Professional Documents
Culture Documents
01-12 PBR Configuration
01-12 PBR Configuration
Uploaded by
Juan Martinez GarciaCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
01-12 PBR Configuration
01-12 PBR Configuration
Uploaded by
Juan Martinez GarciaCopyright:
Available Formats
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
12 PBR Configuration
12.1 Overview of PBR
12.2 Licensing Requirements and Limitations for PBR
12.3 Configuring PBR
12.4 Configuring NQA for PBR
12.5 Configuration Examples for PBR
12.1 Overview of PBR
Definition
Policy-based routing (PBR) allows switches to select routes based on user-defined
policies, and it takes precedence over direct routes, static routes, and routes
generated by dynamic routing protocols. After PBR is configured on the device, if
the received packets (including Layer 2 packets) match PBR rules, the device
forwards the packets according to the rules. If the packets do not match PBR rules,
the device forwards the packets according to the destination address of the
packets.
NOTE
The main differences between PBR and routing policies are:
● PBR changes the forwarding path of packets based on user-defined policies instead of
based on the routes in an IP routing table.
● Routing policies change the forwarding path of packets by filtering routes and setting
route attributes. For example, route attributes (including reachability) can be set to
change the forwarding path of network traffic.
Purpose
Traditionally, to determine the routes used to forward packets, a switch searches
its IP routing table based on the destination address carried in the packets. To
allow switches to route packets based on user-defined policies, PRB can be
configured.
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1031
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
Benefits
PBR has the following advantages:
● Allows network administrators to define policies for routing packets,
improving route selection flexibility.
● Enables different data flows to be forwarded on different links, increasing link
efficiency.
● Allows cost-effective links to be used for transmitting service data without
affecting service quality, reducing the cost of enterprise data services.
12.2 Licensing Requirements and Limitations for PBR
Involved Network Elements
Other network elements are not required.
Licensing Requirements
PBR is a basic feature of a switch and is not under license control.
Feature Support in V200R020C10
All models of S300, S500, S2700, S5700, and S6700 series switches support PBR.
NOTE
For details about software mappings, visit Info-Finder and search for the desired product
model.
Feature Limitations
On the S2720-EI, S5720I-SI, S5720-LI, S2730S-S, S5735-L1,S300, S5735-L, S5735S-
L, S5735S-L1, S5735S-L-M, S5720S-LI, S5720S-SI, S5720-SI, S5735-S, S500, S5735-
S-I, and S5735S-S, PBR takes effect only for the packets forwarded at Layer 3 but
not for the packets forwarded at Layer 2. On other switch models, PBR takes effect
for the packets forwarded at both Layer 2 and Layer 3.
12.3 Configuring PBR
Context
After a redirection action is configured, a switch redirects packets matching traffic
classification rules to a specified next-hop address.
A traffic policy containing the redirection action can be used globally, on an
interface, or in a VLAN in the inbound direction.
Pre-configuration Tasks
Before configuring PBR, complete the following tasks:
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1032
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
● Configure IP addresses for interfaces and configure routing protocols to
ensure connectivity.
● Configure an ACL to classify traffic.
Procedure
1. Configure a traffic classifier.
For details about configuring a traffic classifier, see Configuring a Traffic
Classifier in "MQC Configuration" in the S300, S500, S2700, S5700, and S6700
V200R020C10 Configuration Guide - QoS.
2. Configure a traffic behavior.
a. Run traffic behavior behavior-name
A traffic behavior is created and the traffic behavior view is displayed;
alternatively, the view of an existing traffic behavior is displayed.
b. Run the following commands as required.
▪ Run redirect [ remote ] [ vpn-instance vpn-instance-name ] ip-
nexthop { ip-address [ track-nqa admin-name test-name ] } &<1-4>
[ forced | low-precedence ] *
The switch is configured to redirect packets matching traffic
classification rules to the specified next-hop IP address.
A maximum of four next-hop IP addresses can be configured in a
traffic behavior. If multiple next-hop IP addresses are configured, the
switch determines the active and standby links according to the
sequence in which next-hop IP addresses were configured. The next-
hop IP address that was configured first has the highest priority and
the link for this next hop is used as the active link. Links for other
next hops are used as standby links. If the active link goes Down, the
link for the next hop with the highest priority functions as the new
active link to transmit traffic. If the previous active link recovers from
the fault, traffic is switched back to this previous active link.
NOTE
Configuring redirection can implement PBR.
If the low-precedence parameter is specified, the priority of redirection-
based PBR is lowered below that of statically configured routes or routes
generated by dynamic routing protocols (rather than being higher by
default).
▪ Run redirect [ remote ] [ vpn-instance vpn-instance-name ] ipv6-
nexthop { ipv6-address | link-local link-local-address interface
interface-type interface-number } &<1-4> [ forced ]
The switch is configured to redirect IPv6 packets matching traffic
classification rules to the configured next-hop address.
▪ Run redirect [ vpn-instance vpn-instance-name ] ip-multihop
{ nexthop ip-address } &<2-4>
Or run redirect [ vpn-instance vpn-instance-name ] ip-multihop
acl-ip-pool-name
The switch is configured to redirect packets matching traffic
classification rules to one of the configured next hops.
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1033
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
If multiple next hops are specified, the switch redirects packets
through equal-cost routes for load balancing.
If the outbound interface corresponding to a next-hop IP address
goes Down or a route changes, the switch transmits traffic to the
outbound interface corresponding to an available next hop.
If the switch has no ARP entry matching the specified next-hop IP
address, the redirect ip-multihop command can be used but
redirection does not take effect (the switch continues to forward
packets to the original destination) until the switch obtains the
corresponding ARP entry.
▪ Run redirect [ vpn-instance vpn-instance-name ] ipv6-multihop
{ ipv6-address | link-local link-local-address interface interface-type
interface-number } &<2-4>
Or run redirect [ vpn-instance vpn-instance-name ] ipv6-multihop
acl6-ip-pool-name
The switch is configured to redirect IPv6 packets matching traffic
classification rules to one of the configured next hops.
If multiple next hops are specified, the switch redirects packets
through equal-cost routes for load balancing.
c. (Optional) Run statistic enable
The traffic statistics collection function is enabled.
d. Run quit
Exit from the traffic behavior view.
e. Run quit
Exit from the system view.
3. Configure a traffic policy.
For details about configuring a traffic policy, see Configuring a Traffic Policy
in "MQC Configuration" in the S300, S500, S2700, S5700, and S6700
V200R020C10 Configuration Guide - QoS.
4. Apply the traffic policy.
– Apply a traffic policy to an interface.
i. Run system-view
The system view is displayed.
ii. Run interface interface-type interface-number
The interface view is displayed.
iii. Run traffic-policy policy-name inbound
A traffic policy is applied to the inbound direction of the interface.
– Apply a traffic policy to a VLAN.
i. Run system-view
The system view is displayed.
ii. Run vlan vlan-id
The VLAN view is displayed.
iii. Run traffic-policy policy-name inbound
A traffic policy is applied to the VLAN.
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1034
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
The system then applies the policy to the incoming packets that are
sent from the VLAN and match traffic classification rules.
– Apply a traffic policy globally.
i. Run system-view
The system view is displayed.
ii. Run traffic-policy policy-name global inbound [ slot slot-id ]
A traffic policy is applied globally.
Verifying the Configuration
● Run the display traffic classifier user-defined [ classifier-name ] command
to check the traffic classifier configuration.
● Run the display traffic behavior user-defined [ behavior-name ] command
to check the traffic behavior configuration.
● Run the display traffic policy user-defined [ policy-name [ classifier
classifier-name ] ] command to check the configuration of a specified user-
defined traffic policy.
● Run the display traffic-applied [ interface [ interface-type interface-
number ] | vlan [ vlan-id ] ] { inbound | outbound } [ verbose ] command to
check information about ACL-based simplified and MQC-based traffic policies
applied to the system, a VLAN, or an interface.
NOTE
The display traffic-applied command cannot be used to check information about
ACL-based simplified and MQC-based traffic policies applied to a sub-interface.
However, traffic policies can be applied to a sub-interface.
● Run the display traffic policy { interface [ interface-type interface-number
[.subinterface-number ] ] | vlan [ vlan-id ] | ssid-profile [ ssid-profile-name ]
| global } [ inbound | outbound ] command to check the traffic policy
configuration.
NOTE
Only the S5731-H, S5731-S, S5731S-H, S5731S-S, S5732-H, S6720-EI, S6720S-EI,
S6730-H, S6730S-H, S6730-S, and S6730S-S support sub-interfaces.
Only the S5731-H, S5731S-H, S5732-H, S6730S-H, and S6730-H support ssid-profile
[ ssid-profile-name ].
● Run the display traffic-policy applied-record [ policy-name ] command to
check the application records of a specified traffic policy.
12.4 Configuring NQA for PBR
Background
PBR allows switches to select paths and forward packets based on defined policies.
However, PBR lacks a fault detection mechanism. In a scenario where the link for
the redirection next hop becomes faulty, PBR becomes ineffective only after the
ARP entry of the redirection next hop is aged. As a result, services cannot be
immediately switched to another link, causing service interruptions.
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1035
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
Network quality analysis (NQA) for PBR solves this issue by providing a fault
detection mechanism for PBR. In the same scenario, the next hop will become
ineffective immediately without waiting for the aging of its ARP entry. This is
because the NQA test identifies the fault. NQA for PBR helps shorten the service
interruption time and improve QoS.
Pre-configuration Tasks
Before configuring NQA for PBR, complete the following tasks:
● Configure IP addresses and routing protocols for interfaces to ensure
connectivity.
● Configure an ACL if the ACL needs to be used to classify traffic.
Procedure
1. Configure an ICMP NQA test instance.
a. Run system-view
The system view is displayed.
b. Run nqa test-instance admin-name test-name
An NQA test instance is created, and the test instance view is displayed.
c. Run test-type icmp
The test type is set to ICMP.
NOTE
When NQA is associated with PBR, only an ICMP NQA test instance can be used
to check whether a route from the source to the destination is reachable.
d. Run destination-address ipv4 ip-address
The destination address is set for the NQA test instance.
e. (Optional) Run frequency interval
The interval at which the NQA test instance automatically runs is set.
By default, no automatic test interval is set. The system performs the test
only once.
f. (Optional) Run probe-count number
The number of probes to be sent each time is set for the NQA test
instance.
By default, the number of probes to be sent each time is 3.
By sending multiple probes for an NQA test instance, the network quality
can be estimated more accurately based on the collected statistics.
g. (Optional) Run interval { milliseconds interval | seconds interval }
The interval at which probe packets are sent is set for the NQA test
instance.
For the default interval at which probe packets are sent, see the
command reference manual.
h. (Optional) Run timeout time
The timeout period of a probe is set for the NQA test instance.
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1036
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
By default, the timeout period of a probe for FTP test instances is 15s and
that for other test instances is 3s.
i. Set the NQA test instance startup mode as required to start the NQA test
instance.
▪ Run start now [ end { at [ yyyy/mm/dd ] hh:mm:ss | delay
{ seconds second | hh:mm:ss } | lifetime { seconds second |
hh:mm:ss } } ]
The NQA test instance is started immediately.
▪ Run start at [ yyyy/mm/dd ] hh:mm:ss [ end { at [ yyyy/mm/dd ]
hh:mm:ss | delay { seconds second | hh:mm:ss } | lifetime { seconds
second | hh:mm:ss } } ]
The NQA test instance is started at the specified time.
▪ Run start delay { seconds second | hh:mm:ss } [ end { at
[ yyyy/mm/dd ] hh:mm:ss | delay { seconds second | hh:mm:ss } |
lifetime { seconds second | hh:mm:ss } } ]
The NQA test instance is started after the specified delay.
j. Run quit
Return to the system view.
k. Run quit
Exit from the system view.
2. Configure a traffic classifier.
For details about configuring a traffic classifier, see Configuring a Traffic
Classifier in "MQC Configuration" in the S300, S500, S2700, S5700, and S6700
V200R020C10 Configuration Guide - QoS.
3. Configure a traffic behavior.
a. Run system-view
The system view is displayed.
b. Run traffic behavior behavior-name
A traffic behavior is created and the traffic behavior view is displayed;
alternatively, the existing traffic behavior view is displayed.
c. Run redirect [ remote ] [ vpn-instance vpn-instance-name ] ip-nexthop
{ ip-address [ track-nqa admin-name test-name ] } &<1-4> [ forced |
low-precedence ] *
The packets matching traffic classification rules are redirected to the
specified next hop, and association between PBR and the NQA test
instance is configured.
To configure association between PBR and the NQA test instance, specify
the track-nqa admin-name test-name parameter.
NOTE
In a given traffic behavior, a next-hop IP address can be bound to only one NQA
test instance.
On the switch, a maximum of eight NQA test instances can be bound.
d. (Optional) Run statistic enable
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1037
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
The traffic statistics collection function is enabled.
e. Run quit
Return to the system view.
f. Run quit
Exit from the system view.
4. Configure a traffic policy.
For details about configuring a traffic policy, see Configuring a Traffic Policy
in "MQC Configuration" in the S300, S500, S2700, S5700, and S6700
V200R020C10 Configuration Guide - QoS.
5. Apply the traffic policy.
– Apply the traffic policy to an interface.
i. Run system-view
The system view is displayed.
ii. Run interface interface-type interface-number
The interface view is displayed.
iii. Run traffic-policy policy-name inbound
The traffic policy is applied to the inbound direction of the interface.
– Apply the traffic policy to a VLAN.
i. Run system-view
The system view is displayed.
ii. Run vlan vlan-id
The VLAN view is displayed.
iii. Run traffic-policy policy-name inbound
The traffic policy is applied to the VLAN.
Subsequently, the system performs traffic policing on the incoming
packets that are sent from the VLAN and match traffic classification
rules.
– Apply the traffic policy globally.
i. Run system-view
The system view is displayed.
ii. Run traffic-policy policy-name global inbound [ slot slot-id ]
The traffic policy is applied globally.
Verifying the Configuration
● Run the display traffic classifier user-defined [ classifier-name ] command
to check the traffic classifier configuration.
● Run the display traffic behavior user-defined [ behavior-name ] command
to check the traffic behavior configuration.
● Run the display traffic policy user-defined [ policy-name [ classifier
classifier-name ] ] command to check the configuration of a specified user-
defined traffic policy.
● Run the display traffic-applied [ interface [ interface-type interface-
number ] | vlan [ vlan-id ] ] { inbound | outbound } [ verbose ] command to
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1038
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
check information about ACL-based simplified and MQC-based traffic policies
applied to the system, a VLAN, or an interface.
NOTE
The display traffic-applied command cannot be used to check information about
ACL-based simplified and MQC-based traffic policies applied to a sub-interface.
However, traffic policies can be applied to a sub-interface.
● Run the display traffic policy { interface [ interface-type interface-number
[.subinterface-number ] ] | vlan [ vlan-id ] | ssid-profile [ ssid-profile-name ]
| global } [ inbound | outbound ] command to check the traffic policy
configuration.
NOTE
Only the S5731-H, S5731-S, S5731S-H, S5731S-S, S5732-H, S6720-EI, S6720S-EI,
S6730-H, S6730S-H, S6730-S, and S6730S-S support sub-interfaces.
Only the S5731-H, S5731S-H, S5732-H, S6730S-H, and S6730-H support ssid-profile
[ ssid-profile-name ].
● Run the display traffic-policy applied-record [ policy-name ] command to
check the application records of a specified traffic policy.
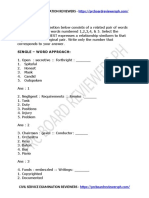
12.5 Configuration Examples for PBR
12.5.1 Example for Configuring PBR Based on IP Addresses
Networking Requirements
In Figure 12-1, the Switch on the aggregation layer is a Layer 3 forwarding device,
and an LSW on the access layer serves as the user gateway. There is a reachable
route between the Switch and LSW. The Switch is connected to two core routers
through two links: a high-speed link with the gateway 10.1.20.1/24 and a low-
speed link with the gateway 10.1.30.1/24.
The enterprise requires that the Switch forward packets from 192.168.100.0/24
and 192.168.101.0/24 to the core layer through the high-speed link and low-speed
link, respectively.
Figure 12-1 Networking diagram for configuring PBR
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1039
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
Configuration Roadmap
Implement PBR through redirection so that the Switch can provide differentiated
services. The configuration roadmap is as follows:
1. Create VLANs and configure interfaces to connect the enterprise' devices to
external network devices.
2. Configure ACL rules to separately match packets with source IP addresses
192.168.100.0/24 and 192.168.101.0/24.
3. Configure traffic classifiers and bind them to ACL rules so that the Switch can
differentiate packets.
4. Configure traffic behaviors to redirect the packets matching different rules to
10.1.20.1/24 and 10.1.30.1/24 separately.
5. Configure a traffic policy, bind it to the traffic classifiers and traffic behaviors,
and apply it to the inbound direction of GE0/0/3 to implement PBR.
Procedure
Step 1 Create VLANs and configure interfaces.
# Create VLANs 100 and 200 on the Switch.
<HUAWEI> system-view
[HUAWEI] sysname Switch
[Switch] vlan batch 100 200
Configure GE0/0/1, GE0/0/2, and GE0/0/3 on the Switch as trunk interfaces, and
add them to VLANs 100 and 200.
[Switch] interface gigabitethernet 0/0/1
[Switch-GigabitEthernet0/0/1] port link-type trunk
[Switch-GigabitEthernet0/0/1] port trunk allow-pass vlan 100 200
[Switch-GigabitEthernet0/0/1] quit
[Switch] interface gigabitethernet 0/0/2
[Switch-GigabitEthernet0/0/2] port link-type trunk
[Switch-GigabitEthernet0/0/2] port trunk allow-pass vlan 100 200
[Switch-GigabitEthernet0/0/2] quit
[Switch] interface gigabitethernet 0/0/3
[Switch-GigabitEthernet0/0/3] port link-type trunk
[Switch-GigabitEthernet0/0/3] port trunk allow-pass vlan 100 200
[Switch-GigabitEthernet0/0/3] quit
# Create VLANIF 100 and VLANIF 200, and configure IP addresses for them.
[Switch] interface vlanif 100
[Switch-Vlanif100] ip address 10.1.20.2 24
[Switch-Vlanif100] quit
[Switch] interface vlanif 200
[Switch-Vlanif200] ip address 10.1.30.2 24
[Switch-Vlanif200] quit
Step 2 Configure ACL rules.
# On the Switch, create advanced ACLs 3001 and 3002 to permit packets with
source IP addresses 192.168.100.0/24 and 192.168.101.0/24 respectively.
[Switch] acl 3001
[Switch-acl-adv-3001] rule permit ip source 192.168.100.0 0.0.0.255
[Switch-acl-adv-3001] quit
[Switch] acl 3002
[Switch-acl-adv-3002] rule permit ip source 192.168.101.0 0.0.0.255
[Switch-acl-adv-3002] quit
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1040
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
Step 3 Configure traffic classifiers.
# On the Switch, create traffic classifiers c1 and c2, and bind c1 to ACL 3001 and
c2 to ACL 3002.
[Switch] traffic classifier c1 operator or
[Switch-classifier-c1] if-match acl 3001
[Switch-classifier-c1] quit
[Switch] traffic classifier c2 operator or
[Switch-classifier-c2] if-match acl 3002
[Switch-classifier-c2] quit
Step 4 Configure traffic behaviors.
# On the Switch, create traffic behaviors b1 and b2 to redirect traffic to
10.1.20.1/24 and 10.1.30.1/24, respectively.
[Switch] traffic behavior b1
[Switch-behavior-b1] redirect ip-nexthop 10.1.20.1
[Switch-behavior-b1] quit
[Switch] traffic behavior b2
[Switch-behavior-b2] redirect ip-nexthop 10.1.30.1
[Switch-behavior-b2] quit
Step 5 Configure a traffic policy and apply it to an interface.
# On the Switch, create a traffic policy p1, and bind it to the traffic classifiers and
traffic behaviors.
[Switch] traffic policy p1
[Switch-trafficpolicy-p1] classifier c1 behavior b1
[Switch-trafficpolicy-p1] classifier c2 behavior b2
[Switch-trafficpolicy-p1] quit
# Apply the traffic policy p1 to the inbound direction of GE0/0/3.
[Switch] interface gigabitethernet 0/0/3
[Switch-GigabitEthernet0/0/3] traffic-policy p1 inbound
[Switch-GigabitEthernet0/0/3] return
Step 6 Verify the configuration.
# Check the ACL configuration.
<Switch> display acl 3001
Advanced ACL 3001, 1 rule
Acl's step is 5
rule 5 permit ip source 192.168.100.0 0.0.0.255
<Switch> display acl 3002
Advanced ACL 3002, 1 rule
Acl's step is 5
rule 5 permit ip source 192.168.101.0 0.0.0.255
# Check the traffic classifier configuration.
<Switch> display traffic classifier user-defined
User Defined Classifier Information:
Classifier: c2
Operator: OR
Rule(s) :if-match acl 3002
Classifier: c1
Operator: OR
Rule(s) : if-match acl 3001
Total classifier number is 2
# Check the traffic policy configuration.
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1041
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
<Switch> display traffic policy user-defined p1
User Defined Traffic Policy Information:
Policy: p1
Classifier: c1
Operator: OR
Behavior: b1
Redirect: no forced
Redirect ip-nexthop
10.1.20.1
Classifier: c2
Operator: OR
Behavior: b2
Redirect: no forced
Redirect ip-nexthop
10.1.30.1
----End
Configuration Files
● Switch configuration file
#
sysname Switch
#
vlan batch 100 200
#
acl number 3001
rule 5 permit ip source 192.168.100.0 0.0.0.255
acl number 3002
rule 5 permit ip source 192.168.101.0 0.0.0.255
#
traffic classifier c1 operator or
if-match acl 3001
traffic classifier c2 operator or
if-match acl 3002
#
traffic behavior b1
redirect ip-nexthop 10.1.20.1
traffic behavior b2
redirect ip-nexthop 10.1.30.1
#
traffic policy p1 match-order config
classifier c1 behavior b1
classifier c2 behavior b2
#
interface Vlanif100
ip address 10.1.20.2 255.255.255.0
#
interface Vlanif200
ip address 10.1.30.2 255.255.255.0
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 100 200
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 100 200
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 100 200
traffic-policy p1 inbound
#
return
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1042
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
12.5.2 Example for Configuring PBR
Networking Requirements
In Figure 12-2, enterprise users are dual-homed to external network devices
through the Switch. The Switch is connected to two core routers through two
links, a high-speed link with the gateway 10.1.30.1/24 and a low-speed link with
the gateway 10.1.20.1/24.
The enterprise requires that outgoing packets with IP precedences 4, 5, 6, and 7 be
transmitted on the high-speed link and outgoing packets with IP precedences 0, 1,
2, and 3 be transmitted on the low-speed link.
Figure 12-2 PBR networking
Configuration Roadmap
Implement PBR through redirection so that the Switch can provide differentiated
services. The configuration roadmap is as follows:
1. Create VLANs and configure interfaces to connect the enterprise' devices to
external network devices.
2. Configure ACL rules to separately match the packets with IP precedences of 4,
5, 6, and 7 and the packets with IP precedences of 0, 1, 2, and 3.
3. Configure traffic classifiers and bind them to ACL rules in the traffic classifiers
so that the Switch can differentiate packets.
4. Configure traffic behaviors to redirect the packets matching traffic
classification rules to 10.1.20.1/24 and 10.1.30.1/24 separately.
5. Configure a traffic policy, bind it to the traffic classifiers and traffic behaviors,
and apply it to the inbound direction of GE0/0/3 to implement PBR.
Procedure
Step 1 Create VLANs and configure interfaces.
# Create VLAN 100 and VLAN 200 on the Switch.
<HUAWEI> system-view
[HUAWEI] sysname Switch
[Switch] vlan batch 100 200
# Configure GE0/0/1, GE0/0/2, and GE0/0/3 on the Switch as trunk interfaces and
add them to VLAN 100 and VLAN 200.
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1043
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
[Switch] interface gigabitethernet 0/0/1
[Switch-GigabitEthernet0/0/1] port link-type trunk
[Switch-GigabitEthernet0/0/1] port trunk allow-pass vlan 100 200
[Switch-GigabitEthernet0/0/1] quit
[Switch] interface gigabitethernet 0/0/2
[Switch-GigabitEthernet0/0/2] port link-type trunk
[Switch-GigabitEthernet0/0/2] port trunk allow-pass vlan 100 200
[Switch-GigabitEthernet0/0/2] quit
[Switch] interface gigabitethernet 0/0/3
[Switch-GigabitEthernet0/0/3] port link-type trunk
[Switch-GigabitEthernet0/0/3] port trunk allow-pass vlan 100 200
[Switch-GigabitEthernet0/0/3] quit
NOTE
Configure the interface connecting the LSW to the Switch as a trunk interface and add it to
VLAN 100 and VLAN 200.
# Create VLANIF 100 and VLANIF 200 and configure IP addresses for them.
[Switch] interface vlanif 100
[Switch-Vlanif100] ip address 10.1.20.2 24
[Switch-Vlanif100] quit
[Switch] interface vlanif 200
[Switch-Vlanif200] ip address 10.1.30.2 24
[Switch-Vlanif200] quit
Step 2 Configure ACLs.
# Create advanced ACLs 3001 and 3002 on the Switch. ACL 3001 permits packets
with IP precedences of 0, 1, 2, and 3 and ACL 3002 permits packets with IP
precedences of 4, 5, 6, and 7.
[Switch] acl 3001
[Switch-acl-adv-3001] rule permit ip precedence 0
[Switch-acl-adv-3001] rule permit ip precedence 1
[Switch-acl-adv-3001] rule permit ip precedence 2
[Switch-acl-adv-3001] rule permit ip precedence 3
[Switch-acl-adv-3001] quit
[Switch] acl 3002
[Switch-acl-adv-3002] rule permit ip precedence 4
[Switch-acl-adv-3002] rule permit ip precedence 5
[Switch-acl-adv-3002] rule permit ip precedence 6
[Switch-acl-adv-3002] rule permit ip precedence 7
[Switch-acl-adv-3002] quit
Step 3 Configure traffic classifiers.
On the Switch, create traffic classifiers c1 and c2, and bind c1 to ACL 3001 and c2
to ACL 3002.
[Switch] traffic classifier c1 operator and
[Switch-classifier-c1] if-match acl 3001
[Switch-classifier-c1] quit
[Switch] traffic classifier c2 operator and
[Switch-classifier-c2] if-match acl 3002
[Switch-classifier-c2] quit
Step 4 Configure traffic behaviors.
# On the Switch, create traffic behaviors b1 and b2 to redirect traffic to
10.1.20.1/24 and 10.1.30.1/24, respectively.
[Switch] traffic behavior b1
[Switch-behavior-b1] redirect ip-nexthop 10.1.20.1
[Switch-behavior-b1] quit
[Switch] traffic behavior b2
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1044
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
[Switch-behavior-b2] redirect ip-nexthop 10.1.30.1
[Switch-behavior-b2] quit
Step 5 Configure a traffic policy and apply it to an interface.
# On the Switch, create a traffic policy p1, and bind it to the traffic classifiers and
traffic behaviors.
[Switch] traffic policy p1
[Switch-trafficpolicy-p1] classifier c1 behavior b1
[Switch-trafficpolicy-p1] classifier c2 behavior b2
[Switch-trafficpolicy-p1] quit
# Apply the traffic policy p1 to the inbound direction of GE0/0/3.
[Switch] interface gigabitethernet 0/0/3
[Switch-GigabitEthernet0/0/3] traffic-policy p1 inbound
[Switch-GigabitEthernet0/0/3] return
Step 6 Verify the configuration.
# Check the ACL configuration.
<Switch> display acl 3001
Advanced ACL 3001, 4 rules
Acl's step is 5
rule 5 permit ip precedence routine
rule 10 permit ip precedence priority
rule 15 permit ip precedence immediate
rule 20 permit ip precedence flash
<Switch> display acl 3002
Advanced ACL 3002, 4 rules
Acl's step is 5
rule 5 permit ip precedence flash-override
rule 10 permit ip precedence critical
rule 15 permit ip precedence internet
rule 20 permit ip precedence network
# Check the traffic classifier configuration.
<Switch> display traffic classifier user-defined
User Defined Classifier Information:
Classifier: c2
Operator: AND
Rule(s) : if-match acl 3002
Classifier: c1
Operator: AND
Rule(s) : if-match acl 3001
Total classifier number is 2
# Check the traffic policy configuration.
<Switch> display traffic policy user-defined p1
User Defined Traffic Policy Information:
Policy: p1
Classifier: c1
Operator: AND
Behavior: b1
Redirect: no forced
Redirect ip-nexthop
10.1.20.1
Classifier: c2
Operator: AND
Behavior: b2
Redirect: no forced
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1045
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
Redirect ip-nexthop
10.1.30.1
----End
Configuration Files
● Switch configuration file
#
sysname Switch
#
vlan batch 100 200
#
acl number 3001
rule 5 permit ip precedence routine
rule 10 permit ip precedence priority
rule 15 permit ip precedence immediate
rule 20 permit ip precedence flash
acl number 3002
rule 5 permit ip precedence flash-override
rule 10 permit ip precedence critical
rule 15 permit ip precedence internet
rule 20 permit ip precedence network
#
traffic classifier c1 operator and
if-match acl 3001
traffic classifier c2 operator and
if-match acl 3002
#
traffic behavior b1
redirect ip-nexthop 10.1.20.1
traffic behavior b2
redirect ip-nexthop 10.1.30.1
#
traffic policy p1 match-order config
classifier c1 behavior b1
classifier c2 behavior b2
#
interface Vlanif100
ip address 10.1.20.2 255.255.255.0
#
interface Vlanif200
ip address 10.1.30.2 255.255.255.0
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 100 200
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 100 200
#
interface GigabitEthernet0/0/3
port link-type trunk
port trunk allow-pass vlan 100 200
traffic-policy p1 inbound
#
return
12.5.3 Example for Configuring PBR to Import Traffic to the
Firewall in Bypass Mode
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1046
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
Networking Requirements
In Figure 12-3, enterprise users need to access the Internet through SwitchA (core
switch) and the router (access gateway).
To ensure the security of the enterprise's intranet, traffic entering the intranet
needs to be imported to the firewall in bypass mode.
Figure 12-3 Networking for configuring PBR to import traffic to the firewall in
bypass mode
Configuration Roadmap
The configuration roadmap is as follows:
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1047
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
● Configure an IP address for each interface and configure a routing protocol
between the switch and firewall to ensure that there is a reachable route.
● Configure PBR on SwitchA to redirect traffic to the firewall for security
detection. Traffic that is sent from the external network to the enterprise
intranet will be redirected.
NOTE
This example provides only the switch configuration. For the firewall configuration, see the
firewall documentation.
Procedure
Step 1 Configure an IP address for each interface on SwitchA and the firewall, and
configure a routing protocol on SwitchA.
# Assign an IP address to each interface of SwitchA. By default, a switch interface
is a Layer 2 interface. Before configuring an IP address for a switch interface, run
the undo portswitch command to change the interface to a Layer 3 interface.
<HUAWEI> system-view
[HUAWEI] sysname SwitchA
[SwitchA] interface gigabitethernet 0/0/1
[SwitchA-GigabitEthernet0/0/1] undo portswitch
[SwitchA-GigabitEthernet0/0/1] ip address 10.1.1.2 24
[SwitchA-GigabitEthernet0/0/1] quit
[SwitchA] interface gigabitethernet 0/0/2
[SwitchA-GigabitEthernet0/0/2] undo portswitch
[SwitchA-GigabitEthernet0/0/2] ip address 10.1.20.1 24
[SwitchA-GigabitEthernet0/0/2] quit
[SwitchA] interface gigabitethernet 0/0/3
[SwitchA-GigabitEthernet0/0/3] undo portswitch
[SwitchA-GigabitEthernet0/0/3] ip address 10.1.10.6 24
[SwitchA-GigabitEthernet0/0/3] quit
[SwitchA] interface gigabitethernet 0/0/4
[SwitchA-GigabitEthernet0/0/4] undo portswitch
[SwitchA-GigabitEthernet0/0/4] ip address 10.1.11.6 24
[SwitchA-GigabitEthernet0/0/4] quit
# Configure a routing protocol on SwitchA to ensure Layer 3 connectivity. OSPF is
used as an example.
Generally, two OSPF processes are configured on the firewall to advertise uplink
and downlink network segments. Therefore, two OSPF processes need to be
configured on SwitchA.
[SwitchA] ospf 100
[SwitchA-ospf-100] area 0
[SwitchA-ospf-100-area-0.0.0.0] network 10.1.1.0 0.0.0.255
[SwitchA-ospf-100-area-0.0.0.0] network 10.1.10.0 0.0.0.255
[SwitchA-ospf-100-area-0.0.0.0] quit
[SwitchA-ospf-100] quit
[SwitchA] ospf 200
[SwitchA-ospf-200] area 0
[SwitchA-ospf-200-area-0.0.0.0] network 10.1.11.0 0.0.0.255
[SwitchA-ospf-200-area-0.0.0.0] network 10.1.20.0 0.0.0.255
[SwitchA-ospf-200-area-0.0.0.0] quit
[SwitchA-ospf-200] quit
Step 2 Configure PBR on SwitchA to redirect traffic to the firewall for security detection.
Traffic that is sent from the external network to the enterprise intranet will be
redirected.
# Configure a traffic classifier to match all traffic.
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1048
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
[SwitchA] traffic classifier c1
[SwitchA-classifier-c1] if-match any
[SwitchA-classifier-c1] quit
# Configure a traffic behavior to redirect matching traffic to the firewall (with the
next-hop address 10.1.10.5).
[SwitchA] traffic behavior b1
[SwitchA-behavior-b1] redirect ip-nexthop 10.1.10.5
[SwitchA-behavior-b1] quit
# Configure a traffic policy.
[SwitchA] traffic policy p1
[SwitchA-trafficpolicy-p1] classifier c1 behavior b1
[SwitchA-trafficpolicy-p1] quit
# Apply the traffic policy to the inbound direction of GigabitEthernet0/0/1 on
SwitchA.
[SwitchA] interface gigabitethernet 0/0/1
[SwitchA-GigabitEthernet0/0/1] traffic-policy p1 inbound
[SwitchA-GigabitEthernet0/0/1] quit
[SwitchA] quit
Step 3 Verify the configuration.
# Check the traffic classifier configuration.
<SwitchA> display traffic classifier user-defined c1
User Defined Classifier Information:
Classifier: c1
Operator: AND
Rule(s) : if-match any
# Check the traffic behavior configuration.
<SwitchA> display traffic behavior user-defined b1
User Defined Behavior Information:
Behavior: b1
Redirect: no forced
Redirect ip-nexthop
10.1.10.5
# Check the traffic policy configuration.
<SwitchA> display traffic policy user-defined p1
User Defined Traffic Policy Information:
Policy: p1
Classifier: c1
Operator: AND
Behavior: b1
Redirect: no forced
Redirect ip-nexthop
10.1.10.5
# Check the traffic policy record.
<SwitchA> display traffic-policy applied-record
#
-------------------------------------------------
Policy Name: p1
Policy Index: 0
Classifier:c1 Behavior:b1
-------------------------------------------------
*interface GigabitEthernet0/0/1
traffic-policy p1 inbound
slot 0 : success
-------------------------------------------------
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1049
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
Policy total applied times: 1.
#
----End
Configuration Files
● SwitchA configuration file
#
sysname SwitchA
#
traffic classifier c1 operator and
if-match any
#
traffic behavior b1
redirect ip-nexthop 10.1.10.5
#
traffic policy p1 match-order config
classifier c1 behavior b1
#
interface GigabitEthernet0/0/1
undo portswitch
ip address 10.1.1.2 255.255.255.0
traffic-policy p1 inbound
#
interface GigabitEthernet0/0/2
undo portswitch
ip address 10.1.20.1 255.255.255.0
#
interface GigabitEthernet0/0/3
undo portswitch
ip address 10.1.10.6 255.255.255.0
#
interface GigabitEthernet0/0/4
undo portswitch
ip address 10.1.11.6 255.255.255.0
#
ospf 100
area 0.0.0.0
network 10.1.1.0 0.0.0.255
network 10.1.10.0 0.0.0.255
#
ospf 200
area 0.0.0.0
network 10.1.11.0 0.0.0.255
network 10.1.20.0 0.0.0.255
#
return
12.5.4 Example for Configuring NQA for PBR
Networking Requirements
In Figure 12-4, an enterprise uses SwitchA as an aggregation switch and access
switch LSW as a user gateway. There are reachable routes between SwitchA and
LSW. SwitchA connects to two core switches, SwitchB and SwitchC, through a
high-speed link with the gateway 10.1.20.1/24 and a low-speed link with the
gateway 10.1.30.1/24, respectively. A default route has been configured on
SwitchA to ensure that traffic is transmitted through the high-speed link by
default. The enterprise has the following requirements:
● Use PBR to direct packets with the source IP address 192.168.101.0/24 to the
low-speed link. This is to reduce the bandwidth pressure on the high-speed
link.
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1050
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
● If the low-speed link becomes faulty, packets with the source IP address
192.168.101.0/24 must be rapidly switched back to the high-speed link to
minimize service interruption caused by the link fault.
Figure 12-4 Configuring NQA for PBR
Configuration Roadmap
The configuration roadmap is as follows:
1. Create VLANs and configure interfaces to connect the enterprise' devices to
external network devices.
2. Configure an NQA test instance to detect low-speed link quality. This
configuration provides a fault detection mechanism for PBR.
3. Configure an ACL to match packets with the source address 192.168.101.0/24
that need to be directed to the low-speed link.
4. Configure a traffic classifier and bind it to the ACL so that SwitchA can
differentiate packets.
5. Configure a traffic behavior to redirect packets with the source IP address
192.168.101.0/24 to 10.1.30.1 and configure the NQA test instance for PBR.
6. Configure a traffic policy, bind it to the traffic classifier and traffic behavior,
and apply it to the inbound direction of GE0/0/3 on SwitchA to associate NQA
with PBR.
Procedure
Step 1 Specify the VLANs to which interfaces belong.
# Configure SwitchA. The configurations of SwitchB and SwitchC are similar and
are not mentioned here.
<HUAWEI> system-view
[HUAWEI] sysname SwitchA
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1051
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
[SwitchA] vlan batch 100 200
[SwitchA] interface gigabitethernet 0/0/1
[SwitchA-GigabitEthernet0/0/1] port link-type trunk
[SwitchA-GigabitEthernet0/0/1] port trunk allow-pass vlan 100
[SwitchA-GigabitEthernet0/0/1] quit
[SwitchA] interface gigabitethernet 0/0/2
[SwitchA-GigabitEthernet0/0/2] port link-type trunk
[SwitchA-GigabitEthernet0/0/2] port trunk allow-pass vlan 200
[SwitchA-GigabitEthernet0/0/2] quit
Step 2 Configure an IP address for each VLANIF interface.
# Configure SwitchA. The configurations of SwitchB and SwitchC are similar and
are not mentioned here.
[SwitchA] interface vlanif 100
[SwitchA-Vlanif100] ip address 10.1.20.2 24
[SwitchA-Vlanif100] quit
[SwitchA] interface vlanif 200
[SwitchA-Vlanif200] ip address 10.1.30.2 24
[SwitchA-Vlanif200] quit
Step 3 Configure an NQA test instance on SwitchA.
[SwitchA] nqa test-instance user test
[SwitchA-nqa-user-test] test-type icmp
[SwitchA-nqa-user-test] destination-address ipv4 10.1.30.1
[SwitchA-nqa-user-test] frequency 11
[SwitchA-nqa-user-test] probe-count 2
[SwitchA-nqa-user-test] interval seconds 5
[SwitchA-nqa-user-test] timeout 4
[SwitchA-nqa-user-test] start now
[SwitchA-nqa-user-test] quit
Step 4 Check the NQA test result on SwitchA.
[SwitchA] display nqa results test-instance user test
NQA entry(user, test) :testflag is active ,testtype is icmp
1 . Test 288 result The test is finished
Send operation times: 2 Receive response times: 2
Completion:success RTD OverThresholds number: 0
Attempts number:1 Drop operation number:0
Disconnect operation number:0 Operation timeout number:0
System busy operation number:0 Connection fail number:0
Operation sequence errors number:0 RTT Status errors number:0
Destination ip address:10.1.30.1
Min/Max/Average Completion Time: 3/4/3
Sum/Square-Sum Completion Time: 7/25
Last Good Probe Time: 2014-09-09 09:55:38.2
Lost packet ratio: 0 %
If the command output contains Completion:success and Lost packet ratio: 0 %,
the NQA test is successful and links are normal.
Step 5 Configure an ACL.
# Create an advanced ACL 3001 on SwitchA to permit packets with the source IP
address 192.168.101.0/24.
[SwitchA] acl 3001
[SwitchA-acl-adv-3001] rule permit ip source 192.168.101.0 0.0.0.255
[SwitchA-acl-adv-3001] quit
Step 6 Configure a traffic classifier.
# Create a traffic classifier c1 on SwitchA, and bind c1 to ACL 3001.
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1052
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
[SwitchA] traffic classifier c1 operator or
[SwitchA-classifier-c1] if-match acl 3001
[SwitchA-classifier-c1] quit
Step 7 Configure a traffic behavior.
# Create a traffic behavior b1 on SwitchA to redirect packets to 10.1.30.1, and
configure NQA for PBR.
[SwitchA] traffic behavior b1
[SwitchA-behavior-b1] redirect ip-nexthop 10.1.30.1 track-nqa user test
[SwitchA-behavior-b1] quit
Step 8 Configure a traffic policy and apply it to an interface.
# Create a traffic policy p1 on SwitchA, and bind it to the traffic classifier and
traffic behavior.
[SwitchA] traffic policy p1
[SwitchA-trafficpolicy-p1] classifier c1 behavior b1
[SwitchA-trafficpolicy-p1] quit
# Apply the traffic policy p1 to the inbound direction of GE0/0/3 on SwitchA.
[SwitchA] interface gigabitethernet 0/0/3
[SwitchA-GigabitEthernet0/0/3] traffic-policy p1 inbound
[SwitchA-GigabitEthernet0/0/3] return
Step 9 Verify the configuration.
# Check the ACL configuration.
<SwitchA> display acl 3001
Advanced ACL 3001, 1 rule
Acl's step is 5
rule 5 permit ip source 192.168.101.0 0.0.0.255
# Check the traffic classifier configuration.
<SwitchA> display traffic classifier user-defined
User Defined Classifier Information:
Classifier: c1
Operator: OR
Rule(s) : if-match acl 3001
Total classifier number is 1
# Check the traffic policy configuration.
<SwitchA> display traffic policy user-defined p1
User Defined Traffic Policy Information:
Policy: p1
Classifier: c1
Operator: OR
Behavior: b1
Redirect: no forced
Redirect ip-nexthop
10.1.30.1 track-nqa user test
The preceding command output shows that PBR on SwitchA has been associated
with NQA. If a link becomes faulty, PBR on SwitchA becomes ineffective
immediately without waiting for the aging of ARP entries. Subsequently, traffic is
forwarded according to the IP routing table on SwitchA.
----End
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1053
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
Configuration Files
● SwitchA configuration file
#
sysname SwitchA
#
vlan batch 100 200
#
acl number 3001
rule 5 permit ip source 192.168.101.0 0.0.0.255
#
traffic classifier c1 operator or
if-match acl 3001
#
traffic behavior b1
redirect ip-nexthop 10.1.30.1 track-nqa user test
#
traffic policy p1 match-order config
classifier c1 behavior b1
#
interface Vlanif100
ip address 10.1.20.2 255.255.255.0
#
interface Vlanif200
ip address 10.1.30.2 255.255.255.0
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 100
#
interface GigabitEthernet0/0/2
port link-type trunk
port trunk allow-pass vlan 200
#
interface GigabitEthernet0/0/3
traffic-policy p1 inbound
#
nqa test-instance user test
test-type icmp
destination-address ipv4 10.1.30.1
frequency 11
interval seconds 5
timeout 4
probe-count 2
start now
#
return
● SwitchB configuration file
#
sysname SwitchB
#
vlan batch 100
#
interface Vlanif100
ip address 10.1.20.1 255.255.255.0
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 100
#
return
● SwitchC configuration file
#
sysname SwitchC
#
vlan batch 200
#
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1054
S300, S500, S2700, S5700, and S6700 Series
Ethernet Switches
Configuration Guide - IP Unicast Routing 12 PBR Configuration
interface Vlanif200
ip address 10.1.30.1 255.255.255.0
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 200
#
return
Issue 03 (2022-06-27) Copyright © Huawei Technologies Co., Ltd. 1055
You might also like
- Configuring IP Unicast RoutingDocument8 pagesConfiguring IP Unicast Routingxcvbvcb cvbcvbvcNo ratings yet
- Research DocumentationDocument315 pagesResearch DocumentationAlf Gomez100% (1)
- MDT 2010 Setup Step by StepDocument35 pagesMDT 2010 Setup Step by StepDave ColemanNo ratings yet
- About Policy-Based RedirectDocument6 pagesAbout Policy-Based RedirectAvinashNo ratings yet
- Route Policy BasedDocument14 pagesRoute Policy BasedDavid Manson CáceresNo ratings yet
- BGP Flowspec Conceptual ArchitectureDocument26 pagesBGP Flowspec Conceptual ArchitecturemorpheusnaakNo ratings yet
- 2 IP Router Configuration: 2.1 in This ChapterDocument55 pages2 IP Router Configuration: 2.1 in This Chapterravi kantNo ratings yet
- ART Assignment FinalDocument5 pagesART Assignment FinalABU ANAS SIDDIKNo ratings yet
- Configuring IP Routing Protocol IndependentDocument28 pagesConfiguring IP Routing Protocol IndependentsonnyNo ratings yet
- PB RouteDocument6 pagesPB RouteEdgar NavarroNo ratings yet
- IP Static Route ConfigurationDocument8 pagesIP Static Route ConfigurationHakim QaradaghiNo ratings yet
- 5 продвинутых технологий Cisco, которые нужно знать: Ruslan Savchenko ведущийDocument50 pages5 продвинутых технологий Cisco, которые нужно знать: Ruslan Savchenko ведущийAnonymous OQhJsHNo ratings yet
- Inter AS MPLS VPN PDFDocument11 pagesInter AS MPLS VPN PDFSandeepChodhuryNo ratings yet
- Asa PBRDocument12 pagesAsa PBRpiyushhoteNo ratings yet
- Anurag Gautam: Mobile:+91-9536511773 Email IdDocument3 pagesAnurag Gautam: Mobile:+91-9536511773 Email IdAnurag GautamNo ratings yet
- Lecture 12 - Path Control Implementation Part 1Document48 pagesLecture 12 - Path Control Implementation Part 1Raynard RoopnarineNo ratings yet
- B l3vpn CG Asr9000 63xDocument200 pagesB l3vpn CG Asr9000 63xkinglive_scribNo ratings yet
- B l3vpn CG Asr9000 67xDocument242 pagesB l3vpn CG Asr9000 67xgx zoliNo ratings yet
- Configuring IP Routing Protocol-Independent Features: Use Variable-Length Subnet MasksDocument28 pagesConfiguring IP Routing Protocol-Independent Features: Use Variable-Length Subnet MaskskanakadurgaNo ratings yet
- Configuring Link Bundling On The Cisco ASR 9000 Series RouterDocument66 pagesConfiguring Link Bundling On The Cisco ASR 9000 Series Routeriqbal apriansyahNo ratings yet
- L2VPN Services Over Segment Routing For Traffic Engineering PolicyDocument50 pagesL2VPN Services Over Segment Routing For Traffic Engineering PolicyMuhammad Adel EsmailNo ratings yet
- Assignment 2 MasetwalDocument6 pagesAssignment 2 MasetwalEstifanos EndalewNo ratings yet
- Mpls VPN BasicDocument11 pagesMpls VPN BasicNlend IsraëlNo ratings yet
- Segment RoutingDocument8 pagesSegment RoutingjeteleprojsbcNo ratings yet
- Cisco 3750 Switch QOS Configuration GuideDocument132 pagesCisco 3750 Switch QOS Configuration Guidejames opioNo ratings yet
- Policy Based Routing in The Branch Arubaos 8.XDocument29 pagesPolicy Based Routing in The Branch Arubaos 8.XkarthikkumarkanniyappanNo ratings yet
- Policy Based Routing PBRDocument8 pagesPolicy Based Routing PBRminhphanhoang89No ratings yet
- Mpls VPN BasicDocument13 pagesMpls VPN BasicMohamed FarhaniNo ratings yet
- CN Lab 2022BCS005Document5 pagesCN Lab 2022BCS005Akshat NayakNo ratings yet
- Configuring A Basic MPLS VPN: Document ID: 13733Document12 pagesConfiguring A Basic MPLS VPN: Document ID: 13733jguillen82No ratings yet
- Mpls VPN BasicDocument13 pagesMpls VPN Basicsouly88No ratings yet
- Basic Mpls VPN ConfigDocument15 pagesBasic Mpls VPN ConfigvelramsenNo ratings yet
- MP VPN Ias OptabDocument44 pagesMP VPN Ias OptabalexNo ratings yet
- Deploying Cisco Service Provider Network Routing (642-883) : Exam DescriptionDocument2 pagesDeploying Cisco Service Provider Network Routing (642-883) : Exam DescriptionChavara MatekweNo ratings yet
- 3GPP LTE Radio Layer 2Document81 pages3GPP LTE Radio Layer 2Aniko AddafiNo ratings yet
- Unified MPLS Functionality, Features, and Configuration ExampleDocument16 pagesUnified MPLS Functionality, Features, and Configuration ExampleAndy BrogerNo ratings yet
- Ip Routerconfig NokiaDocument62 pagesIp Routerconfig NokiaOsama ZaidNo ratings yet
- A Hierarchical Multilayer Qos Routing System With Dynamic Sla ManagementDocument14 pagesA Hierarchical Multilayer Qos Routing System With Dynamic Sla ManagementosjuroNo ratings yet
- B Segment Routing CG Asr9000 65xDocument156 pagesB Segment Routing CG Asr9000 65xAndres CervantesNo ratings yet
- En Route v7 Ch04Document97 pagesEn Route v7 Ch04Nik IkhwanNo ratings yet
- Configuring OSPFDocument40 pagesConfiguring OSPFputakoNo ratings yet
- Quickspecs: Aruba 3810 Switch Series ModelsDocument30 pagesQuickspecs: Aruba 3810 Switch Series ModelstienNo ratings yet
- Dynamic Failover Between Two WAN Links - PacketLifeDocument10 pagesDynamic Failover Between Two WAN Links - PacketLifefqtsysNo ratings yet
- Cisco ASR 9000 Series Aggregation Services Router MPLS Layer 3 VPNDocument142 pagesCisco ASR 9000 Series Aggregation Services Router MPLS Layer 3 VPNdexonnNo ratings yet
- Iri PBR Default Nexthop RouteDocument6 pagesIri PBR Default Nexthop Routemmi.sohailNo ratings yet
- Interas Mpls VPNDocument34 pagesInteras Mpls VPNAmit Baran ChatterjeeNo ratings yet
- Clase 3 VRF, PBR & IpslaDocument58 pagesClase 3 VRF, PBR & IpslaOscar sanchezNo ratings yet
- CCNP ENCOR v8 Chapter & Final Exam Design DocumentsDocument19 pagesCCNP ENCOR v8 Chapter & Final Exam Design DocumentsManuel RojasNo ratings yet
- Lecture 7 Routing AlgorithmDocument16 pagesLecture 7 Routing AlgorithmavoybinodiniNo ratings yet
- B Release Notes Asr9k r742Document43 pagesB Release Notes Asr9k r742rkrao77No ratings yet
- Static Routing ConfigurationDocument3 pagesStatic Routing Configurationalimad0900No ratings yet
- Hoja de Datos Nokia 7210Document13 pagesHoja de Datos Nokia 7210Liliana BorotocheNo ratings yet
- Cisco Systems IOS XR 161522Document282 pagesCisco Systems IOS XR 161522Moisés MiguelNo ratings yet
- Summary - Cisco SD-WAN Operation and Deployment5Document1 pageSummary - Cisco SD-WAN Operation and Deployment5Velasco SebastiaoNo ratings yet
- CN 2022BCS005Document5 pagesCN 2022BCS005Akshat NayakNo ratings yet
- BlueCoat ISPDocument39 pagesBlueCoat ISPanh00No ratings yet
- iIOS NAT Load-Balancing With Optimized Edge Routing For Two Internet ConnectionsDocument7 pagesiIOS NAT Load-Balancing With Optimized Edge Routing For Two Internet ConnectionsCesar Rene Parada FloresNo ratings yet
- CN Lab 2022bcs035Document8 pagesCN Lab 2022bcs035Akshat NayakNo ratings yet
- Versatile Routing and Services with BGP: Understanding and Implementing BGP in SR-OSFrom EverandVersatile Routing and Services with BGP: Understanding and Implementing BGP in SR-OSNo ratings yet
- LEARN MPLS FROM SCRATCH PART-B: A Beginners guide to next level of networkingFrom EverandLEARN MPLS FROM SCRATCH PART-B: A Beginners guide to next level of networkingNo ratings yet
- LEARN MPLS FROM SCRATCH PART-A: A Beginner's Guide to Next Level of NetworkingFrom EverandLEARN MPLS FROM SCRATCH PART-A: A Beginner's Guide to Next Level of NetworkingNo ratings yet
- Cechl04-2.40 5Document36 pagesCechl04-2.40 5Francisco GNo ratings yet
- CSE Reviewer Part 4Document8 pagesCSE Reviewer Part 4AsukinNo ratings yet
- Lecture1 2013 AnnotatedDocument24 pagesLecture1 2013 Annotatedfatihy73No ratings yet
- DLL Reading Program Sy23 24Document2 pagesDLL Reading Program Sy23 24Mark BaniagaNo ratings yet
- DRA26 Warmachine ChasesDocument2 pagesDRA26 Warmachine ChasesSteve FilipettiNo ratings yet
- Activity - 6 Table SettingDocument22 pagesActivity - 6 Table SettingFaith Gregorio100% (1)
- AAC Java Lab 2017 June - OctDocument50 pagesAAC Java Lab 2017 June - OctNelson Raja100% (1)
- Lifelong Vitality Program Ingredient HighlightsDocument49 pagesLifelong Vitality Program Ingredient HighlightsJacqui Decker100% (1)
- Space Mouse (Rahul Raj)Document20 pagesSpace Mouse (Rahul Raj)Anurag MahajanNo ratings yet
- FertilizationDocument11 pagesFertilizationapi-303068393No ratings yet
- Photography and PhotoshopDocument4 pagesPhotography and PhotoshopEstefania IdrovoNo ratings yet
- Blue Prism Portal User GuideDocument5 pagesBlue Prism Portal User Guidebhavana2264No ratings yet
- Worksheet 2B-QP MS (Dynamics)Document9 pagesWorksheet 2B-QP MS (Dynamics)kolNo ratings yet
- ARTICLE - Find Your Car's Date of Manufacture (VIN) - Team-BHPDocument12 pagesARTICLE - Find Your Car's Date of Manufacture (VIN) - Team-BHParunsukesanNo ratings yet
- Enteral Nutrition Safety System With EnfitDocument12 pagesEnteral Nutrition Safety System With EnfitRenata OlmosNo ratings yet
- Polymers: Chemistry ProjectDocument20 pagesPolymers: Chemistry ProjectAtul Singh Arora80% (200)
- 1) New Firms Added: Amendment-3 To Approved List (W.e.f. 1 Jan-2021) Page 1 of 8Document8 pages1) New Firms Added: Amendment-3 To Approved List (W.e.f. 1 Jan-2021) Page 1 of 8Subrata MukherjeeNo ratings yet
- Vulcathene Product CatalogueDocument21 pagesVulcathene Product CatalogueFLYNAS LOGISTICSNo ratings yet
- Peter WalkerDocument24 pagesPeter WalkerGustavo de la O33% (3)
- Applicant - Student Name Father Name Course / Branch / YearDocument2 pagesApplicant - Student Name Father Name Course / Branch / Yearg c lallNo ratings yet
- Troubleshooting HUAWEI VPNDocument146 pagesTroubleshooting HUAWEI VPNeoweka100% (1)
- Presentation - India Entry Services SIRC 17062021 1 PDFDocument75 pagesPresentation - India Entry Services SIRC 17062021 1 PDFashok babuNo ratings yet
- CR 10260-1998-OtklDocument21 pagesCR 10260-1998-OtklVasko MandilNo ratings yet
- 1 CellsDocument4 pages1 CellsSheniqua GreavesNo ratings yet
- TechnicalDataSheet (TDS) BONDERITEL-GPPRODAG English 01082015Document2 pagesTechnicalDataSheet (TDS) BONDERITEL-GPPRODAG English 01082015carlos dominguez torresNo ratings yet
- A Coupling Capacitor Voltage Transformer RepresentDocument7 pagesA Coupling Capacitor Voltage Transformer RepresentLucas De MeloNo ratings yet
- Hemoglobin (American English)Document2 pagesHemoglobin (American English)Ana MariaNo ratings yet
- Financial Control of Public FundsDocument136 pagesFinancial Control of Public FundsDavid Abbam AdjeiNo ratings yet