Professional Documents
Culture Documents
Overview
Uploaded by
sweetyCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Overview
Uploaded by
sweetyCopyright:
Available Formats
1.
Introduction
Brief history and background of RSA
Importance of public-key cryptography
2. Principles of RSA
Mathematical foundations (modular arithmetic, Euler's totient function)
Key components: public key, private key, modulus, exponentiation
3. Key Generation
Prime number generation
Calculation of modulus and public/private exponents
Key size considerations and recommendations
4. Encryption Process
Message representation and padding schemes
Modular exponentiation
Encryption algorithm step-by-step
5. Decryption Process
Modular exponentiation with private key
Decryption algorithm step-by-step
6. Security Analysis
Strengths and weaknesses of RSA
Attacks: brute force, factoring, timing attacks, chosen ciphertext attacks
Impact of key size on security
Recommendations for secure implementation
7. Practical Implementations
Real-world applications of RSA
Integration with other cryptographic algorithms
Performance considerations and optimizations
8. Future Directions
Post-quantum cryptography and RSA's resilience
Alternatives and improvements to RSA
Research trends and ongoing developments
9. Conclusion
Summary of key findings and insights
Importance of RSA in modern cryptography
Final thoughts on the algorithm's relevance and longevity
You might also like
- Computer and Information Security HandbookFrom EverandComputer and Information Security HandbookRating: 2.5 out of 5 stars2.5/5 (4)
- Modified Rsa Encryption Algorithm Using Four Keys IJERTCONV3IS07021Document5 pagesModified Rsa Encryption Algorithm Using Four Keys IJERTCONV3IS07021Jeff HambreNo ratings yet
- CISSP Exam Study Guide For Security Professionals: NIST Cybersecurity Framework, Risk Management, Digital Forensics & GovernanceFrom EverandCISSP Exam Study Guide For Security Professionals: NIST Cybersecurity Framework, Risk Management, Digital Forensics & GovernanceNo ratings yet
- Cryptography and System SecurityDocument3 pagesCryptography and System SecurityNirishNo ratings yet
- CSS (Comps)Document392 pagesCSS (Comps)rp2145611No ratings yet
- Public-Key Cryptography Standards: PKCS: Yongge Wang, PH.D., University of North Carolina at CharlotteDocument19 pagesPublic-Key Cryptography Standards: PKCS: Yongge Wang, PH.D., University of North Carolina at Charlottemail4290No ratings yet
- CSS - Orientation TE SEM VI FH - 22Document17 pagesCSS - Orientation TE SEM VI FH - 22Atul ShintreNo ratings yet
- B.Tech. Computer: Uka Tarsadia UniversityDocument6 pagesB.Tech. Computer: Uka Tarsadia UniversityPatelNo ratings yet
- 202CS002-Information and Network Security.Document2 pages202CS002-Information and Network Security.keerthiksNo ratings yet
- Information and Network SecurityDocument4 pagesInformation and Network SecurityMananNo ratings yet
- Xin Zhou 2011Document4 pagesXin Zhou 2011Shashi TiwariNo ratings yet
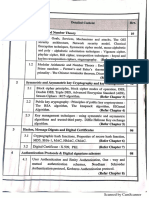
- Gujarat Technological University: Page 1 of 6Document6 pagesGujarat Technological University: Page 1 of 6Parshw PatelNo ratings yet
- Ijert Ijert: Improvement Over Public Key Encryption Algorithm For Security in Network CommunicationsDocument4 pagesIjert Ijert: Improvement Over Public Key Encryption Algorithm For Security in Network CommunicationsNandha KumarNo ratings yet
- System Programming and Compiler ConstructionDocument29 pagesSystem Programming and Compiler ConstructionTauros OPNo ratings yet
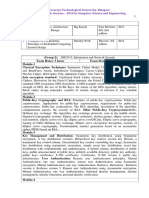
- Course OutlineDocument3 pagesCourse OutlineFasiledesNo ratings yet
- CH 6Document2 pagesCH 6al.wasel711No ratings yet
- Info. SecurityDocument3 pagesInfo. Securitytirth_diwaniNo ratings yet
- Birla Institute of Technology and Science, Pilani Pilani Campus Instruction DivisionDocument3 pagesBirla Institute of Technology and Science, Pilani Pilani Campus Instruction DivisionGuntaas SinghNo ratings yet
- UntitledDocument5 pagesUntitledTushar KapoorNo ratings yet
- Lesson Plan Unit I Introduction & Number Theory 10 HoursDocument2 pagesLesson Plan Unit I Introduction & Number Theory 10 Hoursshika2906No ratings yet
- CSE4003 Cyber-Security ETH 1 AC41Document8 pagesCSE4003 Cyber-Security ETH 1 AC41govindNo ratings yet
- 8th Sem SyllabusDocument9 pages8th Sem SyllabusEngineer BhaiyaNo ratings yet
- Network Security and Cryptography: Course Code: 15Cs1105 Pre-Requisites: Computer NetworksDocument3 pagesNetwork Security and Cryptography: Course Code: 15Cs1105 Pre-Requisites: Computer Networks17131A05K1 SHAIK RESHMANo ratings yet
- Ite4001 Network-And-Information-security Eth 1.1 47 Ite4001Document2 pagesIte4001 Network-And-Information-security Eth 1.1 47 Ite4001Prateek AgarwalNo ratings yet
- Ite4001 Network-And-Information-security Eth 1.1 47 Ite4001Document2 pagesIte4001 Network-And-Information-security Eth 1.1 47 Ite4001Vivek GopalshettyNo ratings yet
- AU Security Course OutlineDocument3 pagesAU Security Course OutlinesamuelNo ratings yet
- Semester - 8 GTU SyllabusDocument9 pagesSemester - 8 GTU SyllabusPanchal Dhaval MNo ratings yet
- Course Number: Cosc377 Course Title: Credit Hours: Prerequisites: Course DescriptionDocument2 pagesCourse Number: Cosc377 Course Title: Credit Hours: Prerequisites: Course DescriptionSamNo ratings yet
- Gujarat Technological University: Information TechnologyDocument2 pagesGujarat Technological University: Information TechnologyHomik SoniNo ratings yet
- 3it02: Information Security CREDITS - 4 (LTP: 3,0,2)Document2 pages3it02: Information Security CREDITS - 4 (LTP: 3,0,2)bhargeshpatelNo ratings yet
- How To Use RSA or How To Improve The Efficiency of RSA Without Loosing Its SecurityDocument4 pagesHow To Use RSA or How To Improve The Efficiency of RSA Without Loosing Its SecuritySaurabh SinghNo ratings yet
- CS175 Cryptography & Network SecurityDocument1 pageCS175 Cryptography & Network SecurityDev VatsNo ratings yet
- Software Project Management: SyllabusDocument6 pagesSoftware Project Management: SyllabusAnonymous rFt9CaE1No ratings yet
- Course Outline Information SecurityDocument1 pageCourse Outline Information SecurityJebesaNo ratings yet
- Computer Crytography-Mit 5114-Take Away 2Document10 pagesComputer Crytography-Mit 5114-Take Away 2JoelNo ratings yet
- CSE403 Network SecurityDocument2 pagesCSE403 Network SecurityrajatNo ratings yet
- Cryptography - Lecture14Document12 pagesCryptography - Lecture14AbhijeetNo ratings yet
- 09 - Chapter 5Document21 pages09 - Chapter 5Dr D SuneethaNo ratings yet
- CS8792 Course File FormatDocument93 pagesCS8792 Course File FormatnancypeterNo ratings yet
- High Speed Implementation of RSA Algorithm With Modified Keys ExchangeDocument5 pagesHigh Speed Implementation of RSA Algorithm With Modified Keys ExchangeYoniNo ratings yet
- CSE2008 SyllabusDocument2 pagesCSE2008 SyllabusABHAY POTLURI 20BCI0017No ratings yet
- Cryptography and Network Security: Type of Course: Course Duration: Exam Date: 2 Prof. Sourav MukhopadhyayDocument1 pageCryptography and Network Security: Type of Course: Course Duration: Exam Date: 2 Prof. Sourav MukhopadhyayBored GamerNo ratings yet
- IT502 - Information SecurityDocument3 pagesIT502 - Information SecurityNader AzalNo ratings yet
- Cryptography & Network Security SyllDocument1 pageCryptography & Network Security SyllBarnali DuttaNo ratings yet
- Cryptography and Network Security: UNIT-1Document5 pagesCryptography and Network Security: UNIT-1atmadeep09No ratings yet
- Syllabus Covered For 1 MST - 7th SEm UPDATEDDocument2 pagesSyllabus Covered For 1 MST - 7th SEm UPDATEDVianyNo ratings yet
- Cyber Security CourseDocument5 pagesCyber Security Coursesanghi ranjithkumarNo ratings yet
- Master PDFDocument36 pagesMaster PDFAshrafNo ratings yet
- ISS404: Security Architecture, Design and Models SyllabusDocument2 pagesISS404: Security Architecture, Design and Models SyllabusLeNantais SonderangeboteNo ratings yet
- Building Information Security Using New Expanded RSA CryptosystemDocument4 pagesBuilding Information Security Using New Expanded RSA Cryptosystemabdulg abdulNo ratings yet
- Title 5Document2 pagesTitle 5М. ЭнэрэлтNo ratings yet
- Instructor: Nelly FazioDocument3 pagesInstructor: Nelly FazioJorge GuerreroNo ratings yet
- Course Objectives: Students Will Try To LearnDocument4 pagesCourse Objectives: Students Will Try To LearnAbhiNo ratings yet
- CryptographyDocument2 pagesCryptographykundankeshari2537No ratings yet
- DownloadDocument10 pagesDownloadAtul GautamNo ratings yet
- Ec3401 Networks and Security SyllabusDocument3 pagesEc3401 Networks and Security Syllabusabinayasundaramoorthi2000No ratings yet
- Student SyllabusDocument1 pageStudent SyllabusAnurag PokhriyalNo ratings yet
- CNS SyllabusDocument2 pagesCNS SyllabuskathiravanNo ratings yet
- Synopsis of ThesisDocument5 pagesSynopsis of Thesishimanshus13No ratings yet
- Set Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNFrom EverandSet Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNRating: 5 out of 5 stars5/5 (1)
- The Compete Ccna 200-301 Study Guide: Network Engineering EditionFrom EverandThe Compete Ccna 200-301 Study Guide: Network Engineering EditionRating: 5 out of 5 stars5/5 (4)
- Microsoft Certified Azure Fundamentals Study Guide: Exam AZ-900From EverandMicrosoft Certified Azure Fundamentals Study Guide: Exam AZ-900No ratings yet
- Concise Guide to OTN optical transport networksFrom EverandConcise Guide to OTN optical transport networksRating: 4 out of 5 stars4/5 (2)
- Alcatel-Lucent Service Routing Architect (SRA) Self-Study Guide: Preparing for the BGP, VPRN and Multicast ExamsFrom EverandAlcatel-Lucent Service Routing Architect (SRA) Self-Study Guide: Preparing for the BGP, VPRN and Multicast ExamsNo ratings yet
- Cybersecurity: A Simple Beginner’s Guide to Cybersecurity, Computer Networks and Protecting Oneself from Hacking in the Form of Phishing, Malware, Ransomware, and Social EngineeringFrom EverandCybersecurity: A Simple Beginner’s Guide to Cybersecurity, Computer Networks and Protecting Oneself from Hacking in the Form of Phishing, Malware, Ransomware, and Social EngineeringRating: 5 out of 5 stars5/5 (40)
- AWS Certified Solutions Architect Study Guide: Associate SAA-C02 ExamFrom EverandAWS Certified Solutions Architect Study Guide: Associate SAA-C02 ExamNo ratings yet
- PHP BLUEPRINT: An Essential Beginners Guide to Learn the Realms of PHP From A-ZFrom EverandPHP BLUEPRINT: An Essential Beginners Guide to Learn the Realms of PHP From A-ZNo ratings yet
- Hacking Network Protocols: Complete Guide about Hacking, Scripting and Security of Computer Systems and Networks.From EverandHacking Network Protocols: Complete Guide about Hacking, Scripting and Security of Computer Systems and Networks.Rating: 5 out of 5 stars5/5 (2)
- Evaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsFrom EverandEvaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsRating: 5 out of 5 stars5/5 (1)
- Networking Fundamentals: Develop the networking skills required to pass the Microsoft MTA Networking Fundamentals Exam 98-366From EverandNetworking Fundamentals: Develop the networking skills required to pass the Microsoft MTA Networking Fundamentals Exam 98-366No ratings yet
- Azure Networking: Command Line Mastery From Beginner To ArchitectFrom EverandAzure Networking: Command Line Mastery From Beginner To ArchitectNo ratings yet
- Hacking: A Beginners Guide To Your First Computer Hack; Learn To Crack A Wireless Network, Basic Security Penetration Made Easy and Step By Step Kali LinuxFrom EverandHacking: A Beginners Guide To Your First Computer Hack; Learn To Crack A Wireless Network, Basic Security Penetration Made Easy and Step By Step Kali LinuxRating: 4.5 out of 5 stars4.5/5 (67)
- Software-Defined Networks: A Systems ApproachFrom EverandSoftware-Defined Networks: A Systems ApproachRating: 5 out of 5 stars5/5 (1)
- Microsoft Azure Infrastructure Services for Architects: Designing Cloud SolutionsFrom EverandMicrosoft Azure Infrastructure Services for Architects: Designing Cloud SolutionsNo ratings yet
- Computer Systems and Networking Guide: A Complete Guide to the Basic Concepts in Computer Systems, Networking, IP Subnetting and Network SecurityFrom EverandComputer Systems and Networking Guide: A Complete Guide to the Basic Concepts in Computer Systems, Networking, IP Subnetting and Network SecurityRating: 4.5 out of 5 stars4.5/5 (13)
- Designing and Building Security Operations CenterFrom EverandDesigning and Building Security Operations CenterRating: 3 out of 5 stars3/5 (3)