Professional Documents
Culture Documents
Software Development Explained in Detail
Uploaded by
mohini aiyangar0 ratings0% found this document useful (0 votes)
20 views12 pagesprocedure
Copyright
© © All Rights Reserved
Available Formats
PPTX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this Documentprocedure
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
20 views12 pagesSoftware Development Explained in Detail
Uploaded by
mohini aiyangarprocedure
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
You are on page 1of 12
Software Development explained in Detail
• IEC 61508 Part 3 covers specific requirements for safety-related
software.
• As in other parts of the standard, a safety lifecycle is to be used as the
basis of requirements compliance.
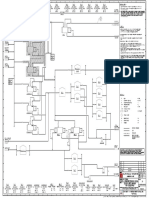
• Figure on next slide shows the software safety lifecycle which is an
expanded plan for Phase 9 of the overall safety lifecycle from Part 1
and is closely linked with the hardware lifecycle.
• As for the overall safety lifecycle, there are requirements for a
functional safety management plan and safety requirements
specification, including all verification and assessment activities
Software Development explained
• The major phases of the software safety lifecycle are shown in Figure
as below
Software Development explained in Detail
• Appropriate quality and safety assurance procedures must be
included. Each step of the software safety life cycle must be divided
into elementary activities with the functions, inputs and outputs
specified for each phase. The standard has complete details of
example software safety lifecycle. During each step of process,
appropriate “techniques and measures” must be used.
• The End User prefers to use “Certified Functional blocks” because all
the steps as detailed below are already taken care of and are
reviewed and certified by third party like TUV SUD.
Software Safety Requirements Specification
• The requirements for software safety shall be sufficiently detailed to
allow design and implementation and to allow a functional safety
assessment.
• Software developers should review the document to verify that it
contains sufficient details. It should be noted that this is often
another iterative process.
• The requirements must be clear, precise, verifiable, testable,
maintainable, and feasible. The requirements must also be
appropriate for the safety integrity level and traceable back to the
specification of the safety requirements of the safety-related system.
Software Validation Plan
• A plan must be set up to demonstrate that the software satisfies the
safety requirements set out in the specification. A combination of
analysis and testing techniques is allowed and the chosen techniques
must be specified in the plan which must consider:
• Required equipment.
• Who will be in charge of the validation & When it will be done
• The modes of operation to be validated like: Start Up, Reset, Manual,
automatic, Shut down
• Reasonably foreseeable abnormal conditions.
• Expected results and pass/fail criteria.
Integration and testing
• Tests of the integration between the hardware and software are
created during the design and development phases and specify the
following:
• Test cases and test data in manageable integration sets.
• Test environment, tools, and configuration.
• Test criteria.
• Procedures for corrective action on failure of test.
The integration testing results shall state each test and the pass/fail
results.
Software verification
• The software verification process tests and evaluates the results of
the software safety life cycle phases to insure they are correct and
consistent with the input information to those phases.
• A verification report must include an explanation of all activities and
results. Verification must be performed on:
• Software safety requirements, Software architecture design, Software
system design
• Software module design, Software source code, Data
• Software module testing, Software integration testing, Hardware
integration testing
• .Software safety requirements testing
Software Validation
• Software validation is done as an overall check to insure that the
software design meets the software safety requirements and
must include the appropriate documentation. The validation may be
done as part of overall system validation or it may be done separately
for the software.
• Testing must be the primary method of validation with analysis used
only to supplement. All tools used in the validation must be calibrated
and an approved, quality system must be in place.
• If validation is done separately for the software, the validation must
follow the software safety validation plan.
Operator Interface7
Check lists-Operator Interface
Item
Item Yes No N/A Comments
#
7.1 Has failure (loss) of the interface been considered?
Are alternate means available to bring the process
7.2 to
a safe state?
Are the following information shown on the
7.3 interface:
1 Where the process is in sequence?
2 Indication that a SIF action has occurred?
3 Indication that a SIF function is bypassed?
Indication that a SIF component or subsystem has
4 failed or is in a degraded state?
5 Status of field devices?
Is the update time appropriate for the application
7.4 under emergency conditions?
Have the operators been checked for color
7.5 blindness?
Is it possible to change SIS program logic from the
7.6 operator interface?
Do parameters that can be changed have security
7.7 access protection?
Check Lists- Communication
Item Item Yes No N/A Comments
#
Can communication failures have an adverse affect
9.1 on the SIS?
Are communication signals isolated from other
9.2 energy sources?
Has write protection been implemented so that
9.3 external systems cannot corrupt SIS memory?
If not, why?
Are interfaces robust enough to withstand EMI/RFI
9.4
And power disturbances?
Check Lists- Application Logic requirements
Item Item Yes No N/A Comments
#
Do all parties have a formal revision and release
12.1 control program for application logic?
Is the logic written in a clear and unambiguous
12.2 manner that is understandable to all parties?
12.3 Does the program include comments?
Within the logic specification, is there a clear and
12.4 concise statement of:
1 Each safety-related function (SIF)?
2 Information to be given to the operators?
The required action of each operator command,
3 including illegal or unexpected commands?
The communication requirements between the SIS
4 and other equipments?
The initial states for all internal variables and
5 external interfaces?
6 The required action for out-of-range variables?
Check List- Embedded Software
Item Item Yes No N/A Comments
#
Can the vendor provide evidence of an independent
13.1 safety assessment of all embedded software?
Has the software been used in similar applications
13.2 for a significant period of time?
Is the vendor software documented sufficiently for
13.3 the user to understand its operation and how to
implement the desired functionality?
Are the results of abnormal math operation fully
13.4 documented?
Are there procedures for the control of software
13.5 versions in use and the update of all similar systems?
For spare which contain firmware, is there a
13.6 procedure to insure all modules are compatible?
13.7 Can software versions in use easily be checked?
If errors are found in embedded software, are they
13.8 reported to and corrected by the vendor, and
incorporated into the SIS only after checking and testing
the corrected code?
Has the vendor made an impact analysis for software
13.9 corrections or changes?
Does the manufacturer provide competent technical
13.10 support?
You might also like
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeFrom EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeRating: 4 out of 5 stars4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingFrom EverandThe Little Book of Hygge: Danish Secrets to Happy LivingRating: 3.5 out of 5 stars3.5/5 (399)
- Activated Carbon For VOC PDFDocument4 pagesActivated Carbon For VOC PDFrocotroncosoNo ratings yet
- Scope of Feed - EgyptDocument16 pagesScope of Feed - Egyptmohini aiyangarNo ratings yet
- Guidance on storage, loading and unloading of petrol at terminalsDocument34 pagesGuidance on storage, loading and unloading of petrol at terminalsCalo AlcaloNo ratings yet
- SIF Tag SIF Description Required Achieved SIL RRF SIL RRFDocument1 pageSIF Tag SIF Description Required Achieved SIL RRF SIL RRFmohini aiyangarNo ratings yet
- CP SilDocument2 pagesCP Silmohini aiyangarNo ratings yet
- Simple Steps To SIL ValidationDocument2 pagesSimple Steps To SIL Validationmohini aiyangarNo ratings yet
- Principal Validation ChecklistDocument3 pagesPrincipal Validation Checklistmohini aiyangarNo ratings yet
- Truck VRU Inquiry FormDocument6 pagesTruck VRU Inquiry Formmohini aiyangarNo ratings yet
- Tuv CertificateDocument2 pagesTuv Certificatemohini aiyangarNo ratings yet
- Rules of ThumbDocument105 pagesRules of ThumbEllen DawitriNo ratings yet
- VRU Containment Systems GuideDocument6 pagesVRU Containment Systems GuideIdehen KelvinNo ratings yet
- Functional Safety Certification ApplicationDocument5 pagesFunctional Safety Certification Applicationmohini aiyangarNo ratings yet
- Document 1Document4 pagesDocument 1mohini aiyangarNo ratings yet
- SIL Validation ProcedureDocument2 pagesSIL Validation Proceduremohini aiyangarNo ratings yet
- Document 1Document4 pagesDocument 1mohini aiyangarNo ratings yet
- Partial Life CycleDocument1 pagePartial Life Cyclemohini aiyangarNo ratings yet
- SectionDocument23 pagesSectionmohini aiyangarNo ratings yet
- Functional Safety Certification ApplicationDocument5 pagesFunctional Safety Certification Applicationmohini aiyangarNo ratings yet
- WikaDocument13 pagesWikamohini aiyangarNo ratings yet
- Shoe Dog: A Memoir by the Creator of NikeFrom EverandShoe Dog: A Memoir by the Creator of NikeRating: 4.5 out of 5 stars4.5/5 (537)
- Never Split the Difference: Negotiating As If Your Life Depended On ItFrom EverandNever Split the Difference: Negotiating As If Your Life Depended On ItRating: 4.5 out of 5 stars4.5/5 (838)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceFrom EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceRating: 4 out of 5 stars4/5 (895)
- The Yellow House: A Memoir (2019 National Book Award Winner)From EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Rating: 4 out of 5 stars4/5 (98)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryFrom EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryRating: 3.5 out of 5 stars3.5/5 (231)
- Grit: The Power of Passion and PerseveranceFrom EverandGrit: The Power of Passion and PerseveranceRating: 4 out of 5 stars4/5 (588)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureFrom EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureRating: 4.5 out of 5 stars4.5/5 (474)
- On Fire: The (Burning) Case for a Green New DealFrom EverandOn Fire: The (Burning) Case for a Green New DealRating: 4 out of 5 stars4/5 (73)
- Team of Rivals: The Political Genius of Abraham LincolnFrom EverandTeam of Rivals: The Political Genius of Abraham LincolnRating: 4.5 out of 5 stars4.5/5 (234)
- The Emperor of All Maladies: A Biography of CancerFrom EverandThe Emperor of All Maladies: A Biography of CancerRating: 4.5 out of 5 stars4.5/5 (271)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersFrom EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersRating: 4.5 out of 5 stars4.5/5 (344)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaFrom EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaRating: 4.5 out of 5 stars4.5/5 (266)
- The Unwinding: An Inner History of the New AmericaFrom EverandThe Unwinding: An Inner History of the New AmericaRating: 4 out of 5 stars4/5 (45)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyFrom EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyRating: 3.5 out of 5 stars3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreFrom EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreRating: 4 out of 5 stars4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)From EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Rating: 4.5 out of 5 stars4.5/5 (119)
- Her Body and Other Parties: StoriesFrom EverandHer Body and Other Parties: StoriesRating: 4 out of 5 stars4/5 (821)
- SC27N11983 27042 1stCDDocument21 pagesSC27N11983 27042 1stCDjavier_khanNo ratings yet
- Acrow GASS Aluminium Product GuideDocument8 pagesAcrow GASS Aluminium Product GuideTrần AlanNo ratings yet
- Transaction-Related Audit Objective Possible Internal Controls Common Tests of ControlsDocument3 pagesTransaction-Related Audit Objective Possible Internal Controls Common Tests of ControlsJustin DavenportNo ratings yet
- استمارة تدقيقDocument29 pagesاستمارة تدقيقdr.alwahar1No ratings yet
- Ten Common Mistakes in Finite Element AnalysisDocument2 pagesTen Common Mistakes in Finite Element AnalysiscmuralisNo ratings yet
- EBR (Toyo Setal) KoM 27 June 2013 FPSO P-74 Rev1Document27 pagesEBR (Toyo Setal) KoM 27 June 2013 FPSO P-74 Rev1Allan SousaNo ratings yet
- Validation of Analytical Method: Ashok Suthar Regulatory Associate Regulatory Affairs Amneal PharmaceuticalsDocument40 pagesValidation of Analytical Method: Ashok Suthar Regulatory Associate Regulatory Affairs Amneal Pharmaceuticalsshashank786No ratings yet
- Notification HAL Operator PostsDocument7 pagesNotification HAL Operator PostsRohitRajakNo ratings yet
- PhilHealth - Electronic - Claims - Implementation - Guide For PECWS 2.5 (20190130)Document79 pagesPhilHealth - Electronic - Claims - Implementation - Guide For PECWS 2.5 (20190130)Jomelle WongNo ratings yet
- Iso IATF 16949 Upgrade Planner and Delta ChecklistDocument14 pagesIso IATF 16949 Upgrade Planner and Delta ChecklistHomero Januncio100% (1)
- South Norfolk GuidanceDocument12 pagesSouth Norfolk GuidanceBryant CoolNo ratings yet
- DG2V 35 Electronics Graded Unit 2Document75 pagesDG2V 35 Electronics Graded Unit 2Mullah FassudinNo ratings yet
- Leave Management SystemDocument47 pagesLeave Management SystemReshma Hedaoo100% (1)
- HACCP VALIDATION AND VERIFICATION GUIDEDocument37 pagesHACCP VALIDATION AND VERIFICATION GUIDETeti AzrilNo ratings yet
- John Kingsley - Inst & Control CybersecurityDocument8 pagesJohn Kingsley - Inst & Control CybersecurityJohn KingsleyNo ratings yet
- Qualification of Autoclave, RMG, FBD, Cone Blender, Tablet MachineDocument11 pagesQualification of Autoclave, RMG, FBD, Cone Blender, Tablet MachineDANIBATANo ratings yet
- Autopipe: Acceptance Test SetDocument185 pagesAutopipe: Acceptance Test SetAob AprilNo ratings yet
- Vse Company Profile MalaysiaDocument21 pagesVse Company Profile MalaysiaYan AungNo ratings yet
- Espectrómetro FT-IR Nicolet Is 10Document1 pageEspectrómetro FT-IR Nicolet Is 10Adriano BludegardNo ratings yet
- Boiler Tube Thickness ProcedureDocument19 pagesBoiler Tube Thickness Procedureamol1321100% (3)
- Halal - An Emerging Food Quality Standard Standard - Similarities of Halal & Similarities of Halal & HACCPDocument20 pagesHalal - An Emerging Food Quality Standard Standard - Similarities of Halal & Similarities of Halal & HACCPChristy Brown100% (1)
- ISO 9001/IATF 16949 RequirementsDocument402 pagesISO 9001/IATF 16949 RequirementsRohit Soni0% (1)
- 65-HACCP Certification Scheme June 2012Document64 pages65-HACCP Certification Scheme June 2012Osman AitaNo ratings yet
- Tec - Asset Verification and Physical Asset Tagging ProjectDocument1 pageTec - Asset Verification and Physical Asset Tagging ProjectTaofiq100% (1)
- The Implementation of The New Standard EN ISO 18563 For Ultrasonic Phased-Array Systems at The ManufacturerDocument7 pagesThe Implementation of The New Standard EN ISO 18563 For Ultrasonic Phased-Array Systems at The ManufacturershaxahNo ratings yet
- Computer System Validation Using GAMP 5Document47 pagesComputer System Validation Using GAMP 5Andrew Turner100% (5)
- EnergyMetering Installation ManualDocument12 pagesEnergyMetering Installation ManualpatzucNo ratings yet
- Ao 43 S 1999Document92 pagesAo 43 S 1999Ella RivaNo ratings yet
- G Sop 011005Document21 pagesG Sop 011005Rubén Reyes SalgadoNo ratings yet
- ASTM C1093-15aDocument6 pagesASTM C1093-15aLaboepn1No ratings yet