: 1st Edition - 2024No ratings yet
- CNS - M1L0Document18 pagesCNS - M1L0Viraj KaleNo ratings yet
- System SecurityDocument4 pagesSystem SecurityTanishka MayekarNo ratings yet
- W.E.F Academic Year 2012-13 G' SchemeDocument5 pagesW.E.F Academic Year 2012-13 G' SchemeSanket bhosaleNo ratings yet
- CNCS2004-Cybersecurity SyllabusDocument3 pagesCNCS2004-Cybersecurity SyllabusZoyaNo ratings yet
- Computersecurity OutlineDocument5 pagesComputersecurity Outlineshifara TesfayeNo ratings yet
- RCS 322 Computer System SecurityDocument5 pagesRCS 322 Computer System SecuritymkweleboiNo ratings yet
- Syllabus For Diploma in Cyber SecurityDocument4 pagesSyllabus For Diploma in Cyber SecurityppghoshinNo ratings yet
- AI 403 Cyber Security and ForensicsDocument2 pagesAI 403 Cyber Security and Forensicssomnath.sinhaNo ratings yet
- Information Security: Dr. Pranita UpadhyayaDocument35 pagesInformation Security: Dr. Pranita UpadhyayaMANOJNo ratings yet
- Course OutlineDocument3 pagesCourse OutlinemubareklibenNo ratings yet
- Pis SyllabusDocument2 pagesPis SyllabusM.K BhaiNo ratings yet
- Security Standards & Audits SyllabusDocument2 pagesSecurity Standards & Audits SyllabusRuma SahaNo ratings yet
- TECH3701 Security June 2005Document2 pagesTECH3701 Security June 2005conor1990No ratings yet
- (R17A0526) Information Security Digital NotesDocument143 pages(R17A0526) Information Security Digital NotesPrafulla Durgadhar GawandeNo ratings yet
- CSE4003 Cyber-Security ETH 1 AC41Document8 pagesCSE4003 Cyber-Security ETH 1 AC41govindNo ratings yet
- Updated(Week 1 & 2)-1Document49 pagesUpdated(Week 1 & 2)-1Muhammad Hassan AwanNo ratings yet
- Cryptography & Network SecurityDocument2 pagesCryptography & Network Securityrishabhdubey0% (1)
- MSU InfoSec Module OutlineDocument3 pagesMSU InfoSec Module OutlineMusariri TalentNo ratings yet
- Title 5Document2 pagesTitle 5М. ЭнэрэлтNo ratings yet
- Course OutlineDocument3 pagesCourse OutlineFasiledesNo ratings yet
- IIT Jammu Times Offers Post Graduate Diploma in Cyber Security - BrochureDocument22 pagesIIT Jammu Times Offers Post Graduate Diploma in Cyber Security - BrochureKhushal OzaNo ratings yet
- Network and System Security Course OverviewDocument3 pagesNetwork and System Security Course OverviewVibhuNo ratings yet
- Syllabus in Computer System SecurityDocument3 pagesSyllabus in Computer System SecurityEra BuzoNo ratings yet
- Week 1 Lecture 1 Information SecurityDocument28 pagesWeek 1 Lecture 1 Information SecurityZulkifl HasanNo ratings yet
- M.Sc. ICT Security CourseDocument4 pagesM.Sc. ICT Security CourseMuller MuleyNo ratings yet
- Syllabus - UCS005E-Information and Network SecurityDocument2 pagesSyllabus - UCS005E-Information and Network Security2BA17CS056 SANTHOSHNo ratings yet
- MCSCB Cyber SecurityDocument16 pagesMCSCB Cyber SecurityKrishna Kumaran ThampiNo ratings yet
- IT Information Security SyllabusDocument2 pagesIT Information Security SyllabuslekhaNo ratings yet
- IS Security INSY3073 - Course OutlineDocument10 pagesIS Security INSY3073 - Course Outlinetaye teferaNo ratings yet
- Cybersecurity Fundamentals Course OutlineDocument4 pagesCybersecurity Fundamentals Course Outlinem3lw1nNo ratings yet
- IT 513 Course OutlineDocument4 pagesIT 513 Course OutlineWaleed HussainNo ratings yet
- IT502 - Information SecurityDocument3 pagesIT502 - Information SecurityNader AzalNo ratings yet
- Information SecurityDocument2 pagesInformation Securityvowafe1088No ratings yet
- Information Assurance and SecurityDocument2 pagesInformation Assurance and SecurityJennifer G. PugalNo ratings yet
- L7Document55 pagesL7Faith NyongesaNo ratings yet
- Introduction To Information SecurityDocument5 pagesIntroduction To Information SecurityjamesNo ratings yet
- 15ec835 NCS SyllabusDocument2 pages15ec835 NCS SyllabusKulandaivel MurugeshNo ratings yet
- Jntuh College of Engineering Hyderabad Dept of Computer Science and EngineeringDocument4 pagesJntuh College of Engineering Hyderabad Dept of Computer Science and EngineeringsidNo ratings yet
- Cryptography and System SecurityDocument3 pagesCryptography and System SecurityNirishNo ratings yet
- Basic Ethical Hackintg and Cyber SecuritDocument3 pagesBasic Ethical Hackintg and Cyber SecuritRASHEED YUSUFNo ratings yet
- Bca Ds Sem-5 Information Security FundamentalsDocument4 pagesBca Ds Sem-5 Information Security FundamentalsVikas SharmaNo ratings yet
- Cyber Security Notes 4-1Document81 pagesCyber Security Notes 4-1Sripriya BellaryNo ratings yet
- Lecture2 Intro (Part-II)Document42 pagesLecture2 Intro (Part-II)Love GatesNo ratings yet
- Information Security Analysis and Audit CourseDocument3 pagesInformation Security Analysis and Audit CourseSukriti Jaitly100% (1)
- Ethical Hacking and Counter Measures Course OutlineDocument7 pagesEthical Hacking and Counter Measures Course Outlineresearch.aiNo ratings yet
- 1 Introduction Network Security CryptographyDocument76 pages1 Introduction Network Security CryptographyPulkit RanjanNo ratings yet
- 16CS2E56 Cyber Security SyllabusDocument1 page16CS2E56 Cyber Security SyllabuskrishnakumarNo ratings yet
- (An Introduction To Computer) : SecurityDocument51 pages(An Introduction To Computer) : SecurityguntureanNo ratings yet
- Cryptography & Network Security Course OverviewDocument44 pagesCryptography & Network Security Course OverviewFree FireNo ratings yet
- Bcse309l Cryptography-And-Network-Security TH 1.0 67 Bcse309lDocument3 pagesBcse309l Cryptography-And-Network-Security TH 1.0 67 Bcse309lMohnish KodukullaNo ratings yet
- CPIS 602 Network Security Intro Lecture Agenda Objectives Contents Resources Grading ContactDocument7 pagesCPIS 602 Network Security Intro Lecture Agenda Objectives Contents Resources Grading ContactManal SaeedNo ratings yet
- Information Security Course OverviewDocument1 pageInformation Security Course Overviewpoonam jindalNo ratings yet
- Information Security Privacy SyllabusDocument1 pageInformation Security Privacy SyllabusANUPMA PRITYNo ratings yet
- CSE403 Network SecurityDocument2 pagesCSE403 Network SecurityrajatNo ratings yet
- Identity and Access Management With CybersecurityDocument17 pagesIdentity and Access Management With CybersecuritySathiyaNo ratings yet
- Course Outline Information SecurityDocument1 pageCourse Outline Information SecurityJebesaNo ratings yet
- Course Plan Information SecurityDocument7 pagesCourse Plan Information SecurityMalik KashifNo ratings yet
- Online Banking Security LevelDocument3 pagesOnline Banking Security LevelfarahfaroroNo ratings yet
- Cyberlaws and SecurityDocument1 pageCyberlaws and Security17001009023 HINGULA BHATNo ratings yet
- Group 03 SecurityDocument9 pagesGroup 03 Securitymakangara22No ratings yet
- Group 8 Ism&csnDocument10 pagesGroup 8 Ism&csnmakangara22No ratings yet
- Assignment 1 INFORMATION SECURITYDocument7 pagesAssignment 1 INFORMATION SECURITYmakangara22No ratings yet
- Information System SecurityDocument10 pagesInformation System Securitymakangara22No ratings yet
- Security PresentationDocument12 pagesSecurity Presentationmakangara22No ratings yet
- Group 8 Ism&csnDocument10 pagesGroup 8 Ism&csnmakangara22No ratings yet
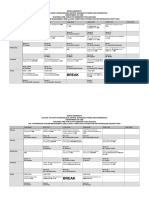
- Timetable V3Document3 pagesTimetable V3makangara22No ratings yet
- Lecture4 AccessControlDocument13 pagesLecture4 AccessControlmakangara22No ratings yet
- Lecture 1Document26 pagesLecture 1makangara22No ratings yet
- Lecture3 AutheticationDocument28 pagesLecture3 Autheticationmakangara22No ratings yet
- Security in Practice: Examining The Collaborative Management of Sensitive Information in Childcare Centers and Physicians' OfficesDocument386 pagesSecurity in Practice: Examining The Collaborative Management of Sensitive Information in Childcare Centers and Physicians' OfficesLaurian VegaNo ratings yet
- SAMPLE GDPR Data Protection Policy TemplateDocument4 pagesSAMPLE GDPR Data Protection Policy Templateoyoo100% (1)
- FD CyberDocument23 pagesFD Cybersudarshan kumarNo ratings yet
- Parul SinghDocument4 pagesParul SinghDevendra KumarNo ratings yet
- Rights of The Mentally Disabled PersonsDocument9 pagesRights of The Mentally Disabled Personsmanu sethi100% (1)
- TheCentralite2024 Undertaking HSDocument1 pageTheCentralite2024 Undertaking HSyuki.kikusawa-22No ratings yet
- BRF Notes PDFDocument13 pagesBRF Notes PDFTheres Ann royNo ratings yet
- CEUSA CH 1 Intro To Cyber SecurityDocument9 pagesCEUSA CH 1 Intro To Cyber SecurityEbenezer KobNo ratings yet
- TASK 1 - BSBCUS501 Develop A Customer Service PlanDocument5 pagesTASK 1 - BSBCUS501 Develop A Customer Service PlanVioleta Hoyos Lopez100% (3)
- DeathDocument1 pageDeathPavan KumarNo ratings yet
- Apple's Winning Marketing StrategyDocument12 pagesApple's Winning Marketing Strategysandy nopen SilalahiNo ratings yet
- PrSLoc Sybil Attack Detection For Localization With Privat - 2023 - ComputersDocument11 pagesPrSLoc Sybil Attack Detection For Localization With Privat - 2023 - ComputersAkashah ArshadNo ratings yet
- Social MediaDocument7 pagesSocial MediaBibiVmvNo ratings yet
- "Friending" "Following" and "Digging" Up Evidentiary Dirt The Ethical ImplicatioDocument20 pages"Friending" "Following" and "Digging" Up Evidentiary Dirt The Ethical ImplicatioMcSteveNo ratings yet
- Social Media Has Become A Ubiquitous Presence in Our LivesDocument1 pageSocial Media Has Become A Ubiquitous Presence in Our LivesAzbi NurediniNo ratings yet
- Chapter 1 Building Planning and DrawingDocument48 pagesChapter 1 Building Planning and DrawingSri D. Pavan KumarNo ratings yet
- Code of EthicsDocument5 pagesCode of EthicspvlreyesNo ratings yet
- Annual Cyber Security Training New Hire PDFDocument82 pagesAnnual Cyber Security Training New Hire PDFsajeerNo ratings yet
- Curecast Emr BrochureDocument7 pagesCurecast Emr BrochureCurecast HealthNo ratings yet
- Data Sharing AgreementDocument4 pagesData Sharing AgreementRSTU PRO8No ratings yet
- Freedom On The Net 2012Document662 pagesFreedom On The Net 2012Sergio Octavio ContrerasNo ratings yet
- BRAINSTORMINGDocument8 pagesBRAINSTORMINGAnuprabha XI BNo ratings yet
- SOP NEET UG Round 1 2023Document2 pagesSOP NEET UG Round 1 2023dhruvwaldiagmchldNo ratings yet
- Employment Law OutlineDocument11 pagesEmployment Law OutlineBrian McKinneyNo ratings yet
- T7 B12 DOJ Doc Req 35-13 Packet 5 FDR - Entire Contents - Response Letters - Reports 404Document147 pagesT7 B12 DOJ Doc Req 35-13 Packet 5 FDR - Entire Contents - Response Letters - Reports 4049/11 Document ArchiveNo ratings yet
- BFP Applicant Information FormDocument3 pagesBFP Applicant Information FormGerika Aura RPhNo ratings yet
- DRSFormDocument11 pagesDRSFormramadhanNo ratings yet
- Rademacher V ABC - MSJDocument26 pagesRademacher V ABC - MSJTHROnlineNo ratings yet
- RCM Certificate of Beamed Antenna 201904 (RCM-05033172)Document2 pagesRCM Certificate of Beamed Antenna 201904 (RCM-05033172)Сергей МирошниченкоNo ratings yet
- SWEDEN-The Electronic Communications Act 2003 389Document24 pagesSWEDEN-The Electronic Communications Act 2003 389Eddie Urenda TellezNo ratings yet
- Microsoft Azure Infrastructure Services for Architects: Designing Cloud SolutionsFrom EverandMicrosoft Azure Infrastructure Services for Architects: Designing Cloud SolutionsNo ratings yet
- AWS Certified Cloud Practitioner Study Guide: CLF-C01 ExamFrom EverandAWS Certified Cloud Practitioner Study Guide: CLF-C01 ExamRating: 5 out of 5 stars5/5 (1)
- Computer Systems and Networking Guide: A Complete Guide to the Basic Concepts in Computer Systems, Networking, IP Subnetting and Network SecurityFrom EverandComputer Systems and Networking Guide: A Complete Guide to the Basic Concepts in Computer Systems, Networking, IP Subnetting and Network SecurityRating: 4.5 out of 5 stars4.5/5 (13)
- CCNA: 3 in 1- Beginner's Guide+ Tips on Taking the Exam+ Simple and Effective Strategies to Learn About CCNA (Cisco Certified Network Associate) Routing And Switching CertificationFrom EverandCCNA: 3 in 1- Beginner's Guide+ Tips on Taking the Exam+ Simple and Effective Strategies to Learn About CCNA (Cisco Certified Network Associate) Routing And Switching CertificationNo ratings yet
- ITIL 4: Digital and IT strategy: Reference and study guideFrom EverandITIL 4: Digital and IT strategy: Reference and study guideRating: 5 out of 5 stars5/5 (1)
- The Compete Ccna 200-301 Study Guide: Network Engineering EditionFrom EverandThe Compete Ccna 200-301 Study Guide: Network Engineering EditionRating: 5 out of 5 stars5/5 (4)
- Amazon Web Services (AWS) Interview Questions and AnswersFrom EverandAmazon Web Services (AWS) Interview Questions and AnswersRating: 4.5 out of 5 stars4.5/5 (3)
- The CompTIA Network+ Computing Technology Industry Association Certification N10-008 Study Guide: Hi-Tech Edition: Proven Methods to Pass the Exam with Confidence - Practice Test with AnswersFrom EverandThe CompTIA Network+ Computing Technology Industry Association Certification N10-008 Study Guide: Hi-Tech Edition: Proven Methods to Pass the Exam with Confidence - Practice Test with AnswersNo ratings yet
- The Ultimate Kali Linux Book - Second Edition: Perform advanced penetration testing using Nmap, Metasploit, Aircrack-ng, and EmpireFrom EverandThe Ultimate Kali Linux Book - Second Edition: Perform advanced penetration testing using Nmap, Metasploit, Aircrack-ng, and EmpireNo ratings yet
- Computer Networking: The Complete Beginner's Guide to Learning the Basics of Network Security, Computer Architecture, Wireless Technology and Communications Systems (Including Cisco, CCENT, and CCNA)From EverandComputer Networking: The Complete Beginner's Guide to Learning the Basics of Network Security, Computer Architecture, Wireless Technology and Communications Systems (Including Cisco, CCENT, and CCNA)Rating: 4 out of 5 stars4/5 (4)
- Evaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsFrom EverandEvaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsRating: 5 out of 5 stars5/5 (1)
- Computer Networking: The Complete Guide to Understanding Wireless Technology, Network Security, Computer Architecture and Communications Systems (Including Cisco, CCNA and CCENT)From EverandComputer Networking: The Complete Guide to Understanding Wireless Technology, Network Security, Computer Architecture and Communications Systems (Including Cisco, CCNA and CCENT)No ratings yet
- Designing and Building Security Operations CenterFrom EverandDesigning and Building Security Operations CenterRating: 3 out of 5 stars3/5 (3)
- ITIL® 4 Direct, Plan and Improve (DPI): Your companion to the ITIL 4 Managing Professional and Strategic Leader DPI certificationFrom EverandITIL® 4 Direct, Plan and Improve (DPI): Your companion to the ITIL 4 Managing Professional and Strategic Leader DPI certificationNo ratings yet
- Introduction to Cyber-Warfare: A Multidisciplinary ApproachFrom EverandIntroduction to Cyber-Warfare: A Multidisciplinary ApproachRating: 4.5 out of 5 stars4.5/5 (3)
- AWS Certified Solutions Architect Study Guide: Associate SAA-C02 ExamFrom EverandAWS Certified Solutions Architect Study Guide: Associate SAA-C02 ExamNo ratings yet
- ITIL® 4 Create, Deliver and Support (CDS): Your companion to the ITIL 4 Managing Professional CDS certificationFrom EverandITIL® 4 Create, Deliver and Support (CDS): Your companion to the ITIL 4 Managing Professional CDS certificationRating: 5 out of 5 stars5/5 (2)
- Advanced Antenna Systems for 5G Network Deployments: Bridging the Gap Between Theory and PracticeFrom EverandAdvanced Antenna Systems for 5G Network Deployments: Bridging the Gap Between Theory and PracticeRating: 5 out of 5 stars5/5 (1)