Professional Documents
Culture Documents
4 Test4 Review - S
4 Test4 Review - S
Uploaded by
muhammadbinsafdar555Original Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
4 Test4 Review - S
4 Test4 Review - S
Uploaded by
muhammadbinsafdar555Copyright:
Available Formats
1
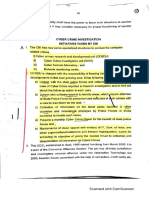
Pakistan International School Jeddah - English Section
Computer Science (0478)
Test 4 Review Sheet– Y9-____ Total Marks: Obtained Marks:
Name: Student ID: Date:
Y9
Computer science 0478
Test4 Review Sheet
Time allowed: 40 min
Note: Calculator is not allowed.
Y9-CS-2023-24-Test4 Review Sheet
2
1.
Y9-CS-2023-24-Test4 Review Sheet
3
2.
Y9-CS-2023-24-Test4 Review Sheet
4
Y9-CS-2023-24-Test4 Review Sheet
5
3.
Y9-CS-2023-24-Test4 Review Sheet
6
Y9-CS-2023-24-Test4 Review Sheet
7
5.
Y9-CS-2023-24-Test4 Review Sheet
8
Y9-CS-2023-24-Test4 Review Sheet
9
6.
Y9-CS-2023-24-Test4 Review Sheet
10
7.
Y9-CS-2023-24-Test4 Review Sheet
11
8.
Y9-CS-2023-24-Test4 Review Sheet
12
9.
Y9-CS-2023-24-Test4 Review Sheet
13
Y9-CS-2023-24-Test4 Review Sheet
14
10.
Study the flowchart.
Y9-CS-2023-24-Test4 Review Sheet
15
11.
Y9-CS-2023-24-Test4 Review Sheet
16
12.
Y9-CS-2023-24-Test4 Review Sheet
17
Y9-CS-2023-24-Test4 Review Sheet
18
13.
Y9-CS-2023-24-Test4 Review Sheet
19
14.
Y9-CS-2023-24-Test4 Review Sheet
20
Y9-CS-2023-24-Test4 Review Sheet
21
15. Fill in the blank with the words given below. One word can be used more than once.
private key public network Asymmetric encryption same key
encryption Symmetric encryption public key eavesdropper
intercepted
When data is transmitted over any ………………………………………… (wired or wireless), there is
always a risk of it being intercepted by, for example, a hacker. Under these circumstances, a hacker
is often referred to as an ………………………………………… Using
………………………………………… helps to minimise this risk.
………………………………………… alters data into a form that is unreadable by anybody for whom
the data is not intended. It cannot prevent the data being …………………………………………, but it
stops it from making any sense to the eavesdropper. This is particularly important if the data is
sensitive or confidential (for example, credit card/bank details, medical history or legal documents).
………………………………………… uses an encryption key; the
…………………………………………is used to encrypt and decrypt the encoded message. First of all,
consider a simple system that uses a 10-digit denary encryption key (this gives 1 × 1010 possible
codes); and a decryption key.
………………………………………… was developed to overcome the security problems associated
with symmetric encryption. It makes use of two keys called the
…………………………………………and the ………………………………………….
Y9-CS-2023-24-Test4 Review Sheet
You might also like
- Pile Design and Construction Rules of ThumbFrom EverandPile Design and Construction Rules of ThumbRating: 4.5 out of 5 stars4.5/5 (15)
- MTS-5800 User Manual Ethernet Testing enDocument378 pagesMTS-5800 User Manual Ethernet Testing enbartee000100% (3)
- Machine Design Elements and AssembliesFrom EverandMachine Design Elements and AssembliesRating: 3.5 out of 5 stars3.5/5 (2)
- Asme N 511 2007Document49 pagesAsme N 511 2007monsepack100% (1)
- IE202 Fall2020 SS2Document5 pagesIE202 Fall2020 SS2HandeeorNo ratings yet
- 3DG-P45-00001 (Pipe Stress Analysis 190)Document33 pages3DG-P45-00001 (Pipe Stress Analysis 190)Ali Metin100% (1)
- Testing of High Voltage Cable SystemsDocument28 pagesTesting of High Voltage Cable SystemsGualadrake100% (2)
- Cisco Sdwan Design GuideDocument102 pagesCisco Sdwan Design GuideSheik ShareefNo ratings yet
- (NIST Technical Note 1665) DongHun Yeo - Database-Assisted Design for Wind_ Concepts, Software, and Example for High-Rise Reinforced Concrete Structures-National Institute of Standards and Technology .pdfDocument87 pages(NIST Technical Note 1665) DongHun Yeo - Database-Assisted Design for Wind_ Concepts, Software, and Example for High-Rise Reinforced Concrete Structures-National Institute of Standards and Technology .pdfGovind GauravNo ratings yet
- Prediction of Warship Manoeuvring CoefficientsDocument76 pagesPrediction of Warship Manoeuvring Coefficientsa aNo ratings yet
- Composite GirdersDocument268 pagesComposite GirdersdeathesNo ratings yet
- CEM513 Productivity Study OnDocument46 pagesCEM513 Productivity Study OnHector MejiaNo ratings yet
- Calculation of Contact StressDocument23 pagesCalculation of Contact StressDaniel Popa100% (1)
- Solar Photovoltaic IV Curve TracerDocument71 pagesSolar Photovoltaic IV Curve TracerHữu Tuấn LêNo ratings yet
- Ar95 109Document133 pagesAr95 109Shashank ChNo ratings yet
- Topographic SurveyingDocument111 pagesTopographic SurveyingAhmet DerdiyokNo ratings yet
- LCM500 Leakage Current Monitor: User GuideDocument74 pagesLCM500 Leakage Current Monitor: User GuideThien Nguyen VanNo ratings yet
- Doble LCM 500 ManualDocument122 pagesDoble LCM 500 Manualarytri farismansyahNo ratings yet
- ME 189 Project List 2014-15 - 9-30-14 PDFDocument53 pagesME 189 Project List 2014-15 - 9-30-14 PDFGenie MecaNo ratings yet
- Backfill For Subsurface StructuresDocument61 pagesBackfill For Subsurface StructureskkkelvinNo ratings yet
- TDocument280 pagesTPeggy GreenNo ratings yet
- CIH Equation SheetsDocument8 pagesCIH Equation SheetsfrancisNo ratings yet
- Math 2240 Final Exam 2010Document6 pagesMath 2240 Final Exam 2010Karl ToddNo ratings yet
- 22046564r003 - 5800 - MSAM - 40-100G Ethernet TestingDocument460 pages22046564r003 - 5800 - MSAM - 40-100G Ethernet TestingCleber Rodrigues100% (1)
- Ground Anchor SystemsDocument76 pagesGround Anchor Systemspatricklim1982100% (4)
- Hif 12020Document48 pagesHif 12020நந்த_குமார்No ratings yet
- High Capacity Concrete Anchor SystemsDocument52 pagesHigh Capacity Concrete Anchor SystemsVANo ratings yet
- EM 1110-2-1911 (Construction Control For Earth and Rock-Fill Dams)Document100 pagesEM 1110-2-1911 (Construction Control For Earth and Rock-Fill Dams)SiPp.TNo ratings yet
- Naca 4415Document152 pagesNaca 4415cesamavNo ratings yet
- User's Guide: Computer Program For Analysis of Beam-ColumnDocument113 pagesUser's Guide: Computer Program For Analysis of Beam-ColumnjeanecefNo ratings yet
- Foundation - Impact Testing MCDocument26 pagesFoundation - Impact Testing MCsidhesh87No ratings yet
- Manual For Design & Construction Monitoring of Soil Nail WallsDocument45 pagesManual For Design & Construction Monitoring of Soil Nail Wallsmohmisa100% (1)
- High Capacity Concrete AnchorsDocument52 pagesHigh Capacity Concrete AnchorsvictorrbgNo ratings yet
- IMS Test Availability Schedule - CAT - Ims IndiaDocument6 pagesIMS Test Availability Schedule - CAT - Ims IndiaSumit KumarNo ratings yet
- Advance Design Validation Guide 2023 Volume IVDocument849 pagesAdvance Design Validation Guide 2023 Volume IVkeffy_bfk100% (1)
- Earthling System Electrical and Instruments Test ProcedureDocument23 pagesEarthling System Electrical and Instruments Test ProcedurejavadNo ratings yet
- Military Standard: MI14TD-105O 29Document68 pagesMilitary Standard: MI14TD-105O 29gumieljNo ratings yet
- High-Temperature Material Lattice Combining Low Thermal Expansion, High Stiffness and StrengthDocument45 pagesHigh-Temperature Material Lattice Combining Low Thermal Expansion, High Stiffness and Strengthsohanlal29No ratings yet
- TM 1-1500-328-23Document98 pagesTM 1-1500-328-23homer314No ratings yet
- Mooring Integrity Le Beon Manufacturing Dot 2014-79Document22 pagesMooring Integrity Le Beon Manufacturing Dot 2014-79Matthew BanksNo ratings yet
- HEC-5 UsersManual (CPD-5)Document380 pagesHEC-5 UsersManual (CPD-5)Arabelle Clarice RoxasNo ratings yet
- TransPort PT878GC Portable Gas Ultrasonic Flowmeter 910 229B1Document307 pagesTransPort PT878GC Portable Gas Ultrasonic Flowmeter 910 229B1ÁlvaroAnabalónSalamancaNo ratings yet
- 687 - 10092 SoftDocument35 pages687 - 10092 SoftMREFAATNo ratings yet
- SpecSys6 Base FEA ReportDocument3 pagesSpecSys6 Base FEA ReportnikolaiffbNo ratings yet
- Mil HDBK 299Document188 pagesMil HDBK 299jim100% (1)
- Em - 1110 2 1911Document101 pagesEm - 1110 2 1911ujosec6138No ratings yet
- Antwi 10781220Document122 pagesAntwi 10781220Yasser MehNo ratings yet
- Report No.: CG-D-O5-94Document62 pagesReport No.: CG-D-O5-94Tolga SağinNo ratings yet
- CFD Study of Thick Flatback Airfoils Using OpenFOAMDocument172 pagesCFD Study of Thick Flatback Airfoils Using OpenFOAMMason925No ratings yet
- 22046564r015 EthernetTestingGuide PDFDocument632 pages22046564r015 EthernetTestingGuide PDFFaisal KarimNo ratings yet
- Development of Autonomous Unmanned Aerial Vehicle Research Platform - Modeling Simulating and Flight TestingDocument202 pagesDevelopment of Autonomous Unmanned Aerial Vehicle Research Platform - Modeling Simulating and Flight TestingFabio CardosoNo ratings yet
- Drag Predictions For Projectiles...Document49 pagesDrag Predictions For Projectiles...MoltKeeNo ratings yet
- Ms Common WorkDocument25 pagesMs Common WorkSahabzada AamirNo ratings yet
- GLASSDocument56 pagesGLASSAris OlimpoNo ratings yet
- Economic and Financial Modelling with EViews: A Guide for Students and ProfessionalsFrom EverandEconomic and Financial Modelling with EViews: A Guide for Students and ProfessionalsNo ratings yet
- Fibonacci and Gann Applications in Financial Markets: Practical Applications of Natural and Synthetic Ratios in Technical AnalysisFrom EverandFibonacci and Gann Applications in Financial Markets: Practical Applications of Natural and Synthetic Ratios in Technical AnalysisRating: 5 out of 5 stars5/5 (2)
- Intel SSD DCT 3 0 X User GuideDocument73 pagesIntel SSD DCT 3 0 X User GuideIman Teguh PNo ratings yet
- Introduction To Sitecore 9 Architecture and Scaling v2Document47 pagesIntroduction To Sitecore 9 Architecture and Scaling v2Kiran PatilNo ratings yet
- Structures: Fahad Majeed UET TaxilaDocument23 pagesStructures: Fahad Majeed UET TaxilaUmer KhanNo ratings yet
- What Are The Requirements of The ATMDocument2 pagesWhat Are The Requirements of The ATMUvindu HarshanNo ratings yet
- CIFSDocument15 pagesCIFSRakesh V RakeshNo ratings yet
- Machine Model PV1GDocument1 pageMachine Model PV1GManuelNo ratings yet
- FortiGate VM ESXiDocument8 pagesFortiGate VM ESXiEddy StoicaNo ratings yet
- AHC822 ManualDocument2 pagesAHC822 ManualThuận Nguyễn VănNo ratings yet
- Circuit and Packet SwitchingDocument76 pagesCircuit and Packet SwitchingBharani DharanNo ratings yet
- B Cisco Business Wifi 6 Admin GuideDocument182 pagesB Cisco Business Wifi 6 Admin GuideiziNo ratings yet
- Simple Migration Strategies For Maximum Fire ProtectionDocument2 pagesSimple Migration Strategies For Maximum Fire ProtectionFrancisco RamirezNo ratings yet
- Muhammad FawadDocument5 pagesMuhammad Fawadmuhammad.fawad.n1No ratings yet
- Large Screen Panel Instruments User Manual: 3 Instrument InstallationDocument4 pagesLarge Screen Panel Instruments User Manual: 3 Instrument InstallationVu MinhNo ratings yet
- Unit 5 - Compiler Design - WWW - Rgpvnotes.inDocument20 pagesUnit 5 - Compiler Design - WWW - Rgpvnotes.inAkashNo ratings yet
- E. B. Magalona National High SchoolDocument2 pagesE. B. Magalona National High Schoolric jason pedralNo ratings yet
- Lexicographically Palindromic StringDocument3 pagesLexicographically Palindromic StringKrijayNo ratings yet
- Eicedriver™ - Power Driver Ics For Drives, Solar, Ups, Heating and VentilationDocument59 pagesEicedriver™ - Power Driver Ics For Drives, Solar, Ups, Heating and VentilationNelson Camilo de AlmeidaNo ratings yet
- Worksheet Shoot The BugDocument15 pagesWorksheet Shoot The Bugmuskan gargNo ratings yet
- Cloud Computing RespDocument2 pagesCloud Computing RespIgorJalesNo ratings yet
- Unit 5 - Wireless Network - WWW - Rgpvnotes.inDocument18 pagesUnit 5 - Wireless Network - WWW - Rgpvnotes.inZappY100% (1)
- LAB211 Assignment: Title Background Program SpecificationsDocument2 pagesLAB211 Assignment: Title Background Program SpecificationsQuân HuyNo ratings yet
- Krishnankoil: Career ObjectiveDocument3 pagesKrishnankoil: Career ObjectiveSivakumar PothirajNo ratings yet
- Prepared by Bushemmy Page 1 of 9Document9 pagesPrepared by Bushemmy Page 1 of 9Bushahiro EmmyNo ratings yet
- Irjet V7i31041Document5 pagesIrjet V7i31041Anirudh sai ReddyNo ratings yet
- Shailaja Macherla ResumeDocument5 pagesShailaja Macherla ResumeBheeshma TanneruNo ratings yet
- Objective:: Dhanesh K Raveendran Incident ManagerDocument4 pagesObjective:: Dhanesh K Raveendran Incident ManagerDHANESH KNo ratings yet
- Voyager Version 7.4 User ManualDocument45 pagesVoyager Version 7.4 User ManualFenzi100% (2)
- Module 8 PDFDocument26 pagesModule 8 PDFAMIYA KRISHNA UPADHYAYNo ratings yet