Professional Documents
Culture Documents
Face Recognition Technology: Presented By: R.VAISHNAVI 20RH1A05K0
Uploaded by
Dubasi Harshini0 ratings0% found this document useful (0 votes)
8 views13 pagesThis document provides an overview of face recognition technology. It discusses the history of face recognition, which began in the 1960s. It also outlines how face recognition works by capturing images, measuring geometric facial features, calculating a formula to represent the face, and comparing it to images in a database. The document lists applications such as security, immigration, and banking. It discusses advantages like improved security and speed, and disadvantages like data storage needs and accuracy issues. The conclusion states that face recognition will have many applications in smart environments.
Original Description:
Original Title
SEMINAR 1
Copyright
© © All Rights Reserved
Available Formats
PPTX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis document provides an overview of face recognition technology. It discusses the history of face recognition, which began in the 1960s. It also outlines how face recognition works by capturing images, measuring geometric facial features, calculating a formula to represent the face, and comparing it to images in a database. The document lists applications such as security, immigration, and banking. It discusses advantages like improved security and speed, and disadvantages like data storage needs and accuracy issues. The conclusion states that face recognition will have many applications in smart environments.
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
8 views13 pagesFace Recognition Technology: Presented By: R.VAISHNAVI 20RH1A05K0
Uploaded by
Dubasi HarshiniThis document provides an overview of face recognition technology. It discusses the history of face recognition, which began in the 1960s. It also outlines how face recognition works by capturing images, measuring geometric facial features, calculating a formula to represent the face, and comparing it to images in a database. The document lists applications such as security, immigration, and banking. It discusses advantages like improved security and speed, and disadvantages like data storage needs and accuracy issues. The conclusion states that face recognition will have many applications in smart environments.
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
You are on page 1of 13
FACE RECOGNITION
TECHNOLOGY
Presented by: R.VAISHNAVI
20RH1A05K0
CONTENTS:
•Introduction
•History
•Implementation
•How it works
•Applications
•Uses
•Advantages
•Disadvantages
•Security
•Conclusion
INTRODUCTION:
It is a category of biometric software for automatic
identification.
It makes use the most usual human identifier,face and
unique facial characteristics.
It was invented by
WOODROW WILSON
BLEDSOE
HISTORY:
The earliest pioneers of facial recognition were Wood
Bledsoe,Helen Chan Wolf and Charles Bisson.
In 1964 and 1965,Beldsoe along with Wolf and Bisson
began work using computers to recognise the human face.
EBL approach by Sung and Poggio(1994)
The neural network
approach by Rowley
etal(1998).
Face Recognition Vendor
Test(2002)
Face Recognition Grand
Challenges(2006)
CHARLES
HELEN CHAN WOLF
BISSON
IMPLEMENTATION:
The implementation of face recognition technology
includes the following stages:
•Image acquisation
•Image processing
•Distinctive characteristic location
•Template matching
•Template creation
These nodal points are measured creating a numerical
code,called a face print,
representing the face in
the database.
HOW IT WORKS:
Step-1: Captures images or vedios.
Step-2: Reads the geometric measurements on the face.
Step-3: Calculates a mathematical formula for the captured
face.
Step-4: Compares it with the image in the database.
APPLICATIONS:
Government use:
a)Security/Counterterrorism
b)Immigration
c)Voter verification
Commercial use:
a)Day care
b)Residential security
c)Banking using ATM
Fraud detection
Payments
Healthcare
Advertising
USES:
It can be used for a multitude of applications,from
security to advertisements.Here are some of them:
Mobile phone manufactures,such as Apple,for consumer
security.
Modernizing public safety
Creating a better shopping experience
Streamlining customer service
Diagnosing rare diseases
Tracking school attendance
Locating lost pets
Unlock phones
Prevent Retail crime
Find missing persons
ADVANTAGES:
No need to physically contact a device for authentication
purpose.
Improved level of security.
High security
High accuracy
Fully automated
Low invasiveness
High speed
Identification support system
DISADVANTAGES:
Scarce Data Storage
Insufficient camera angle
Not as accurate as other biometrics
Large amounts of storage needed
Good quality of images required
Can’t tell differance between identical twins
Problem when the person change the hairstyle,shave or
beard or wear glasses.
SECURITY:
Currently there are no laws in United States that
specially protect an individual’s biometric data.
This is being studied or deployed for airport security.
Data from facial recognition system may be captured
and stored and an individual may not even know it.
This information can be accessed by hackers.
CONCLUSION:
A face recognition system must be able to recognise a
face in many different imaging situations.
It will find faces efficiently without exhaustively
searching the image.
Face recognition systems are going to have widespread
application in smart environments.
THANK YOU
You might also like
- Face Recognition Technology 4U9Document18 pagesFace Recognition Technology 4U9nikhilacha9177No ratings yet
- Seminar Presentation ON: "Face Recognition Technology"Document14 pagesSeminar Presentation ON: "Face Recognition Technology"SasidharKalidindiNo ratings yet
- Lecture Attendance Using Face RecognitionDocument14 pagesLecture Attendance Using Face Recognitionthoshif khanNo ratings yet
- Face Recognition and Retrieval Using LLBP and URFB: G.Komala Yadav, M.Venkata RamanaDocument22 pagesFace Recognition and Retrieval Using LLBP and URFB: G.Komala Yadav, M.Venkata RamanaInternational Organization of Scientific Research (IOSR)No ratings yet
- ReferencesDocument17 pagesReferencesmaleksd111No ratings yet
- Facial Recognition SeminarDocument19 pagesFacial Recognition SeminarTony Omorotionmwan AirhiavbereNo ratings yet
- Secure Face Unlock: On Smart Phone: BY-Arti Rameshwar Babar Guided by - R H KulkarniDocument18 pagesSecure Face Unlock: On Smart Phone: BY-Arti Rameshwar Babar Guided by - R H KulkarniAmar Nath BabarNo ratings yet
- Facial Recognition TechnologyDocument8 pagesFacial Recognition TechnologyMeera Gayathri DNo ratings yet
- IDocument25 pagesImaleksd111No ratings yet
- UNIT-3: Face RecognitionDocument47 pagesUNIT-3: Face RecognitionYohaan JNo ratings yet
- Face Recognition: (Name of Author)Document8 pagesFace Recognition: (Name of Author)Beenish JahanzebNo ratings yet
- Face Detection and Recognition TechnologyDocument6 pagesFace Detection and Recognition TechnologyNilesh SharmaNo ratings yet
- Face Recognition Using OpencvDocument70 pagesFace Recognition Using OpencvPrathyusha100% (5)
- Facial Recognition System: Unlocking the Power of Visual IntelligenceFrom EverandFacial Recognition System: Unlocking the Power of Visual IntelligenceNo ratings yet
- Face RecognitionDocument17 pagesFace Recognitionምንሼ ነው ዘመኑNo ratings yet
- 2D Face RecognitionDocument28 pages2D Face Recognitionjit_72No ratings yet
- 0109 Dwayne SilvapintoDocument22 pages0109 Dwayne SilvapintoNaitik LodhaNo ratings yet
- Kamenská - Facial RecognitionDocument9 pagesKamenská - Facial RecognitionDominika KamenskáNo ratings yet
- Next Generation Identity Verification Based On Face-Gait BiometricsDocument7 pagesNext Generation Identity Verification Based On Face-Gait BiometricsOl-Parfum ShopNo ratings yet
- Chapter One - ThreeDocument30 pagesChapter One - ThreeDev jibreenNo ratings yet
- Face Recognition With Images in DetailDocument15 pagesFace Recognition With Images in DetailDeep PuniwalaNo ratings yet
- Biometric Systems: ITC571 Assignment-2 (Project Proposal & Plan)Document12 pagesBiometric Systems: ITC571 Assignment-2 (Project Proposal & Plan)Abdex AliyiNo ratings yet
- 1.1 General Introduction: Face Recognition SystemDocument78 pages1.1 General Introduction: Face Recognition SystemShreya MaheshwariNo ratings yet
- VIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIDocument17 pagesVIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIIapi-291159108No ratings yet
- BlackHat DC 09 Nguyen Face Not Your PasswordDocument16 pagesBlackHat DC 09 Nguyen Face Not Your PasswordHandry WahyudiNo ratings yet
- Face Recognition TechnologyDocument26 pagesFace Recognition TechnologySANDIP PODDARNo ratings yet
- ATM SkyDocument11 pagesATM Skysandeep kumar yadavNo ratings yet
- Bio MetricsDocument32 pagesBio MetricsAnuja UpadhyeNo ratings yet
- V3i3 1331Document8 pagesV3i3 1331Ha TranNo ratings yet
- Biometrics - An AuthenticationDocument24 pagesBiometrics - An AuthenticationrenjythNo ratings yet
- Preprints202007 0479 v1Document56 pagesPreprints202007 0479 v1Mike ShufflebottomNo ratings yet
- Face Recognition TechnologyDocument30 pagesFace Recognition TechnologyRsyedNo ratings yet
- A Comparative Study of Face Recognition TechniquesDocument9 pagesA Comparative Study of Face Recognition TechniquesFrengki SimatupangNo ratings yet
- A Review On Face Detection TechniquesDocument7 pagesA Review On Face Detection TechniquesEditor IJTSRDNo ratings yet
- Face Recognition Systems A SurveyDocument34 pagesFace Recognition Systems A SurveysNo ratings yet
- Apps PDFDocument6 pagesApps PDFOliifan BaayyooNo ratings yet
- Electronics 09 01188 With CoverDocument53 pagesElectronics 09 01188 With CoverManuel EliasNo ratings yet
- Research Paper On Face RecognitionDocument6 pagesResearch Paper On Face Recognitionfjluthulg100% (1)
- Face Recognition Using PCADocument30 pagesFace Recognition Using PCAamit15094775100% (6)
- Final Year Project Literature Review - OldDocument14 pagesFinal Year Project Literature Review - OldTaslim Musa-AzeezNo ratings yet
- A Survey of Face Recognition TechniquesDocument28 pagesA Survey of Face Recognition Techniquesaisyah az-zahra ibrahimNo ratings yet
- Seminar Face Recognition TechnologyDocument21 pagesSeminar Face Recognition TechnologyAmanNo ratings yet
- 10 Chapter1 PDFDocument5 pages10 Chapter1 PDFTony ChopperNo ratings yet
- Chapter IiiDocument56 pagesChapter Iiiharshit47333No ratings yet
- Biometrics in Secure E-TransactionDocument4 pagesBiometrics in Secure E-TransactionREx Ethics100% (1)
- Biometrics Is The Technique of Using Unique, Non-TransferableDocument24 pagesBiometrics Is The Technique of Using Unique, Non-Transferableapi-3746880No ratings yet
- Face Recognition Research Papers 2015Document5 pagesFace Recognition Research Papers 2015fzk3bszq100% (1)
- Camera Ready Paper Iccmc 2022Document6 pagesCamera Ready Paper Iccmc 2022vansh kediaNo ratings yet
- Face Recognition Technology: What Are Biometrics?Document5 pagesFace Recognition Technology: What Are Biometrics?pramodNo ratings yet
- Share Face Recognition TechnologyDocument15 pagesShare Face Recognition TechnologyBikram RockNo ratings yet
- Facial Recognition Technology: Seema Singh 0809710086 CS-BDocument23 pagesFacial Recognition Technology: Seema Singh 0809710086 CS-BSupriya KushwahaNo ratings yet
- Face RecognitionDocument20 pagesFace Recognitionpixels mmmutNo ratings yet
- Face Detection and RecognitionDocument17 pagesFace Detection and RecognitionAbhishek GargNo ratings yet
- Presented By: Biometric Technology To DistinctlyDocument13 pagesPresented By: Biometric Technology To Distinctlymanikumar147No ratings yet
- Face Recognition TechnologyDocument25 pagesFace Recognition Technologysudhanshu2050No ratings yet
- Face Recognition Report 1Document26 pagesFace Recognition Report 1Binny DaraNo ratings yet
- Face Recognition Thesis ReportDocument7 pagesFace Recognition Thesis ReportBrandi Gonzales100% (1)
- Face Recognition Technology: Seminar ReportDocument35 pagesFace Recognition Technology: Seminar ReportAekansh JainNo ratings yet
- Dare's Project Proposal NewDocument5 pagesDare's Project Proposal NewOwolabi PetersNo ratings yet
- Seventh Pay Commission ArrearsDocument11 pagesSeventh Pay Commission Arrearssantosh bharathyNo ratings yet
- L5CoachMentorReflectiveLog TemplateDocument9 pagesL5CoachMentorReflectiveLog TemplateHadusssNo ratings yet
- Inspection List For Electrical PortableDocument25 pagesInspection List For Electrical PortableArif FuadiantoNo ratings yet
- Student Material CN Version - 2017.11.10Document25 pagesStudent Material CN Version - 2017.11.10Jagaddeesha BRNo ratings yet
- 1 final-LESSON-1-U1-Humanities-and-Arts-in-the-Western-Concept-dallyDocument10 pages1 final-LESSON-1-U1-Humanities-and-Arts-in-the-Western-Concept-dallyVilla JibbNo ratings yet
- Switch RotatoriosDocument12 pagesSwitch RotatoriosRoberto AndrésNo ratings yet
- D4530Document5 pagesD4530rimi7al100% (1)
- Dynamic Analysis of Synchronous Reluctance Motor Drives Based On Simulink and Finite Element ModelDocument5 pagesDynamic Analysis of Synchronous Reluctance Motor Drives Based On Simulink and Finite Element ModelenmnabilNo ratings yet
- Absolute Containers Brochure 2019 2 27 PDFDocument19 pagesAbsolute Containers Brochure 2019 2 27 PDFEduardo SolanoNo ratings yet
- Brochure Exterior LightingDocument49 pagesBrochure Exterior Lightingmurali_227No ratings yet
- Semantic SearchMonkeyDocument39 pagesSemantic SearchMonkeyPaul TarjanNo ratings yet
- KIT REQUEST FORM - GradDocument2 pagesKIT REQUEST FORM - Graddamie aadamsNo ratings yet
- Class 12 Physics Mcqs Chapter: 6 Electromagnetic Induction: AnswerDocument12 pagesClass 12 Physics Mcqs Chapter: 6 Electromagnetic Induction: AnswerDiksha TNo ratings yet
- G120D Getting Started 0418 en-USDocument94 pagesG120D Getting Started 0418 en-USHamadi Ben SassiNo ratings yet
- PDF - Gate Valve OS and YDocument10 pagesPDF - Gate Valve OS and YLENINROMEROH4168No ratings yet
- 翻译件 2021 The - Early - Life - of - Marx's - "Mode - 【彩云小译】Document61 pages翻译件 2021 The - Early - Life - of - Marx's - "Mode - 【彩云小译】James BNo ratings yet
- Low Invasion CoringDocument4 pagesLow Invasion CoringKHALEDFEKAIRNo ratings yet
- Loading and Hauling Dump Truck: DumperDocument2 pagesLoading and Hauling Dump Truck: DumperRJNo ratings yet
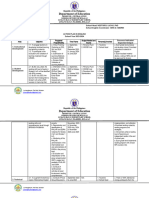
- English Action Plan 2023-2024Document5 pagesEnglish Action Plan 2023-2024Gina DaligdigNo ratings yet
- Project Scheduling: Marinella A. LosaDocument12 pagesProject Scheduling: Marinella A. LosaMarinella LosaNo ratings yet
- Human Resource Development Multiple Choice Question (GuruKpo)Document4 pagesHuman Resource Development Multiple Choice Question (GuruKpo)GuruKPO90% (20)
- Literature Review Is The Backbone of ResearchDocument7 pagesLiterature Review Is The Backbone of Researchafmzweybsyajeq100% (1)
- Example of Presentation Planning Document 1uf6cq0Document2 pagesExample of Presentation Planning Document 1uf6cq0Wilson MorenoNo ratings yet
- Awb 4914934813Document1 pageAwb 4914934813Juandondr100% (1)
- DOPE Personality TestDocument8 pagesDOPE Personality TestMohammed Hisham100% (1)
- Recruitment and SelectionDocument50 pagesRecruitment and SelectionAmrita BhatNo ratings yet
- 33392-01 Finegayan Water Tank KORANDO PDFDocument3 pages33392-01 Finegayan Water Tank KORANDO PDFShady RainNo ratings yet
- Assignment ProblemsDocument22 pagesAssignment ProblemsPooja Yadav100% (1)
- Final Exam DiassDocument9 pagesFinal Exam Diassbaby rafa100% (3)
- 10 DLAH-Vessel Movement 28 Nov - 7 Dec 2020Document3 pages10 DLAH-Vessel Movement 28 Nov - 7 Dec 2020herlambangNo ratings yet