Professional Documents
Culture Documents
Chapte 6 - Systems Design
Uploaded by
Samuel Nderitu0 ratings0% found this document useful (0 votes)
17 views39 pagesSystems Design
Original Title
Chapte 6 -systems design
Copyright
© © All Rights Reserved
Available Formats
PPTX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentSystems Design
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
17 views39 pagesChapte 6 - Systems Design
Uploaded by
Samuel NderituSystems Design
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
You are on page 1of 39
Lecture 6
Foundations for Systems Design
North Tec – TAI TOKERAU WANANGA
Outline
What Is Systems Design?
Design Activities
System Controls and Security
North Tec – TAI TOKERAU WANANGA 2
Learning Objectives
Describe systems design and contrast it with
systems analysis
List the documents and models used as
inputs to or output from systems design
Explain each major design activity
Describe security methods and controls
North Tec – TAI TOKERAU WANANGA 3
Overview
Analysis says “what” is required and design tells us “how”
the system will be configured and constructed
Chapters 2, 3, 4 and 5 covered systems analysis activities
(requirements)
This chapter introduces system design and the design
activities involved in systems development
Design bridges the gap between requirements to actual
implementation
North Tec – TAI TOKERAU WANANGA 4
What is Systems Design
Analysis provides the starting point for design
Design provides the starting point for
implementation
Analysis and design results are documented to
coordinate the work
Objective of design is to define, organize, and
structure the components of the final solution to
serve as a blue print for construction
North Tec – TAI TOKERAU WANANGA 5
Analysis to Design to
Implementation
North Tec – TAI TOKERAU WANANGA 6
Design Models
Design is a model building activity
The formality of the project will dictate the type,
complexity, and depth of models
Agile/iteration projects typically build fewer models,
but models are still created
Jumping to programming without design often causes
less than optimum solutions and may require rework
North Tec – TAI TOKERAU WANANGA 7
Analysis
Models to
Design
Models
North Tec – TAI TOKERAU WANANGA 8
Design Activities
Design activities correspond to components of the new
system
The environment
Application components
User interface
Database
Software classes and methods
North Tec – TAI TOKERAU WANANGA 9
Design Activities and Iterations
North Tec – TAI TOKERAU WANANGA 10
Key Design Questions for each
Activity
North Tec – TAI TOKERAU WANANGA 11
Describe the Environment
Two key elements in the environment
Communications with External Systems
Message formats
Web and networks
Communication protocols
Security methods
Error detection and recovery
Conforming to an existing Technology Architecture
Discover and describe existing architecture
Chapter 7 provides more details
North Tec – TAI TOKERAU WANANGA 12
Design the Application
Components
Application component is a well defined unit of
software that performs some function(s)
Issues involve how to package components
including
Scope and size – what are the functions, boundaries, interfaces?
Programming language – what are the accepted languages?
Build or buy – is an acceptable version available to purchase?
North Tec – TAI TOKERAU WANANGA 13
Typical models for defining
application components
North Tec – TAI TOKERAU WANANGA 14
Design the User Interface
To the user, the User Interface is the system.
The user interface has large impact of user
productivity
Includes both Analysis and Design tasks
Requires heavy user involvement
Current needs require multiple user interfaces
Many different devices and environments
North Tec – TAI TOKERAU WANANGA 15
Typical
models
for user
interface
design
North Tec – TAI TOKERAU WANANGA 16
Design the Database
By definition, an Information System requires data
– usually in a database
Current technology frequently use Relational
Database Management Systems (RDBMS)
Requires converting the data model to a relational
database
Requires addressing of many other technical issues
Throughput and response time
Security
North Tec – TAI TOKERAU WANANGA 17
Typical Table Definition as part
of Database Schema
North Tec – TAI TOKERAU WANANGA 18
Design Software Classes and
Methods
• AKA Detailed Design
• A model building activity
• Design Class Diagram
• Sequence Diagrams
• State-Machine Diagrams
North Tec – TAI TOKERAU WANANGA 19
Typical
Design
Class
Diagram
with
attributes
and
methods
North Tec – TAI TOKERAU WANANGA 20
System Controls and Security
• Integrity Controls
• Controls that maintain integrity of inputs, outputs and data
and programs
• Security Controls
• Controls that protect the assets from threats, internal and
external
North Tec – TAI TOKERAU WANANGA 21
Integrity and Security Controls
North Tec – TAI TOKERAU WANANGA 22
Designing Integrity Controls
• Integrated into application programs and DBMS
• Objectives of Integrity Controls
• Ensure that only appropriate and correct business
transactions are accepted
• Ensure that transactions are recorded and processed
correctly
• To protect and safeguard assets such as the database
North Tec – TAI TOKERAU WANANGA 23
Input Controls
• Prevent invalid or erroneous data from entering the
system
• Value Limit Controls
• Check the range of inputs for reasonableness
• Completeness Controls
• Ensure all the data has been entered
• Data Validation Controls
• Ensure that specific data values are correct
• Field Combination Controls
• Ensure data is correct based on relationships between fields
North Tec – TAI TOKERAU WANANGA 24
Output Controls
• To ensure that output arrives at proper destination (for
authorized eyes) and is accurate, current, and
complete
• Examples
• Physical access to printers and display devices
• Discarded data – protect from “dumpster diving”
• Labels on printed and electronic output to correctly identify
source of data
North Tec – TAI TOKERAU WANANGA 25
Redundancy, Backup and
Recovery
• Protect data and systems from catastrophes
• Databases
• Hardware
• Software applications
• Networks
• On-site versus off-site copies
North Tec – TAI TOKERAU WANANGA 26
Fraud Prevention
• Critical to prevent internal fraud, embezzlement, or
loss
• Fraud triangle
• Opportunity
• Motive
• Rationalization
North Tec – TAI TOKERAU WANANGA 27
Fraud Risk – Factors and
Techniques
North Tec – TAI TOKERAU WANANGA 28
Designing Security Controls
• Protect all assets against external threats
• Other objectives
• Protect and maintain a stable, functioning operating
environment 24/7 (equipment, operating systems, DBMSs)
• Protect information and transactions during transmission
across networks and Internet
North Tec – TAI TOKERAU WANANGA 29
Designing Security Controls
• Access Controls – Limit a person’s ability to access
servers, files, data, applications
• Authentication – to identify users
• Multifactor Authentication
• Access control list – list of valid users
• Authorization – authenticated user’s list of permission level for
each resource
• Registered Users – those with authorization
• Unauthorized Users – anyone not registered
• Privileged Users – those that maintain lists and systems
North Tec – TAI TOKERAU WANANGA 30
Types
of
users
North Tec – TAI TOKERAU WANANGA 31
Data Encryption
• Method to secure data – stored or in transmission
• Encryption – alter data so it is unrecognizable
• Decryption – converted encrypted data back to readable
format
• Encryption Algorithm – mathematical transformation of
the data
• Encryption Key – a long data string that allows the same
algorithm to produce unique encryptions
North Tec – TAI TOKERAU WANANGA 32
Symmetric Key Encryption
• Encryption method that uses the same key to encrypt
and decrypt
North Tec – TAI TOKERAU WANANGA 33
Asymmetric Key Encryption
• Encryption method that uses different keys to encrypt
and decrypt
• AKA Public Key Encryption
North Tec – TAI TOKERAU WANANGA 34
Digital Signatures and
Certificates
• Digital Signature – technique where a document is
encrypted using a private key
• Note – implements previous slide, but in reverse
• Document is encrypted with private key, but then can only be
decrypted with correct public key
• Digital Certificate – An organizations name and public
that is encrypted and certified by an authorized third
party
• Certifying Authority – the authorized third party
• Widely known and accepted – built into Web browsers
North Tec – TAI TOKERAU WANANGA 35
Secure Transactions
Secure Sockets Layer (SSL) – standard set of protocols
for authentication and authorization
Transport Layer Security (TLS) – an Internet standard
equivalent to SSL
IP Security (IPSec) – Internet security protocol at a low-
level transmission
Hypertext Transfer Protocol Secure (HTTPS) – Internet
standard to transmit Web pages
North Tec – TAI TOKERAU WANANGA 37
Summary
This chapter introduces the concept of Systems Design
Analysis is fact finding and modeling
Design is modeling to specify how system will be implemented
Design is bridge between analysis an implementation
North Tec – TAI TOKERAU WANANGA 38
Summary (continued)
Activities of Systems Design
Describe the environment
Design the application components
Design the User Interface
Design the database
Design the software classes and methods
North Tec – TAI TOKERAU WANANGA 39
Summary (continued)
System Controls and Security
Integrity Controls
Input controls
Output controls
Backup and recovery
Fraud prevention
Security Controls
Access controls
Data encryption
Digital signatures and certificates
Secure transactions
North Tec – TAI TOKERAU WANANGA 40
You might also like
- Practical Data Acquisition for Instrumentation and Control SystemsFrom EverandPractical Data Acquisition for Instrumentation and Control SystemsNo ratings yet
- Session 2 - ISYS6542-20210105D5181 - Foundations For System DesignDocument41 pagesSession 2 - ISYS6542-20210105D5181 - Foundations For System DesignRonan WisnuNo ratings yet
- Top-Down Network DesignDocument26 pagesTop-Down Network DesignAffo Alex50% (2)
- Security and Software Defined Networks PDFDocument31 pagesSecurity and Software Defined Networks PDFBùi ThànhNo ratings yet
- Chapter 1 1Document45 pagesChapter 1 1Bab KebedeNo ratings yet
- Itec411 - Network Design: Chapter 1 - Identifying Your Customer'S Needs and GoalsDocument34 pagesItec411 - Network Design: Chapter 1 - Identifying Your Customer'S Needs and GoalsNatenael BerhanuNo ratings yet
- Monitoring and AuditingDocument31 pagesMonitoring and AuditingFlorence Heart ViñasNo ratings yet
- Software Engineering: Dr.K.M.Anandkumar Associate Professor / CSEDocument43 pagesSoftware Engineering: Dr.K.M.Anandkumar Associate Professor / CSESiddiqNo ratings yet
- File Tracking System-DocumentationDocument116 pagesFile Tracking System-DocumentationXayd Karim55% (11)
- Ch1. System Design PhaseDocument4 pagesCh1. System Design Phaseomarsayed.cppNo ratings yet
- E223 Lesson 1 (IS Slide)Document62 pagesE223 Lesson 1 (IS Slide)eeshien1No ratings yet
- IT Infrastructure ArchitectureDocument20 pagesIT Infrastructure ArchitectureAlyssa Marie SantosNo ratings yet
- CISA, Certified Information Systems AuditorDocument188 pagesCISA, Certified Information Systems AuditorasebeNo ratings yet
- Network+ Guide To Networks 5 EditionDocument62 pagesNetwork+ Guide To Networks 5 EditionRyan OrtegaNo ratings yet
- Lecture 4 - Network and IT InfrastructureDocument47 pagesLecture 4 - Network and IT InfrastructureHoney DhaliwalNo ratings yet
- Enterasys Nac GuideDocument19 pagesEnterasys Nac GuideIchwan SetiawanNo ratings yet
- TDNetworkDocument364 pagesTDNetworkiraguz1No ratings yet
- RCS315 Design 1 L1Document31 pagesRCS315 Design 1 L1Davis PunjilaNo ratings yet
- Ch2. System Technical ArchitectureDocument3 pagesCh2. System Technical Architectureomarsayed.cppNo ratings yet
- Data Warehouse ArchitectureDocument63 pagesData Warehouse ArchitectureJasper Andrew Adjarani100% (2)
- Top-Down Network Design: Chapter OneDocument28 pagesTop-Down Network Design: Chapter OneAshNo ratings yet
- Chapter 1 IntroductionDocument76 pagesChapter 1 IntroductionFekadselassie TeshaleNo ratings yet
- Jaringan Komputer A PDFDocument328 pagesJaringan Komputer A PDFSmk AlghozalyNo ratings yet
- IT Organizational ChartDocument9 pagesIT Organizational ChartDédé KambalaNo ratings yet
- Group 3 Software Presentation 1Document34 pagesGroup 3 Software Presentation 1walyiseNo ratings yet
- Roles of Computer ProfessionalsDocument40 pagesRoles of Computer ProfessionalsDymond Daniel100% (1)
- Modern Systems Analysis & DesignDocument49 pagesModern Systems Analysis & DesignAliasgar SuratwalaNo ratings yet
- Network Design: Chapter OneDocument16 pagesNetwork Design: Chapter OneAnonymous O8qTQZXNo ratings yet
- Information Technology in Business AND Its Impact On Audit ProcessDocument33 pagesInformation Technology in Business AND Its Impact On Audit ProcessSyahrul Aman IsmailNo ratings yet
- NSE - LinuxDocument2 pagesNSE - LinuxArfat ShaikhNo ratings yet
- Security Design in A Windows 2003 Environment: CIS 288 Designing A Secure Network FrameworkDocument10 pagesSecurity Design in A Windows 2003 Environment: CIS 288 Designing A Secure Network Frameworkghar_dashNo ratings yet
- Data vs. InformationDocument72 pagesData vs. InformationHardik SharmaNo ratings yet
- Cissp Security ArchitectureDocument20 pagesCissp Security Architecturefern12No ratings yet
- File Tracking SystemDocument109 pagesFile Tracking Systemradshan2967% (3)
- Network Design Chapter 1Document11 pagesNetwork Design Chapter 1ISHETU0% (1)
- File Security with AES EncryptionDocument53 pagesFile Security with AES EncryptionPvlt 99No ratings yet
- Sysad313 - What Is System Administration: ObjectivesDocument3 pagesSysad313 - What Is System Administration: ObjectivesErwinMacaraigNo ratings yet
- Module 2 GITDocument7 pagesModule 2 GITjohnmichaelaspe1234No ratings yet
- Introduction To Emerging TechnologiesDocument36 pagesIntroduction To Emerging Technologiesyordi teshomeNo ratings yet
- Mitigating Software Integrity Attacks With Trusted Computing in a Time Distribution NetworkDocument17 pagesMitigating Software Integrity Attacks With Trusted Computing in a Time Distribution NetworkgeethakaniNo ratings yet
- System Admin Documentation GuideDocument67 pagesSystem Admin Documentation GuideyogaarsaNo ratings yet
- Chapter 09Document18 pagesChapter 09阮胡明利No ratings yet
- Req EnggDocument33 pagesReq EnggPrateek DubeyNo ratings yet
- ICT Technician - Job AdvertDocument3 pagesICT Technician - Job AdvertPambwe MwabaNo ratings yet
- Lecture 10Document52 pagesLecture 10Rana GaballahNo ratings yet
- PenTest 04 - 2015Document99 pagesPenTest 04 - 2015Alexandru Puiu100% (11)
- Systems Programming and Computer Control Module OverviewDocument17 pagesSystems Programming and Computer Control Module OverviewDiana RoseNo ratings yet
- Network+ Guide To Networks 5 EditionDocument102 pagesNetwork+ Guide To Networks 5 EditionRyan OrtegaNo ratings yet
- Chapter 1 - Introduction To Software EngineeringDocument28 pagesChapter 1 - Introduction To Software EngineeringSara Saraswathy SureshNo ratings yet
- Network Troubleshooting BasicsDocument63 pagesNetwork Troubleshooting Basicsmayu mayuranNo ratings yet
- System Development - Programming Language and Program Development Tools - Program DevelopmentDocument41 pagesSystem Development - Programming Language and Program Development Tools - Program DevelopmentjohnmaurussNo ratings yet
- 01 ITFRST 21032023 121033amDocument12 pages01 ITFRST 21032023 121033amAMIRNo ratings yet
- Chapter 4 - Software DesignDocument42 pagesChapter 4 - Software DesignshimelisNo ratings yet
- Hardware SecurityDocument26 pagesHardware Securityjayamalar100% (1)
- Information System Development and Programming Languages.: ICT Long #6 MR - SultanDocument6 pagesInformation System Development and Programming Languages.: ICT Long #6 MR - SultanȻħ ŠultanNo ratings yet
- IS Lecture 3Document58 pagesIS Lecture 3Abdul MoizNo ratings yet
- Assistan Officer It - JDDocument2 pagesAssistan Officer It - JDM Khurram HameedNo ratings yet
- Domain4 - Security Architecture & ModelsDocument26 pagesDomain4 - Security Architecture & Modelsdrilling moneytreeNo ratings yet
- ITEC85 ReviewerDocument11 pagesITEC85 ReviewerAntero Jr. SolisNo ratings yet
- Brain Rules 10-12Document47 pagesBrain Rules 10-12Samuel NderituNo ratings yet
- From Research Organizations: Science NewsDocument6 pagesFrom Research Organizations: Science NewsSamuel NderituNo ratings yet
- From Research Organizations: Science NewsDocument6 pagesFrom Research Organizations: Science NewsSamuel NderituNo ratings yet
- Brain Rules Intro and Rules 1-3Document34 pagesBrain Rules Intro and Rules 1-3Samuel NderituNo ratings yet
- Case StudyDocument5 pagesCase StudySamuel NderituNo ratings yet
- Consent For PhotographyDocument1 pageConsent For PhotographySamuel NderituNo ratings yet
- LaPlace Power Inventory Case StudyDocument1 pageLaPlace Power Inventory Case StudySamuel NderituNo ratings yet
- Fy17 Cafr Final LDDocument116 pagesFy17 Cafr Final LDSamuel NderituNo ratings yet
- Are You A JerkDocument8 pagesAre You A JerkSamuel NderituNo ratings yet
- ZapposDocument2 pagesZapposSamuel NderituNo ratings yet
- Wk4 Example SystemsExecuteChangeDocument6 pagesWk4 Example SystemsExecuteChangeSamuel Nderitu100% (1)
- Module 5 Case Accounting For Decision and Transfer PricingDocument14 pagesModule 5 Case Accounting For Decision and Transfer PricingSamuel NderituNo ratings yet
- Regional HospitalDocument5 pagesRegional HospitalSamuel NderituNo ratings yet
- Flyer SampleDocument2 pagesFlyer SampleSamuel NderituNo ratings yet
- Western Region Eastern Region Original Price Sale Price Days To Sell Original PriceDocument4 pagesWestern Region Eastern Region Original Price Sale Price Days To Sell Original PriceSamuel NderituNo ratings yet
- Sol16 4eDocument77 pagesSol16 4eSamuel NderituNo ratings yet
- Fortiweb v6.0.2 Admin Guide PDFDocument833 pagesFortiweb v6.0.2 Admin Guide PDFSOC PGASCOMNo ratings yet
- HFM Copy UtilityDocument19 pagesHFM Copy UtilityPaul SudebNo ratings yet
- Secure Programming With Static AnalysisDocument56 pagesSecure Programming With Static Analysissurnj1No ratings yet
- Free PDF Physics BooksDocument2 pagesFree PDF Physics BooksRandyNo ratings yet
- PCS-9882n+ìETHERNET SWITCH 2010catalog-15Document2 pagesPCS-9882n+ìETHERNET SWITCH 2010catalog-15Rinda_RaynaNo ratings yet
- Manual de Utilizaçao Do Sap Basis Um. Um Otimo Documento para Administraçao Dos AmbientesDocument390 pagesManual de Utilizaçao Do Sap Basis Um. Um Otimo Documento para Administraçao Dos AmbientesEDUSUPORTENo ratings yet
- CCNA Exploration: Routing Protocols and Concepts: Certificate of Course CompletionDocument2 pagesCCNA Exploration: Routing Protocols and Concepts: Certificate of Course CompletionAlejandro MontoyaNo ratings yet
- Pearson - Complete A+ Guide To IT Hardware & Software (Exams 220-1001 & 220-1002) Lab ManualDocument636 pagesPearson - Complete A+ Guide To IT Hardware & Software (Exams 220-1001 & 220-1002) Lab ManualAndrew Quezon Lachica100% (17)
- Information Search and Analysis Skills: 1 ©niitDocument13 pagesInformation Search and Analysis Skills: 1 ©niitMILANNo ratings yet
- TRM MS51 16KSeries EN Rev1.00 PDFDocument275 pagesTRM MS51 16KSeries EN Rev1.00 PDFsivanathNo ratings yet
- ITCE 314 Lab Report 6Document7 pagesITCE 314 Lab Report 6Amna AzmatNo ratings yet
- Adaptive cross-layer algorithms for multimedia transmission and energy management in wireless networksDocument92 pagesAdaptive cross-layer algorithms for multimedia transmission and energy management in wireless networksSamaWhiteNo ratings yet
- Lte Epc Umts 3GPPDocument222 pagesLte Epc Umts 3GPPjbarriospNo ratings yet
- Ads 2400NDocument4 pagesAds 2400NRana WilliamNo ratings yet
- TSEL LTE OMC Guideline - V9Document131 pagesTSEL LTE OMC Guideline - V9Mira HasanahNo ratings yet
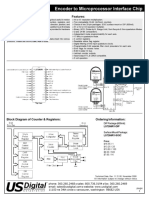
- Encoder To Microprocessor Interface Chip Chip: Features: DescriptionDocument6 pagesEncoder To Microprocessor Interface Chip Chip: Features: DescriptionserviciobsasNo ratings yet
- JAMF Client MGT White PaperDocument36 pagesJAMF Client MGT White PapervesahavaNo ratings yet
- IOT (Internet of Things) SecurityDocument41 pagesIOT (Internet of Things) SecurityaksdafNo ratings yet
- TWAIN Scanning Library GuideDocument10 pagesTWAIN Scanning Library GuidembianchettoNo ratings yet
- Fast Track Hacking-Backtrack5 Tutorial: Tutorials Web Design Tutorials Catia V5 Tutorials Backtrack 3D Max TutorialsDocument5 pagesFast Track Hacking-Backtrack5 Tutorial: Tutorials Web Design Tutorials Catia V5 Tutorials Backtrack 3D Max TutorialsprasanjeetbNo ratings yet
- ECI DCME DTX-600 - Carritech TelecommunicationsDocument2 pagesECI DCME DTX-600 - Carritech TelecommunicationsCarritech TelecommunicationsNo ratings yet
- Buffer Overflow Attacks on Linux Principles Analyzing and ProtectionDocument5 pagesBuffer Overflow Attacks on Linux Principles Analyzing and ProtectionГенеральный ГелиосNo ratings yet
- FS-8700-62 J-Bus: Driver ManualDocument14 pagesFS-8700-62 J-Bus: Driver ManualEric DunnNo ratings yet
- AIS Simkin ch10Document54 pagesAIS Simkin ch10SuhardhitaNo ratings yet
- Hx100V User ManualDocument274 pagesHx100V User Manualcarrier20% (1)
- AD1238: REST Services in Domino - Key To Modern Web ApplicationsDocument47 pagesAD1238: REST Services in Domino - Key To Modern Web ApplicationsGerard SortoNo ratings yet
- Hadoop Updated Course ContentDocument3 pagesHadoop Updated Course Contentnandy39No ratings yet
- Computer SportDocument2 pagesComputer SportKhaerul QuNo ratings yet
- NGFW POC Student Guide Day 1Document47 pagesNGFW POC Student Guide Day 1SAPTARSHI GHOSHNo ratings yet
- LIMS Directory - Winter 2017 - Product Pricing and DemosDocument173 pagesLIMS Directory - Winter 2017 - Product Pricing and DemosmaximixNo ratings yet