Professional Documents
Culture Documents
IoT Application Layer Protocol-FA19
Uploaded by
fa20-bce-0460 ratings0% found this document useful (0 votes)
2 views22 pagesCopyright
© © All Rights Reserved
Available Formats
PPTX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
2 views22 pagesIoT Application Layer Protocol-FA19
Uploaded by
fa20-bce-046Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
You are on page 1of 22
Application Protocols for IoT
Dr. Abbas Javed
Assistant Professor
Department of Electrical and Computer Engineering,
COMSATS University Islamabad, Lahore Campus
abbasjaved@cuilahore.edu.pk
The Transport Layer
• Transmission Control Protocol (TCP): This connection-oriented
protocol requires a session to get established between the source and
destination before exchanging data. You can view it as an equivalent to a
traditional telephone conversation, in which two phones must be
connected and the communication link established before the parties can
talk.
• User Datagram Protocol (UDP): With this connectionless protocol,
data can be quickly sent between source and destination—but with no
guarantee of delivery. This is analogous to the traditional mail delivery
system, in which a letter is mailed to a destination. Confirmation of the
reception of this letter does not happen until another letter is sent in
response.
• TCP is the main protocol used at the transport layer for human interactions over
the Internet.
• TCP is able to transport large volumes of data into smaller sets of packets and
ensures reassembly in a correct sequence, flow control, window adjustment, and
retransmission of lost packets.
• UDP is most often used in the context of network services or for real-time data
traffic, where performance and latency are more important than packet
retransmissions.
• Application layer protocols take care of the function of guaranteed error-free
packet reception.
• When selecting a transport layer for IoT application layer protocols, the impact on
both the lower and upper layers of the stack must be evaluated.
IoT application layer protocols
• IoT application layer protocols are designed to run on constrained nodes with
a small compute footprint and are well adapted to the network bandwidth
constraints on cellular or satellite links or constrained 6LoWPAN networks. Two
well-known examples of IoT application layer protocols are Message Queuing
Telemetry Transport (MQTT) and Constrained Application Protocol (CoAP).
• MQTT: MQTT is a lightweight publish/subscribe messaging protocol designed
for use on limited bandwidth and unreliable networks. It is commonly used for
telemetry and control applications and is supported by a wide range of IoT
devices.
• CoAP: CoAP is a simple protocol designed for constrained devices and
networks. It is used to transfer data between devices and can operate over
both UDP and TCP protocols. It is commonly used for resource-constrained
devices, such as sensors and actuators.
• Constrained IoT devices defined as class 0 send or receive only a few
bytes of data
• These devices do not implement a fully structured network protocol
stack due to processing capability, power constraints, and cost
• Class 0 devices are usually simple smart objects that are severely
constrained
IoT Application Layer Protocols
• In constrained networks or large-scale deployments of constrained
nodes, verbose web-based and data model protocols may be too heavy
for IoT applications.
• The IoT industry is working on new lightweight protocols that are
better suited to large numbers of constrained nodes and networks.
• Two of the most popular protocols are CoAP and MQTT.
Message Queuing Telemetry Transport
(MQTT)- Introduction
• MQTT stands for Message Queuing Telemetry Transport
• Developed by IBM and Arcom in the late 1990s for monitoring and
controlling a large number of sensors in harsh environments
• Lightweight, reliable, and cost-effective protocol
• Now standardized by OASIS (Organization for the Advancement of
Structured Information Standards)
MQTT Architecture
• Client/server and publish/subscribe framework based on TCP/IP
• MQTT client can act as a publisher to send data to an MQTT server
acting as a message broker
• The message broker handles the subscription and unsubscription
process and pushes the application data to MQTT clients acting as
subscribers
• MQTT decouples the data transmission between publishers and
subscribers
• Publishers and subscribers do not have to be online at the same time
MQTT Wildcards and Subscriptions
• Clients can subscribe to all data or specific data from the information
tree of a publisher
• Presence of a message broker ensures that information can be
buffered and cached in case of network failures
• MQTT clients can use wildcards to subscribe to all data or specific
data
• Subscribers express a desire to receive information from publishers
MQTT Control Packets
• Control packets run over a TCP transport using port 1883
• Optionally, MQTT can be secured using TLS on port 8883, and
WebSocket can also be used
• Each control packet consists of a 2-byte fixed header with optional
variable header fields and optional payload
• Control packet can contain a payload up to 256 MB
MQTT Message Format
MQTT Message Format
• Message format overview provided in Figure 6-11
• Contains a smaller header of 2 bytes compared to 4 bytes for CoAP
• The first MQTT field in the header is Message Type, which identifies
the kind of MQTT packet within a message
• Fourteen different types of control packets are specified in MQTT
version 3.1.1
• MQTT header is DUP (Duplication Flag). This flag, when set, allows the
client to notate that the packet has been sent previously, but an
acknowledgement was not received
MQTT Message Types
• CONNECT: Client to server request to connect
• CONNACK: Server to client connect acknowledgement
• PUBLISH: Client to server or server to client publish message
• PUBACK: Client to server or server to client publish acknowledgement
• PUBREC: Client to server or server to client publish received
• PUBREL: Client to server or server to client publish release
• PUBCOMP: Client to server or server to client publish complete
• SUBSCRIBE: Client to server subscribe request
• SUBACK: Server to client subscribe acknowledgement
• UNSUBSCRIBE: Client to server unsubscribe request
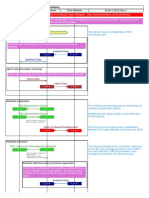
• Three Type of QoS
• QoS 0
• Best-effort and unacknowledged data service
• No response or retry
• Message arrives once or not at all
• QoS 1
• Message delivery occurs at least once
• Packet identifier in variable header
• PUBACK packets
• QoS 2
• Message delivery occurs exactly once
• PUBREC, PUBREL, and PUBCOMP packets
• Packet identifier in variable header
• Retain flag
• Purpose of Retain flag
• Found only in PUBLISH message
• Notification to server to hold onto message data
• MQTT sessions
• Four phases of MQTT sessions i.e., session establishment, authentication, data
exchange, and session termination.
• Unique client ID for each client connecting to server
• Delivery of application message to multiple clients
• Subscriptions and unsubscriptions
• SUBSCRIBE/SUBACK control packets for subscriptions
• UNSUBSCRIBE/UNSUBACK control packets for unsubscriptions
• DISCONNECT control packet for graceful termination of connection
Topic strings and topic names
• How message broker uses topic string to filter messages
• Hierarchical structure of topic names
• Example of a topic name: adt/lora/adeunis/0018B2000000023A
Wildcard characters
• Subscription to multiple topics using wildcard characters
• Pound sign (#) matches any number of levels
• Plus sign (+) matches only one topic level
• Excluding topic names beginning with dollar sign ($)
Conclusion
• MQTT is a lightweight and reliable protocol for monitoring and
controlling sensors in harsh environments
• MQTT uses a client/server and publish/subscribe framework based on
TCP/IP
• MQTT clients can subscribe to all data or specific data using wildcards
• MQTT control packets consist of a 2-byte fixed header with optional
variable header fields and optional payload
• Fourteen different types of control packets are specified in MQTT
version 3.1.1.
You might also like
- Coap &MQTTDocument19 pagesCoap &MQTTvidhyambikaNo ratings yet
- MQTT (Message Queue: Telemetry Transport)Document21 pagesMQTT (Message Queue: Telemetry Transport)hpokhrelNo ratings yet
- CPE 445-Internet of Things - Chapter 6Document44 pagesCPE 445-Internet of Things - Chapter 6fa20-bce-046No ratings yet
- Iot Unit 4Document53 pagesIot Unit 4SRHNo ratings yet
- IoT Messaging ProtocolsDocument60 pagesIoT Messaging ProtocolsGUJARATHI KAVANNo ratings yet
- Introduction To The Iot Protocol, MQTT: Peter Niblett Ibm Senior Technical Staff MemberDocument47 pagesIntroduction To The Iot Protocol, MQTT: Peter Niblett Ibm Senior Technical Staff MemberJames Doolin100% (1)
- 12 01 2023 - CSE3009 IOT BK MQTT TopicsDocument30 pages12 01 2023 - CSE3009 IOT BK MQTT TopicsMann PandyaNo ratings yet
- IoT Messaging ProtocolsDocument58 pagesIoT Messaging ProtocolsPranjal YadavNo ratings yet
- MQTTDocument27 pagesMQTTMANUJA SNo ratings yet
- Edge To Cloud ProtocolDocument21 pagesEdge To Cloud ProtocolMuzammil BalochNo ratings yet
- Study Ex-8-MQTT ProtocolDocument4 pagesStudy Ex-8-MQTT ProtocolG KalaiarasiNo ratings yet
- Unit - Iv: Transport LayerDocument55 pagesUnit - Iv: Transport LayerSundaram MuthuNo ratings yet
- Co APDocument12 pagesCo APsri sai xeroxNo ratings yet
- Chp4 The Internet Transport Protocolv2Document68 pagesChp4 The Internet Transport Protocolv2Suriya Mahendran100% (1)
- Chess ClassDocument59 pagesChess Classameershaikh5009No ratings yet
- Unit - 3 NotesDocument48 pagesUnit - 3 NotesAnish RajNo ratings yet
- Iot Protocol: Advanced Message Queuing Protocol (AMQP)Document5 pagesIot Protocol: Advanced Message Queuing Protocol (AMQP)rujula shindeNo ratings yet
- HTTPDocument8 pagesHTTPKhushboo TNo ratings yet
- 2014 Issnip MQTT CoapDocument7 pages2014 Issnip MQTT CoapGalih Yudha PratamaNo ratings yet
- CC CCCC CCCC CCCCDocument6 pagesCC CCCC CCCC CCCCViic ZanettiNo ratings yet
- Unit 3Document96 pagesUnit 3kodofa6907No ratings yet
- Itc4303 - L4&L5Document80 pagesItc4303 - L4&L5KhalifaNo ratings yet
- MQTTDocument24 pagesMQTTKanu PatelNo ratings yet
- IoT U-IDocument51 pagesIoT U-IVardhan TvkNo ratings yet
- unit 4Document42 pagesunit 4sakshamsharma7257No ratings yet
- 05 - Unit 2 Week 7 - ProtocolDocument48 pages05 - Unit 2 Week 7 - ProtocolPathum ChamudithaNo ratings yet
- Chapter 5 - TransportDocument56 pagesChapter 5 - Transportajitsah110920No ratings yet
- Base IOTDocument99 pagesBase IOTnguyenbaviet89No ratings yet
- PC-Lec 13Document25 pagesPC-Lec 13sagar323No ratings yet
- MQTT ReportDocument18 pagesMQTT ReportMANUJA S83% (6)
- CN UNIT 4 Transport LayerDocument32 pagesCN UNIT 4 Transport Layerharsharewards1No ratings yet
- CHAPTER 5 Transport LayerDocument18 pagesCHAPTER 5 Transport LayerRani rajpurohitNo ratings yet
- IoT Protocols and Analytics in 40 CharactersDocument72 pagesIoT Protocols and Analytics in 40 CharactersToshnav KhatkeNo ratings yet
- Unit-4_SocketProgramming (1)Document30 pagesUnit-4_SocketProgramming (1)sakshampatwal2004No ratings yet
- Unit V Lec PlanDocument7 pagesUnit V Lec PlanNivethithaa DhanrajNo ratings yet
- Design Principles For Web ConnectivityDocument46 pagesDesign Principles For Web ConnectivityAryan VNo ratings yet
- Module 4Document31 pagesModule 4puneeth TNo ratings yet
- MQTT Vs Opc Ua: Simon DetollenaereDocument22 pagesMQTT Vs Opc Ua: Simon DetollenaereJosé María Rodríguez RiveraNo ratings yet
- Transport Layer ServicesDocument71 pagesTransport Layer ServicesSomnath SinhaNo ratings yet
- ADVANCED NETWORK PROTOCOLSDocument30 pagesADVANCED NETWORK PROTOCOLSJanus Cesar Ruizan QuilenderinoNo ratings yet
- DE Iot 10 08 2020Document54 pagesDE Iot 10 08 2020akhNo ratings yet
- Unit 3Document126 pagesUnit 3PrathameshNo ratings yet
- 4) Physical Design of IotDocument29 pages4) Physical Design of IotAkshaya BNo ratings yet
- Process-to-Process Delivery with UDP and TCPDocument53 pagesProcess-to-Process Delivery with UDP and TCPShiza SahooNo ratings yet
- FALLSEM2023-24 BCSE308L TH VL2023240100950 2023-04-24 Reference-Material-VDocument28 pagesFALLSEM2023-24 BCSE308L TH VL2023240100950 2023-04-24 Reference-Material-VManan SantokiNo ratings yet
- Communication ProtocolsTCPDocument11 pagesCommunication ProtocolsTCPDhiviyansh Punamiya OT3 - 433No ratings yet
- 13 01 2023 - CSE3009 IOT BK WebSocket XMPP DDSDocument14 pages13 01 2023 - CSE3009 IOT BK WebSocket XMPP DDSMann PandyaNo ratings yet
- Sending and Receiving TCPIP PacketsDocument30 pagesSending and Receiving TCPIP PacketsXNo ratings yet
- Department of Computer Science MCADocument6 pagesDepartment of Computer Science MCAMOHAMMED ASHICKNo ratings yet
- UNIT 3 TCP UDP Transport Layer ProtocolsDocument42 pagesUNIT 3 TCP UDP Transport Layer ProtocolsmOrtyyNo ratings yet
- IoT Protocols IoT ArchitectureDocument18 pagesIoT Protocols IoT ArchitectureVenkatasamy EEENo ratings yet
- AssignmentDocument4 pagesAssignmentChirantan BhuyanNo ratings yet
- MQTT - Iot Messaging Protocol Francisco Quintero Lead Firmware EngineerDocument33 pagesMQTT - Iot Messaging Protocol Francisco Quintero Lead Firmware EngineerChouichi GhadaNo ratings yet
- Unit 1Document12 pagesUnit 1svtNo ratings yet
- cn-unit-5-computer-network-notesDocument33 pagescn-unit-5-computer-network-notesgdsc.pragatiNo ratings yet
- 5 IoT MQTTDocument10 pages5 IoT MQTTramalingam sNo ratings yet
- MQTT Smart HouseDocument5 pagesMQTT Smart Househuyminh vuNo ratings yet
- Virtual Private Network: Internal Guide: Created By: Mr. Pravin Madha Nisarg KhandharDocument20 pagesVirtual Private Network: Internal Guide: Created By: Mr. Pravin Madha Nisarg KhandharSunil PillaiNo ratings yet
- Transport LayerDocument8 pagesTransport LayerKrishna VamsiNo ratings yet
- Smart and Connected CitiesDocument15 pagesSmart and Connected Citiesfa20-bce-046No ratings yet
- IoT SecurityDocument42 pagesIoT Securityfa20-bce-046No ratings yet
- Laboratory3 ECIDocument12 pagesLaboratory3 ECIfa20-bce-046No ratings yet
- CPE 445-Internet of Things-Chapter 5Document19 pagesCPE 445-Internet of Things-Chapter 5fa20-bce-046No ratings yet
- CPE 445-Internet of Things - Chapter 7Document39 pagesCPE 445-Internet of Things - Chapter 7fa20-bce-046No ratings yet
- MDS2205 GoWide4.6 User ManualDocument134 pagesMDS2205 GoWide4.6 User ManualNguyễn Công CườngNo ratings yet
- HyderabadDocument6 pagesHyderabadKaushal PrabhudesaiNo ratings yet
- Switch - 02: SW-SG220-LAB-LT1-02#sh RunDocument5 pagesSwitch - 02: SW-SG220-LAB-LT1-02#sh RunBudi XperiaNo ratings yet
- Routing and Switching Assignment #2: Instructor: Ali Ahmad SiddiquiDocument4 pagesRouting and Switching Assignment #2: Instructor: Ali Ahmad SiddiquiShahzad AliNo ratings yet
- ISE Lab 02Document76 pagesISE Lab 02hussamm0177No ratings yet
- Module 1-4Document17 pagesModule 1-4Faizan AttarNo ratings yet
- The Bryant Advantage CCNP ROUTE Study Guide: Back To IndexDocument57 pagesThe Bryant Advantage CCNP ROUTE Study Guide: Back To IndexTyler MillsNo ratings yet
- SNMP Serial Interface UtilizationDocument3 pagesSNMP Serial Interface Utilizationskydon86No ratings yet
- A664part7draft3 WDDocument85 pagesA664part7draft3 WDBernie DNo ratings yet
- Ethernet Alarms: © Tejas Networks India LTD., 2007, Proprietary InformationDocument23 pagesEthernet Alarms: © Tejas Networks India LTD., 2007, Proprietary InformationAyan GNo ratings yet
- Training DCACI 300-620Document324 pagesTraining DCACI 300-620Boumendil Abdelilah100% (7)
- TCP Wrapper Network Monitoring, Access Control, and Booby TrapsDocument7 pagesTCP Wrapper Network Monitoring, Access Control, and Booby Trapsdelta craiovaNo ratings yet
- Nexus 7k - Getting Started Examples - Part1 (Basics, VDC and VPC) - NetworkGeekStuffDocument26 pagesNexus 7k - Getting Started Examples - Part1 (Basics, VDC and VPC) - NetworkGeekStuffJean Jacques BelyNo ratings yet
- AP-7532 Access Point: Installation GuideDocument57 pagesAP-7532 Access Point: Installation Guidejarko tarrilloNo ratings yet
- LTE Handover: Source to Target eNodeBDocument3 pagesLTE Handover: Source to Target eNodeBArun BaidyaNo ratings yet
- Sdwan-17.9 - WorkshopDocument38 pagesSdwan-17.9 - Workshopweeoam01No ratings yet
- Braindumpstudy: Braindumpstudy Exam Dumps, High Pass Rate!Document13 pagesBraindumpstudy: Braindumpstudy Exam Dumps, High Pass Rate!gandalf56No ratings yet
- Openstack Super Bootcamp PDFDocument96 pagesOpenstack Super Bootcamp PDFPrasadValluraNo ratings yet
- Module 13 Packet Filtering and Proxy ServerDocument42 pagesModule 13 Packet Filtering and Proxy ServerNasRul NasrullahNo ratings yet
- Lab C4 Wireless WorksheetDocument2 pagesLab C4 Wireless WorksheetCameron HulseNo ratings yet
- Installation Guide: Fortigate 200Document54 pagesInstallation Guide: Fortigate 200mahamat ismael abdelkerimNo ratings yet
- Wire Shark AnalysisDocument10 pagesWire Shark AnalysisMaraNo ratings yet
- Network Intrusion Detection System Using SnortDocument22 pagesNetwork Intrusion Detection System Using SnortGetLyricsNo ratings yet
- Amazon Route 53 - AWS Cheat SheetDocument15 pagesAmazon Route 53 - AWS Cheat SheetOswaldo HernandezNo ratings yet
- 15EC752-Iot & Wireless Sensor Networks - Question Bank Module-1 Overview of Internet of ThingsDocument3 pages15EC752-Iot & Wireless Sensor Networks - Question Bank Module-1 Overview of Internet of ThingsrichaNo ratings yet
- Aviat DVM-ExP2 Stabilized Microwave Platform Data Sheet - Sept 2015Document2 pagesAviat DVM-ExP2 Stabilized Microwave Platform Data Sheet - Sept 2015simog1972No ratings yet
- VSOL Special FeaturesDocument55 pagesVSOL Special FeaturesEnzo GodoyNo ratings yet
- Packet Scheduling in Multipath TCP Fundamentals Lessons and OpportunitiesDocument13 pagesPacket Scheduling in Multipath TCP Fundamentals Lessons and OpportunitieshughNo ratings yet
- MTS200R: TER Time-SyncDocument4 pagesMTS200R: TER Time-SyncSatyamNo ratings yet
- Svi 9220 User GuideDocument103 pagesSvi 9220 User GuideAdrian MafteiNo ratings yet