Professional Documents
Culture Documents
JO MSW Bypassing Critical Protections Standard
Uploaded by
cbatanaOriginal Description:
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
JO MSW Bypassing Critical Protections Standard
Uploaded by
cbatanaCopyright:
Available Formats
JOSOP 407 — Bypassing Critical
Protections Standard
Approved 27 February 2008
Version 1.1.1.A Posted 30 March 2009
JO – Bypassing Critical Protections Standard
Table of Contents
1.0 Purpose, Objectives and Scope......................................................................................... 3
1.1 Purpose ...................................................................................................................... 3
1.2 Objective.................................................................................................................... 3
1.3 Scope ......................................................................................................................... 3
2.0 Requirements ..................................................................................................................... 3
3.0 Terms and Definitions ....................................................................................................... 4
4.0 Roles, Responsibilities and Training Requirements....................................................... 5
4.1 Initial Training ........................................................................................................... 5
4.2 Refresher Training ..................................................................................................... 6
5.0 Standard Instructions ....................................................................................................... 6
5.1 Bypassing Steps ......................................................................................................... 6
5.2 Assessing and Managing Hazards ............................................................................. 6
5.3 Bypass Administration and Controls ......................................................................... 7
5.3.1 Layers of Protection ......................................................................................... 7
5.3.2 Minimizing Personnel and Critical Protection Devices in Bypass at Any One
Time ................................................................................................................. 7
5.3.3 Identifying Bypassed Critical Protection Devices ........................................... 7
5.3.4 Monitoring of Operating Conditions/Parameters............................................. 8
5.4 Monitoring and Audit ................................................................................................ 9
6.0 Records ............................................................................................................................. 10
6.1 Required Records .................................................................................................... 10
6.2 Retention Requirements .......................................................................................... 10
7.0 References ........................................................................................................................ 10
8.0 Other Guidance Documents ........................................................................................... 10
9.0 Document Control ........................................................................................................... 10
Appendix A: JO Critical Protection Bypass Register .......................................................... 12
Appendix B: JO Critical Protections Bypass Audit Sheet ................................................... 13
ii Version 1.1.1.A Posted 30 March 2009.
Printed 15 August 2013. Uncontrolled when printed.
JOSOP407JO_MSW_BypassingCriticalProtectionsStandard(updated).doc
JO – Bypassing Critical Protections Standard
1.0 Purpose, Objectives and Scope
1.1 Purpose
The purpose of this standard is to ensure that bypassing of critical protections is
performed in a safe and controlled manner.
1.2 Objective
This standard establishes the requirements for the safe performance of the necessary
bypassing of critical protections.
NOTE: Each Global Upstream strategic business unit (SBU) or location may have
additional regulatory requirements.
1.3 Scope
This Bypassing Critical Protection Standard covers work performed by JO employees
and their delegates and contractors within JO operational control.
This standard is applicable to plant/platform critical protective devices or systems where
it is possible to apply a hardware or software bypass, force, inhibit, override, or their
electrical equivalent.
This standard does not apply to the following:
• When the purpose of the bypass is for Lockout/tagout. For lockout/tagout, please
see JO – Isolation of Hazardous Energy Standard.
• “Startup overrides” designed with automatic removal after a specified time delay
• Permanent bypasses, the application of bypasses that change the basis of design as
it relates to safety and/or critical protections that are already properly isolated, must
be managed under the JO - Management of Change Process and/or the JO -
Isolation of Hazardous Energy Standard.
NOTE: This system is not intended to replace the Isolation of Hazardous Energy
Standard. However, on occasion it may be used in conjunction with the Isolation of
Hazardous Energy Standard.
2.0 Requirements
1. Personnel involved in the authorization, approval, and implementation of
bypassing critical protections shall be trained and competent in the roles for which
they are responsible.
2. Hazards involved with bypassing critical protections for maintenance or testing,
planned or unplanned, must be assessed, and alternative protections must be
identified.
3. Bypassing, isolating, or removing critical protections during upset/abnormal
operating conditions in order to maintain production is strictly forbidden.
4. Only a minimum number of critical protective devices shall be bypassed at a time.
There shall be at least one other layer of protection whenever a critical protection is
on bypass.
5. Facility management shall conduct periodic audits and verifications to ensure
compliance to this standard.
Version 1.1.1.A Posted 30 March 2009. 3
Printed 15 August 2013. Uncontrolled when printed.
JOSOP407JO_MSW_BypassingCriticalProtectionsStandard(updated).doc
JO – Bypassing Critical Protections Standard
3.0 Terms and Definitions
The following terms and definitions apply to the JO – Safe Work Practice (SWP) –
Bypassing Critical Protections:
Bypass - To temporarily block out, isolate, override, inhibit, force, jumper, or disable a
device or system so that it will not perform its designed function for the purpose of
testing, maintenance and startup.
NOTE: For the purpose of this standard, the words “bypass,” “isolate,” “override,”
“inhibit,” “force,” “jumper,” “block,” “disable” or any other term used to describe the
temporary act of disabling a critical protective device or system have the same meaning.
Critical Protections - Devices or systems designed to protect personnel, the
environment, process, equipment and properties from an undesirable event. Functional
critical protections are a vital component of safety systems. They are designed and
installed to ensure safe, reliable and environmentally sound operations. Critical
protections consist of hardware and software which include, but are not limited to, the
following:
• Shutdown devices or systems such as Pressure Safety Low Low (PSLL), Pressure
Safety High High (PSHH), Emergency Shutdown (ESD) valves, etc.
• Fire and gas detection and fire suppression devices such as fire pumps, deluge
systems, fusible loops, CO2 fire extinguishing systems, etc.
• Pressure Safety Valve (PSV), Blowdown Valve (BDV) and associated valves
• Safety critical manual valves that are (normally) locked open or closed
• Equipment safeguards, overspeed trip, fired equipment flame detectors and similar
safety systems
Effective Monitoring - Effective monitoring is, in effect, taking the place of the critical
protections. An individual must be able to manually provide the same level of protection
as the bypassed critical protection(s) in a timely manner in order to prevent an
undesirable event. (Leaving the area for breaks, parts, supplies or tools would
compromise effective monitoring.)
Flag/Tag - A hanging, removable placard that identifies the status of a critical protection
device. Tags should only be used on bypassed or temporarily out-of-service devices or
components.
In-Service - The device or component is performing its designed function.
Layers of Protection (LOPs) or Lines of Defense (LODs) - Measures for prevention
and mitigation of major accidents. These LOPs serve either to prevent an initiating event
from developing into an incident, or to mitigate the consequences of an incident once it
occurs.
Maintenance - Adjustments or repairs, typically for a short duration (e.g., 15 minutes),
that can be performed without compromising effective monitoring.
Out-of-Service - A device or component is out-of-service (OOS) when it is not being
used to perform its intended function, and it is properly isolated by the use of the JO
Isolation of Hazardous Energy SWP standard.
4 Version 1.1.1.A. Posted 30 March 2009.
Printed 15 August 2013. Uncontrolled when printed.
JOSOP407JO_MSW_BypassingCriticalProtectionsStandard(updated).doc
JO – Bypassing Critical Protections Standard
Properly Isolated Protection - Protective devices or systems that are properly isolated
or disconnected by means of positive isolation; for example, a blind flange to prevent
transfer or communication of any fluids.
Qualified Person - A person who has successfully completed a production safety system
training program and who is familiar with the site-specific monitoring procedures of that
facility. Any person who has not received the required training must be directly
supervised by a qualified person when engaged in installing, testing, inspecting, flagging,
bypassing, monitoring or maintaining critical protections.
Remote Site - Satellite or subordinate offshore platform that is not bridge-connected to
the parent facility, or an onshore site that is controlled remotely by its parent facility
using SCADA (Supervisory Control and Data Acquisition).
Remote Monitoring - Monitoring of operating parameters on a remote site by a
qualified person at a central location by means of a telecommunications system such as
SCADA.
Startup - The period of time required for the production process to stabilize while
resuming normal operations.
Testing - The process of validating the set point and/or functionality of a device or
system.
Temporarily Out-of-Service - A component is temporarily out-of-service when it is in
standby, shutdown or not-in-use mode, but when needed, can easily be returned to
service. These components are NOT isolated from production facilities.
4.0 Roles, Responsibilities and Training Requirements
There must be clearly defined roles, and personnel must meet the training and
competency requirements of this standard prior to starting work. JO is responsible for
establishing the methodology to achieve competence.
When selecting personnel for these positions, consideration should be given to their level
of experience and their past performance.
The following roles and responsibilities are specific to Bypassing Critical Protections
and are further defined in the JO –Training Requirements Tool:
• Qualified Person
Ensure effective monitoring and layers of protection are in place when bypassing systems
Monitoring of operating parameters on a remote site
Utilize management of change process when appropriate
May participate in hazard analysis and identification of controls to be implemented to eliminate or
minimize risk
Partakes in post-job debrief if required
Ensures competent personnel perform required functions
Stops the work if unsafe conditions develop
For updates refer to JO_MSW_TrainingRequirementsTool.doc
4.1 Initial Training
Personnel must meet the competency requirements of this standardized safe work
practice prior to starting work. Refer to the JO – Training Requirements Tool.
Version 1.1.1.A Posted 30 March 2009. 5
Printed 15 August 2013. Uncontrolled when printed.
JOSOP407JO_MSW_BypassingCriticalProtectionsStandard(updated).doc
JO – Bypassing Critical Protections Standard
4.2 Refresher Training
Refresher training must be provided as follows:
• As required by applicable regulations or JO policy
• As needed when identified by verification, inspections, incidents or audits.
5.0 Standard Instructions
When considering work that involves bypassing critical protection devices, always
consider whether there is a viable alternative to performing a bypass while equipment,
operations or process is shut down.
5.1 Bypassing Steps
The following steps should be followed when placing a critical protection device in
bypass:
1. Identify critical protection devices to be temporarily bypassed
2. Obtain approval to bypass devices
3. Flag devices to be bypassed
4. Perform bypass
5. Monitor the bypassed or blocked-out functions
6. Complete startup, shutdown, operation, maintenance, or testing activities
7. Return critical protective device or system to normal service, and verify
functionality
8. Check/verify work completion and notify affected personnel before removing the
bypasses and flags
5.2 Assessing and Managing Hazards
Bypassing critical protections must be managed in accordance with the JO – Managing
Safe Work Process and the JO Permit to Work Standard.
NOTE: For longer term bypasses, the JO – Isolation of Hazardous Energy Standard
and JO – Management of Change Process should be consulted.
A hazard analysis shall be conducted to assess the potential consequences and effects
prior to the application of bypasses, inhibits/overrides, force, or disable. This includes
the use of any bypass that is required for plant startup that does not time out or that
reverts to a live state when the plant returns to normal operating condition.
A hazard analysis that has previously been used for this purpose may be used again,
providing it has been reviewed, updated and signed off as current.
A completed hazard analysis may indicate that the override, inhibit or force may not
safely be applied, or that further, detailed hazard analysis is required in consultation with
other subject matter experts (SMEs).
6 Version 1.1.1.A. Posted 30 March 2009.
Printed 15 August 2013. Uncontrolled when printed.
JOSOP407JO_MSW_BypassingCriticalProtectionsStandard(updated).doc
JO – Bypassing Critical Protections Standard
5.3 Bypass Administration and Controls
5.3.1 Layers of Protection
Layers of protection shall be considered before bypassing any critical protection device
or system. The minimum number of layers of protection for any initiating event at any
time must be maintained when bypassing critical protection devices or systems.
The hierarchy of the layer of protection must start with the design (inherent safety).
Assuming the design of the equipment meets JO standards, the next layer of protection to
be considered is control.
5.3.2 Minimizing Personnel and Critical Protection Devices in
Bypass at Any One Time
Only the minimum number of critical protection devices shall be bypassed at any one
time.
The number of personnel who monitor protection devices in lieu of automatic protection
shall be kept to an absolute minimum. Any person asked to perform the function of a
critical protection device while that protective device is in bypass shall know and
understand the procedures regarding this type of monitoring.
If the requirements of section 5.2 Assessing and Managing Hazards are met, protective
devices or systems may be bypassed to allow startup, maintenance or testing tasks to be
performed.
Although it may be convenient to override extra critical protection devices to
prevent nuisance shut-ins or to use “group override,” use of such group devices is
not permitted.
As soon as the task is completed, the protection device must be placed back in service.
Remove the flag/tag and notify the affected personnel.
5.3.3 Identifying Bypassed Critical Protection Devices
Critical protection devices that have been bypassed must be identified by a bypass flag or
tag at the bypass or isolation point.
JO/facility shall identify bypassed critical protection devices or systems by a minimum
of two identification methods. Two of these three may be used in any combination:
bypass register, flagging, and/or bypass display board.
Critical protection devices and systems which are temporarily out of service shall be
tagged “temporarily out of service.” These flags or tags shall be fitted to the devices
being bypassed where they are located, such as at the local control panel, isolation valve,
etc.
The purpose of a flag or tag is to be a visual reminder/alert to personnel that a critical
protection is in bypass.
5.3.3.1 Personal Tags
A sufficient number of bypass flags/tags shall be provided to each qualified person.
These flags/tags should be accounted for at the end of each work shift. This
requirement has the following benefits:
• Provides immediate availability of flags/tags
• Provides built-in compliance so that only a minimum number of devices may
be bypassed
Version 1.1.1.A Posted 30 March 2009. 7
Printed 15 August 2013. Uncontrolled when printed.
JOSOP407JO_MSW_BypassingCriticalProtectionsStandard(updated).doc
JO – Bypassing Critical Protections Standard
• Serves as a reminder to the qualified person to review the day’s work and
account for flagged devices placed on bypass
5.3.3.2 Bypass Tag Display Board
Bypass tag display board(s) may be used as another means of control and
communication. The board should be located at each facility in the control room or at
the panels, whichever location is deemed more effective by the workgroup.
The bypass tag display board provides the following advantages:
• Flags are readily accessible any time a critical protection device or system
needs to be bypassed.
• Tag display boards visually alert personnel that a critical protection device or
system is on bypass if a flag/tag is missing from its hanger.
• The tag display board serves as a reminder to personnel to review the day’s
work and to account for flagged critical protection devices or systems placed
on bypass.
5.3.3.3 Bypass Register
Bypass register(s) may be used as another means of control and communication. The
register should be located at each facility in the control room or at the panels,
whichever location is deemed more effective by the work group. A sample bypass
register is provided in Appendix A: JO Critical Protection Bypass Register.
The bypass register provides the following advantages:
• The register serves as a reminder to personnel to review the day’s work and to
account for flagged critical protection devices or systems placed on bypass.
5.3.3.4 Secondary Flagging
A secondary flagging device shall be installed on the front of an auxiliary control
panel so that it is clearly visible if the condition or operating mode of a bypassed
critical protection device cannot easily be seen (i.e., devices/isolation valves are
inside a control panel, slave panels, plugged relay ports, on a boat landing ESD, etc.).
5.3.4 Monitoring of Operating Conditions/Parameters
5.3.4.1 Site-Specific Monitoring
Any critical protection device on a piece of equipment that does not have an equal
and redundant device to detect the same condition shall be continually monitored by
a qualified person(s) at the location while the device is in bypass.
When a qualified person is monitoring a bypassed critical protection device, he or she
is taking the place of the critical protection device, and must be able to manually
provide the same level of protection as the critical protection device in a timely
manner to prevent an undesirable event. Qualified personnel shall monitor the
bypassed or blocked-out functions until the critical protection device or system is
placed back in service.
The area controller at the location shall determine the process, procedures, and
number of personnel required to provide effective monitoring for each critical
protection device or system that is placed in bypass. Effective monitoring can be
conducted by one individual on more than one critical protection device in the same
8 Version 1.1.1.A. Posted 30 March 2009.
Printed 15 August 2013. Uncontrolled when printed.
JOSOP407JO_MSW_BypassingCriticalProtectionsStandard(updated).doc
JO – Bypassing Critical Protections Standard
general area, provided the person can freely move around the general area of
production equipment and effectively monitor more than one process simultaneously.
Qualified persons who are bypassing critical protection devices or systems will be
responsible for answering the following questions:
• What is the process variable to be monitored?
• What device will be used to monitor the process variable?
• How will the process be controlled?
• At what point must the qualified person react to prevent an undesirable event?
• Will this procedure provide the same level of protection as the critical
protection device?
• How many people are required to effectively monitor the bypassed
system/equipment?
NOTE: It is not necessary to monitor the bypassed critical protection device or
system function which has been placed out-of-service. However, the pressure safety
valve on any out-of-service component must be left in service, maintained, and tested
in accordance with company policy or applicable regulatory requirements.
5.3.4.2 Remote Monitoring
On some occasions, there may be a need to bypass critical protection devices or
systems, and monitor the operating parameter using the Supervisory Control and
Data Acquisition (SCADA) system. The only time that bypassed critical protection
devices or systems may be remotely bypassed and monitored is when all of the
following conditions are met:
• The SCADA control operator must place the critical protection device or
system on bypass only as part of a reset or startup activity.
• Radio communications must be maintained at all times between the person at
the remote location and the SCADA control operator.
• The SCADA control operator may only monitor a minimum number of critical
protection devices. If multiple critical protection devices or systems are to be
monitored, the SCADA control operator must be able to view the appropriate
data on one SCADA screen.
• The bypassed critical protection device or system must be returned to service
immediately after it has been cleared and the process has stabilized.
• Remote monitoring of mechanically disabled critical protection devices or
systems (e.g., “pinning” a pneumatic relay) is not allowed.
• Other site-specific guidelines may be required. These should be documented
and maintained at the remote control facility.
5.4 Monitoring and Audit
Routine monitoring and auditing shall be conducted to ensure that this standard is being
applied properly.
The supervisor responsible for the work area shall monitor and conduct periodic audits to
review the integrity of the bypassing procedure. Appendix B: JO Critical Protections
Bypass Audit Sheet may be used.
Version 1.1.1.A Posted 30 March 2009. 9
Printed 15 August 2013. Uncontrolled when printed.
JOSOP407JO_MSW_BypassingCriticalProtectionsStandard(updated).doc
JO – Bypassing Critical Protections Standard
6.0 Records
6.1 Required Records
The following records will be kept:
• Copies of permits and associated documentation shall be maintained in accordance
with the JO Permit to Work Standard.
6.2 Retention Requirements
Documentation shall be retained as required by local regulation, JO policy, or for a
minimum of six months, whichever is greater.
7.0 References
Table 1. Document List
Title File Name
JO – Training Requirements Tool JO_MSW_TrainingRequirementsTool.doc
JO – Isolation of Hazardous Energy Standard JO_MSW_IsolationofHazardousEnergy
Standard.doc
8.0 Other Guidance Documents
Table 2. Document List
Title File Name
American Petroleum Institute (API) American Petroleum Institute (API)
Recommended Practice (RP) 14-C, Safety
Analysis for Production Platforms
9.0 Document Control
Table 1: Document Control Information
Description GU Common SBU-Specific
Approval Date 27 February 2008 17 December 2008
10 Version 1.1.1.A. Posted 30 March 2009.
Printed 15 August 2013. Uncontrolled when printed.
JOSOP407JO_MSW_BypassingCriticalProtectionsStandard(updated).doc
JO – Bypassing Critical Protections Standard
Description GU Common SBU-Specific
Next Revision Due 27 February 2011 17 December 2011
Control Number
Table 2: Document History
Version Date Notes
Number
1.0 27 February 2008 Initial Release
1.1 8 December 2008 Added bookmarks for OE Mentor
1.1.1 17 December SAC Adoption of MSW
2008
1.1.1.A 30 March 2009 JO Version Created
Version 1.1.1.A Posted 30 March 2009. 11
Printed 15 August 2013. Uncontrolled when printed.
JOSOP407JO_MSW_BypassingCriticalProtectionsStandard(updated).doc
JO – Bypassing Critical Protections Standard
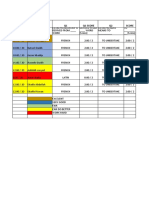
Appendix A: JO Critical Protection Bypass Register
Date Time Operator On Tag Description Reason for Bypass Date Back in Time Back in Operator on
Bypassed Bypassed Duty Number Service Service Duty
For Shift Handover:
I have reviewed and confirmed that this Bypass Register is correct and current.
Outgoing shift responsible person - Name: ___________________________ Signature: ____________________Date:___________ Time: ______________
Incoming shift responsible person - Name: ___________________________ Signature: ____________________Date:___________ Time: _____________
12 Version 1.1.1.A. Posted 30 March 2009.
Printed 15 August 2013. Uncontrolled when printed.
JOSOP407JO_MSW_BypassingCriticalProtectionsStandard(updated).doc
JO - Bypassing Critical Protections
Appendix B: JO Critical Protections Bypass Audit Sheet
TOTAL NUMBER OF BYPASSES/INHIBITS/OVERRIDES BYPASSES/ OVERRIDES
AT TIME OF AUDIT INHIBITS
Comments
(Mandatory where answer is No)
Is the Bypass/Inhibit/Override classified correctly? Yes/No
Is the Bypass/Inhibit/Override Hazard Analysis completed and Yes/No
documented correctly?
Was the appropriate level of authorization given before allowing Yes/No
bypass to take place?
Do the Bypass/Inhibit/Override Registers reflect the true Yes/No
equipment inhibit status and correctly reflect the status of the
Hazard Analysis forms?
Are identified additional control measures in place? Yes/No
Have actions to be taken in the event of a genuine trip/alarm on Yes/No
the device inhibited/overridden been identified?
Are bypassed devices or systems properly flagged or tagged? Yes/No
Are inhibits/overrides that have been removed correctly signed Yes/No
off?
Did outgoing shift and incoming shift review and sign off Bypass Yes/No
Register?
Identify any inhibits/overrides that are continually in use or frequently installed and request engineering support
for a solution.
Remedial actions required:
General comments:
Audited by (Print Name): Signature: Time: Date:
NOTE: Attach photocopies of relevant documents as appropriate.
Version 1.1.1.A. Posted 30 March 2009. 13
Printed 15 August 2013. Uncontrolled when printed.
JOSOP407JO_MSW_BypassingCriticalProtectionsStandard(updated).doc
You might also like
- BD Solutions PDFDocument31 pagesBD Solutions PDFLoya Yang100% (3)
- 01.-Panel Descarga 4004R (579-354)Document102 pages01.-Panel Descarga 4004R (579-354)Carlos Talivento Andrade100% (3)
- Landscape Composition Lite by Mads Peter IversenDocument25 pagesLandscape Composition Lite by Mads Peter IversenEduar Osorno100% (2)
- Durabilt 5MV TGEH-6685Document78 pagesDurabilt 5MV TGEH-6685Luis Cordoba0% (1)
- Studio 5000 Logix Designer Advanced Lab ManualDocument280 pagesStudio 5000 Logix Designer Advanced Lab ManualOtávio Martins100% (1)
- SMC Flex User ManualDocument140 pagesSMC Flex User ManualjoaoNo ratings yet
- ASCO RCS-Safety-ManualV9535R2x PDFDocument22 pagesASCO RCS-Safety-ManualV9535R2x PDFpaul_brightNo ratings yet
- Isolation LOTO Procedure V1 0Document14 pagesIsolation LOTO Procedure V1 0Aceel Fitch100% (2)
- A Feasibility Study of Using Two-Component Polyurethane Adhesive in PDFDocument6 pagesA Feasibility Study of Using Two-Component Polyurethane Adhesive in PDFALINo ratings yet
- SWP Bypassing Critical Protections GuidelinesDocument10 pagesSWP Bypassing Critical Protections Guidelinesesakkiraj1590100% (1)
- KMS-0024 Fusesaver Control Panel - Type 1 Operating Instructions R05Document28 pagesKMS-0024 Fusesaver Control Panel - Type 1 Operating Instructions R05jean alvesNo ratings yet
- L13 - Studio 5000® and Logix Advanced Lab: For Classroom Use Only!Document216 pagesL13 - Studio 5000® and Logix Advanced Lab: For Classroom Use Only!cuongvcs100% (1)
- Procedimiento de Trabajo Seguro para ExcavacionesDocument10 pagesProcedimiento de Trabajo Seguro para ExcavacionesJeduardo Ch-mezaNo ratings yet
- Ai 5303 Tips05 SIEMENS ManualDocument34 pagesAi 5303 Tips05 SIEMENS ManualrogeriolucenaNo ratings yet
- Test Frame User GuideF0435F24EC43Document26 pagesTest Frame User GuideF0435F24EC43Francisco PestañoNo ratings yet
- 579-989 - Installation Guide 4010ESDocument112 pages579-989 - Installation Guide 4010ESLuis Garcia NoriegaNo ratings yet
- Introduction To Safety SystemsDocument24 pagesIntroduction To Safety SystemsThiyagarajan SankaranNo ratings yet
- HES203 - Isolation of Hazardous Energy Standard PDFDocument32 pagesHES203 - Isolation of Hazardous Energy Standard PDFmahdi_gNo ratings yet
- IBU Work at HeightDocument28 pagesIBU Work at HeightAndrianto BakriNo ratings yet
- 320Document22 pages320Muneendra SharmaNo ratings yet
- Controller Setting Kit Software (ACT Controller) : Product NameDocument33 pagesController Setting Kit Software (ACT Controller) : Product NameCesar ChaconNo ratings yet
- Fall UseGuide-2015 PDFDocument29 pagesFall UseGuide-2015 PDFAbdel Nasser Al-sheikh YousefNo ratings yet
- Hướng dẫn sử dụng thiết bị đo lưu lượng gió Testo 420Document26 pagesHướng dẫn sử dụng thiết bị đo lưu lượng gió Testo 420Testo Việt NamNo ratings yet
- ThinManager Basics LabDocument151 pagesThinManager Basics Labvõ cường100% (1)
- Explosion Suspension SystemDocument19 pagesExplosion Suspension SystemMohamed AAmerNo ratings yet
- Somachine Basic Example Guide: Importing Twido Drive Macros To M221 Xsample - Twido - Macro - Drive - Conversion - SmbeDocument42 pagesSomachine Basic Example Guide: Importing Twido Drive Macros To M221 Xsample - Twido - Macro - Drive - Conversion - SmbeMagda DiazNo ratings yet
- PRO 4 5 0001 1 02-Energy-IsolationDocument23 pagesPRO 4 5 0001 1 02-Energy-IsolationNOUREDINENo ratings yet
- Lesson 7 Control of Hazardous Energy: 10 Hour OSHA ConstructionDocument29 pagesLesson 7 Control of Hazardous Energy: 10 Hour OSHA ConstructionCarlos LopézNo ratings yet
- Testo Probes A700000008644025Document50 pagesTesto Probes A700000008644025americo vazNo ratings yet
- Cis WSH Cetsp27 114797 7Document77 pagesCis WSH Cetsp27 114797 7naveedNo ratings yet
- SIS-OW351 - 45 - Ovation SIS Safety ManualDocument37 pagesSIS-OW351 - 45 - Ovation SIS Safety ManualRicardas KragnysNo ratings yet
- Sifang - csc-211 Multifunction Protection Ied Manual (Fosf.451.152e) - v1.00Document48 pagesSifang - csc-211 Multifunction Protection Ied Manual (Fosf.451.152e) - v1.00MarkusKunNo ratings yet
- Sargas-Pj1 FSM en RFLP 250915Document150 pagesSargas-Pj1 FSM en RFLP 250915william lozadaNo ratings yet
- EI-LOTO Written Program Final-REV 06-01-2016Document51 pagesEI-LOTO Written Program Final-REV 06-01-2016AnilNo ratings yet
- Instruction Manual: SK-H SeriesDocument12 pagesInstruction Manual: SK-H SeriesDbxbxn CbdnfnNo ratings yet
- Ultrasil™ Polymer-Housed Varistar™ Surge Arrester Iec 60099-4 For MV Systems To 36 KV Installation InstructionsDocument8 pagesUltrasil™ Polymer-Housed Varistar™ Surge Arrester Iec 60099-4 For MV Systems To 36 KV Installation InstructionsNguyen Anh TuNo ratings yet
- Ns Tast GD 003Document40 pagesNs Tast GD 003cbatanaNo ratings yet
- GF Pre Acp DNP3 EngDocument164 pagesGF Pre Acp DNP3 EngEduardo CampoverdeNo ratings yet
- 975 Uf Uvir Manual Del UsuarioDocument84 pages975 Uf Uvir Manual Del Usuariojose roberto reyes reyesNo ratings yet
- SA R7 Service Manual Rev3.0 ENGDocument216 pagesSA R7 Service Manual Rev3.0 ENGcezary.klosowski.marmedNo ratings yet
- Lockout Tagout Program June 2003Document9 pagesLockout Tagout Program June 2003labn7No ratings yet
- CopieDocument62 pagesCopieYacine BoumertitNo ratings yet
- LOTO Policy Template - Go To File - Download To EditDocument19 pagesLOTO Policy Template - Go To File - Download To EdithamidsohailNo ratings yet
- Asco Pilot Valve Operating ManualDocument7 pagesAsco Pilot Valve Operating ManualSankar SasmalNo ratings yet
- 200 A, 15 and 25 KV Class Loadbreak Bushing Insert S500121Document8 pages200 A, 15 and 25 KV Class Loadbreak Bushing Insert S500121Roberto CedilloNo ratings yet
- Aoralscan 2 - User Manual - V1.0.0.30Document118 pagesAoralscan 2 - User Manual - V1.0.0.30Bagus Nenda WijayaNo ratings yet
- E-C.2.4-HQ-PRO-001 Process and Mechanical Valving and Isolation PhilosophyDocument16 pagesE-C.2.4-HQ-PRO-001 Process and Mechanical Valving and Isolation Philosophyagaricus100% (2)
- 501 2012 6 28 27 39 561Document26 pages501 2012 6 28 27 39 561MITHILESH KUMARNo ratings yet
- 20 Autopulse Z-10Document89 pages20 Autopulse Z-10zayagoraNo ratings yet
- SO Safety Manual F300K DLT7663 19 AEN 003Document22 pagesSO Safety Manual F300K DLT7663 19 AEN 003Ali JamaliNo ratings yet
- SIFANG CSC-101 - V1.20 - Numerical EHV Transmission Line Protection Equipment Manual - 2014-01Document115 pagesSIFANG CSC-101 - V1.20 - Numerical EHV Transmission Line Protection Equipment Manual - 2014-01MarkusKunNo ratings yet
- Form 6 Microprocessor-Based Recloser Control Automatic Source Transfer (AST) Application InstructionsDocument44 pagesForm 6 Microprocessor-Based Recloser Control Automatic Source Transfer (AST) Application InstructionsRachmad Adi WidodoNo ratings yet
- Paxprimo Vatech Installation CablesDocument72 pagesPaxprimo Vatech Installation CablesJoseluis MoralesNo ratings yet
- SUNGROW SG320 - 350HX User Manual enDocument127 pagesSUNGROW SG320 - 350HX User Manual enJhossaffMackenzieNo ratings yet
- Perating Nstructions: Movitrac B KeypadDocument32 pagesPerating Nstructions: Movitrac B Keypaddrdmg22No ratings yet
- DroppedObjectsPreventionStandard - Eng 05 05 17 PDFDocument15 pagesDroppedObjectsPreventionStandard - Eng 05 05 17 PDFAndrew LiddellNo ratings yet
- FT Historian IN11Document100 pagesFT Historian IN11Uriel Lv100% (1)
- NK-O3 Safety Manuals (Rev.1)Document18 pagesNK-O3 Safety Manuals (Rev.1)greatenick.nbNo ratings yet
- Quick Reference Guide Kurzanleitung Instruction de Service Guía de Referencias Rápidas Guida Di Riferimento RapidoDocument402 pagesQuick Reference Guide Kurzanleitung Instruction de Service Guía de Referencias Rápidas Guida Di Riferimento RapidoRoger RiveroNo ratings yet
- Lockout Tagout Program: University of WashingtonDocument12 pagesLockout Tagout Program: University of WashingtonVictorNo ratings yet
- Process IsolationDocument13 pagesProcess IsolationBhuran AkshayNo ratings yet
- Chainsaw Operator's Manual: Chainsaw Safety, Maintenance and Cross-cutting TechniquesFrom EverandChainsaw Operator's Manual: Chainsaw Safety, Maintenance and Cross-cutting TechniquesRating: 5 out of 5 stars5/5 (1)
- TD3 AutoDocument2 pagesTD3 AutocbatanaNo ratings yet
- 11 Champs MaturesDocument73 pages11 Champs MaturescbatanaNo ratings yet
- Ns Tast GD 003Document40 pagesNs Tast GD 003cbatanaNo ratings yet
- Gs36j40b20-01en - 002 SFM R302Document4 pagesGs36j40b20-01en - 002 SFM R302cbatanaNo ratings yet
- Pedagogical Practice in Teaching - Learning Mathematics in Secondary in School LevelDocument8 pagesPedagogical Practice in Teaching - Learning Mathematics in Secondary in School LevelapfgNo ratings yet
- M.Arch Synopsis Structure PDFDocument5 pagesM.Arch Synopsis Structure PDFTeja VedulaNo ratings yet
- DESIGNDocument29 pagesDESIGNerick kazindukiNo ratings yet
- Biovia Materials Studio Dmol: DatasheetDocument3 pagesBiovia Materials Studio Dmol: DatasheettonymailinatorNo ratings yet
- Batch 3 UnescoDocument27 pagesBatch 3 UnescoHeaven Diaz100% (1)
- Springer Reassessing European Impressions of Indian AstronomyDocument7 pagesSpringer Reassessing European Impressions of Indian AstronomyAnkur KakkarNo ratings yet
- Signal Estimation & Detection TheoryDocument6 pagesSignal Estimation & Detection TheoryMANISH TIWARINo ratings yet
- Review Article Tracing The Recorded History of ThiDocument61 pagesReview Article Tracing The Recorded History of ThiPreparaduriasFisicaMatematicaNo ratings yet
- Unisonic Technologies Co., LTD: 9A, 700V N-CHANNEL Power MosfetDocument4 pagesUnisonic Technologies Co., LTD: 9A, 700V N-CHANNEL Power MosfetJoshi Joseph JoyNo ratings yet
- Physical Science SHS Lesson 14.4 Models of The UniverseDocument23 pagesPhysical Science SHS Lesson 14.4 Models of The UniverseJoy DolorosaNo ratings yet
- CMC Chapter 03Document59 pagesCMC Chapter 03api-294176229No ratings yet
- D & E - Module 4Document43 pagesD & E - Module 4vivekNo ratings yet
- Notes & Notes: Biostatistics & EBMDocument35 pagesNotes & Notes: Biostatistics & EBMamhhospital0No ratings yet
- HIC SEA IV - Delegate ProspectusDocument12 pagesHIC SEA IV - Delegate ProspectusNguyễn Hồng PhượngNo ratings yet
- Angl 5Document24 pagesAngl 5Latika ChoudhuryNo ratings yet
- SYM Starter U04 OSEWorksheetDocument4 pagesSYM Starter U04 OSEWorksheetCarolinaNo ratings yet
- Spring 2018 Graduate Course Descriptions - 0Document25 pagesSpring 2018 Graduate Course Descriptions - 0IvanNo ratings yet
- Book Report Project GuidelinesDocument2 pagesBook Report Project GuidelinesArmando Jose Medina MirandaNo ratings yet
- Energy Tech - 2016 - WesterhoffDocument11 pagesEnergy Tech - 2016 - WesterhoffMario CastilloNo ratings yet
- Journal of Pharmaceutical Sciences: Naseem Ahmad Charoo, Mark Durivage, Ziyaur Rahman, Mohamad Haitham AyadDocument6 pagesJournal of Pharmaceutical Sciences: Naseem Ahmad Charoo, Mark Durivage, Ziyaur Rahman, Mohamad Haitham Ayadmehrdarou.qaNo ratings yet
- Daily Lesson PlanDocument15 pagesDaily Lesson PlanNur MaizanNo ratings yet
- Entrepreneurship Development Test 2 Assessment SheetDocument7 pagesEntrepreneurship Development Test 2 Assessment SheetHaseeb ShaikhNo ratings yet
- The Cement Industry in EthiopiaDocument7 pagesThe Cement Industry in EthiopiaTesfaye Azanie1No ratings yet
- Causes of Decay of BuildingsDocument20 pagesCauses of Decay of Buildingsthrigya myakalaNo ratings yet
- Iso 3745 2012 en PDFDocument11 pagesIso 3745 2012 en PDFMARIO ALBERTO MANILLA CORDOBANo ratings yet
- Shormista AssignmentDocument31 pagesShormista AssignmentSwakshar DebNo ratings yet
- 3QGB Screw PumpDocument7 pages3QGB Screw PumpWily WayerNo ratings yet