Professional Documents
Culture Documents
Cybercrime
Uploaded by
James Ronald VetonioCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Cybercrime
Uploaded by
James Ronald VetonioCopyright:
Available Formats
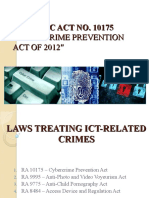
Cybercrime offense under (RA ACT 10175)
“Cybercrime Prevention Act of 2012”
Categories of Cybercrime:
1. Crimes against CIA (Confidentiality, Integrity and Availability)
2. Computer Related Offenses
3. Content Related Offenses
4. Other Cybercrime Offenses
Crimes against CIA:
A. Illegal Access- the unauthorized access to the whole or any part of a computer
- access of any application without right.
A. Illegal Interception – the interception by technical means without any NON-public transmission of computer data
to from or within a computer system
- unauthorized intercepting of a non-public communication
“Man-in-the middle attack (MITM) the one who eavesdrop the communication between the sender and receiver.
B. Data Interference – the intentional or reckless alteration, damaging deletion or deterioration of computer data.
Electronic documents or electronic data message without right.
- including the introduction of transmission of viruses.
- tampering of data intentionally or recklessly.
C. System Interference – the intentional alteration or reckless, hindering or interference with the functioning of a
computer or computer network by: inputting, transmitting, damaging, deleting or deteriorating.
- altering or suppressing computer data or program electronic document or electronic data without right or authority.
DOS- one source only
DDos: Distribution Denial of service attack.
- A cyber-attack a specific server or network. PURPOSE: to disrupt a normal operation
D. Misuse of Device- it is the use, production, sale, procurement, importation and distribution of a device including
computer programs for the purpose of committing offenses specified in this act.
“Includes computer passwords, access code any similar Data.”
A. Computer Related Forgery:
The unauthorized input, alteration deletion of any computer data without resulting in inauthentic data, with the intent that
be acted upon for the purpose to appear authentic.
B. Computer- Related Fraud- the unauthorized input, alteration, deletion of any computer data or program
interference in the functioning of a computer system, causing damage. PURPOSE: perpetuate fraud (with fraudulent
intent)
C. Computer Related Identity theft- the intentional acquisition, use, misuses, transfer, possess, alteration or
deletion of identifying information belonging to another.
Content Related Offenses:
A. Cybersex- the willful engagement, maintenance, control or operation (directly or indirectly) of any lascivious
exhibition of sexual organ or sexual activity with the aid of a computer system, for favor or consideration. Also known as
“INTERACTIVE PROSTITUTION”
B. Child Pornography- the unlawful or prohibited acts defined and punishable by RA 9775 (Anti-child
Pornography act of 2009) committed through computer system: PROVIDED: Penalty to be imposed shall be 1 degree
higher that that provided for the said law.
C. Unsolicited Commercial Communication – the transmission of commercial electronic communication with the
use of computer system which seeks to: advertise, sell, or offer for sale of products and services. Also known as “SPAMS”
Other CC Offenses
A. Aiding or Abetting in the Commission of the Cybercrime.
- any person who willfully abets or aids the commission of any of the offenses enumerated in this act shall be held liable.
B. Attempt to the Commission of Cybercrime
- any person who willfully attempts to commit any of the offenses enumerated in this Act shall be held Liable.
Nigerian SCAM- also known as advance fee fraud or 419. The Nigerian Prince scam is a phishing attack when swindlers
reach out to potential victims and promise a large sum of money in return for some help.
You might also like
- BAGUHIN Cyber EnvironmentDocument171 pagesBAGUHIN Cyber EnvironmentDonita BernardinoNo ratings yet
- Cybercrime Prevention ActDocument16 pagesCybercrime Prevention Actalamat888No ratings yet
- Ra 10175Document39 pagesRa 10175LYLE DALE AVANCENo ratings yet
- CybercrimeDocument6 pagesCybercrimeLEIGHANNE ZYRIL SANTOSNo ratings yet
- Primer On Cybercrimes Under The Cybercrime Prevention Act of 2012Document5 pagesPrimer On Cybercrimes Under The Cybercrime Prevention Act of 2012Audrey Kristina MaypaNo ratings yet
- NOTESDocument13 pagesNOTESJan Jireh SueloNo ratings yet
- Cyber-Bullying: Republic Act No. 10175Document41 pagesCyber-Bullying: Republic Act No. 10175Lord William PacuribNo ratings yet
- Lesson 1 Intro To CybercrimeDocument6 pagesLesson 1 Intro To CybercrimeJerico N. loberianoNo ratings yet
- Cybercrimes Under The Cybercrime Prevention Act of 2012Document6 pagesCybercrimes Under The Cybercrime Prevention Act of 2012Crislene CruzNo ratings yet
- Cybercrime OffensesDocument3 pagesCybercrime OffensesJanille Tomajin-CapinpinNo ratings yet
- CybercrimeDocument6 pagesCybercrimeAya PaneloNo ratings yet
- Introduction To CybercrimeDocument9 pagesIntroduction To CybercrimeReyes SonnyNo ratings yet
- CyberCrime Prevention ActDocument3 pagesCyberCrime Prevention ActBrian Almeria100% (1)
- Cybercrime GRP4Document18 pagesCybercrime GRP4colord639No ratings yet
- Cybercrime Laws 1Document7 pagesCybercrime Laws 1Anime AddictNo ratings yet
- Crim Law 2Document5 pagesCrim Law 2LJ RamirezNo ratings yet
- Electronic CrimeDocument110 pagesElectronic CrimeClyde Louis Oliver-LinagNo ratings yet
- Report Add DataDocument2 pagesReport Add DataLlylynn MendozaNo ratings yet
- Cybercrime and Environmental Protection and LawsDocument86 pagesCybercrime and Environmental Protection and Lawspaolovarias7No ratings yet
- Punishable Acts Section 4. Cybercrime OffensesDocument3 pagesPunishable Acts Section 4. Cybercrime OffensesTwinkle MempinNo ratings yet
- Cybercrime LawDocument32 pagesCybercrime LawRomel AtanacioNo ratings yet
- Republic Act No. 10175 An Act Defining Cybercrime, Providing For The Prevention, Investigation, Suppression and The Imposition of Penalties Therefor and For Other PurposesDocument2 pagesRepublic Act No. 10175 An Act Defining Cybercrime, Providing For The Prevention, Investigation, Suppression and The Imposition of Penalties Therefor and For Other PurposesElla Dela CernaNo ratings yet
- Cybercrime: By: Nikko Jay E. PavericioDocument16 pagesCybercrime: By: Nikko Jay E. PavericioJpAguirreNo ratings yet
- Beige White Aesthetic Vintage Scrapbook Group Project PresentationDocument66 pagesBeige White Aesthetic Vintage Scrapbook Group Project PresentationbadangayonmgbNo ratings yet
- What Is Cyber CrimeDocument3 pagesWhat Is Cyber CrimeJackson DavidNo ratings yet
- Media and Information LanguageDocument19 pagesMedia and Information LanguageFahad HADJI USOPHNo ratings yet
- Cybercrimes Under The Cybercrime Prevention Act of 2012 (RA 10175) OCRDocument4 pagesCybercrimes Under The Cybercrime Prevention Act of 2012 (RA 10175) OCRsigillus.primusNo ratings yet
- Presentation + - RA 10175Document47 pagesPresentation + - RA 10175Bravo Matalasik83% (6)
- Cybercrime Prevention Act of 2012Document47 pagesCybercrime Prevention Act of 2012John Dale UmaliNo ratings yet
- Cyber LawsDocument37 pagesCyber LawsAL BE RTNo ratings yet
- Health Related LawsDocument38 pagesHealth Related LawspeanutNo ratings yet
- MERILYNDocument3 pagesMERILYNKathryn Ann Garro FlorentinoNo ratings yet
- 06 RA 10175 Cybercrime LawDocument12 pages06 RA 10175 Cybercrime LawJustin John AmorosoNo ratings yet
- RA10175Document5 pagesRA10175Roger GAMINGNo ratings yet
- January 13 - Pros. Landicho (Cybercrime Act of 2012)Document102 pagesJanuary 13 - Pros. Landicho (Cybercrime Act of 2012)Abraham S. OlegarioNo ratings yet
- Chapter 10 UpdatedDocument47 pagesChapter 10 UpdatedsnoppyfromytNo ratings yet
- Cybercrime OffensesDocument20 pagesCybercrime Offensescamille capalacNo ratings yet
- Republic Act No. 10175: "Cybercrime Prevention Act of 2012Document48 pagesRepublic Act No. 10175: "Cybercrime Prevention Act of 2012Ronel Genoves Y BarreraNo ratings yet
- Introduction To Cybercrime and Environmental Laws and ProtectionDocument10 pagesIntroduction To Cybercrime and Environmental Laws and ProtectionNikki Dela TorreNo ratings yet
- Midterm Topic Cdi 107nDocument9 pagesMidterm Topic Cdi 107njaspermonreal2001No ratings yet
- Weeks 4 5Document11 pagesWeeks 4 5CM Soriano TalamayanNo ratings yet
- Health 10Document10 pagesHealth 10kukuhpaigeNo ratings yet
- Republic of The Philippines R.A 10175Document13 pagesRepublic of The Philippines R.A 10175Al FernandezNo ratings yet
- Cybercrime Prevention ACT OF 2012 (R.A. 10175) : Reported byDocument18 pagesCybercrime Prevention ACT OF 2012 (R.A. 10175) : Reported byMadz Rj MangorobongNo ratings yet
- Be It Enacted by The Senate and House of Representatives of The Philippines in Congress AssembledDocument14 pagesBe It Enacted by The Senate and House of Representatives of The Philippines in Congress AssembledNonoy D VolosoNo ratings yet
- Cybercrime Law: Republic Act No. 10175Document22 pagesCybercrime Law: Republic Act No. 10175Jastine AnneNo ratings yet
- ABES. Comm 106 9.1Document4 pagesABES. Comm 106 9.1Medeah Faye AbesNo ratings yet
- CybercrimeDocument3 pagesCybercrimeJastine AnneNo ratings yet
- Performance Task 1Document5 pagesPerformance Task 1Johana MiraflorNo ratings yet
- Assignment No. 2Document3 pagesAssignment No. 2Niña Rica PunzalanNo ratings yet
- Republic Act No Cyber CrimeDocument10 pagesRepublic Act No Cyber CrimeGlorious El DomineNo ratings yet
- Q&A Cybercrime Prevention ActDocument3 pagesQ&A Cybercrime Prevention ActRafael Juico100% (2)
- Documents On SomethingDocument2 pagesDocuments On SomethingSophia AndreaNo ratings yet
- Types of Cybercrimes: 1. Illegal Access 2. Illegal InterceptionDocument3 pagesTypes of Cybercrimes: 1. Illegal Access 2. Illegal InterceptionKel GuzmanNo ratings yet
- Cybercrime LawDocument12 pagesCybercrime Lawprincess twilightNo ratings yet
- Module 8 IT 101Document20 pagesModule 8 IT 101leaadel92No ratings yet
- Is - This Information May Be in The Form of Text Documents, Images, Audio ClipsDocument7 pagesIs - This Information May Be in The Form of Text Documents, Images, Audio ClipsDonita BernardinoNo ratings yet
- CybercrimeDocument2 pagesCybercrimeJong CruzNo ratings yet
- Penetration Testing Methodology: (Company Name)Document6 pagesPenetration Testing Methodology: (Company Name)Sky WalkerNo ratings yet
- CPENT BrochureDocument13 pagesCPENT Brochurenoayran120No ratings yet
- Ghsa 5Document2 pagesGhsa 5danishark777No ratings yet
- Trackdart - Tracking Details: Sign inDocument1 pageTrackdart - Tracking Details: Sign inThulasi RamanNo ratings yet
- Question: Wet Catalyst Pellets Having A Diameter of 12.7 MM Are Being DriDocument1 pageQuestion: Wet Catalyst Pellets Having A Diameter of 12.7 MM Are Being DriPrabhasha JayasundaraNo ratings yet
- Pertinax Solutions CorporateDocument20 pagesPertinax Solutions CorporateMalikNo ratings yet
- English Language and The New MediaDocument2 pagesEnglish Language and The New MediaKrissa Jean KingNo ratings yet
- LT1242X - 1 Alarm LogDocument10 pagesLT1242X - 1 Alarm LogSudipta Das0% (1)
- Sharmila Krishnappa ResumeDocument2 pagesSharmila Krishnappa ResumeKaranMPaiNo ratings yet
- MJJ Query ASPNETDocument186 pagesMJJ Query ASPNETMichelle JonesNo ratings yet
- E-Tech Module True (Repaired)Document197 pagesE-Tech Module True (Repaired)Ma'am Digs VlogNo ratings yet
- Lesson 3 Contextualize Online ResearchDocument43 pagesLesson 3 Contextualize Online ResearchFeitz LesterNo ratings yet
- Product - INTERNET LEASE LINESDocument9 pagesProduct - INTERNET LEASE LINESforexpeindiaNo ratings yet
- Cradle Point CTR35 DatasheetDocument2 pagesCradle Point CTR35 DatasheetHunterNo ratings yet
- Norman Brandinger-HA With OpenSIPSDocument41 pagesNorman Brandinger-HA With OpenSIPSdragelecNo ratings yet
- CryptographyDocument23 pagesCryptographyLady BugNo ratings yet
- B1 - Elon Musk On Metaverse and Web3Document3 pagesB1 - Elon Musk On Metaverse and Web3Florencia SanseauNo ratings yet
- LABSEC-1010 Configuration of SSL Inspection/ Decryption On Cisco Firepower TechnologyDocument15 pagesLABSEC-1010 Configuration of SSL Inspection/ Decryption On Cisco Firepower TechnologyФуад МустафаевNo ratings yet
- 1.2 FPX - Guide - AFFINHWANGDocument3 pages1.2 FPX - Guide - AFFINHWANGpang syNo ratings yet
- Security Digital Certificate ManagerDocument96 pagesSecurity Digital Certificate Managertesttest testNo ratings yet
- (March-2021) Latest Braindump2go 312-50v11 PDF Dumps and 312-50v11 VCE Dumps (906-945)Document11 pages(March-2021) Latest Braindump2go 312-50v11 PDF Dumps and 312-50v11 VCE Dumps (906-945)Lê Huyền MyNo ratings yet
- Notes On Privacy, Control and LawDocument9 pagesNotes On Privacy, Control and LawMichelleneChenTadleNo ratings yet
- ABAP Development - Displaying A DMS PDF Document..in WDDocument3 pagesABAP Development - Displaying A DMS PDF Document..in WDage0110100% (1)
- DHCP QuestionsDocument5 pagesDHCP QuestionsCarlos CabezasNo ratings yet
- Coupa EDI Connection InformationDocument4 pagesCoupa EDI Connection InformationRaviNo ratings yet
- IRM 7 Windows Malware DetectionDocument2 pagesIRM 7 Windows Malware DetectionbogneNo ratings yet
- 2 DayDocument24 pages2 DayMohammed Ibrahim AdogaNo ratings yet
- Day 20 - Programmatic Email and Affiliate - Day 20Document49 pagesDay 20 - Programmatic Email and Affiliate - Day 20Aarti IyerNo ratings yet
- Cybersecurity Survival GuideDocument355 pagesCybersecurity Survival GuideWai Yan PhyoeNo ratings yet
- Fingerprint Access Standalone User's Manual V1.1.2Document31 pagesFingerprint Access Standalone User's Manual V1.1.2Miguel AlcivarNo ratings yet