Professional Documents
Culture Documents
smc00 Edited
smc00 Edited
Uploaded by
vincent laneOriginal Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
smc00 Edited
smc00 Edited
Uploaded by
vincent laneCopyright:
Available Formats
See discussions, stats, and author profiles for this publication at: https://www.researchgate.
net/publication/3876432
Distributed denial of service attacks
Conference Paper · February 2000
DOI: 10.1109/ICSMC.2000.886455 · Source: IEEE Xplore
CITATIONS READS
298 7,301
4 authors, including:
Stuart H. Rubin M.H. Smith
NIWC-Pacific Institute of Electrical and Electronics Engineers
193 PUBLICATIONS 1,401 CITATIONS 44 PUBLICATIONS 900 CITATIONS
SEE PROFILE SEE PROFILE
Ljiljana Trajkovic
Simon Fraser University
201 PUBLICATIONS 2,962 CITATIONS
SEE PROFILE
All content following this page was uploaded by Ljiljana Trajkovic on 25 December 2014.
The user has requested enhancement of the downloaded file.
Distributed Denial of Service Attacks
Felix Lau Stuart H. Rubin Michael H. Smith Ljiljana Trajkovic
Simon Fraser University SPAWAR Systems Center University of Calgary Simon Fraser University
Burnaby, BC, Canada San Diego, CA, USA Calgary, AB, Canada Burnaby, BC, Canada
V5A 1S6 92152-5001 T2N 1N4 V5A 1S6
fwlau@cs.sfu.ca srubin@spawar.navy.mil mhs@mining.ubc.ca ljilja@cs.sfu.ca
Abstract 2. Characteristics of Distributed Denial of
Service Attacks
We discuss distributed denial of service attacks in the
Internet. We were motivated by the widely known February
A denial of service attack is characterized by an explicit
2000 distributed attacks on Yahoo!, Amazon.com, CNN.com,
attempt by an attacker to prevent legitimate users of a
and other major Web sites. A denial of service is
service from using the desired resources. Examples of denial
characterized by an explicit attempt by an attacker to prevent
of service attacks include [6]:
legitimate users from using resources. An attacker may
attempt to: “flood” a network and thus reduce a legitimate § attempts to “flood” a network, thereby preventing
user’s bandwidth, prevent access to a service, or disrupt legitimate network traffic
service to a specific system or a user. We describe methods § attempts to disrupt connections between two machines,
and techniques used in denial of service attacks, and we list thereby preventing access to a service
possible defenses. In our study, we simulate a distributed
§ attempts to prevent a particular individual from
denial of service attack using ns-2 network simulator. We
accessing a service
examine how various queuing algorithms implemented in a
network router perform during an attack, and whether § attempts to disrupt service to a specific system or
legitimate users can obtain desired bandwidth. We find that person.
under persistent denial of service attacks, class based The distributed format adds the “many to one” dimension
queuing algorithms can guarantee bandwidth for certain that makes these attacks more difficult to prevent [17]. A
classes of input flows. distributed denial of service attack is composed of four
elements, as shown in Figure 1 [4]. First, it involves a victim,
i.e., the target host that has been chosen to receive the
brunt of the attack. Second, it involves the presence of the
attack daemon agents. These are agent programs that
1. Introduction actually conduct the attack on the target victim. Attack
daemons are usually deployed in host computers. These
We studied distributed denial of service attacks in the daemons affect both the target and the host computers. The
Internet such as the widely publicized, distributed attacks task of deploying these attack daemons requires the attacker
on Yahoo!, Amazon.com, CNN.com, and other major Web to gain access and infiltrate the host computers. The third
sites in February 2000. Even though denial of service attacks component of a distributed denial of service attack is the
have existed for some time, their recent distributed formats control master program. Its task is to coordinate the attack.
have made these attacks more difficult to prevent. Finally, there is the real attacker, the mastermind behind the
In this paper we first summarize the methods involved in attack. By using a control master program, the real attacker
denial of service attacks, list possible defenses, and discuss can stay behind the scenes of the attack. The following
in more depth the attack on Yahoo!. We then use a network steps take place during a distributed attack [7]:
simulator to study distributed denial of service attacks. Our 1. The real attacker sends an “execute” message to the
simulation study examines how various queuing services in control master program.
network routers may alleviate the problem of denying
2. The control master program receives the “execute”
bandwidth to legitimate users during the denial of service
message and propagates the command to the attack
attack. Finally, we use simulation results to recommend
daemons under its control.
certain queuing algorithms that may protect users in cases
of distributed denial of service attacks. 3. Upon receiving the attack command, the attack
daemons begin the attack on the victim.
Daemon “amplifier” [16]. There are two parties who are hurt by this
Master
type of attack: the intermediate broadcast devices
(amplifiers) and the spoofed source address target (the
Daemon
victim). The victim is the target of a large amount of traffic
Daemon
that the amplifiers generate. This attack has the potential to
Daemon
overload an entire network.
SYN Flood attack is also known as the Transmission
Daemon Control Protocol (TCP) SYN attack, and is based on
Real Attacker exploiting the standard TCP three–way handshake. The
Victim
TCP three-way handshake requires a three-packet exchange
to be performed before a client can officially use the service.
A server, upon receiving an initial SYN (synchronize/start)
Figure 1: The four components of a distributed denial of request from a client, sends back a SYN/ACK
service attack: a real attacker, a control master program, (synchronize/acknowledge) packet and waits for the client
attack daemons and the victim [4]. to send the final ACK (acknowledge). However, it is
possible to send a barrage of initial SYN’s without sending
the corresponding ACK’s, essentially leaving the server
Although it seems that the real attacker has little to do but
waiting for the non-existent ACK’s [3]. Considering that the
sends out the “execute” command, he/she actually has to
server only has a limited buffer queue for new connections,
plan the execution of a successful distributed denial of
SYN Flood results in the server being unable to process
service attack. The attacker must infiltrate all the host
other incoming connections as the queue gets overloaded
computers and networks where the daemon attackers are to
[8].
be deployed. The attacker must study the target’s network
topology and search for bottlenecks and vulnerabilities that UDP Flood attack is based on UDP echo and character
can be exploited during the attack. Because of the use of generator services provided by most computers on a
attack daemons and control master programs, the real network. The attacker uses forged UDP packets to connect
attacker is not directly involved during the attack, which the echo service on one machine to the character generator
makes it difficult to trace who spawned the attack. (chargen) service on another machine. The result is that the
two services consume all available network bandwidth
In the following subsections, we review some well-known
between the machines as they exchange characters between
attack methods (Smurf, SYN Flood, and User Datagram
themselves. A variation of this attack called ICMP Flood,
Protocol (UDP) Flood) and the current distributed denial of
floods a machine with ICMP packets instead of UDP
service methods (Trinoo, Tribe Flood Network, Stacheldraht,
packets.
Shaft, and TFN2K). We describe defense mechanisms that
can be employed by networks, and briefly review the Yahoo!
attack.
2.2 Methods of Distributed Denial of Service
Attacks
2.1 Methods of Denial of Service Attacks
In this section, we describe the distributed denial of service
We described below some widely known basic denial of methods employed by an attacker. These techniques help
service attack methods that are employed by the attack an attacker coordinate and execute the attack. These types
daemons. of attacks plagued the Internet in February 2000. However,
these distributed attack techniques still rely on the
Smurf attack involves an attacker sending a large amount of previously described attack methods to carry out the
Internet Control Message Protocol (ICMP) echo traffic to a attacks.
set of Internet Protocol (IP) broadcast addresses. The ICMP
echo packets are specified with a source address of the The techniques are listed in chronological order. It can be
target victim (spoofed address) [9]. Most hosts on an IP observed that as time has passed, the distributed
network will accept ICMP echo requests [5] and reply to techniques (Trinoo, TFN, Stacheldraht, Shaft, and TFN2K)
them with an echo reply to the source address, in this case, have become technically more advanced and, hence, more
the target victim. This multiplies the traffic by the number of difficult to detect.
responding hosts. On a broadcast network, there could Trinoo uses TCP to communicate between the attacker and
potentially be hundreds of machines to reply to each ICMP the control master program. The master program
packet. The process of using a network to elicit many communicates with the attack daemons using UDP packets.
responses to a single packet has been labeled as an
Trinoo’s attack daemons implement UDP Flood attacks Applying Security Patches: To guard against denial of
against the target victim [10]. service attacks, host computers must be updated with the
Tribe Flood Network (TFN) uses a command line interface latest security patches and techniques. For example, in the
to communicate between the attacker and the control master case of the SYN Flood attack [8], there are three steps that
program. Communication between the control master and the host computers can take to guard themselves from
attack daemons is done via ICMP echo reply packets. attacks: increase the size of the connection queue, decrease
TFN’s attack daemons implement Smurf, SYN Flood, UDP the time-out waiting for the three-way handshake, and
Flood, and ICMP Flood attacks [10]. employ vendor software patches to detect and circumvent
the problem.
Stacheldraht (German term for “barbed wire”) is based on
the TFN attack. However, unlike TFN, Stacheldraht uses an Disabling Unused Services: If UDP echo or chargen
encrypted TCP connection for communication between the services are not required, disabling them will help to defend
attacker and master control program. Communication against the attack. In general, if network services are
between the master control program and attack daemons is unneeded or unused, the services should be disabled to
conducted using TCP and ICMP, and involves an automatic prevent tampering and attacks.
update technique for the attack daemons. The attack Performing Intrusion Detection: By performing intrusion
daemons for Stacheldraht implement Smurf, SYN Flood, UDP detection, a host computer and network are guarded against
Flood, and ICMP Flood attacks [10]. being a source for an attack, as while as being a victim of an
Shaft is modeled after Trinoo. Communication between the attack. Network monitoring is a very good pre-emptive way
control master program and attack daemons is achieved of guarding against denial of service attacks. By monitoring
using UDP packets. The control master program and the traffic patterns, a network can determine when it is under
attacker communicate via a simple TCP telnet connection. A attack, and can take the required steps to defend itself. By
distinctive feature of Shaft is the ability to switch control inspecting host systems, a host can also prevent it from
master servers and ports in real time, hence making hosting an attack on another network [19].
detection by intrusion detection tools difficult [11].
TFN2K uses TCP, UDP, ICMP, or all three to communicate 2.4 Yahoo! Attack
between the control master program and the attack
daemons. Communication between the real attacker and
control master is encrypted using a key-based CAST-256 The attacks on the major Web sites began in early February
algorithm [1]. In addition, TFN2K conducts covert exercises 2000, with the first major attack being on Yahoo! on
to hide itself from intrusion detection systems. TFN2K February 7 [15]. The surprise attack took the Yahoo! site
attack daemons implement Smurf, SYN, UDP, and ICMP down for more than three hours. It was based on the Smurf
Flood attacks [2]. attack, and most likely, the Tribe Flood Network technique.
At the peak of the attack, Yahoo! was receiving more than
one gigabit per second of data requests.
2.3 Defenses Against Attacks Yahoo! has stated that it was unprepared for this magnitude
of an attack, and hence, was not ready to defend itself.
Many observers have stated that there are currently no Yahoo! receives huge number of visitors every day, and
successful defenses against a fully distributed denial of most likely believed that the bandwidth provided to the
service attack. This may be true. Nevertheless, there are users by their Internet service providers would defend them
numerous safety measures that a host or network can against any type of denial of service attacks. However, they
perform to make the network and neighboring networks did not account for a large distributed denial of service
more secure. These measures include: attack from numerous servers and networks across the
Internet.
Filtering Routers: Filtering all packets entering and leaving
the network protects the network from attacks conducted
from neighboring networks, and prevents the network itself
from being an unaware attacker [12]. This measure requires
installing ingress and egress packet filters on all routers. 3. Simulation Scenarios
Disabling IP Broadcasts: By disabling IP broadcasts, host
computers can no longer be used as amplifiers in ICMP Using the simulation tools, we examine how various queuing
Flood and Smurf attacks. However, to defend against this algorithms implemented in a network router perform during
attack, all neighboring networks need to disable IP an attack, and whether legitimate users can obtain desired
broadcasts. service. We use the ns–2 network simulator [18] to simulate
a distributed denial of service attack on a targeted router.
We simulate a simplified version of the distributed denial of § Deficit Round Robin scheduling is an algorithm that
service attack on a single targeted router, shown in Figure 2 services each flow in a predefined sequence.
[17]. We simulate the attack using UDP packets. Our main § Random Early Detection (Drop) tries to anticipate
goal is to compare several queuing algorithms and to congestion by monitoring the queue [13]. When the
determine whether the queuing methods in the target router specified threshold is reached, it randomly discards or
could provide a better share of bandwidth to the legitimate marks the packets.
users during the attack. We measure the throughput
provided to the legitimate users and to the attackers when § Class Based Queuing (Packet by Packet Round Robin
using the following queuing algorithms: DropTail, Fair and Weighted Round Robin) queues packets according
Queuing, Stochastic Fair Queuing, Deficit Round Robin, to criteria defined by an administrator [14]. It provides
Random Early Detection, and Class Based Queuing (Packet differential forwarding service for each class. Packets
by Packet Round Robin and Weighted Round Robin). are divided into a hierarchy of classes defined by input
flows. For our simulations, we develop two classes of
Class Based Queuing: a class of known flows
(legitimate users) and a class of unknown flows. For
each class, we allocated a minimum bandwidth
allotment.
Figure 2: The simulated distributed denial of service attack 4. Simulation Results
scenario [17].
We now discuss the results obtained from our simulation
We conduct the ns-2 simulations using three network study. For each queuing algorithm, except DropTail, we
topologies. Each network topology consists of one simulate topologies A, B, and C.
legitimate user, one target host, and a varied number of In the case of DropTail queuing algorithm, we only simulate
attack daemons, as shown in Figure 3. topology A because only two attackers were required to
In our simulation scenarios, we use a single target router overload the target router. The legitimate user has 0.1
with a 1 Mbps bandwidth. All network links have 1 Mbps Mbps, while the two attackers each have allocated 0.6 Mbps
bandwidth, with a delay of 100 ms. The legitimate user is bandwidth. Since the target router has a buffer size of 1
defined as a UDP agent sending packets of size 500 bytes at Mbps, and the input links have 1.3 Mbps bandwidth,
a rate of 0.1 Mbps. The attack daemons are defined as UDP overloading the buffer in the router only requires two
agents sending packets of size 500 bytes at rates of 0.3 to attackers and packet loss in the router is to be expected.
1.0 Mbps. All sources generated constant bit rate (CBR) The legitimate user’s bandwidth was reduced to zero once
traffic. the attack executed by the two attack daemons was fully
engaged. As shown in Figure 4, the user's bandwidth
(bottom curve) falls to zero at approximately 2.5 sec after the
beginning of the attack.
Figure 3: Simulated network topologies A, B, and C (left to
right). Target is the right most node in the networks.
In our simulations, we use the following queuing algorithms
available in ns-2:
§ DropTail is a queuing algorithm based on a first-come-
first-serve discipline.
§ Fair Queuing is an algorithm that attempts to allocate
bandwidth fairly among all input flows.
§ Stochastic Fair Queuing involves a hash function used Figure 4: Simulation results using DropTail queuing
to map flows to a queue. algorithm and network topology A. Shown are User 1,
Attacker 1, Attacker 2, and the total bandwidth. Once the legitimate user's bandwidth, the twelve attacker's bandwidth,
attack is fully engaged, the legitimate user (bottom curve) is and the total bandwidth for the target router (top), and the
left with little or no bandwidth. legitimate user's bandwidth (bottom).
In simulation scenarios using the remaining queuing Finally, two variants of the Class Based Queuing algorithms
algorithms, topologies A and B did not provide enough were successful in providing full bandwidth requested by
traffic overload to prevent legitimate users from receiving the legitimate user. In fact, with appropriately defined flow
requested bandwidth. However, simulations based on classes (with known and unknown flags), the legitimate user
topology C resulted in several target routers being was able to obtain all requested bandwidth, as shown in
overloaded during the attack by the twelve attack daemons. Figure 6 (bottom).
For the simulation scenario with topology C, we allocated Unlike other queuing algorithms that we simulated, Class
0.1 Mbps to the legitimate user, 0.5 Mbps bandwidth was Based Queuing algorithms require extra overhead and effort
given to attackers 1-6, and 1.0 Mbps was given to attackers to be implemented, because input flows to a Class Based
7-12. The total input bandwidth of the attackers is 9.0 Queuing based routers must be a priori categorized and
Mbps. managed. Hence, this queuing discipline may not be a
Two queuing algorithms (Random Early Detection and Class feasible solution for routers with a large number of input
Based Queuing) are successful in providing bandwidth links.
requested by the legitimate user during the simulations
using network topology C. Fair Queuing, Stochastic Fair
Queuing, and Deficit Round Robin Queuing are algorithms
that provided little or no bandwidth to the legitimate user
during the attack. Although the user did not receive full
throughput with Random Early Detection queuing, he/she
continued to receive service through most of the duration of
the attack scenario, as shown in Figure 5 (bottom).
Figure 6: Simulation results using Class Based Queuing
(packet by packet round robin) algorithm and topology C.
The legitimate user obtained most of the requested 0.1
Mbps bandwidth. Shown are bandwidths for the legitimate
user, twelve attack daemons, and the total bandwidth for the
target router (top), and the bandwidth for the legitimate user
only (bottom).
Figure 5: Simulation results using Random Early Detection
queuing algorithm and network topology C. Shown are the
In summary, our simulation results indicate that Class Based [2] J. Barlow and W. Thrower, “TFN2K – an analysis,”
Queuing had the best performance and provided the full Feb. 2000, http://packetstorm.securify.com/distributed/TFN2k_
bandwidth that the legitimate user requested. The Random Analysis.htm.
Early Detection algorithm was the best among algorithms
that required no additional overhead. It was able to provide [3] S. Bellovin, “Security problems in the TCP/IP protocol suite,”
40% of the bandwidth requested by the user. Comput. Commun. Rev., vol. 19, no. 2, pp. 32-48, Apr. 1989.
[4] S. Bellovin, “Distributed denial of service attacks,” Feb. 2000,
http://www.research.att.com/~smb/talks.
5. Conclusions [5] S. Bellovin, Ed., “The ICMP traceback message,” Network
Working Group Internet Draft, Mar. 2000, http://www.
research.att.com/~smb/papers/draft-bellovin-itrace-00.txt.
In this paper, we discussed distributed denial of service
attacks on the Internet. We described how distributed [6] CERT ® Coordination Center, Cert Advisories: “CA-2000-01
attacks are conducted, we reviewed some well known denial-of-service developments,” http://www.cert.org/advisories/
distributed denial of service techniques, and discuss CA-2000-01.html; “CA-99-17 denial-of-service tools,”
various defense mechanisms that could be employed by http://www.cert.org/advisories/CA-99-17-denial-of-service-
networks and hosts. tools.html; “CA-98-13-tcp-denial-of-service: vulnerability in
We used network simulation tools to examine the certain TCP/IP implementations,” http://www.cert.org/advisories/
performance of various queuing algorithms in alleviating the CA-98-13-tcp-denial-of-service.html.
distributed denial of service attacks and in providing desired
[7] CERT ® Coordination Center, “Results of the distributed
service to the users. It was found that the majority of
systems intruder tools workshop,” Nov. 1999,
routing algorithms that we considered provided no
http://www.cert.org/reports/dsit_workshop.pdf.
bandwidth to the legitimate user during the attack.
Nevertheless, even under persistent denial of service [8] Cisco Systems, Inc., “Defining strategies to protect against
attacks, Class Based Queuing algorithm could guarantee TCP SYN denial of service attacks,” July 1999,
bandwidth for certain classes of input flows, while Random http://www.cisco.com/warp/public/707/4.html.
Early Detection was successful in providing limited
bandwidth to legitimate users. Since implementation of a [9] Daemon9, Infinity, and Route, “IP-spoofing demystified:
Class Based Queuing algorithm required additional effort, trust-relationship exploitation,” Phrack Mag., June 1996,
there is a tradeoff between its performance and the http://www.fc.net/phrack/files/p48/p48-14.html.
implementation overhead. In summary, our simulation
[10] D. Dittrich, “The DoS project's ‘Trinoo’ distributed denial of
results indicated that implementing queuing algorithms in
service attack tool,” Oct. 1999; “The ‘Stacheldraht’ distributed
network routers may provide the desired solution in
denial of service attack tool,” Dec. 1999; “The ‘Tribe Flood
protecting users in cases of distributed denial of service
Network’ distributed denial of service attack tool,” Oct. 1999,
attacks.
http://www.washington.edu/People/dad.
[11] D. Dittrich, S. Dietrich, and N. Long, “An analysis of the
Acknowledgements ‘Shaft’ distributed denial of device tool,” Mar. 2000,
http://netsec.gsfc.nasa.gov/~spock/shaft_analysis.txt.
We thank V. Markovski for his assistance with the ns-2
[12] P. Ferguson and D. Senie, “RFC 2267: Network ingress
network simulator. This research was supported by the
filtering: defeating denial of service attacks which employ IP
NSERC Grant 216844-99 and the BC Advanced Systems
source address spoofing,” Jan. 1998, http://info.internet.isi.edu/in-
Institute Fellowship.
notes/rfc/files/rfc2267.txt.
[13] S. Floyd and V. Jacobson, “Random early detection gateways
for congestion avoidance,” IEEE/ACM Trans. Networking, vol. 1
References no. 4, pp. 397-413, Aug. 1993.
[14] S. Floyd and V. Jacobson, “Link-sharing and resource
[1] C. Adams and J. Gilchrist, “RFC 2612: The CAST-256 management models for packet networks,” IEEE/ACM Trans.
encryption algorithm,” June 1999, http://www.cis.ohio- Networking, vol. 3 no. 4, pp. 365-386, Aug. 1995.
state.edu/htbin/rfc/rfc2612.html.
[15] A. Harrison, “The denial-of-service aftermath,” Feb. 2000,
http://www.cnn.com/2000/TECH/computing/02/14/dos
.aftermath.idg/index.html.
[16] C. A. Huegen, “The latest in denial of service attacks:
‘Smurfing’ description and information to minimize effects,” Feb.
2000, http://users.quadrunner.com/chuegen/smurf.cgi.
[17] B. Martin, “Have script, will destroy (lessons in DoS),” Feb.
2000, http://www.attrition.org.
[18] ns-2 network simulator, http://www.isi.edu/nsnam/ns .
[19] T. H. Ptacek and T. N. Newsham, “Insertion, evasion, and
denial of service: eluding network intrusion detection,” Secure
Networks, Inc., Jan. 1998, http://www.clark.net/~roesch/
idspaper.html.
View publication stats
You might also like
- Internet Phone Services Simplified (VoIP)Document176 pagesInternet Phone Services Simplified (VoIP)sumanth83137No ratings yet
- CEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021From EverandCEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021No ratings yet
- ISP Edge DesignDocument61 pagesISP Edge Designnihadabed77100% (1)
- BMW Bus Systems PDFDocument76 pagesBMW Bus Systems PDFGeorge NutaNo ratings yet
- ITN Module 16 STDDocument35 pagesITN Module 16 STDnurul husaifahNo ratings yet
- An Ultimate Guide To DDos Attack: Detection, Prevention and MitigationDocument41 pagesAn Ultimate Guide To DDos Attack: Detection, Prevention and MitigationTechAppriseNo ratings yet
- Distributed Denial of Service Attacks: Prepared For: Prof. Ruby Lee ELE 572Document86 pagesDistributed Denial of Service Attacks: Prepared For: Prof. Ruby Lee ELE 572Mihir AsharNo ratings yet
- SSL and TLS EssentialsDocument212 pagesSSL and TLS EssentialsAbrasaxEimi370No ratings yet
- Hotel Accounting ManualDocument25 pagesHotel Accounting ManualXuân Phong Bùi100% (1)
- RFP For Procurement of Network Access Control (Nac) Solution With Manageable Network SwitchesDocument66 pagesRFP For Procurement of Network Access Control (Nac) Solution With Manageable Network SwitchesShailja vermaNo ratings yet
- Latest HCIA SECURITY PDFDocument70 pagesLatest HCIA SECURITY PDFIbrahimaNo ratings yet
- Ddos AttacksDocument29 pagesDdos AttackssportythieveNo ratings yet
- Sap Hana System Replication Failover On SUSE LINUX For Sap ApplicationsDocument30 pagesSap Hana System Replication Failover On SUSE LINUX For Sap ApplicationsMohsinIqbalNo ratings yet
- Final Project On E BankingDocument71 pagesFinal Project On E BankingTarun Dhiman0% (2)
- smc00 EditedDocument8 pagessmc00 EditedOsca MutaiNo ratings yet
- Characteristics of Distributed Denial Service AttacksDocument6 pagesCharacteristics of Distributed Denial Service AttacksRoger RibeiroNo ratings yet
- DDoS Final PDCS PaperDocument8 pagesDDoS Final PDCS PaperEduardo CANo ratings yet
- Demystifying Denial of Service AttacksDocument11 pagesDemystifying Denial of Service AttacksAdarsh SaxenaNo ratings yet
- W2-Module 002Document20 pagesW2-Module 002Jitlee PapaNo ratings yet
- Ddos Attacks, Detection Parameters and Mitigation in Cloud EnvironmentDocument4 pagesDdos Attacks, Detection Parameters and Mitigation in Cloud EnvironmentAbere BalewNo ratings yet
- Active Attack Passive Attack: Disabling Unused ServicesDocument5 pagesActive Attack Passive Attack: Disabling Unused ServicesMohamad MansourNo ratings yet
- Inferring Internet Denial-of-Service Activity: Caida San Diego Supercomputer Center University of California, San DiegoDocument14 pagesInferring Internet Denial-of-Service Activity: Caida San Diego Supercomputer Center University of California, San DiegoNiltonNo ratings yet
- Extenuate DDos Attacks in CloudDocument4 pagesExtenuate DDos Attacks in CloudkiranNo ratings yet
- CSE DDos ReportDocument19 pagesCSE DDos ReportAbhinavms AbhinavmsNo ratings yet
- 32 Topic 4-ActiveDocument3 pages32 Topic 4-ActiveVladimir ApostolovNo ratings yet
- ServiceProtector Student GuideDocument339 pagesServiceProtector Student GuideRamil BektimirovNo ratings yet
- Chapter 04 - Network SecurityDocument25 pagesChapter 04 - Network SecurityJaye 99No ratings yet
- All NL All The DayDocument74 pagesAll NL All The Dayاحمد سالمNo ratings yet
- Dyn DDOS CyberattackDocument3 pagesDyn DDOS Cyberattackblob mlNo ratings yet
- (IJCST-V11I6P7) :tarun VasagiriDocument6 pages(IJCST-V11I6P7) :tarun VasagiriEighthSenseGroupNo ratings yet
- Chapter 1: Introduction: 1 Denial of ServiceDocument23 pagesChapter 1: Introduction: 1 Denial of ServiceManu JoseNo ratings yet
- Dark Seul Attack Kill ChainDocument4 pagesDark Seul Attack Kill ChainmaxNo ratings yet
- A Survey of Distributed Denial of Service Attacks and DefensesDocument18 pagesA Survey of Distributed Denial of Service Attacks and Defensesdanilo.chagasNo ratings yet
- Security in Ad Hoc NetworkDocument8 pagesSecurity in Ad Hoc Networkmurthy venkataNo ratings yet
- Science Direct 2Document7 pagesScience Direct 2ghouse1508No ratings yet
- Hack Wired Network May 04Document22 pagesHack Wired Network May 04Brandon BrinkNo ratings yet
- Taming The 800 Pound Gorilla: The Rise and Decline of NTP Ddos AttacksDocument14 pagesTaming The 800 Pound Gorilla: The Rise and Decline of NTP Ddos AttacksFiti HoyNo ratings yet
- Detecting Distributed Denial of ServiceDocument20 pagesDetecting Distributed Denial of ServicemolaviNo ratings yet
- Review of Syn-Flooding Attack Detection MechanismDocument19 pagesReview of Syn-Flooding Attack Detection MechanismijdpsNo ratings yet
- R Syn-Flooding Attack Detection Mechanism: Eview ofDocument19 pagesR Syn-Flooding Attack Detection Mechanism: Eview ofMah NoorNo ratings yet
- التقرير النهائيDocument9 pagesالتقرير النهائياحمد سالمNo ratings yet
- Survey DDoS DefenseDocument24 pagesSurvey DDoS DefenseDaniel AlejandroNo ratings yet
- A Survey of Distributed Denial-Of-Service Attack, Prevention, and Mitigation TechniquesDocument33 pagesA Survey of Distributed Denial-Of-Service Attack, Prevention, and Mitigation TechniquesReveng EngNo ratings yet
- DNSSEC For Cyber Forensics: Research Open AccessDocument14 pagesDNSSEC For Cyber Forensics: Research Open AccessFadli WijayaNo ratings yet
- Lecture Two Threats To Information Systems and Computer SecurityDocument15 pagesLecture Two Threats To Information Systems and Computer SecuritynzumahezronNo ratings yet
- Colonial Pipeline Ransomware Attack 2021 11122023 053758pmDocument8 pagesColonial Pipeline Ransomware Attack 2021 11122023 053758pmAkhtar HussainNo ratings yet
- Mitigation of Denial of Service AttackDocument7 pagesMitigation of Denial of Service AttackZatin GuptaNo ratings yet
- 2018 - The Dynamic Analysis of WannaCry RansomwareDocument8 pages2018 - The Dynamic Analysis of WannaCry Ransomwareaulia rachmaNo ratings yet
- Distributed Hop Count Filtering and Round Trip Time Technique To Combat Ip Spoofing Based Distributed Denial of Service (Ddos) AttacksDocument10 pagesDistributed Hop Count Filtering and Round Trip Time Technique To Combat Ip Spoofing Based Distributed Denial of Service (Ddos) Attackstuan_fet2005No ratings yet
- Network Security: Compromises and Countermeasures: Key WordsDocument6 pagesNetwork Security: Compromises and Countermeasures: Key Wordsabdel_lakNo ratings yet
- Injection Attacks Reloaded: Tunnelling Malicious Payloads Over DNSDocument19 pagesInjection Attacks Reloaded: Tunnelling Malicious Payloads Over DNSayviwurbayviwurbNo ratings yet
- Cyber SecurityDocument17 pagesCyber SecurityanjulNo ratings yet
- Cloud Threat and Security Concern: International Journal of Emerging Trends & Technology in Computer Science (IJETTCS)Document5 pagesCloud Threat and Security Concern: International Journal of Emerging Trends & Technology in Computer Science (IJETTCS)International Journal of Application or Innovation in Engineering & ManagementNo ratings yet
- Denial of Service DoS Attacks and Their PDFDocument4 pagesDenial of Service DoS Attacks and Their PDFmohammad ramdhanNo ratings yet
- Unit - IDocument15 pagesUnit - IashaNo ratings yet
- 1.4.1.1 Lab - Researching Network Attacks and Security Audit ToolsDocument4 pages1.4.1.1 Lab - Researching Network Attacks and Security Audit Toolssafwan eshamasulNo ratings yet
- Aamir-Zaidi2019 Article DDoSAttackDetectionWithFeatureDocument25 pagesAamir-Zaidi2019 Article DDoSAttackDetectionWithFeatureadfafNo ratings yet
- Detecting Service Violations and Dos AttacksDocument13 pagesDetecting Service Violations and Dos AttacksPrithiv SubramaniamNo ratings yet
- An Integrated Approach For Defending Against Distributed Denial-Of-Service (Ddos) AttacksDocument6 pagesAn Integrated Approach For Defending Against Distributed Denial-Of-Service (Ddos) AttacksgdeepthiNo ratings yet
- IR105+WES STUDENT SLIDES 508cDocument33 pagesIR105+WES STUDENT SLIDES 508cmariduenanNo ratings yet
- Volume Based Ddos Attacks and How To Mitigate Them: Alysson Celso de Almeida SilvaDocument6 pagesVolume Based Ddos Attacks and How To Mitigate Them: Alysson Celso de Almeida SilvaAlyssonAlmeidaNo ratings yet
- Mid Term Exam / Fall 2022 Question No 1Document6 pagesMid Term Exam / Fall 2022 Question No 1usama hanifNo ratings yet
- Sec21 SquarcinaDocument19 pagesSec21 SquarcinaChristian TellengNo ratings yet
- Sad Lab All ExptDocument53 pagesSad Lab All ExptadtiiNo ratings yet
- Loddos Ddos Attacks Evaluation ReportDocument20 pagesLoddos Ddos Attacks Evaluation ReportDewa AsmaraNo ratings yet
- Attack TrendsDocument7 pagesAttack TrendssuyashjainNo ratings yet
- M.C.a. (Sem - IV) Paper - III - Network SecurityDocument197 pagesM.C.a. (Sem - IV) Paper - III - Network SecurityBalaji RamNo ratings yet
- Osi Security Architecture Tcs 619Document17 pagesOsi Security Architecture Tcs 619Asit KumarNo ratings yet
- An On Premises Defense Is The Cornerstone For Multilayer Ddos ProtectionDocument7 pagesAn On Premises Defense Is The Cornerstone For Multilayer Ddos Protectionnihadabed77No ratings yet
- Product Data Sheet0900aecd804dc62dDocument5 pagesProduct Data Sheet0900aecd804dc62dnihadabed77No ratings yet
- PE8216/PE8324: Energy Intelligence SolutionsDocument11 pagesPE8216/PE8324: Energy Intelligence Solutionsnihadabed77No ratings yet
- Caching Solution For Save Isp BandwidthDocument15 pagesCaching Solution For Save Isp Bandwidthnihadabed77No ratings yet
- H4IRPTZ DP Installation Guide ENDocument29 pagesH4IRPTZ DP Installation Guide ENnihadabed77No ratings yet
- Idirect X3 Evolution Series Activation Procedure: Step 1: Install and Upgrade Your Modem Firmware and ConfigurationDocument2 pagesIdirect X3 Evolution Series Activation Procedure: Step 1: Install and Upgrade Your Modem Firmware and Configurationnihadabed77No ratings yet
- Broadband Wireless Access Point Solution (AP/Client/Bridge/Repeater) Model: APE24Document2 pagesBroadband Wireless Access Point Solution (AP/Client/Bridge/Repeater) Model: APE24nihadabed77No ratings yet
- NJT5116FDocument2 pagesNJT5116Fnihadabed77No ratings yet
- CTI VCS CONTRL K9 - DatasheetDocument7 pagesCTI VCS CONTRL K9 - Datasheetnihadabed77No ratings yet
- Trango Wireless Backhaul SolutionsDocument55 pagesTrango Wireless Backhaul Solutionsnihadabed77No ratings yet
- Installation Guide: Global CacheDocument48 pagesInstallation Guide: Global Cachenihadabed77No ratings yet
- Brocade 6510 DatasheetDocument7 pagesBrocade 6510 DatasheetnashwanNo ratings yet
- Data and Computer Communications: Tenth Edition by William StallingsDocument17 pagesData and Computer Communications: Tenth Edition by William StallingsChristian XavierNo ratings yet
- CN Question Bank Unit-3-4Document2 pagesCN Question Bank Unit-3-447Parth PatelNo ratings yet
- Girish P.P Mobile Number: + 91 9901461560 (Bangalore) Mobile Number: + 91-9995751116 (Kerala) Skype Id: Girishharidas1989Document5 pagesGirish P.P Mobile Number: + 91 9901461560 (Bangalore) Mobile Number: + 91-9995751116 (Kerala) Skype Id: Girishharidas1989asifzharafNo ratings yet
- Agilent Rid UrsDocument13 pagesAgilent Rid Ursjeyapragash RamadassNo ratings yet
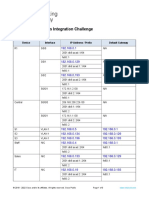
- 17.8.2 Packet Tracer - Skills Integration Challenge 1Document3 pages17.8.2 Packet Tracer - Skills Integration Challenge 1Anant GargNo ratings yet
- 01 ENSP Study GuideDocument3 pages01 ENSP Study GuideAbdullah Akkam100% (1)
- Lentronics JunglePAX Brochure 31950B EN 202105Document12 pagesLentronics JunglePAX Brochure 31950B EN 202105Bruno MarceloNo ratings yet
- NKN BrochureDocument6 pagesNKN BrochurephazarikaNo ratings yet
- HikCentral Professional V1.6.0 - DatasheetDocument33 pagesHikCentral Professional V1.6.0 - DatasheetdieterchNo ratings yet
- Quick Start Guide - OTV v1.4.2Document40 pagesQuick Start Guide - OTV v1.4.2martono693100% (1)
- COC3Document72 pagesCOC3Aprilyn Martelino Obregon100% (1)
- Networking Concepts and HardwareDocument28 pagesNetworking Concepts and HardwareOrlando FelixNo ratings yet
- Web Info NetDocument25 pagesWeb Info NetHSFXHFHXNo ratings yet
- Huawei Certification Written Exam GuideDocument19 pagesHuawei Certification Written Exam Guideayash smartNo ratings yet
- Pass4sure 312-50v9 DumpsDocument6 pagesPass4sure 312-50v9 Dumpsjpince0% (1)
- Lwip PortDocument10 pagesLwip PortKarthik KichuNo ratings yet
- Aviat Networks ProVision BrochureDocument8 pagesAviat Networks ProVision BrochureAviat NetworksNo ratings yet
- Analysis To Improve Gray-Hole Attack Minimization in MANET: AbstractDocument6 pagesAnalysis To Improve Gray-Hole Attack Minimization in MANET: AbstracttanpreetsinghNo ratings yet
- Samsung SCX 4623FDocument121 pagesSamsung SCX 4623FIonut TanasescuNo ratings yet
- File Distribution Instant Messaging Video Streaming Distributed ComputingDocument7 pagesFile Distribution Instant Messaging Video Streaming Distributed ComputingRamanathan SunderNo ratings yet
- ONAP PNF Plug and PlayDocument43 pagesONAP PNF Plug and PlayCapri CaviedesNo ratings yet
- Curriculum Vitae: Name: Address: Mobile: At:Post: AstagiDocument3 pagesCurriculum Vitae: Name: Address: Mobile: At:Post: AstagiVinod BabuNo ratings yet