Professional Documents
Culture Documents
Pix-Vpnclient PPTP Mppe Ipsec
Uploaded by
Yeng Yee Ng0 ratings0% found this document useful (0 votes)
7 views7 pagesPix-Vpnclient Pptp Mppe Ipsec
Original Title
Pix-Vpnclient Pptp Mppe Ipsec
Copyright
© © All Rights Reserved
Available Formats
PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentPix-Vpnclient Pptp Mppe Ipsec
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
0 ratings0% found this document useful (0 votes)
7 views7 pagesPix-Vpnclient PPTP Mppe Ipsec
Uploaded by
Yeng Yee NgPix-Vpnclient Pptp Mppe Ipsec
Copyright:
© All Rights Reserved
Available Formats
Download as PDF, TXT or read online from Scribd
You are on page 1of 7
Configuring the PIX Firewall and VPN Clients
Using PPTP, MPPE and IPSec
Document ID: 14095
Contents
Introduction
Prerequisites
Requirements
Components Used
Conventions
Configure
Network Diagram
Configurations
Cisco VPN 3000 Client 2.5.x or Cisco VPN Client 3.x and 4.x
Windows 98/2000/XP PPTP Client Setup
Verify
Troubleshoot
Troubleshooting Commands
Microsoft Related Issues
Related Information
Introduction
In this sample configuration, four different kinds of clients connect and encrypt traffic with the Cisco Secure
PIX Firewall as tunnel endpoint:
Users that run Cisco Secure VPN Client 1.1 on Microsoft Windows 95/98/NT
Users that run the Cisco Secure VPN 3000 Client 2.5.x on Windows 95/98/NT
Users that run native Windows 98/2000/XP PointtoPoint Tunneling Protocol (PPTP) clients
Users that run the Cisco VPN Client 3.x/4.x on Windows 95/98/NT/2000/XP
In this example, a single pool for IPsec and PPTP is configured. However, the pools can also be made
separate.
Prerequisites
Requirements
There are no specific requirements for this document.
Components Used
The information in this document is based on these software and hardware versions:
PIX Software Release 6.3.3
Cisco Secure VPN Client 1.1
Cisco VPN 3000 Client version 2.5
Cisco VPN Client 3.x and 4.x
Microsoft Windows 2000 and Windows 98 clients
Note: This was tested on PIX Software Release 6.3.3 but should work on release 5.2.x and 5.3.1. PIX
Software Release 6.x is required for the Cisco VPN Client 3.x and 4.x. (Support for the Cisco VPN 3000
Client 2.5 is added in PIX Software Release 5.2.x. The configuration also works for PIX Software Release
5.1.x, except for the Cisco VPN 3000 Client part.) IPsec and PPTP/Microsoft PointtoPoint Encryption
(MPPE) should be made to work separately first. If they do not work separately, they do not work together.
Note: PIX 7.0 uses the inspect rpc command to handle RPC packets. The inspect sunrpc command enables
or disables application inspection for the Sun RPC protocol. Sun RPC services can run on any port on the
system. When a client attempts to access an RPC service on a server, it must find out which port that
particular service runs on. It does this by querying the portmapper process on the wellknown port number
111. The client sends the RPC program number of the service, and gets back the port number. From this point
on, the client program sends its RPC queries to that new port.
The information in this document was created from the devices in a specific lab environment. All of the
devices used in this document started with a cleared (default) configuration. If your network is live, make sure
that you understand the potential impact of any command.
Conventions
Refer to the Cisco Technical Tips Conventions for more information on document conventions.
Configure
In this section, you are presented with the information to configure the features described in this document.
Note: Use the Command Lookup Tool (registered customers only) to obtain more information on the
commands used in this section.
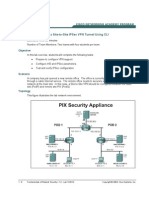
Network Diagram
This document uses the network setup shown in this diagram.
Configurations
This document uses these configurations.
Cisco Secure PIX Firewall
Cisco Secure VPN Client 1.1
Cisco Secure PIX Firewall
PIX Version 6.3(3)
interface ethernet0 auto
interface ethernet1 100full
nameif ethernet0 outside security0
nameif ethernet1 inside security100
enable password 8Ry2YjIyt7RRXU24 encrypted
passwd 2KFQnbNIdI.2KYOU encrypted
hostname goss515A
fixup protocol ftp 21
fixup protocol h323 h225 1720
fixup protocol h323 ras 17181719
fixup protocol http 80
fixup protocol ils 389
fixup protocol rsh 514
fixup protocol rtsp 554
fixup protocol sip 5060
fixup protocol sip udp 5060
fixup protocol skinny 2000
fixup protocol smtp 25
fixup protocol sqlnet 1521
names
accesslist 101 permit ip 10.99.99.0 255.255.255.0 192.168.1.0 255.255.255.0
pager lines 24
mtu outside 1500
mtu inside 1500
ip address outside 172.18.124.152 255.255.255.0
ip address inside 10.99.99.1 255.255.255.0
ip audit info action alarm
ip audit attack action alarm
ip local pool bigpool 192.168.1.1192.168.1.254
pdm history enable
arp timeout 14400
nat (inside) 0 accesslist 101
timeout xlate 3:00:00
timeout conn 1:00:00 halfclosed 0:10:00 udp 0:02:00 rpc 0:10:00 h225 1:00:00
timeout h323 0:05:00 mgcp 0:05:00 sip 0:30:00 sip_media 0:02:00
timeout uauth 0:05:00 absolute
aaaserver TACACS+ protocol tacacs+
aaaserver RADIUS protocol radius
aaaserver LOCAL protocol local
no snmpserver location
no snmpserver contact
snmpserver community public
no snmpserver enable traps
floodguard enable
sysopt connection permitipsec
sysopt connection permitpptp
crypto ipsec transformset myset espdes espmd5hmac
crypto dynamicmap dynmap 10 set transformset myset
crypto map mymap 10 ipsecisakmp dynamic dynmap
crypto map mymap client configuration address initiate
crypto map mymap client configuration address respond
crypto map mymap interface outside
isakmp enable outside
! Cisco Secure_VPNClient_key.
isakmp key ******** address 0.0.0.0 netmask 0.0.0.0
isakmp identity address
isakmp client configuration addresspool local bigpool outside
! ISAKMP Policy for Cisco VPN Client 2.5 or
! Cisco Secure VPN Client 1.1.
isakmp policy 10 authentication preshare
isakmp policy 10 encryption des
isakmp policy 10 hash md5
! The 1.1 and 2.5 VPN Clients use DiffieHellman (DH)
! group 1 policy (PIX default).
isakmp policy 10 group 1
isakmp policy 10 lifetime 86400
! ISAKMP Policy for VPN Client 3.0 and 4.0.
isakmp policy 20 authentication preshare
isakmp policy 20 encryption des
isakmp policy 20 hash md5
! The 3.0/4.0 VPN Clients use DH group 2 policy
! and PIX 6.0 code.
isakmp policy 20 group 2
isakmp policy 20 lifetime 86400
vpngroup vpn3000all addresspool bigpool
vpngroup vpn3000all dnsserver 10.99.99.99
vpngroup vpn3000all winsserver 10.99.99.99
vpngroup vpn3000all defaultdomain password
vpngroup vpn3000all idletime 1800
! VPN 3000 group_name and group_password.
vpngroup vpn3000all password ********
telnet timeout 5
ssh timeout 5
console timeout 0
vpdn group 1 accept dialin pptp
vpdn group 1 ppp authentication pap
vpdn group 1 ppp authentication chap
vpdn group 1 ppp authentication mschap
vpdn group 1 ppp encryption mppe auto
vpdn group 1 client configuration address local bigpool
vpdn group 1 pptp echo 60
vpdn group 1 client authentication local
! PPTP username and password.
vpdn username cisco password *********
vpdn enable outside
terminal width 80
Cryptochecksum:d41d8cd98f00b204e9800998ecf8427e
: end
goss515A#
Cisco Secure VPN Client 1.1
1 TACconn
My Identity
Connection security: Secure
Remote Party Identity and addressing
ID Type: IP subnet
10.99.99.0
255.255.255.0
Port all Protocol all
Connect using secure tunnel
ID Type: IP address
172.18.124.152
Preshared Key=CiscoSecure_VPNClient_key
Authentication (Phase 1)
Proposal 1
Authentication method: preshared key
Encryp Alg: DES
Hash Alg: MD5
SA life: Unspecified
Key Group: DH 1
Key exchange (Phase 2)
Proposal 1
Encapsulation ESP
Encrypt Alg: DES
Hash Alg: MD5
Encap: tunnel
SA life: Unspecified
no AH
2 Other Connections
Connection security: Nonsecure
Local Network Interface
Name: Any
IP Addr: Any
Port: All
Cisco VPN 3000 Client 2.5.x or Cisco VPN Client 3.x and 4.x
Select Options > Properties > Authentication. Groupname and group password match the group_name and
group_password on the PIX as in:
vpngroup vpn3000all password ********
Hostname = 172.18.124.152
Windows 98/2000/XP PPTP Client Setup
You can contact the vendor who makes the PPTP client. Refer to How to Configure the Cisco Secure PIX
Firewall to Use PPTP for information on how to set this up.
Verify
There is currently no verification procedure available for this configuration.
Troubleshoot
This section provides information you can use to troubleshoot your configuration.
Troubleshooting Commands
The Output Interpreter Tool (registered customers only) (OIT) supports certain show commands. Use the OIT
to view an analysis of show command output.
Note: Refer to Important Information on Debug Commands before you use debug commands.
PIX IPsec Debug
debug crypto ipsecDisplays the IPsec negotiations of phase 2.
debug crypto isakmpDisplays the Internet Security Association and Key Management Protocol
(ISAKMP) negotiations of phase 1.
debug crypto engineDisplays the traffic that is encrypted.
PIX PPTP Debug
debug ppp ioDisplays the packet information for the PPTP PPP virtual interface.
debug ppp errorDisplays PPTP PPP virtual interface error messages.
debug vpdn errorDisplays PPTP protocol error messages.
debug vpdn packetsDisplays PPTP packet information about PPTP traffic.
debug vpdn eventsDisplays PPTP tunnel event change information.
debug ppp uauthDisplays the PPTP PPP virtual interface AAA user authentication debugging
messages.
Microsoft Related Issues
How to Keep RAS Connections Active After Logging Off When you log off from a Windows
Remote Access Service (RAS) client, any RAS connections are automatically disconnected. In order
to remain connected after you log off, enable the KeepRasConnections key in the registry on the RAS
client.
User Is Not Alerted When Logging On with Cached Credentials Symptoms When you
attempt to log on to a domain from a Windowsbased workstation or member server and a domain
controller cannot be located, no error message is displayed. Instead, you are logged on to the local
computer using cached credentials.
How to Write an LMHOSTS File for Domain Validation and Other Name Resolution Issues
There can be instances when you experience name resolution issues on your TCP/IP network and
you need to use Lmhosts files to resolve NetBIOS names. This article discusses the proper method of
creating an Lmhosts file to aid in name resolution and domain validation.
Related Information
IPsec Negotiation/IKE Protocols Support Pages
PIX Command Reference
Cisco PIX 500 Series Security Appliances Support Page
Requests for Comments (RFCs)
Configuring IPsec Network Security
Configuring Internet Key Exchange Security Protocol
Technical Support & Documentation Cisco Systems
Contacts & Feedback | Help | Site Map
2012 2013 Cisco Systems, Inc. All rights reserved. Terms & Conditions | Privacy Statement | Cookie Policy | Trademarks of
Cisco Systems, Inc.
Updated: Oct 13, 2008 Document ID: 14095
You might also like
- Network Security All-in-one: ASA Firepower WSA Umbrella VPN ISE Layer 2 SecurityFrom EverandNetwork Security All-in-one: ASA Firepower WSA Umbrella VPN ISE Layer 2 SecurityNo ratings yet
- Vpnclient Pix AesDocument11 pagesVpnclient Pix Aesodon7No ratings yet
- Network with Practical Labs Configuration: Step by Step configuration of Router and Switch configurationFrom EverandNetwork with Practical Labs Configuration: Step by Step configuration of Router and Switch configurationNo ratings yet
- Configurar VPN ASA PIX CiscoDocument23 pagesConfigurar VPN ASA PIX CiscoMauro GuañoNo ratings yet
- CISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkFrom EverandCISCO PACKET TRACER LABS: Best practice of configuring or troubleshooting NetworkNo ratings yet
- Cisco Press Configuring The Pix Firewall and VPN Clients Using PPTP, Mppe and IpsecDocument10 pagesCisco Press Configuring The Pix Firewall and VPN Clients Using PPTP, Mppe and IpsecismailNo ratings yet
- Set Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNFrom EverandSet Up Your Own IPsec VPN, OpenVPN and WireGuard Server: Build Your Own VPNRating: 5 out of 5 stars5/5 (1)
- Static Nat PixDocument15 pagesStatic Nat Pixdia3phongNo ratings yet
- Securing Communication of Legacy Applications with IPSec: Step-by-Step Guide to Protecting “Data in Transit” without Changes in Your Existing SoftwareFrom EverandSecuring Communication of Legacy Applications with IPSec: Step-by-Step Guide to Protecting “Data in Transit” without Changes in Your Existing SoftwareNo ratings yet
- Configuring Security FeaturesDocument8 pagesConfiguring Security FeaturesedinNo ratings yet
- Cisco CCNA Command Guide: An Introductory Guide for CCNA & Computer Networking Beginners: Computer Networking, #3From EverandCisco CCNA Command Guide: An Introductory Guide for CCNA & Computer Networking Beginners: Computer Networking, #3No ratings yet
- Lab 14.6.6.2 Configure A Site-To-Site Ipsec VPN Tunnel Using CliDocument9 pagesLab 14.6.6.2 Configure A Site-To-Site Ipsec VPN Tunnel Using CliJohnny Albert RodriguezNo ratings yet
- Building Telephony Systems with OpenSIPS - Second EditionFrom EverandBuilding Telephony Systems with OpenSIPS - Second EditionNo ratings yet
- Lab 10: Vpns - Ipsec Remote Access VPN: 10.1 DetailsDocument24 pagesLab 10: Vpns - Ipsec Remote Access VPN: 10.1 Detailscharles81No ratings yet
- Password Recovery Procedure For The PIX: Document ID: 8529Document4 pagesPassword Recovery Procedure For The PIX: Document ID: 8529JESUS REYESNo ratings yet
- Python Networking 101: Navigating essentials of networking, socket programming, AsyncIO, network testing, simulations and AnsibleFrom EverandPython Networking 101: Navigating essentials of networking, socket programming, AsyncIO, network testing, simulations and AnsibleNo ratings yet
- Checkpoint InterviewDocument18 pagesCheckpoint InterviewKaushal Kishor100% (1)
- Palo Alto Networks PlatformsDocument8 pagesPalo Alto Networks PlatformskumarNo ratings yet
- Mikrotik With 3cx PabxDocument3 pagesMikrotik With 3cx PabxMarcusTottiNo ratings yet
- DMVPN and Easy VPN Server With ISAKMP Profiles Configuration ExampleDocument16 pagesDMVPN and Easy VPN Server With ISAKMP Profiles Configuration Examplejhony_sieteNo ratings yet
- How To - Establish VPN Tunnel Between Cyberoam and CISCO PIXDocument4 pagesHow To - Establish VPN Tunnel Between Cyberoam and CISCO PIXsanju_81No ratings yet
- Ipsec Pix70 NatDocument28 pagesIpsec Pix70 NatRicardo Cien FuegosNo ratings yet
- CP 3000Document30 pagesCP 3000Deepak SharmaNo ratings yet
- Configure Nat On MikrotikDocument4 pagesConfigure Nat On Mikrotiknazm basmNo ratings yet
- Cisco Ipsec Static DynamicDocument9 pagesCisco Ipsec Static DynamichsitadmNo ratings yet
- PIX/ASA: Establish and Troubleshoot Connectivity Through The Cisco Security ApplianceDocument7 pagesPIX/ASA: Establish and Troubleshoot Connectivity Through The Cisco Security AppliancetsibiNo ratings yet
- EdgeRouter - L2TP IPsec VPN Server - Ubiquiti Networks Support and Help CenterDocument11 pagesEdgeRouter - L2TP IPsec VPN Server - Ubiquiti Networks Support and Help CenterFlorian MarinNo ratings yet
- CCP VPN Routera Routerb Config 00 PDFDocument20 pagesCCP VPN Routera Routerb Config 00 PDFharry2uniqueNo ratings yet
- CCNAS v1.1 SBADocument10 pagesCCNAS v1.1 SBACaleb Peters0% (1)
- Linksys Rv082 VPN Router Interoperability Profile: C o M C OmDocument11 pagesLinksys Rv082 VPN Router Interoperability Profile: C o M C OmhackergenomaNo ratings yet
- WPA Configuration Overview: Registered Customers OnlyDocument10 pagesWPA Configuration Overview: Registered Customers OnlyErick CamiloNo ratings yet
- Cisco CCNA Security Chapter 8 ExamDocument7 pagesCisco CCNA Security Chapter 8 ExamPaulina EcheverríaNo ratings yet
- Configuring An Ipsec Tunnel Through A Firewall With Nat: Document Id: 14138Document8 pagesConfiguring An Ipsec Tunnel Through A Firewall With Nat: Document Id: 14138pandvas5No ratings yet
- 5-CCIE Security V6.0 Lab-Demo-591Lab-16PgDocument16 pages5-CCIE Security V6.0 Lab-Demo-591Lab-16Pgmhakeem.elsaeedNo ratings yet
- CCNA Security Skills Based Challenge LabDocument9 pagesCCNA Security Skills Based Challenge LabSiaw YsNo ratings yet
- Cisco Spiad - Labv1.3.1Document91 pagesCisco Spiad - Labv1.3.1fernando JmzNo ratings yet
- Home Skip To Content Skip To Navigation Skip To FooterDocument33 pagesHome Skip To Content Skip To Navigation Skip To FooterNathan Petreli Ad'aNo ratings yet
- SIC Practical1 by STUD - TalksDocument9 pagesSIC Practical1 by STUD - TalksPradeep PrajapatiNo ratings yet
- VPN Pix PrivateDocument13 pagesVPN Pix PrivateRaj KaranNo ratings yet
- Configuring and Testing The VPN ClientDocument8 pagesConfiguring and Testing The VPN Clientonlycisco.tkNo ratings yet
- Configuring Remote Access Ipsec VPNS: Summary of The ConfigurationDocument8 pagesConfiguring Remote Access Ipsec VPNS: Summary of The ConfigurationvatzanNo ratings yet
- Dynamic PixDocument15 pagesDynamic PixAndika PajriNo ratings yet
- Configuring PPP and Authentication: in This SectionDocument16 pagesConfiguring PPP and Authentication: in This SectionSridatta PranavNo ratings yet
- How To - Establish VPN Tunnel Between Cyberoam and Cisco Router PIXDocument15 pagesHow To - Establish VPN Tunnel Between Cyberoam and Cisco Router PIXNurain AkramNo ratings yet
- Windows Server 2022 NPS RadiusDocument26 pagesWindows Server 2022 NPS RadiusKayNo ratings yet
- SECURE10LGDocument150 pagesSECURE10LGAzzafirNo ratings yet
- CCNP Security Secure Lab GuideDocument150 pagesCCNP Security Secure Lab Guidebkaraqa67% (3)
- Lab 10: IDPS - Snort & Cisco IDPS Sensors: 9.1 DetailsDocument24 pagesLab 10: IDPS - Snort & Cisco IDPS Sensors: 9.1 DetailsewNo ratings yet
- Remote Access IPsec TshootDocument50 pagesRemote Access IPsec Tshootsoumen1977No ratings yet
- Configuring Log SourcesDocument70 pagesConfiguring Log SourcesPichai Ng-arnpairojhNo ratings yet
- Unified Border Element (CUBE) With Cisco Unified Communications Manager (CUCM) Configuration ExampleDocument12 pagesUnified Border Element (CUBE) With Cisco Unified Communications Manager (CUCM) Configuration ExampleJuan GarciaNo ratings yet
- FirewallDocument26 pagesFirewallLekshmi BibinNo ratings yet
- Monitoring 20cisco 20secure 20pix Firewall 20using 20snmp 20and 20syslog 20through 20vpn 20tunnel 101220044316 Phpapp01Document18 pagesMonitoring 20cisco 20secure 20pix Firewall 20using 20snmp 20and 20syslog 20through 20vpn 20tunnel 101220044316 Phpapp01qoriahNo ratings yet
- Pix Asa 70 BrowseDocument9 pagesPix Asa 70 BrowsenakeuNo ratings yet
- 6.3.1.1 Lab - Securing Layer 2 Switches PDFDocument23 pages6.3.1.1 Lab - Securing Layer 2 Switches PDFnganga0% (2)
- 11.2.4.6 Lab - Accessing Network Devices With SSHDocument6 pages11.2.4.6 Lab - Accessing Network Devices With SSHParthPatel0% (3)
- Digi Connect® Wan Application Guide:: Sample Cisco Asa To Digi Connect / Connectport VPN Config PG 1Document6 pagesDigi Connect® Wan Application Guide:: Sample Cisco Asa To Digi Connect / Connectport VPN Config PG 1Miquel Pelegrí QuevedoNo ratings yet
- En Security Chp9 PTActA Secure-Network StudentDocument7 pagesEn Security Chp9 PTActA Secure-Network StudentmyropieNo ratings yet
- B2B VPN Configuration in Cisco ASADocument26 pagesB2B VPN Configuration in Cisco ASAnag_nag19No ratings yet
- HpiopcookbookDocument60 pagesHpiopcookbookSteven GloggerNo ratings yet
- Frequently Asked Questions On Company Formation & Foreign InvestmentDocument5 pagesFrequently Asked Questions On Company Formation & Foreign InvestmentYeng Yee NgNo ratings yet
- Sa Series SSL VPN AppliancesDocument12 pagesSa Series SSL VPN AppliancesYeng Yee NgNo ratings yet
- CheckPoint GuideDocument146 pagesCheckPoint GuideJamesNo ratings yet
- GT26 Software 3.4.1 Release NoteDocument6 pagesGT26 Software 3.4.1 Release NoteHubert Chang EscalanteNo ratings yet
- Datasheet Evolution MetroDocument2 pagesDatasheet Evolution MetroShyju PaulNo ratings yet
- Performance Comparison of EIGRP and ISIS/RIP Protocols: Shravan K. Narisetty, Santosh K. BalsuDocument4 pagesPerformance Comparison of EIGRP and ISIS/RIP Protocols: Shravan K. Narisetty, Santosh K. BalsuZaman SoomroNo ratings yet
- CURLDocument4 pagesCURLlinda976No ratings yet
- RealscanDocument6 pagesRealscanmemoona bibiNo ratings yet
- Link Layer Discovery Protocol LLDP On Huawei s3300 PDFDocument7 pagesLink Layer Discovery Protocol LLDP On Huawei s3300 PDFHussein DhafanNo ratings yet
- CCIE Service ProviderDocument1 pageCCIE Service ProviderwilliammikeNo ratings yet
- 銘板貼紙新Document8 pages銘板貼紙新Nguyễn Hoàng SơnNo ratings yet
- SSH Feature Overview GuideDocument20 pagesSSH Feature Overview GuideNaveen KolliNo ratings yet
- NetApp HCI With Mellanox SN2010 Switch Quick Cabling GuideDocument20 pagesNetApp HCI With Mellanox SN2010 Switch Quick Cabling GuideJuan Pedro Pablo Ameneiro DiazNo ratings yet
- LO1-Plan and Design Internet Infrastructure UpdatedDocument36 pagesLO1-Plan and Design Internet Infrastructure UpdatedKahlid Seid100% (2)
- Cloud Security BenchmarkDocument299 pagesCloud Security Benchmarkmichel bouabreNo ratings yet
- Cisco ISR 4000 Series Router DatasheetDocument20 pagesCisco ISR 4000 Series Router DatasheetMeela ZengNo ratings yet
- 4aa3 0725enwDocument16 pages4aa3 0725enwMohit PandyaNo ratings yet
- Week3 ModifiedDocument48 pagesWeek3 ModifiedAbdullah ShalanNo ratings yet
- Shell Control BoxDocument13 pagesShell Control BoxMonish BoroNo ratings yet
- Question Bank PDFDocument996 pagesQuestion Bank PDFachilllleNo ratings yet
- 01 CN65301EN86GLA0 System ArchitectureDocument28 pages01 CN65301EN86GLA0 System Architecturesaurabh singhNo ratings yet
- Integrated Service Digital Network IsdnDocument6 pagesIntegrated Service Digital Network IsdnvahidinkormanNo ratings yet
- Home Automation Over Ethernet REPORTDocument47 pagesHome Automation Over Ethernet REPORTamitrana86100% (1)
- NC G-Fence-3000 enDocument2 pagesNC G-Fence-3000 enaml tekNo ratings yet
- Ericsson Diameter Signaling ControllerDocument6 pagesEricsson Diameter Signaling ControllerMuthanna AliNo ratings yet
- Subneting IPV4 PretestDocument199 pagesSubneting IPV4 Pretestzulfindra juliantNo ratings yet
- Com 426 Practical (Ogidi)Document4 pagesCom 426 Practical (Ogidi)KhalifaNo ratings yet
- CompTIA Network + N106Document794 pagesCompTIA Network + N106Joe100% (1)
- Cst233 - Information Security & Assurance: Assignment 1 Assignment 2 White Paper RADIUS SecurityDocument10 pagesCst233 - Information Security & Assurance: Assignment 1 Assignment 2 White Paper RADIUS Securityaurox3dNo ratings yet
- Moxa Config InstructionDocument4 pagesMoxa Config InstructionMicutzu EuNo ratings yet
- Profinet IO Slave: X-Gateway Interface AddendumDocument50 pagesProfinet IO Slave: X-Gateway Interface AddendumEcaterina IrimiaNo ratings yet
- Networking and InternetworkingDocument58 pagesNetworking and Internetworkingsrinivasa_ds2kNo ratings yet
- Network Fault Finding and Wireshark: - Analysing SSL/TLSDocument7 pagesNetwork Fault Finding and Wireshark: - Analysing SSL/TLSAlexHera89No ratings yet
- Hacking: A Beginners Guide To Your First Computer Hack; Learn To Crack A Wireless Network, Basic Security Penetration Made Easy and Step By Step Kali LinuxFrom EverandHacking: A Beginners Guide To Your First Computer Hack; Learn To Crack A Wireless Network, Basic Security Penetration Made Easy and Step By Step Kali LinuxRating: 4.5 out of 5 stars4.5/5 (67)
- Linux: The Ultimate Beginner's Guide to Learn Linux Operating System, Command Line and Linux Programming Step by StepFrom EverandLinux: The Ultimate Beginner's Guide to Learn Linux Operating System, Command Line and Linux Programming Step by StepRating: 4.5 out of 5 stars4.5/5 (9)
- iPhone 14 Guide for Seniors: Unlocking Seamless Simplicity for the Golden Generation with Step-by-Step ScreenshotsFrom EverandiPhone 14 Guide for Seniors: Unlocking Seamless Simplicity for the Golden Generation with Step-by-Step ScreenshotsRating: 5 out of 5 stars5/5 (5)
- iPhone Unlocked for the Non-Tech Savvy: Color Images & Illustrated Instructions to Simplify the Smartphone Use for Beginners & Seniors [COLOR EDITION]From EverandiPhone Unlocked for the Non-Tech Savvy: Color Images & Illustrated Instructions to Simplify the Smartphone Use for Beginners & Seniors [COLOR EDITION]Rating: 5 out of 5 stars5/5 (5)
- Hacking Network Protocols: Complete Guide about Hacking, Scripting and Security of Computer Systems and Networks.From EverandHacking Network Protocols: Complete Guide about Hacking, Scripting and Security of Computer Systems and Networks.Rating: 5 out of 5 stars5/5 (2)
- ITIL® 4 Create, Deliver and Support (CDS): Your companion to the ITIL 4 Managing Professional CDS certificationFrom EverandITIL® 4 Create, Deliver and Support (CDS): Your companion to the ITIL 4 Managing Professional CDS certificationRating: 5 out of 5 stars5/5 (2)
- Mastering Windows PowerShell ScriptingFrom EverandMastering Windows PowerShell ScriptingRating: 4 out of 5 stars4/5 (3)
- Microsoft Azure Infrastructure Services for Architects: Designing Cloud SolutionsFrom EverandMicrosoft Azure Infrastructure Services for Architects: Designing Cloud SolutionsNo ratings yet
- Kali Linux - An Ethical Hacker's Cookbook - Second Edition: Practical recipes that combine strategies, attacks, and tools for advanced penetration testing, 2nd EditionFrom EverandKali Linux - An Ethical Hacker's Cookbook - Second Edition: Practical recipes that combine strategies, attacks, and tools for advanced penetration testing, 2nd EditionRating: 5 out of 5 stars5/5 (1)
- The Compete Ccna 200-301 Study Guide: Network Engineering EditionFrom EverandThe Compete Ccna 200-301 Study Guide: Network Engineering EditionRating: 5 out of 5 stars5/5 (4)
- Creating iOS apps with Xcode: Learn how to develop your own app (English Edition)From EverandCreating iOS apps with Xcode: Learn how to develop your own app (English Edition)No ratings yet
- RHCSA Exam Pass: Red Hat Certified System Administrator Study GuideFrom EverandRHCSA Exam Pass: Red Hat Certified System Administrator Study GuideNo ratings yet
- Evaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsFrom EverandEvaluation of Some Websites that Offer Virtual Phone Numbers for SMS Reception and Websites to Obtain Virtual Debit/Credit Cards for Online Accounts VerificationsRating: 5 out of 5 stars5/5 (1)
- IPHONE 15 Pro Max: A Step by Step Comprehensive Guide, Tips, Tricks, With New Features For Seniors and Beginners.From EverandIPHONE 15 Pro Max: A Step by Step Comprehensive Guide, Tips, Tricks, With New Features For Seniors and Beginners.No ratings yet
- Computer Networking: The Complete Beginner's Guide to Learning the Basics of Network Security, Computer Architecture, Wireless Technology and Communications Systems (Including Cisco, CCENT, and CCNA)From EverandComputer Networking: The Complete Beginner's Guide to Learning the Basics of Network Security, Computer Architecture, Wireless Technology and Communications Systems (Including Cisco, CCENT, and CCNA)Rating: 4 out of 5 stars4/5 (4)
- Palo Alto Networks: The Ultimate Guide To Quickly Pass All The Exams And Getting Certified. Real Practice Test With Detailed Screenshots, Answers And ExplanationsFrom EverandPalo Alto Networks: The Ultimate Guide To Quickly Pass All The Exams And Getting Certified. Real Practice Test With Detailed Screenshots, Answers And ExplanationsNo ratings yet
- Cybersecurity: The Beginner's Guide: A comprehensive guide to getting started in cybersecurityFrom EverandCybersecurity: The Beginner's Guide: A comprehensive guide to getting started in cybersecurityRating: 5 out of 5 stars5/5 (2)
- AWS Certified Solutions Architect Study Guide: Associate SAA-C01 ExamFrom EverandAWS Certified Solutions Architect Study Guide: Associate SAA-C01 ExamRating: 4 out of 5 stars4/5 (1)

































































































![iPhone Unlocked for the Non-Tech Savvy: Color Images & Illustrated Instructions to Simplify the Smartphone Use for Beginners & Seniors [COLOR EDITION]](https://imgv2-1-f.scribdassets.com/img/audiobook_square_badge/728318688/198x198/f3385cbfef/1715524978?v=1)