Professional Documents
Culture Documents
E Com
Uploaded by
PRIT KHOKHANI0 ratings0% found this document useful (0 votes)
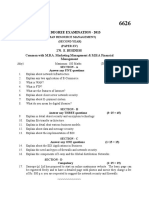
3 views1 pageE-commerce involves listing applications and frameworks, with advantages and limitations of both e-commerce and m-commerce addressed. Components of infrastructure like firewalls, HTTPS, and transaction models are discussed alongside cybersecurity threats including DOS attacks, SQL injection, email fraud, and cyber crimes. The close relationship between e-commerce and cybersecurity is also noted.
Original Description:
Original Title
E-com (1)
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentE-commerce involves listing applications and frameworks, with advantages and limitations of both e-commerce and m-commerce addressed. Components of infrastructure like firewalls, HTTPS, and transaction models are discussed alongside cybersecurity threats including DOS attacks, SQL injection, email fraud, and cyber crimes. The close relationship between e-commerce and cybersecurity is also noted.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
3 views1 pageE Com
Uploaded by
PRIT KHOKHANIE-commerce involves listing applications and frameworks, with advantages and limitations of both e-commerce and m-commerce addressed. Components of infrastructure like firewalls, HTTPS, and transaction models are discussed alongside cybersecurity threats including DOS attacks, SQL injection, email fraud, and cyber crimes. The close relationship between e-commerce and cybersecurity is also noted.
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 1
- E-commerce
- List out appliction
- m-Commerce advantage disadvantage:-
- Write a note on E-commerce architectural framework
commerce architectural framework
- List aims and limitations of E-commerce.
- E com Characteristics (features):
- Firewall of working
- Firewall of type
- Hypertext Transfer Protocol Secure (HTTPS)
- Banking-related crimes
- Email related crime explain in detail
- Explain DOS attack in detail
- "EFT"
- Explain component of i- way with example in detail.
- *Types of SQL Injection:*
- A transaction model
- the advantages and disadvantages of e-commerce:
- E-commerce and cybersecurity are closely intertwined,
- Viruses, worms, and Trojans
- Define cyber smearing , cyber-squatting and cyber
terrorism, data diddling.
- Whatis e- mail fraud ? Explain various forms of email fraud.
You might also like
- EcomimpDocument2 pagesEcomimpAkhil HiraniNo ratings yet
- UntitledDocument1 pageUntitledKrushit NadodaNo ratings yet
- It5 Ecom Dec07Document1 pageIt5 Ecom Dec07Tarun Kumar SahniNo ratings yet
- Pool of The Most Important Qns E CommerceDocument1 pagePool of The Most Important Qns E CommerceHRITIK YADAVNo ratings yet
- Unit Wise Important Important QuestionsDocument1 pageUnit Wise Important Important Questionsniranjanaezhumalai2003No ratings yet
- E-Commerce Questions: Important NoteDocument5 pagesE-Commerce Questions: Important NotebharatnarayananNo ratings yet
- E CommerceDocument3 pagesE CommerceTarun BambhaniyaNo ratings yet
- E-Commerce &web Desigining Sem - 2Document69 pagesE-Commerce &web Desigining Sem - 2sherlockNo ratings yet
- EitDocument1 pageEitgoyalsb2682No ratings yet
- E-Commerce Questions and Answers: What Are The Different Types of E-Marketplaces?Document2 pagesE-Commerce Questions and Answers: What Are The Different Types of E-Marketplaces?GangadharNo ratings yet
- Ecommerce Course OutlineDocument3 pagesEcommerce Course OutlineFaheem AliNo ratings yet
- Assignment 1: E-Commerece Strategic IT Management Cse 7 SemDocument1 pageAssignment 1: E-Commerece Strategic IT Management Cse 7 SemMohallalibrary NgoNo ratings yet
- Computers FaqDocument4 pagesComputers Faqrohit kanojiaNo ratings yet
- E - Commerce and IWTDocument4 pagesE - Commerce and IWTziddirazanNo ratings yet
- Kajal Goud 5 Sybbi Information TechnologyDocument8 pagesKajal Goud 5 Sybbi Information TechnologyKajal GoudNo ratings yet
- Course Outline Subject: Electronic Commerce Course ObjectivesDocument3 pagesCourse Outline Subject: Electronic Commerce Course ObjectivesAwais AfzalNo ratings yet
- C - Commerce Concepts Models Strategies C.S.V. MurthyDocument9 pagesC - Commerce Concepts Models Strategies C.S.V. MurthySulbha Gath100% (2)
- Data Protection TechniquesDocument4 pagesData Protection Techniquesgayathri777No ratings yet
- E-Commerce - IT430 Handouts - RemovedDocument92 pagesE-Commerce - IT430 Handouts - Removedshahbaz shahidNo ratings yet
- Erepublik - Security Explained, Catching Bots and ScriptersDocument6 pagesErepublik - Security Explained, Catching Bots and Scriptersskydesign04No ratings yet
- E-Commerce SyllabusDocument2 pagesE-Commerce SyllabushenaNo ratings yet
- KU Question Bank E-Commerce - 2018Document3 pagesKU Question Bank E-Commerce - 2018Ehhan SinghaniagoldNo ratings yet
- Eccomerce RevisionDocument25 pagesEccomerce RevisionJoshua MercyNo ratings yet
- Assignment Mba Ii Semester 51204-E: Business FundamentalsDocument2 pagesAssignment Mba Ii Semester 51204-E: Business Fundamentalsanandilal dhabaiNo ratings yet
- Important Ques For BT205 and Assignment Ques SetDocument2 pagesImportant Ques For BT205 and Assignment Ques Setkps vlogsNo ratings yet
- Btech It Ecommerce ReportDocument11 pagesBtech It Ecommerce Reportdishant_kapadiaNo ratings yet
- IT430 E CommerceDocument187 pagesIT430 E Commerceapi-3829708No ratings yet
- CNS Question BankDocument2 pagesCNS Question BankSumita Barun kumarNo ratings yet
- Security and Ethics: Section 1Document9 pagesSecurity and Ethics: Section 1alvaroNo ratings yet
- E Commerce SyllabusDocument1 pageE Commerce SyllabusBHAVANI REDDYNo ratings yet
- Ecom 1stDocument1 pageEcom 1stSphinx PoesyNo ratings yet
- IT430 Handouts 1 45Document187 pagesIT430 Handouts 1 45usmanNo ratings yet
- Cyber Security: Table of ContentsDocument75 pagesCyber Security: Table of ContentsayushNo ratings yet
- E-Comerce Course OutlineDocument2 pagesE-Comerce Course OutlineAmar EliasNo ratings yet
- BBA 1155 E - Commerce and Internet LPC 5 0 5: Unit IDocument2 pagesBBA 1155 E - Commerce and Internet LPC 5 0 5: Unit IjacobjabsNo ratings yet
- Assignment of E-CommerceDocument1 pageAssignment of E-Commerceapi-26339138No ratings yet
- CEHDocument6 pagesCEHmela4ever125No ratings yet
- India's Mega Online Education Hub For Class 9-12 Students, Engineers, Managers, Lawyers and DoctorsDocument41 pagesIndia's Mega Online Education Hub For Class 9-12 Students, Engineers, Managers, Lawyers and DoctorsDivyashree100% (5)
- Secure Internet Banking With Visual Authentication Protocol: Saraswathi. R, Shanmathi. G, Preethi. P, Arul. UDocument3 pagesSecure Internet Banking With Visual Authentication Protocol: Saraswathi. R, Shanmathi. G, Preethi. P, Arul. UInternational Journal of Scientific Research in Science, Engineering and Technology ( IJSRSET )No ratings yet
- Internship SyllabusDocument3 pagesInternship Syllabusbooks123No ratings yet
- E-Commerce: Pondicherry UniversityDocument259 pagesE-Commerce: Pondicherry UniversitySuman Naveen JaiswalNo ratings yet
- E-Commerce Essentials: B2B C2BDocument6 pagesE-Commerce Essentials: B2B C2BtanhaitanhaNo ratings yet
- M. B.A. Degree Examination - 2013: 270. E. Business Common With M.B.A. Marketing Management & M.B.A Financial ManagementDocument1 pageM. B.A. Degree Examination - 2013: 270. E. Business Common With M.B.A. Marketing Management & M.B.A Financial ManagementRavi KrishnanNo ratings yet
- E - Commerce-CroppedDocument222 pagesE - Commerce-CroppedZeeshan ShaikhNo ratings yet
- VI Branch: Information Internet and Web TechnologiesDocument3 pagesVI Branch: Information Internet and Web Technologieshimanshu masihNo ratings yet
- Section - A: Objective QuestionsDocument1 pageSection - A: Objective QuestionsNeeraj GautamNo ratings yet
- E-Commerce Questions BankDocument19 pagesE-Commerce Questions BankJasmeet KaurNo ratings yet
- E-Commerce Questions BankDocument19 pagesE-Commerce Questions BankSambasiva Rao100% (1)
- Task 4 - Report of The Security IssuesDocument5 pagesTask 4 - Report of The Security IssuesNic TanNo ratings yet
- Final Ecomers AssigmentDocument16 pagesFinal Ecomers Assigmentnana fosuNo ratings yet
- 01 05 Emerging Technology in E-BusinessDocument13 pages01 05 Emerging Technology in E-BusinessSweeto SaniNo ratings yet
- 401 Eb Q-ADocument3 pages401 Eb Q-AMd. Wahid Abdul HoqueNo ratings yet
- E Commerce Question BankDocument13 pagesE Commerce Question BankManoj Kudur0% (1)
- 249 P16mce4a 2020052110051862Document75 pages249 P16mce4a 2020052110051862shanmugamsundaram6380No ratings yet
- Hacking : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Ethical HackingFrom EverandHacking : The Ultimate Comprehensive Step-By-Step Guide to the Basics of Ethical HackingRating: 5 out of 5 stars5/5 (3)
- Securing Application Deployment with Obfuscation and Code Signing: How to Create 3 Layers of Protection for .NET Release BuildFrom EverandSecuring Application Deployment with Obfuscation and Code Signing: How to Create 3 Layers of Protection for .NET Release BuildNo ratings yet
- Securing .NET Web Services with SSL: How to Protect “Data in Transit” between Client and Remote ServerFrom EverandSecuring .NET Web Services with SSL: How to Protect “Data in Transit” between Client and Remote ServerNo ratings yet